Cybersecurity: What Everyone Needs to Know
by P. W. Singer and Allan Friedman · 3 Jan 2014 · 587pp · 117,894 words
of a conversation The Tor Project, Inc., https://www.torproject.org/, accessed March 17, 2013. Tor built in The Tor Project, Inc., “Tor Browser Bundle,” https://www.torproject.org/projects/torbrowser.html.en, accessed March 17, 2013. circumvent each new technique “How China Blocks the Tor Anonymity Network,” The Physics arXiv (blog), MIT
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
by Kevin Mitnick, Mikko Hypponen and Robert Vamosi · 14 Feb 2017 · 305pp · 93,091 words
exit node, perhaps in Honolulu. To use Tor you will need the modified Firefox browser from the Tor site (torproject.org). Always look for legitimate Tor browsers for your operating system from the Tor project website. Do not use a third-party site. For Android operating systems, Orbot is a legitimate free
…
doesn’t someone just build an e-mail server within Tor? Someone did. Tor Mail was a service hosted on a site accessible only to Tor browsers. However, the FBI seized that server in an unrelated case and therefore gained access to all the encrypted e-mail stored on Tor Mail. This
…
is not, however, available for Android.23 And, at the time of this writing, the Tor project, which maintains the Tor browser (see here), has just released Tor Messenger. Like the Tor browser, the app anonymizes your IP address, which means that messages are difficult to trace (however, please note that, like with the
…
Tor browser, exit nodes are not by default under your control; see here). Instant messages are encrypted using end-to-end encryption. Like Tor, the app is
…
DVD or USB to boot the Tails distribution. When you boot, it will start up the operating system, which features several privacy tools, including the Tor browser. The privacy tools allow you to encrypt e-mail using PGP, encrypt your USB and hard drives, and secure your messages with OTR (off-the
…
Web because it is virtually anonymous. I say “virtually” because nothing truly ever is. Access to the Dark Web can be gained only through a Tor browser. In fact Dark Web sites, with complicated alphanumeric URLs, all end with .onion. As I mentioned earlier, the onion router was created by the US
…
have to see that a request was made to access site X and that a few seconds earlier, someone in New Hampshire fired up the Tor browser. The observer might suspect that the two events were related. Over time, access to the site and repeated access to Tor around the same time
…
could establish a pattern. One way to avoid creating that pattern is to keep your Tor browser connected at all times. In Ulbricht’s case—he got sloppy. Ulbricht apparently didn’t have a plan early on. In his initial discussions of
…
people who wouldn’t have any information about you to identify you to the police—we’re almost set. Almost. From this point on, the Tor browser should always be used to create and access all online accounts because it constantly changes your IP address. One of the first steps is to
…
originating IP addresses. So because even the best of these providers cannot be trusted, we will purchase a VPN service using laundered Bitcoin through the Tor browser. I suggest reviewing a VPN provider’s terms of service and privacy policies and find the one that seems the best of the bunch. You
…
specifically with each other. This is only necessary if you suspect that the original anonymity you’ve established is compromised. Otherwise you could use the Tor browser (after establishing a new Tor circuit) through the anonymous hotspot and VPN to access the Internet using a different persona. Of course, how much or
Cult of the Dead Cow: How the Original Hacking Supergroup Might Just Save the World
by Joseph Menn · 3 Jun 2019 · 302pp · 85,877 words
strategic and it’s causing problems for me. Thanks!” After a protracted struggle among the admins, the old cDc guard wrested control back. Sumners, Xerobank Tor browser creator Steve Topletz, and a few others in NSF, including self-described black hat and white nationalist Timothy “Matlock” Noonan, had their own publication and
Dragnet Nation: A Quest for Privacy, Security, and Freedom in a World of Relentless Surveillance
by Julia Angwin · 25 Feb 2014 · 422pp · 104,457 words
to be in Germany. Browsing on Tor is slow. As a test, I typed New York University’s Web address, www.nyu.edu, into the Tor browser and into the regular Firefox Web browser and clocked each of them. It took twenty seconds to launch in Tor and three seconds to launch
Dark Mirror: Edward Snowden and the Surveillance State
by Barton Gellman · 20 May 2020 · 562pp · 153,825 words
order to make it easier for novices to use, Tor developers had baked their magic into a custom version of Firefox. They called it the Tor Browser Bundle. Now a small team of NSA hackers had come up with a way to see through the browser’s privacy shields. The NSA liked
…
more if you don’t mind a couple quick questions.” Did the method rely on prior identification of a target, or could it compromise any Tor browser? Did it work against all operating systems? Were there any browser plug-ins that blocked the exploit? The intern happily entertained the shoptalk. “Thanks!” he
…
at all if a user switched off JavaScript, a programming language built into modern web browsers. Snowden was safe. He always switched off JavaScript. The Tor browser made that easy enough, but the scripting language was left on by default. Without explaining why, Snowden pointedly reminded me and Poitras in coming months
…
surveillance by, 180–81 Verizon metadata collected by, 142 Federal Trade Commission, 198 Felten, Ed, 232–33 on secrets revealed by metadata, 162–63 Firefox, Tor Browser Bundle of, 80 First Amendment, of U.S. Constitution, 14, 96, 99, 114, 185, 248, 261 FIRSTFRUITS, 225, 277 Brand on, 274 DOJ crime reports
The Dark Net
by Jamie Bartlett · 20 Aug 2014 · 267pp · 82,580 words
of a child for primarily sexual purposes’. According to UK law, these images are classified under five levels of obscenity. Once I’d opened my Tor browser, it took me two mouse clicks to arrive at the page advertising the link. If I had clicked again, I would have committed an extremely
…
’, and how much money you had in your account. Behind the slick facade was a sophisticated security system. The site was accessible only via a Tor browser, products could be bought only with Bitcoin, and visitors were advised to sign up with digital pseudonyms. Any correspondence between buyers and sellers took place
The Bitcoin Guidebook: How to Obtain, Invest, and Spend the World's First Decentralized Cryptocurrency
by Ian Demartino · 2 Feb 2016 · 296pp · 86,610 words
exit node can figure out what everyone requested but not who it belongs to. A Bitcoin address created and accessed by a computer using the Tor browser is virtually untraceable from the outside. If your computer is compromised by malware or viruses, no amount of precautions will prevent tracking. Popular operating systems
Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World
by Bruce Schneier · 2 Mar 2015 · 598pp · 134,339 words
see also counterterrorism; security; September 11, 2001, terrorist attacks thermostats, smart, 15 third-party doctrine, 67–68, 180 TLS (SSL) protocol, 215 TOM-Skype, 70 Tor browser, 158, 216, 217 Torch Concepts, 79 trade secrets, algorithms as, 196 transparency: algorithmic surveillance and, 196 corporate surveillance and, 192, 194, 196, 202, 207–8
American Kingpin: The Epic Hunt for the Criminal Mastermind Behind the Silk Road
by Nick Bilton · 15 Mar 2017 · 349pp · 109,304 words
of attack. He knew he couldn’t find the leader of the site—or leaders, perhaps, he acknowledged—as they were securely cloaked by the Tor browser online. But he also knew how any crime network worked, and that if you start at the bottom, you will eventually make your way to
The Great Firewall of China
by James Griffiths; · 15 Jan 2018 · 453pp · 114,250 words
such as Silk Road and Agora, which existed parallel to the world wide web but were accessible only by using specialised software, such as the Tor Browser. Tor was originally developed by the US government to help agents avoid detection overseas. It remains one of the most popular anti-surveillance tools, although
…
average person was a common complaint, especially for anonymising services such as Tor, although its developers too have since released the far easier-to-grasp Tor Browser. Having used FreeGate extensively myself when I first moved to China in 2010, I can attest to its relative user-friendliness. It also kept ahead
…
, Ilham, 132, 134, 140–1, 143, 150, 152, 158, 195, 199; detention, 157; father killing, 133; harassment experience, 135; trial of, 131, US exile, 140 Tor Browser, 100, 102 Touré, Hamadoun, 228, 231, 236 traffic spikes, websites, 2 Trivedi, Aseem, 209 trolls: Badiucao attacks, 211; pro-China government, 92, 212 Trump, Donald
Orwell Versus the Terrorists: A Digital Short
by Jamie Bartlett · 12 Feb 2015 · 50pp · 15,603 words
Silk Road
by Eileen Ormsby · 1 Nov 2014 · 269pp · 79,285 words
Culture & Empire: Digital Revolution
by Pieter Hintjens · 11 Mar 2013 · 349pp · 114,038 words
Tracers in the Dark: The Global Hunt for the Crime Lords of Cryptocurrency
by Andy Greenberg · 15 Nov 2022 · 494pp · 121,217 words
The Stack: On Software and Sovereignty
by Benjamin H. Bratton · 19 Feb 2016 · 903pp · 235,753 words
Click Here to Kill Everybody: Security and Survival in a Hyper-Connected World
by Bruce Schneier · 3 Sep 2018 · 448pp · 117,325 words
Narconomics: How to Run a Drug Cartel
by Tom Wainwright · 23 Feb 2016 · 325pp · 90,659 words

Fancy Bear Goes Phishing: The Dark History of the Information Age, in Five Extraordinary Hacks
by Scott J. Shapiro · 523pp · 154,042 words
Bitcoin: The Future of Money?
by Dominic Frisby · 1 Nov 2014 · 233pp · 66,446 words
Terms of Service: Social Media and the Price of Constant Connection
by Jacob Silverman · 17 Mar 2015 · 527pp · 147,690 words
Snowden's Box: Trust in the Age of Surveillance
by Jessica Bruder and Dale Maharidge · 29 Mar 2020 · 159pp · 42,401 words
Habeas Data: Privacy vs. The Rise of Surveillance Tech
by Cyrus Farivar · 7 May 2018 · 397pp · 110,222 words
Move Fast and Break Things: How Facebook, Google, and Amazon Cornered Culture and Undermined Democracy
by Jonathan Taplin · 17 Apr 2017 · 222pp · 70,132 words
Radicalized
by Cory Doctorow · 19 Mar 2019 · 444pp · 84,486 words
Bitcoin for the Befuddled
by Conrad Barski · 13 Nov 2014 · 273pp · 72,024 words
Bottoms Up and the Devil Laughs
by Kerry Howley · 21 Mar 2023
The People vs Tech: How the Internet Is Killing Democracy (And How We Save It)
by Jamie Bartlett · 4 Apr 2018 · 170pp · 49,193 words
Going Dark: The Secret Social Lives of Extremists
by Julia Ebner · 20 Feb 2020 · 309pp · 79,414 words
The Future of Money: How the Digital Revolution Is Transforming Currencies and Finance
by Eswar S. Prasad · 27 Sep 2021 · 661pp · 185,701 words
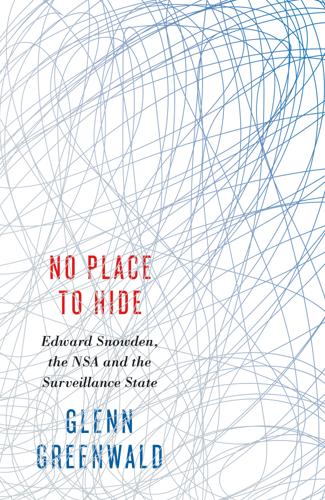
No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State
by Glenn Greenwald · 12 May 2014 · 253pp · 75,772 words