Edward Snowden
description: a former National Security Agency contractor who leaked classified information about global surveillance programs run by American and British spy agencies.
251 results
No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State
by Glenn Greenwald · 12 May 2014 · 253pp · 75,772 words
Glenn Greenwald No Place to Hide Edward Snowden, the NSA and the Surveillance State CONTENTS Title Page About the Author Also by Glenn Greenwald Dedication Epigraph Introduction 1. Contact 2. Ten Days in
…
for them. In America’s increasingly jingoistic and oppressive political climate, this proved to be an intensely controversial stance. It was this background that prompted Edward Snowden, several years later, to choose me as his first contact person for revealing NSA wrong-doing on an even more massive scale. He said he
…
now, either path is possible. Our actions will determine where we end up. 1 CONTACT On December 1, 2012, I received my first communication from Edward Snowden, although I had no idea at the time that it was from him. The contact came in the form of an email from someone calling
…
of the couch did I turn around. The first thing I saw was the unsolved Rubik’s Cube, twirling in the man’s left hand. Edward Snowden said hello but did not extend his hand to shake, as the point of the arrangement was to make this encounter appear to be random
…
do the same. At 2:00 p.m. Eastern time on Sunday, June 9, the Guardian published the story that revealed Snowden to the world: “Edward Snowden: The Whistleblower Behind the NSA Surveillance Revelations.” The top of the article featured Laura’s twelve-minute video; the first line read, “The individual responsible
…
for one of the most significant leaks in US political history is Edward Snowden, a 29-year-old former technical assistant for the CIA and current employee of the defence contractor Booz Allen Hamilton.” The article told Snowden’s
…
a writer. Ellsberg himself, writing the following day in the Guardian, proclaimed that “there has not been in American history a more important leak than Edward Snowden’s release of NSA material—and that definitely includes the Pentagon Papers 40 years ago.” Several hundred thousand people posted the link to their Facebook
…
Rio through Dubai, nowhere near the United States. For the moment, I reasoned, I had done enough. 3 COLLECT IT ALL The archive of documents Edward Snowden had assembled was stunning in both size and scope. Even as someone who had spent years writing about the dangers of secret US surveillance, I
…
a basic form to “justify” the surveillance, and the system returns the information requested. In the first video interview he gave when in Hong Kong, Edward Snowden made an audacious claim: “I, sitting at my desk, could wiretap anyone, from you or your accountant, to a federal judge or even the president
…
own actions. It is the ultimate imbalance, permitting the most dangerous of all human conditions: the exercise of limitless power with no transparency or accountability. Edward Snowden’s revelations subverted that dangerous dynamic by shining a light on the system and how it functions. For the first time, people everywhere were able
…
by General Michael Hayden, who led both the NSA and then the CIA under George Bush, and implemented the agency’s illegal warrantless eavesdropping program. “Edward Snowden,” he wrote on CNN.com, “will likely prove to be the most costly leaker of American secrets in the history of the Republic,” and then
…
want to take a look in the mirror if its editors wanted to understand why sources revealing major national security stories, like Chelsea Manning and Edward Snowden, did not feel safe or motivated to bring them their information. It is true that the New York Times published large troves of documents in
…
is the true measure of how far adversarial journalism in the United States has fallen. EPILOGUE In the very first online conversation I had with Edward Snowden, he told me he had only one fear about coming forward: that his revelations might be greeted with apathy and indifference, which would mean he
…
is the purpose of whistle-blowing, of activism, of political journalism. And that’s what is happening now, thanks to the revelations brought about by Edward Snowden. A NOTE ON SOURCES The endnotes and index for this book can be found at www.glenngreenwald.net. ACKNOWLEDGMENTS In recent years, the efforts of
…
living in a democracy, everyone who values transparency and accountability, owes these whistleblowers a huge debt of gratitude. The long line of predecessors who inspired Edward Snowden begins with Pentagon Papers leaker Daniel Ellsberg, one of my long-time personal heroes and now my friend and colleague, whose example I try to
Dark Mirror: Edward Snowden and the Surveillance State
by Barton Gellman · 20 May 2020 · 562pp · 153,825 words
by Bart Gellman. This page, photograph courtesy of Ben Wizner. LIBRARY OF CONGRESS CATALOGING-IN-PUBLICATION DATA Names: Gellman, Barton, 1960– author. Title: Dark mirror : Edward Snowden and the American Surveillance State / Barton Gellman. Description: New York : Penguin Press, 2020. | Includes bibliographical references and index. Identifiers: LCCN 2019049573 (print) | LCCN 2019049574 (ebook
…
step at a time and you climb up the mountain. You can tell that story later. —Author’s chat with Edward Snowden, June 9, 2013 This book takes up the gauntlet that Edward Snowden threw down for me that day, the same day he unmasked himself to the world. Shortly after this exchange, he
…
a few, are prepared to accept that this essential conversation would not have happened without him. “I know the world changed as a result of Edward Snowden, in a significant way,” former FBI director James B. Comey told me in a long and contemplative discussion of the leaks. “And I can more
…
capability to make it happen. All it would take is paying attention to how the system works, which is your job. —Edward Snowden to author, December 2013 Windows down, radio up, Edward Snowden steered his new Integra north on Highway 750 to a subterranean fortress. The gateway resembled a mine shaft sunk in a
…
. After twenty-five years in uniform, he knew he had no say in the decision. In the first week of May 2004, not long before Edward Snowden’s twenty-first birthday, Lon Snowden found a note under his door. “Dad, I know you’re going to be upset,” it began. His son
…
passed the physical fitness battery, the Army gave him a contract and a ticket to Fort Benning, Georgia. On June 3, 2004, Private First Class Edward Snowden reported for duty at E Company, Second Battalion, 19th Infantry Regiment as a Special Forces recruit. At five feet ten, Snowden began his infantry training
…
this panel some months ago, my fellow panelists did not foresee they’d be sitting up onstage with a guy who had communicated clandestinely with Edward Snowden.” An icebreaker, barely worth a chuckle. My kids would have called it a Dad joke. The response did not augur well. Moderator wit, I find
…
-level programming,” the classified announcement said. “We are also always open for ideas.” SEVEN FIRSTFRUITS You can’t tell everybody without telling the bad guys. —Edward Snowden to author, December 5, 2013 Late that first summer of Snowden, as I made my way through the NSA archive, I came across my own
…
December 21, 2013, to a manager in the Office of the National Counterintelligence Executive, or NCIX. “In the email, Gellman references conversations he has with Edward Snowden. . . . Are these emails useful for NCIX?” The manager replied, “Yes, these types of correspondence are useful. We will ensure they get to the FBI investigations
…
the Google engineer, Ellsberg bent over a borrowed notebook computer. Unfamiliar software logged him into an anonymous account. Somewhere in Moscow, ten time zones away, Edward Snowden awaited Ellsberg online. Each man had played a notable role in his times. Their rendezvous, preserved as a transcript, was self-consciously historic but intended
…
secretly broken into the main communications links that connect Yahoo and Google data centers around the world, according to documents obtained from former NSA contractor Edward Snowden and interviews with knowledgeable officials. By tapping those links, the agency has positioned itself to collect at will from hundreds of millions of user accounts
…
-term waiting game. “Neither of us,” Snowden told me, “have a driving need to see any kind of resolution.” ACKNOWLEDGMENTS My first thanks belong to Edward Snowden, who took me into his confidence and gave life to a vital public debate about the boundaries of secret intelligence in a free society. For
…
More Power,” New York Times, November 22, 2013, https://nyti.ms/31ToL5T. “I’m not sure I’ll ever”: Edward Snowden and Barton Gellman, live encrypted chat, October 2013. his memoir last year: Edward Snowden, Permanent Record (New York: Henry Holt, 2019). a book about power: See, for example, Jeffrey Vagle, “Surveillance Is Still
…
have been very few public references to Q Group. The best one I found is Eli Lake, “Inside the ‘Q Group,’ the Directorate Hunting Down Edward Snowden,” Daily Beast, June 10, 2013, http://thebea.st/1oYatwL. Top Secret, compartmented: The markings on the document were “TOP SECRET//SI//ORCON//NOFORN.” Among other
…
://nyti.ms/1TBmnJp, was a profile of the whistleblower William Binney for the newspaper’s “Op-Docs” series. failed to elicit a reply from Greenwald: Edward Snowden used the handle Cincinnatus, not Verax, for contact with Greenwald. Micah Lee, then a staff technologist at the Electronic Frontier Foundation, said the anonymous source
…
the first Snowden disclosure. See “Presidential Policy Directive 19,” October 10, 2012, http://fas.org/irp/offdocs/ppd/ppd-19.pdf. Also see Glenn Kessler, “Edward Snowden’s Claim That He Had ‘No Proper Channels’ for Protection as a Whistleblower,” Washington Post, March 12, 2014, http://wapo.st/1RMjylz. The Intelligence Community
…
Cheney: See Gellman, Angler, chapters 11 and 12. “Wish I knew the underlying details”: Author to Poitras, August 7, 2012. Years later he told me: Edward Snowden, interview with author, July 1, 2015, Moscow. one final breach of NSA defenses: I tell this story in the final chapter of this book. “Edward
…
lengthy exchange of emails, that he had planned to bike but changed his mind and drove despite the small risk of an epileptic seizure. See Edward Snowden, Permanent Record (New York: Henry Holt, 2019), 215. six seizure-free months before driving: Hawaii’s law was actually stricter than Maryland’s, which forbade
…
Wheeler, and Ky Henderson, “Exclusive: Snowden Tried to Tell NSA About Surveillance Concerns, Documents Reveal,” Vice News, June 4, 2016, https://news.vice.com/article/edward-snowden-leaks-tried-to-tell-nsa-about-surveillance-concerns-exclusive. The full correspondence is at www.documentcloud.org/documents/2852366-Leopold-FOIA-NSA-Emails-About-Snowden
…
, December 29, 2001, https://arstechnica.com/civis/viewtopic.php?p=16430380#p16430380. Shrike and Belgarion: Snowden, Permanent Record, 48. His father, Lonnie G. Snowden Jr.: Edward Snowden and a family confidant, interviews with author, 2015 and 2016. See also Bryan Burrough, Sarah Ellison, and Suzanna Andrews, “The Snowden Saga: A Shadowland of
…
Secrets and Light,” Vanity Fair, May 2014, www.vanityfair.com/news/politics/2014/05/edward-snowden-politics-interview. Snowdens moved north: In 1993, the Snowdens bought a house on Knights Bridge Turn in Crofton, Maryland. See Julie Bykowicz and Greg Giroux
…
, see iqcomparisonsite.com/iqtable.aspx. Also see James Bamford, “The Most Wanted Man in the World,” Wired, August 22, 2014, www.wired.com/2014/08/edward-snowden/. Snowden’s older sister: Federal Judicial Center, “Annual Report” (2015), https://archive.fo/yhlza. She skipped a grade: Family confidant, interview with author, July 22
…
: Family confidant, interview with author, October 12, 2015. His grades were erratic: Family confidant, interview with author, July 22, 2014. refused to return to school: Edward Snowden, interviews with author, 2015. See also Snowden, Permanent Record, 65. “The public education system”: The accent in “spikéd” and the confusion of “its” and “it
…
at random: Snowden and a family confidant, interviews with author, 2014 and 2015. See also Jean Marbella, Shashank Bengali, and David S. Cloud, “Details About Edward Snowden’s Life in Maryland Emerge,” Baltimore Sun, June 10, 2010, www.baltimoresun.com/news/maryland/bs-md-snowden-profile-20130610-story.html. “I’m not
…
system engineering: Snowden, interview with author, July 1, 2015, Moscow; family confidant, interview with author, December 10, 2015. See also Matthew Mosk et al., “Timeline: Edward Snowden’s Life as We Know It,” ABC News, June 13, 2013, http://abcn.ws/21lizMS. Johns Hopkins University cut its ties with the for-profit
…
, Ryuhana Press, Wayback Machine, July 9, 2003, http://web.archive.org/web/20030709083138/http://www.ryuhanapress.com/jodon.html. move-by-move reaction times: See Edward Snowden, writing as TheTrueHOOHA, “Tekken Fans Rite This Way,” Ars Technica OpenForum, April 28, 2003, https://arstechnica.com/civis/viewtopic.php?p=12972113#p12972113. Armed with
…
Battery: Rod Powers, “All About the DLAB,” USmilitary.about.com, October 23, 2015, http://usmilitary.about.com/cs/joiningup/a/dlab.htm. Private First Class Edward Snowden: Snowden’s Army discharge papers, on file with author, include his dates of service from June 3, 2004, to September 28, 2004, his rank as
…
Industries, for his part-time employer. Snowden, Permanent Record, 70. The firm was actually called Clockwork Chihuahua Studios. “The truth is going to get out”: Edward Snowden, interview with author, Moscow, December 6, 2013. he donated $250: Snowden’s campaign contributions, as distinguished from those of a theatrical producer and a tech
…
Paul Gives Thanks to Leaker,” CNN, June 10, 2013, http://cnn.it/28Lj7Xx. he wore a hoodie: Andy Greenberg, “An NSA Coworker Remembers the Real Edward Snowden: ‘A Genius Among Geniuses,’” Forbes, December 16, 2013, http://onforb.es/1YWdXMc. eagle wearing comically oversized headphones: Aaron Jue, “NSA Spying Hoodies,” Electronic Frontier Foundation
…
, October 16, 2012, www.eff.org/deeplinks/2012/10/nsa-spying-hoodies. He also kept a copy: Greenberg, “NSA Coworker Remembers the Real Edward Snowden.” Runa Sandvik: Snowden (as “Cincinnatus”) to Sandvik, Novmber 18, 2012, copy on file with author. At this writing, Sandvik is chief of information security at
…
the record.” “It’s not an exaggeration”: Snowden, chat with author, February 13, 2014. “If you had a guy”: Greenberg, “NSA Coworker Remembers the Real Edward Snowden.” published an automated notice: The lists were published as self-updating RSS feeds, an acronym for “really simple syndication.” crawl around digital networks: The best
…
//SI//REL, on file with author. CAPTAINCRUNCH: Confidential source, interview with author, 2015. In his first filmed interview: Laura Poitras and Glenn Greenwald, “NSA Whistleblower Edward Snowden: ‘I Don’t Want to Live in a Society That Does These Sort of Things,’” Guardian, June 9, 2013, www.theguardian.com/world/video/2013
…
/jun/09/nsa-whistleblower-edward-snowden-interview-video. boarded a flight to Tokyo: Most accounts have reported erroneously that Snowden took a direct flight from Honolulu to Hong Kong. He told
…
-Pike: What’s Different Now,” address at the National Security Agency, May 15, 2015, on file with author. “You may have time constraints”: Author to Edward Snowden, email, May 18, 2013. Our conversation that day was prospective, as I did not yet have the document in hand. I was trying to understand
…
documents, pertaining solely to PRISM, amid his own ongoing work on the larger story. None of that was correct. Glenn Greenwald, No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State (New York: Metropolitan Books, 2014), 16–18. the Post and I assembled lawyers: Ibid. This was a
…
directly with Snowden in late March or early April, he said,” according to that story. Michael Calderone, “How Glenn Greenwald Began Communicating with NSA Whistleblower Edward Snowden,” Huffington Post, June 10, 2013, http://huff.to/1pBnqfl, archived at https://archive.is/fFeol. unaware that Verax was the Cincinnatus: Greenwald, No Place to
…
for Living Under Total Surveillance (New York: Whitney Museum of American Art, 2016); screen shots from the documentary film Citizen Four (Praxis Films, 2014); and Edward Snowden’s pseudonymous video, anon108, “GPG for Journalists—Windows edition | Encryption for Journalists | Anonymous 2013,” Vimeo, January 6, 2013, https://vimeo.com/56881481. I know of
…
, p. 20, on file with author. “The actual architecture is very”: Chris Inglis, interview with author, June 14, 2013. a twelve-minute video: “NSA Whistleblower Edward Snowden: ‘I Don’t Want to Live in a Society That Does These Sort of Things’—Video,” Guardian, June 9, 2013, www.theguardian.com/world/video
…
/2013/jun/09/nsa-whistleblower-edward-snowden-interview-video. “I’m scrolling through my Twitter feed”: C. Danielle Massarini, interview with author, August 12, 2016. CHAPTER FIVE: BACKLASH “We’re not going
…
Hong Kong authorities. The grand jury empaneled in Norfolk very likely has handed up a sealed indictment alleging additional criminal counts. See Criminal Complaint of Edward Snowden, United States v. Edward J. Snowden, Case No. 1:13 CR 265, U.S. District Court for the Eastern District of Virginia, at https://perma
…
31, 2017, at https://perma.cc/HRW5-ETNP. his coming-out video: The Guardian posted the videotaped interview: Laura Poitras and Glenn Greenwald, “NSA Whistleblower Edward Snowden: ‘I Don’t Want to Live in a Society That Does These Sort of Things,’” Guardian, on June 9, 2013, www.theguardian.com/world/video
…
/2013/jun/09/nsa-whistleblower-edward-snowden-interview-video. Hong Kong–based reporter: Lana Lam, “EXCLUSIVE: Whistle-Blower Edward Snowden Talks to South China Morning Post,” South China Morning Post, June 12, 2013, at https://perma.cc/7BM6-7DBQ
…
resemblance: Some have seen these differences as essential to the legitimacy of their respective leaks, comparing Snowden unfavorably to Ellsberg. See Malcolm Gladwell, “Daniel Ellsberg, Edward Snowden, and the Modern Whistle-Blower,” New Yorker, December 19 and 26, 2016, at https://perma.cc/YU2E-EY8W. then six hypotheses: Ashkan typed out a
…
on how Snowden does and does not fit into theoretical models of legitimate civil disobedience, see David Pozen, “Edward Snowden, National Security Whistleblowing and Civil Disobedience,” Lawfare, March 26, 2019, www.lawfareblog.com/edward-snowden-national-security-whistleblowing-and-civil-disobedience. The essay was adapted from the forthcoming volume Whistleblowing Nation: Disclosing U.S
…
”: Rajesh De, interview with author, July 18, 2013. tamper-detection device: This project, called Haven, was coauthored with security developer Nathan Freitas. See Micah Lee, “Edward Snowden’s New App Uses Your Smartphone to Physically Guard Your Laptop,” Intercept, December 22, 2017, https://theintercept.com/2017/12/22/snowdens-new-app-uses
Permanent Record
by Edward Snowden · 16 Sep 2019 · 324pp · 106,699 words
to remember the teacher’s name, or trying not to. She, the polygrapher, began asking questions. The first ones were no-brainers: Was my name Edward Snowden? Was 6/21/83 my date of birth? Then: Had I ever committed a serious crime? Had I ever had a problem with gambling? Had
…
the agency. I wish I remembered the exact chronology of my contracting, but I don’t have a copy of my résumé anymore—that file, Edward_Snowden_Resume.doc, is locked up in the Documents folder of one of my old home computers, since seized by the FBI. I do recall, however
…
and had me call him. A secretary picked up and I told her that my name was Lindsay Mills and I was the girlfriend of Edward Snowden and needed representation. The secretary said, “Oh, let me put you right through.” It was funny to hear the recognition in her voice. Jerry picked
…
’t, green’s not your color. At the fitting room’s entrance was a TV blaring the news and I froze when the announcer said “Edward Snowden’s girlfriend.” I fled the stall, and stood in front of the screen. Watching as my photos flicked by. I whipped out my phone and
…
can end this book is the way I began it: with a dedication to Lindsay, whose love makes life out of exile. ABOUT THE AUTHOR Edward Snowden was born in Elizabeth City, North Carolina, and grew up in the shadow of Fort Meade. A systems engineer by training, he served as an
…
Road, London N1 9RR Associated companies throughout the world www.panmacmillan.com ISBN 978-1-5290-3567-4 Copyright © Edward Snowden 2019. Jacket design by Rodrigo Corral Jacket photograph © Platon The right of Edward Snowden to be identified as the author of this work has been asserted by him in accordance with the Copyright
The Perfect Weapon: War, Sabotage, and Fear in the Cyber Age
by David E. Sanger · 18 Jun 2018 · 394pp · 117,982 words
the concentrated Chinese effort will flow directly to the country’s military might. An equivalent to the Silicon Valley/Washington divide, which bubbled along before Edward Snowden’s disclosures and re-erupted in the battles over the government’s effort to get a back door into encrypted systems, does not exist in
…
as the director say”: Maya Rhodan, “New NSA Chief: Snowden Didn’t Do That Much Damage,” Time, June 30, 2014, time.com/2940332/nsa-leaks-edward-snowden-michael-rogers/. But Merkel was outraged: Alison Smale, “Germany, Too, Is Accused of Spying on Friends,” New York Times, May 6, 2015, www.nytimes.com
This Is How They Tell Me the World Ends: The Cyberweapons Arms Race
by Nicole Perlroth · 9 Feb 2021 · 651pp · 186,130 words
. Together, Jill and Dean said Scott and I were to work alongside the Guardian and ProPublica to write two stories based off the leaks from Edward Snowden, the infamous NSA contractor who had removed thousands of classified documents from the agency’s computers before fleeing to Hong Kong, and later taking up
…
Apple’s backdoor? Back and forth Apple and the Justice Department went, in a courtroom dispute that captivated the country. Everyone from the president to Edward Snowden to the comedian John Oliver weighed in. Polls showed Americans were split but tilting toward Apple, more so every day. Even Carole Adams, the mother
…
on Operation Ivy Bells to describe the undersea cable tap: “40 Years Ago, The Navy’s ‘Operation Ivy Bells’ Ended With a 70s Version of Edward Snowden,” published by Business Insider. A history of Los Alamos is available via the U.S. Department of Energy’s Office of History and Heritage Resources
Gray Day: My Undercover Mission to Expose America's First Cyber Spy
by Eric O'Neill · 1 Mar 2019 · 299pp · 88,375 words
and former CIA employee walked out of the NSA with thumb drives loaded with (according to the NSA) an estimated 1.7 million classified files. Edward Snowden has personally admitted to stealing hundreds of thousands of highly classified files detailing US intelligence-collection programs by the NSA. (The actual number is likely
The Snowden Files: The Inside Story of the World's Most Wanted Man
by Luke Harding · 7 Feb 2014 · 266pp · 80,018 words
Had Your Fun 10. Don’t Be Evil 11. Flight 12. Der Shitstorm! 13. The Broom Cupboard 14. Shoot the Messenger Epilogue: Exile Acknowledgements Foreword Edward Snowden is one of the most extraordinary whistleblowers in history. Never before has anyone scooped up en masse the top-secret files of the world’s
…
in a world where everything that I say, everything I do, everyone I talk to, every expression of creativity or love or friendship is recorded …’ EDWARD SNOWDEN It began with an email. ‘I am a senior member of the intelligence community …’ No name, no job title, no details. The Guardian columnist Glenn
…
, next to a large plastic alligator. They would swap pre-agreed phrases. The source would carry a Rubik’s cube. Oh, and his name was Edward Snowden. It appeared the mystery interlocutor was an experienced spy. Perhaps one with a flair for the dramatic. Everything Greenwald knew about him pointed in one
…
May 2012. After that he disappears, a lost electronic signature amid the vastness of cyberspace. But a year later, as we now know, TheTrueHOOHA, aka Edward Snowden, travels to Hong Kong. Edward Joseph Snowden was born on 21 June 1983. Friends know him as ‘Ed’. His father Lonnie Snowden and mother Elizabeth
…
left Japan and moved across the Pacific to Hawaii. At the same time, it seems he donated to his libertarian political hero Ron Paul. An ‘Edward Snowden’ contributed $250 to Paul’s presidential campaign from an address in Columbia, Maryland. The record describes the donor as an employee of Dell. In May
…
men ‘intelligencers’ or ‘espials’; what they got up to was espiery. (The French term espionage only came into use from the 18th century onwards.) But Edward Snowden, the modern-day espial, could not use his true name if he was to reach out to the US reporters who worked on national security
…
list.’ Five months later, during their encounter in Hong Kong, Greenwald realised his would-be source back in late 2012 had been none other than Edward Snowden. Snowden was among Greenwald’s community of readers. Liking Greenwald’s world view, his brio and his uncompromising approach to government, Snowden had reached out
…
: ‘Your destination is Hong Kong.’ The next day a further message arrived for Poitras, in which the source for the first time gave his name: ‘Edward Snowden’. The name meant nothing; Poitras knew that if she searched Snowden’s name on Google this would immediately alert the NSA. Attached was a map
…
Julian Assange of WikiLeaks was to call, with only some exaggeration, ‘the greatest spying machine the world has ever seen’. But before the appearance of Edward Snowden, very little of the truth about that had reached the surface. The NSA – the biggest and most secretive of the US intelligence agencies – failed on
…
biggest and most intrusive domestic and international surveillance programs were thus kept from the American public in whose name they were being carried out. When Edward Snowden got on a plane for Hong Kong in 2013, the material he held on his laptops was highly explosive. 5 THE MAN IN THE ROOM
…
anyway. So we have literally nothing to lose in terms of access.’ The Guardian was the third-largest newspaper website in the world, well before Edward Snowden came along. But seemingly the White House had little idea what the title was – a newspaper, a free sheet, a blog? – or about the nature
…
were a Chinese spy, why wouldn’t I have flown directly into Beijing? I could be living in a palace, petting a phoenix, by now.’ EDWARD SNOWDEN It had been around 3am local time when the Guardian broke the first of Snowden’s NSA stories. Returning to his Hong Kong hotel room
…
project, developed by the UK. Its fruits are handed over to London’s US paymasters. The program is so sensitive that exposures of it by Edward Snowden drive British officials into fits of anxiety and rage. Those officials’ dream is to ‘master the internet’. This phrase of theirs was what Snowden meant
…
soon became frowsty. ‘It smells like a teenage boy’s bedroom in here,’ said one visitor. Posted onto a whiteboard was a memo from Rusbridger: ‘Edward Snowden approached the Guardian because he says people have no idea of the extent of what he regards as the surveillance state. He argues that technology
…
South China Morning Post, to that of a ‘people smuggler’. Proprietorially claiming Snowden as the latest star player for Team WikiLeaks, the statement said: ‘Mr Edward Snowden, the American whistleblower who exposed evidence of a global surveillance regime conducted by US and UK intelligence agencies, has left Hong Kong legally. He is
…
easy knowing I cannot be coerced into revealing that information, even under torture. With my thanks for your service to the nation we both love, Edward Snowden The letter set out cardinal Snowdon themes: love of country, civic duty, a desire to protect the constitution. Its tone was high-minded and in
…
a terrorist. The British authorities knew that perfectly well. He was the partner of a journalist. They suspected he was in fact carrying copies of Edward Snowden’s NSA and GCHQ files, which Greenwald was engaged in researching and publishing. Their prime purpose, as they were later to admit, was simply to
…
remarked that the details of snooping exposed by newspapers are ‘not even remotely related to fighting terrorism’. He wrote: ‘Osama bin Laden did not need Edward Snowden’s revelations about PRISM to realise the US was listening to every bit of electronic communication: he had already seceded from the world of telephony
…
Home Office said it had acted in the interests of national security. The authorities had wanted to know ‘where Mr Miranda fitted in the broader Edward Snowden network’. The journalists involved weren’t motivated by public interest but were ‘advancing a political or ideological cause’. The day after the review finished – with
…
. Now, it seemed, they were suspects. Epilogue: Exile Somewhere near Moscow 2014–? ‘Even in Siberia there is happiness.’ ANTON CHEKHOV, In Exile For nine weeks Edward Snowden was mostly invisible. There was the odd photo – of a young man pushing a shopping trolley across a Moscow street. (Surely a fake? The man
…
your country when the situation is resolved and thank you for your efforts in upholding the international laws that protect us. ‘With my best regards ‘Edward Snowden’ Days later, Harrison said goodbye to Snowden and flew to Berlin. She had been with him in Moscow for four months. On what was said
Snowden's Box: Trust in the Age of Surveillance
by Jessica Bruder and Dale Maharidge · 29 Mar 2020 · 159pp · 42,401 words
the NSA revelations, the talk show host John Oliver dispatched a camera crew to Times Square. Interviewing passersby, they found most could not accurately identify Edward Snowden. Folks remembered some kind of leak had happened, but not what it was or why it mattered. (They did, however, express grave anxiety over the
…
state — a despot’s dream — it would have been impossible. Intermediate steps and experiments would have been quashed at every turn. In the days after Edward Snowden’s first leaks, the security researcher Moxie Marlinspike referred to that process in a blog post called “We Should All Have Something to Hide.” “Imagine
…
way it was handled would be a disservice to our source, the risks we’ve all taken, and most importantly, to the public for whom Edward Snowden blew the whistle.” She added that, even though the archive was no longer breaking news, “it remains the most significant historical archive documenting the rise
…
Bamford, “The Most Wanted Man In The World,” Wired, September 2014. p. 2 an existential threat to democracy: Glenn Greenwald, Ewen MacAskill, and Laura Poitras, “Edward Snowden: The Whistleblower behind the NSA Surveillance Revelations,” Guardian, June 9, 2013. p. 3 General Social Survey: Chris Cillizza, “Watch Americans’ Trust in Each Other Erode
…
the Bobby McFerrin classic: youtube.com/watch?v=LbTxfN8d2CI. p. 7 Despite my intentions, I never created the time: Glenn Greenwald, No Place to Hide: Edward Snowden, the NSA and the Surveillance State (New York: Metropolitan Books, 2014), 9. p. 8 You always have to trust somebody: Jon Evans, “WhatsApp, Signal and
…
Times’ Editor: Losing Snowden Scoop ‘Really Painful,’” National Public Radio, June 5, 2014, Npr.org. p. 40 New York Times “far too accommodating of power”: Edward Snowden, encrypted email to Laura Poitras in early May 2013. p. 40 the Times spiked a story: Margaret Sullivan, “Lessons in a Surveillance Drama Redux,” New
…
Snowden answering questions: On June 9, the Guardian ran a short film by Laura Poitras. It showed Snowden answering questions posed by Greenwald. “NSA Whistleblower Edward Snowden: ‘I don’t want to live in a society that does these sort of things,’” Guardian, video, June 9, 2013, www.theguardian.com/world/video
…
/2013/jun/09/nsa-whistleblower-edward-snowden-interview-video. p. 48 The Mira Hotel in Kowloon: Ewen MacAskill, “Edward Snowden: How the Spy Story of the Age Leaked Out,” Guardian, June 12, 2013. p. 49 “I will never commit
…
source had contacted another Freedom of the Press Foundation board member: Greenwald, No Place to Hide, 7. pp. 70–2 twelve-minute instructional video: anon108 [Edward Snowden], “GPG for Journalists,” uploaded Sunday, January 6, 2013, vimeo.com/user15675314. p. 72 “Cincinnatus” described his mounting frustration: Greenwald, No Place to Hide, 10. p
…
selected”: Poitras, Citizenfour, 4:22–5:06. p. 73 DARKDIAMOND for Laura and SILVERSHOT for Micah: Poitras, Astro Noise, 101. p. 73 COPPERCOMET for Greenwald: Edward Snowden to Laura Poitras in an encrypted email on April 21, 2013. pp. 73–4 Henk Penning on trust: “On the Apache.org Web of Trust
…
“confirm that no one has ever had a copy of your private key”: Poitras, Citizenfour, 1:19–1:27. p. 80 Lindsay Mills: Paul Lewis, “Edward Snowden’s Girlfriend Lindsay Mills: At the Moment I Feel Alone,” Guardian, June 11, 2013. 4. American Amnesia p. 83 “Power concedes nothing without a demand
…
Surveillance: Live Updates,” RT Question More, October 26, 2013, rt.com. p. 85 Snowden statement: Jesselyn Radack, “My Visit with Edward Snowden,” Nation, October 17, 2013; “Stop Watching Us Rally 10/26/13 Edward Snowden Statement,” YouTube. p. 85 “Privacy Chernobyl”: Till Wäscher, “Six Frames against Surveillance,” Internet Policy Observatory, Globalnetpolicy.org. p. 86
…
iPhone a ‘Marketing Strategy,’” New York Times, February 19, 2016. p. 94 Snowden told the Guardian he had no regrets: Ewen MacAskill and Alex Hern, “Edward Snowden: ‘The People Are Still Powerless, but Now They’re Aware,” Guardian, June 4, 2018. p. 95 John Oliver in Times Square: Adam Chandler, “What It
Surveillance Valley: The Rise of the Military-Digital Complex
by Yasha Levine · 6 Feb 2018 · 474pp · 130,575 words
2 Command, Control, and Counterinsurgency Chapter 3 Spying on Americans Part II: False Promises Chapter 4 Utopia and Privatization Chapter 5 Surveillance Inc. Chapter 6 Edward Snowden’s Arms Race Chapter 7 Internet Privacy, Funded by Spies Epilogue: Mauthausen, Austria Acknowledgments About the Author Notes Index To Nellie and Boris, my parents
…
ago, and uncovering the close ties that exist between US intelligence agencies and the antigovernment privacy movement that has sprung up in the wake of Edward Snowden’s leaks. Surveillance Valley shows that little has changed over the years: the Internet was developed as a weapon and remains a weapon today.
…
relevant in hindsight. It would take more than twenty years for the Internet to spread into most American homes, and four decades would pass before Edward Snowden’s leaks made the world aware of the massive amount of government surveillance happening over the Internet. Today, people still think that surveillance is
…
in a 1970s cybernetic utopia gone bad. It is also an accurate description of the world Google and the Internet have made today. Chapter 6 Edward Snowden’s Arms Race A specter is haunting the modern world, the specter of crypto anarchy. —Timothy C. May, The Crypto Anarchist Manifesto, 1988 In
…
gray shirt open at the collar sitting on a hotel room sofa—calm but looking like he hadn’t slept for days. His name was Edward Snowden—“Ed,” as he wanted people to call him. He was twenty-nine years old. His résumé was a veritable treasure trove of spook world
…
they also be used to fight terrorism, prevent crime, and keep the world safe? The answer is: Of course they can. By the time Edward Snowden appeared on the scene, police departments from San Francisco to Miami were using social media platforms to infiltrate and watch political groups and monitor protests
…
the eyes and ears of a vast interconnected early warning system predicting human behavior—and ultimately change the course of the future. By the time Edward Snowden blew the whistle on the NSA in the summer of 2013, at least a dozen publicly disclosed US government programs were leveraging open source
…
In the 2000s, as the Internet grew into a commercial telecommunications network, the NSA’s signals intelligence mission expanded as well. By the time Edward Snowden transferred to his last and final NSA contracting job at Booz Allen Hamilton in Hawaii in 2013, the agency had a bead on just about
…
NSA, the industry was somehow able to convince the world that it was different, that it somehow stood in opposition to traditional power. Then Edward Snowden screwed everything up. Public disclosure of the NSA’s PRISM program gave a glimpse into the symbiotic relationship between Silicon Valley and the US government
…
bloggers, academics, think tanks, Astroturf groups, lobbyists, and journalists sat at their keyboards, staring at their hands, waiting with bated breath for a backlash.39 Edward Snowden terrified the industry. Catapulted to the status of a cult hero, he now wielded massive influence. He could easily focus on Silicon Valley’s private
…
breed of whistle-blower,” wrote James Bamford.49 But for all the praise he received, this modern-day Daniel Ellsberg cut a peculiar political profile. Edward Snowden eventually escaped to Russia, the only country that could guarantee his safety from the long arm of the United States. There, while living under
…
in the liberatory promise of Tor and cryptography. In his public statements, Dread Pirate Roberts came off as a typical libertarian, not much different from Edward Snowden. He followed Austrian Economics, argued against environmental regulations and child labor laws, praised sweatshops, and mocked the need for minimum wage: “How about someone
…
it to avoid government surveillance and repression in countries like China and Iran. Leakers and whistle-blowers used the network, too. That’s where Edward Snowden came into the story: Tor’s ability to hide people from the prying eyes of the NSA was a key factor in his leaks; he
…
couldn’t have carried them out successfully without it. Snowden Tor Edward Snowden was a huge fan of the Tor Project. He, like the Dread Pirate Roberts, believed in the power of cryptography to liberate the Internet
…
s dark side. Its ability to protect child pornographers from accountability only proved its effectiveness, demonstrating that the technology really was the powerful privacy tool Edward Snowden claimed it to be. Tor was the Internet’s AK-47—a cheap, durable field weapon everyday people could use to overthrow America’s surveillance
…
was happening. My problems had begun when I started digging into the Tor Project. I investigated Tor’s central role in the privacy movement after Edward Snowden presented the project as a panacea to surveillance on the Internet. I wasn’t convinced, and it didn’t take long to find a
…
Tor’s puzzling government support, the leading lights of the privacy community answered it with attacks. Micah Lee, the former EFF technologist who helped Edward Snowden communicate securely with journalists and who now works at The Intercept, attacked me as a conspiracy theorist and accused me and my colleagues at Pando
…
low and tried to understand why my reporting elicited such a vicious and weird reaction from the privacy community. Military contractors hailed as privacy heroes? Edward Snowden promoting a Pentagon-funded tool as a solution to NSA surveillance? Google and Facebook backing privacy technology? And why were privacy activists so hostile to
…
cannon platform in the North Sea off England’s coast. Look that way and find Sarah Harrison, WikiLeaks member and Julian Assange confidante who helped Edward Snowden escape arrest in Hong Kong and find safety in Moscow. She’s laughing and having a good time. I wave as I pass her
…
developers and celebrity supporters talk about their fights against Internet surveillance. Last year, the stage featured Laura Poitras, the Academy Award–winning director of the Edward Snowden documentary, Citizen Four. In her speech, she held up Tor as a powerful antidote to America’s surveillance state. “When I was communicating with
…
laps it up. They love Jacob Appelbaum. Everyone at 32c3 loves Jacob Appelbaum. Appelbaum is the most storied member of the Tor Project. After Edward Snowden and Julian Assange, he is arguably the most famous personality in the Internet privacy movement. He is also the most outrageous. For five years he
…
Internet.103 Strangely enough, these efforts were about to get a major credibility boost from an unlikely source: an NSA contractor by the name of Edward Snowden. Strange Alliances The post-WikiLeaks years were good for the Tor Project. With the government contracts flowing, Roger Dingledine expanded the payroll, adding a
…
to vet the possible leaker and to make sure he really was the NSA technician he claimed to be. This source turned out to be Edward Snowden.108 From the start, the Tor Project stood at the center of Snowden’s story. The leaker’s endorsement and promotion introduced the project
…
a Hacker’s Medal of Valor. With Snowden’s backing, no one even thought to question Tor’s radical antigovernment bona fides. To some, Edward Snowden was a hero. To others, he was a traitor who deserved to be executed. Officials at the NSA claimed that he had caused irreparable harm
…
and every intelligence agency and contractor went on to invest in costly “insider threat” programs designed to spy on employees and make sure that another Edward Snowden would never pop up again. Some called for bringing him back in a black-ops kidnapping; others, like Donald Trump, called for him to
…
young adult science fiction author whose books about a totalitarian government’s surveillance were read and admired by Laura Poitras, Jacob Appelbaum, Roger Dingledine, and Edward Snowden.122 Doctorow was a huge personality in the crypto movement who could fill giant conference halls at privacy conferences. He publicly endorsed OTF’s Internet
…
. Fight for the Future, a Silicon Valley–funded privacy activist organization, described Signal and Tor as “NSA-proof” and urged people to use them. Edward Snowden was the combo’s biggest and most famous booster and repeatedly took to Twitter to tell his three million followers that he used Signal and
…
protect their users from government surveillance? Privacy activists working with Silicon Valley and the US government to fight government surveillance—and with the support of Edward Snowden himself? It is very hard to imagine that back in the 1960s student radicals at Harvard and MIT would have ever thought to partner
…
of government involvement in the privacy space sounds like something cooked up by a paranoiac. In any event, with support from someone as celebrated as Edward Snowden, few had any reason to question why apps like Signal and Tor existed, or what larger purpose they served. It was easier and simpler
…
people could come together to fund tools that countervailed the surveillance power of the state. That suited the sponsors of Internet Freedom just fine. After Edward Snowden, OTF was triumphant. It didn’t mention the leaker by name in its promotional materials, but it profited from the crypto culture he promoted
…
and appeared to be a place where organized criminals could hide in plain sight—until it wasn’t. In October 2013, four months after Edward Snowden came out of hiding and endorsed Tor, a twenty-nine-year-old native Texan by the name of Ross Ulbricht was arrested in a public
…
Ulbricht’s encrypted laptop showed that he believed he was fully protected by Tor. He believed in Tor’s claims that were backed up by Edward Snowden and promoted by Jacob Appelbaum. He believed that everything he did in the murkiness of the dark web would have no bearing on him
…
the clock if he is convicted for any of his murders for hire. The fall of Silk Road pricked Tor’s invincibility. Even as Edward Snowden and organizations like the Electronic Frontier Foundation promoted Tor as a powerful tool against the US surveillance state, that very surveillance state was poking Tor
…
Although demands like this make sense in a research context, they were baffling when applied to Tor. After all, Tor and its backers, including Edward Snowden, presented the project as a real-world anonymity tool that could resist the most powerful attackers. If it was so frail that it needed academic
…
What was going on? Why was the government working at cross-purposes? Did one part simply not know what the other was doing? Strangely enough, Edward Snowden’s NSA documents provided the beginnings of an answer. They showed that multiple NSA programs could punch through Tor’s defenses and possibly even uncloak
…
them. As for the other crypto tools financed by the US government? They suffered similar security and honeypot pitfalls. Take Signal, the encrypted app Edward Snowden said he used every day. Marketed as a secure communication tool for political activists, the app had strange features built in from the very beginning
…
.151 They also might work for someone with a high degree of technical savvy—say, a wily hacker like Julian Assange or a spy like Edward Snowden—who can use Signal and Tor combined with other techniques to effectively cover their tracks from the NSA. But, for the average user, these
…
a part of a geopolitical business strategy, a way of subtly pressuring countries that closed their networks and markets to Western technology companies. But after Edward Snowden’s revelations exposed the industry’s rampant private surveillance practices to the public, Internet Freedom offered another powerful benefit. For years, public opinion has been
…
politics to crypto apps—software made by the very same powerful entities that these apps are supposed to protect us from. In that sense, Edward Snowden is like the branded face of an Internet consumerism-as-rebellion lifestyle campaign, like the old Apple ad about shattering Big Brother or the Nike
…
the consequences,” the right-wing talk show personality (@glennbeck) tweeted on June 9, 2013, https://twitter.com/glennbeck/status/343816977929867265. 49. Bamford, “Edward Snowden: The Untold Story.” 50. Barton Gellman, “Edward Snowden, After Months of NSA Revelations, Says His Mission’s Accomplished,” Washington Post, December 23, 2013. 51. Scott Shane, “Documents on 2012 Drone
…
very people who would design the future features of the Internet—academics as well as employees of the most powerful tech companies in the world. “Edward Snowden at IETF93,” YouTube video, 56:01, posted by Dev Random, July 28, 2015, https://www.youtube.com/watch?v =0NvsUXBCeVA&feature=youtu.be. 65.
…
Glenn Greenwald, No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State (New York: Metropolitan Books, 2014), 24. 66. They posed for a photo at the thirtieth TED
…
to be “NSA-proof” and recommended that people use it every day. Laura Poitras, director of Citizen Four, the Academy Award–winning documentary on Edward Snowden, endorsed Tor as well. “When I was communicating with Snowden for several months before I met him in Hong Kong, we talked often about the
…
only tool to be able to do that,” she told an auditorium full of people at a hacker conference in Germany, a giant picture of Edward Snowden projected behind her on stage (Katina, “This Is What a Tor Supporter Looks Like: Laura Poitras,” Tor Project [blog], November 23, 2015, https://blog
…
reporter/. 76. Anonymous (@YourAnonNews), Twitter post, November 24, 2014, 11:19 am, https://surveillancevalley.com/content/citations/youranonnews-twitter-24-november-2014.png. 77. After Edward Snowden appeared on the scene in 2013, Fight for the Future launched several antisurveillance campaigns, including helping organize a big anti-NSA rally in Washington, DC
…
documentary film, May 2016. 108. “The NSA and Its Willing Helpers,” Spiegel Online, July 8, 2013, http://www.spiegel.de/international/world/interview-with-whistleblower-edward-snowden-on-global-spying-a-910006.html. 109. Patrick Howell O’Neill, “Tor Now Reaches 200,000 Users in Russia,” Daily Dot, June 18, 2014, https
…
accessing individuals’ cellphone data, 265–266 Amazon’s involvement with, 180 ARPA’s Command and Control, 50 covert communication, 224–225 cryptography technology, 38–39 Edward Snowden’s activities, 252–254 establishment and mandate of, 190–191 Google’s involvement with, 5 hacking and cracking Tor, 264–265 Patriot Act, 141–142
…
230 celebrating their anonymity and secrecy, 209–210 cracking the network, 263 cypherpunks, 203–204 Dread Pirate Roberts and Silk Road, 201–205, 260–262 Edward Snowden’s activities and, 206–211, 252–253 enhancing US government power, 223–224 government hacking and cracking, 263–264 government support for, 213–215 investigation
Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World
by Bruce Schneier · 2 Mar 2015 · 598pp · 134,339 words
activists, consumer advocates, and freethinkers. I focus mainly on the NSA, because this is the secret government agency we know best, because of the documents Edward Snowden released. Corporations and governments alike have an insatiable appetite for our data, and I discuss how the two work together in Chapter 6. I call
…
. We may not like to admit it, but we are under mass surveillance. Much of what we know about the NSA’s surveillance comes from Edward Snowden, although people both before and after him also leaked agency secrets. As an NSA contractor, Snowden collected tens of thousands of documents describing many of
…
on the US government, not because it’s the worst offender, but because we know something about its activities—mostly thanks to the actions of Edward Snowden. The US national security surveillance state is robust politically, legally, and technically. The documents from Snowden disclosed at least three different NSA programs to collect
…
small company, owned and operated by a programmer named Ladar Levison, and it was popular among the tech-savvy. It had half a million users, Edward Snowden amongst them. Soon after Snowden fled to Hong Kong in 2013, Levison received a National Security Letter demanding that the company turn over the master
…
was prosecuted in 2011, was forbidden to say the words “whistleblowing” and “overclassification” in his trial. Chelsea Manning was prohibited from using a similar defense. Edward Snowden claims he’s a whistleblower. Many people, including me, agree; others don’t. Secretary of State John Kerry insisted that Snowden should “come back here
…
business practices like tenant farming, child labor, and company stores. They’ll look immoral. The start of this movement, more than anything else, will be Edward Snowden’s legacy. I started this book by talking about data as exhaust: something we all produce as we go about our information-age business. I
…
each time. Beth Friedman, who has copyedited everything I have written for over a decade, continues to be irreplaceable. I would also like to thank Edward Snowden, whose courageous actions resulted in the global conversation we are now having about surveillance. It’s not an exaggeration to say that I would not
…
Greenwald, and Ryan Gallagher (30 Jan 2014), “CSEC used airport Wi-Fi to track Canadian travellers: Edward Snowden documents,” CBC News, http://www.cbc.ca/news/politics/csec-used-airport-wi-fi-to-track-canadian-travellers-edward-snowden-documents-1.2517881. display personal information: Alessandro Acquisti, Ralph Gross, and Fred Stutzman (4 Aug 2011
…
in quest for total surveillance,” Guardian, http://www.theguardian.com/world/2013/nov/02/nsa-portrait-total-surveillance. Glenn Greenwald (2014), No Place to Hide: Edward Snowden, the NSA and the US Surveillance State, Macmillan, chap. 3, http://leaksource.info/2014/07/31/glenn-greenwalds-no-place-to-hide-nsa-documents-excerpts
…
specialized software: The code names for these programs are even cooler. And, most interestingly, this top-secret NSA document seems not to have come from Edward Snowden. Leaksource (30 Dec 2013), “NSA’s ANT Division catalog of exploits for nearly every major software/hardware/firmware,” http://leaksource.info/2013/12/30/nsas
…
Not Take Place, Oxford University Press, http://thomasrid.org/no-cyber-war. nationwide Internet blackout: James Bamford (13 Aug 2014), “Edward Snowden: The untold story,” Wired, http://www.wired.com/2014/08/edward-snowden. 30 countries have cyberwar divisions: Even more have cyberwar capabilities. George Mason University School of Public Policy (Feb 2014), “Cyber
…
brutal state police,” Intercept, https://firstlook.org/theintercept/2014/07/25/nsas-new-partner-spying-saudi-arabias-brutal-state-police. this gives the NSA access: Edward Snowden (7 Mar 2014), “Statement to the European Parliament,” European Parliament, http://www.europarl.europa.eu/document/activities/cont/201403/20140307ATT80674/20140307ATT80674EN.pdf. the NSA spies
…
Internet against Democracy, New Press, p. 21, http://books.google.com/books/?id=j_7EkTI8kVQC. the NSA gets direct access: We knew this even before Edward Snowden, from the previous NSA whistleblower Mark Klein. Mark Klein (8 Jun 2006), “Declaration of Mark Klein,” Hepting, et al., v. AT&T, et al. , United
…
2013), “Lavabit e-mail service abruptly shut down citing government interference,” Guardian, http://www.theguardian.com/technology/2013/aug/08/lavabit-e-mail-shut-down-edward-snowden. Ladar Levison (20 May 2014), “Secrets, lies and Snowden’s email: Why I was forced to shut down Lavabit,” Guardian, http://www.theguardian.com/commentisfree
…
Manning was prohibited: David Dishneau (20 Jul 2012), “Manning largely barred from discussing WikiLeaks harm,” Associated Press, http://seattletimes.com/html/nationworld/2018724246_apusmanningwikileaks.html. Edward Snowden claims: The country is fairly evenly divided on this point. Seth Motel (15 Apr 2014), “NSA coverage wins Pulitzer, but Americans remain divided on Snowden
…
/15/nsa-coverage-wins-pulitzer-but-americans-remain-divided-on-snowden-leaks. John Kerry insisted that: Jonathan Topaz (28 May 2014), “John Kerry: Edward Snowden a ‘coward … traitor,’” Politico, http://www.politico.com/story/2014/05/edward-snowden-coward-john-kerry-msnbc-interview-nsa-107157.html. Hillary Clinton proclaimed: Phoebe Greenwood (4 Jul 2014
…
), “Edward Snowden should have right to legal defense in US, says Hillary Clinton,” Guardian, http://www.theguardian.com/world/2014/jul/04/edward-snowden-legal-defence-hillary-clinton-interview. Both comments are examples: Daniel Ellsberg (30 May 2014), “Snowden
…
/oct/04/tor-attacks-nsa-users-online-anonymity. “endpoint security is so terrifically weak”: Glenn Greenwald and Edward Snowden (17 Jun 2013), “Edward Snowden: NSA whistleblower answers reader questions,” Guardian, http://www.theguardian.com/world/2013/jun/17/edward-snowden-nsa-files-whistleblower. Discoverers can sell vulnerabilities: The ethics of this is discussed here. Serge Egelman
…
://papers.ssrn.com/sol3/papers.cfm?abstract_id=2028152. NSA regularly exploits: Lawrence Lessig (20 Oct 2014), “Institutional corruption and the NSA: Lawrence Lessig interviews Edward Snowden at Harvard Law,” LeakSourceInfo/YouTube, http://www.youtube.com/watch? v=DksIFG3Skb4. Bermuda phone system: Ryan Devereaux, Glenn Greenwald, and Laura Poitras (19 May 2014
…
/09/29/did-the-stuxnet-worm-kill-indias-insat-4b-satellite. Internet blackout in Syria: James Bamford (13 Aug 2014), “Edward Snowden: The untold story,” Wired, http://www.wired.com/2014/08/edward-snowden. a technique called DNS injection: Anonymous (Jul 2012), “The collateral damage of internet censorship by DNS injection,” ACM SIGCOMM Computer
…
state in the US and Europe,” Wake Forest Law Review (forthcoming), http://papers.ssrn.com/sol3/papers.cfm?abstract_id=2349269. Snowden was rebuffed repeatedly: Edward Snowden (7 Mar 2014), “Statement to European Parliament,” http://www.europarl.europa.eu/document/activities/cont/201403/20140307ATT80674/20140307ATT80674EN.pdf. Other law enforcement agencies: Merrick Bobb
…
. danah boyd (19 Jul 2013), “Whistleblowing is the new civil disobedience: Why Edward Snowden matters,” apophenia, http://www.zephoria.org/thoughts/archives/2013/07/19/edward-snowden-whistleblower.html. William E. Scheuerman (Sep 2014), “Whistleblowing as civil disobedience: The case of Edward Snowden,” Philosophy and Social Criticism 40, http://psc.sagepub.com/content/40/7/609
…
: Yochai Benkler makes the case that the smartest thing the US could do is to give Edward Snowden immunity and let him return to the US. Yochai Benkler (8 Sep 2014), “Want to reform the NSA? Give Edward Snowden immunity,” Atlantic, http://www.theatlantic.com/politics/archive/2014/09/want-to-reform-the-nsa
…
-give-edward-snowden-immunity/379612/2. We encourage individuals: US Department of Labor (2014), “The Whistleblower Protection Programs,” http://www
…
its European allies,” Guardian, http://www.theguardian.com/world/2013/jun/30/nsa-leaks-us-bugging-european-allies. Glenn Greenwald (2014), No Place to Hide: Edward Snowden, the NSA and the US Surveillance State, Macmillan, http://glenngreenwald.net. the NSA spied on the UN: Laura Poitras, Marcel Rosenbach, and Holger Stark (26
Orwell Versus the Terrorists: A Digital Short
by Jamie Bartlett · 12 Feb 2015 · 50pp · 15,603 words
The Hacker and the State: Cyber Attacks and the New Normal of Geopolitics
by Ben Buchanan · 25 Feb 2020 · 443pp · 116,832 words
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
by Kevin Mitnick, Mikko Hypponen and Robert Vamosi · 14 Feb 2017 · 305pp · 93,091 words
Bottoms Up and the Devil Laughs
by Kerry Howley · 21 Mar 2023
Breaking News: The Remaking of Journalism and Why It Matters Now
by Alan Rusbridger · 14 Oct 2018 · 579pp · 160,351 words
Cult of the Dead Cow: How the Original Hacking Supergroup Might Just Save the World
by Joseph Menn · 3 Jun 2019 · 302pp · 85,877 words

Fancy Bear Goes Phishing: The Dark History of the Information Age, in Five Extraordinary Hacks
by Scott J. Shapiro · 523pp · 154,042 words
Tools and Weapons: The Promise and the Peril of the Digital Age
by Brad Smith and Carol Ann Browne · 9 Sep 2019 · 482pp · 121,173 words
The System: Who Owns the Internet, and How It Owns Us
by James Ball · 19 Aug 2020 · 268pp · 76,702 words
Dragnet Nation: A Quest for Privacy, Security, and Freedom in a World of Relentless Surveillance
by Julia Angwin · 25 Feb 2014 · 422pp · 104,457 words
The View From Flyover Country: Dispatches From the Forgotten America
by Sarah Kendzior · 24 Apr 2015 · 172pp · 48,747 words
Future Crimes: Everything Is Connected, Everyone Is Vulnerable and What We Can Do About It
by Marc Goodman · 24 Feb 2015 · 677pp · 206,548 words
Messing With the Enemy: Surviving in a Social Media World of Hackers, Terrorists, Russians, and Fake News
by Clint Watts · 28 May 2018 · 324pp · 96,491 words
Dark Territory: The Secret History of Cyber War
by Fred Kaplan · 1 Mar 2016 · 383pp · 105,021 words
Dawn of the Code War: America's Battle Against Russia, China, and the Rising Global Cyber Threat
by John P. Carlin and Garrett M. Graff · 15 Oct 2018 · 568pp · 164,014 words
There's a War Going on but No One Can See It
by Huib Modderkolk · 1 Sep 2021 · 295pp · 84,843 words
The Wires of War: Technology and the Global Struggle for Power
by Jacob Helberg · 11 Oct 2021 · 521pp · 118,183 words
Homeland: The War on Terror in American Life
by Richard Beck · 2 Sep 2024 · 715pp · 212,449 words
Pegasus: How a Spy in Your Pocket Threatens the End of Privacy, Dignity, and Democracy
by Laurent Richard and Sandrine Rigaud · 17 Jan 2023 · 350pp · 115,802 words
My Glorious Defeats: Hacktivist, Narcissist, Anonymous: A Memoir
by Barrett Brown · 8 Jul 2024 · 332pp · 110,397 words
Habeas Data: Privacy vs. The Rise of Surveillance Tech
by Cyrus Farivar · 7 May 2018 · 397pp · 110,222 words
Can It Happen Here?: Authoritarianism in America
by Cass R. Sunstein · 6 Mar 2018 · 434pp · 117,327 words
How to Fix the Future: Staying Human in the Digital Age
by Andrew Keen · 1 Mar 2018 · 308pp · 85,880 words
I Hate the Internet: A Novel
by Jarett Kobek · 3 Nov 2016 · 302pp · 74,350 words
@War: The Rise of the Military-Internet Complex
by Shane Harris · 14 Sep 2014 · 340pp · 96,149 words
Free Speech: Ten Principles for a Connected World
by Timothy Garton Ash · 23 May 2016 · 743pp · 201,651 words
The Panama Papers: Breaking the Story of How the Rich and Powerful Hide Their Money
by Frederik Obermaier · 17 Jun 2016 · 372pp · 109,536 words
Hacker, Hoaxer, Whistleblower, Spy: The Story of Anonymous
by Gabriella Coleman · 4 Nov 2014 · 457pp · 126,996 words
Active Measures: The Secret History of Disinformation and Political Warfare
by Thomas Rid
Culture & Empire: Digital Revolution
by Pieter Hintjens · 11 Mar 2013 · 349pp · 114,038 words
Pay Any Price: Greed, Power, and Endless War
by James Risen · 15 Feb 2014 · 339pp · 99,674 words
Reset
by Ronald J. Deibert · 14 Aug 2020
Spies, Lies, and Algorithms: The History and Future of American Intelligence
by Amy B. Zegart · 6 Nov 2021
We Are Data: Algorithms and the Making of Our Digital Selves
by John Cheney-Lippold · 1 May 2017 · 420pp · 100,811 words
House of Huawei: The Secret History of China's Most Powerful Company
by Eva Dou · 14 Jan 2025 · 394pp · 110,159 words
Doing Time Like a Spy
by John Kiriakou · 11 May 2017 · 299pp · 96,608 words
Pax Technica: How the Internet of Things May Set Us Free or Lock Us Up
by Philip N. Howard · 27 Apr 2015 · 322pp · 84,752 words
Merchants of Truth: The Business of News and the Fight for Facts
by Jill Abramson · 5 Feb 2019 · 788pp · 223,004 words
Because We Say So
by Noam Chomsky
Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon
by Kim Zetter · 11 Nov 2014 · 492pp · 153,565 words
The Secret World: A History of Intelligence
by Christopher Andrew · 27 Jun 2018
Digital Empires: The Global Battle to Regulate Technology
by Anu Bradford · 25 Sep 2023 · 898pp · 236,779 words
Terms of Service: Social Media and the Price of Constant Connection
by Jacob Silverman · 17 Mar 2015 · 527pp · 147,690 words
New Dark Age: Technology and the End of the Future
by James Bridle · 18 Jun 2018 · 301pp · 85,263 words
Cybersecurity: What Everyone Needs to Know
by P. W. Singer and Allan Friedman · 3 Jan 2014 · 587pp · 117,894 words
The Black Box Society: The Secret Algorithms That Control Money and Information
by Frank Pasquale · 17 Nov 2014 · 320pp · 87,853 words
The World as It Is: A Memoir of the Obama White House
by Ben Rhodes · 4 Jun 2018 · 470pp · 148,444 words
System Error: Where Big Tech Went Wrong and How We Can Reboot
by Rob Reich, Mehran Sahami and Jeremy M. Weinstein · 6 Sep 2021
The New Map: Energy, Climate, and the Clash of Nations
by Daniel Yergin · 14 Sep 2020
Coders: The Making of a New Tribe and the Remaking of the World
by Clive Thompson · 26 Mar 2019 · 499pp · 144,278 words
Winners Take All: The Elite Charade of Changing the World
by Anand Giridharadas · 27 Aug 2018 · 296pp · 98,018 words
Click Here to Kill Everybody: Security and Survival in a Hyper-Connected World
by Bruce Schneier · 3 Sep 2018 · 448pp · 117,325 words
Liberalism at Large: The World According to the Economist
by Alex Zevin · 12 Nov 2019 · 767pp · 208,933 words
The Powerful and the Damned: Private Diaries in Turbulent Times
by Lionel Barber · 5 Nov 2020
Palo Alto: A History of California, Capitalism, and the World
by Malcolm Harris · 14 Feb 2023 · 864pp · 272,918 words
Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers
by Andy Greenberg · 5 Nov 2019 · 363pp · 105,039 words
The Laundromat : Inside the Panama Papers, Illicit Money Networks, and the Global Elite
by Jake Bernstein · 14 Oct 2019 · 470pp · 125,992 words
The Great Firewall of China
by James Griffiths; · 15 Jan 2018 · 453pp · 114,250 words
Artificial Whiteness
by Yarden Katz
Pandora's Box: How Guts, Guile, and Greed Upended TV
by Peter Biskind · 6 Nov 2023 · 543pp · 143,084 words
The Narrow Corridor: States, Societies, and the Fate of Liberty
by Daron Acemoglu and James A. Robinson · 23 Sep 2019 · 809pp · 237,921 words

News and How to Use It: What to Believe in a Fake News World
by Alan Rusbridger · 26 Nov 2020 · 371pp · 109,320 words
The Age of Entitlement: America Since the Sixties
by Christopher Caldwell · 21 Jan 2020 · 450pp · 113,173 words
The Dark Net
by Jamie Bartlett · 20 Aug 2014 · 267pp · 82,580 words
The Truth Machine: The Blockchain and the Future of Everything
by Paul Vigna and Michael J. Casey · 27 Feb 2018 · 348pp · 97,277 words
The Internet Is Not the Answer
by Andrew Keen · 5 Jan 2015 · 361pp · 81,068 words
Hit Refresh: The Quest to Rediscover Microsoft's Soul and Imagine a Better Future for Everyone
by Satya Nadella, Greg Shaw and Jill Tracie Nichols · 25 Sep 2017 · 391pp · 71,600 words
The Costs of Connection: How Data Is Colonizing Human Life and Appropriating It for Capitalism
by Nick Couldry and Ulises A. Mejias · 19 Aug 2019 · 458pp · 116,832 words
Disrupt and Deny: Spies, Special Forces, and the Secret Pursuit of British Foreign Policy
by Rory Cormac · 14 Jun 2018 · 407pp
The Seventh Sense: Power, Fortune, and Survival in the Age of Networks
by Joshua Cooper Ramo · 16 May 2016 · 326pp · 103,170 words

Likewar: The Weaponization of Social Media
by Peter Warren Singer and Emerson T. Brooking · 15 Mar 2018
Algorithms of Oppression: How Search Engines Reinforce Racism
by Safiya Umoja Noble · 8 Jan 2018 · 290pp · 73,000 words
Like, Comment, Subscribe: Inside YouTube's Chaotic Rise to World Domination
by Mark Bergen · 5 Sep 2022 · 642pp · 141,888 words
The Brussels Effect: How the European Union Rules the World
by Anu Bradford · 14 Sep 2020 · 696pp · 184,001 words
Listen, Liberal: Or, What Ever Happened to the Party of the People?
by Thomas Frank · 15 Mar 2016 · 316pp · 87,486 words
The Stack: On Software and Sovereignty
by Benjamin H. Bratton · 19 Feb 2016 · 903pp · 235,753 words
The Bitcoin Guidebook: How to Obtain, Invest, and Spend the World's First Decentralized Cryptocurrency
by Ian Demartino · 2 Feb 2016 · 296pp · 86,610 words
The Patient Will See You Now: The Future of Medicine Is in Your Hands
by Eric Topol · 6 Jan 2015 · 588pp · 131,025 words
The Smartphone Society
by Nicole Aschoff
Accessory to War: The Unspoken Alliance Between Astrophysics and the Military
by Neil Degrasse Tyson and Avis Lang · 10 Sep 2018 · 745pp · 207,187 words
Doppelganger: A Trip Into the Mirror World
by Naomi Klein · 11 Sep 2023
Blockchain Revolution: How the Technology Behind Bitcoin Is Changing Money, Business, and the World
by Don Tapscott and Alex Tapscott · 9 May 2016 · 515pp · 126,820 words
Disaster Capitalism: Making a Killing Out of Catastrophe
by Antony Loewenstein · 1 Sep 2015 · 464pp · 121,983 words
But What if We're Wrong? Thinking About the Present as if It Were the Past
by Chuck Klosterman · 6 Jun 2016 · 281pp · 78,317 words
Your Computer Is on Fire
by Thomas S. Mullaney, Benjamin Peters, Mar Hicks and Kavita Philip · 9 Mar 2021 · 661pp · 156,009 words
Blockchain: Blueprint for a New Economy
by Melanie Swan · 22 Jan 2014 · 271pp · 52,814 words
Unit X: How the Pentagon and Silicon Valley Are Transforming the Future of War
by Raj M. Shah and Christopher Kirchhoff · 8 Jul 2024 · 272pp · 103,638 words
The Profiteers
by Sally Denton · 556pp · 141,069 words
The People's Platform: Taking Back Power and Culture in the Digital Age
by Astra Taylor · 4 Mar 2014 · 283pp · 85,824 words
In Our Own Image: Savior or Destroyer? The History and Future of Artificial Intelligence
by George Zarkadakis · 7 Mar 2016 · 405pp · 117,219 words
Lurking: How a Person Became a User
by Joanne McNeil · 25 Feb 2020 · 239pp · 80,319 words
Power and Progress: Our Thousand-Year Struggle Over Technology and Prosperity
by Daron Acemoglu and Simon Johnson · 15 May 2023 · 619pp · 177,548 words
Big Data at Work: Dispelling the Myths, Uncovering the Opportunities
by Thomas H. Davenport · 4 Feb 2014
The Tyranny of Metrics
by Jerry Z. Muller · 23 Jan 2018 · 204pp · 53,261 words
The Fifth Domain: Defending Our Country, Our Companies, and Ourselves in the Age of Cyber Threats
by Richard A. Clarke and Robert K. Knake · 15 Jul 2019 · 409pp · 112,055 words
The Controlled Demolition of the American Empire
by Jeff Berwick and Charlie Robinson · 14 Apr 2020 · 491pp · 141,690 words
Beyond: Our Future in Space
by Chris Impey · 12 Apr 2015 · 370pp · 97,138 words
Move Fast and Break Things: How Facebook, Google, and Amazon Cornered Culture and Undermined Democracy
by Jonathan Taplin · 17 Apr 2017 · 222pp · 70,132 words
Dataclysm: Who We Are (When We Think No One's Looking)
by Christian Rudder · 8 Sep 2014 · 366pp · 76,476 words
The People vs Tech: How the Internet Is Killing Democracy (And How We Save It)
by Jamie Bartlett · 4 Apr 2018 · 170pp · 49,193 words
The Pay Off: How Changing the Way We Pay Changes Everything
by Gottfried Leibbrandt and Natasha de Teran · 14 Jul 2021 · 326pp · 91,532 words
How Democracy Ends
by David Runciman · 9 May 2018 · 245pp · 72,893 words
Scotland’s Jesus: The Only Officially Non-Racist Comedian
by Frankie Boyle · 23 Oct 2013
Rise and Kill First: The Secret History of Israel's Targeted Assassinations
by Ronen Bergman · 30 Jan 2018 · 1,071pp · 295,220 words
Team of Teams: New Rules of Engagement for a Complex World
by General Stanley McChrystal, Tantum Collins, David Silverman and Chris Fussell · 11 May 2015 · 409pp · 105,551 words
The Perfect Police State: An Undercover Odyssey Into China's Terrifying Surveillance Dystopia of the Future
by Geoffrey Cain · 28 Jun 2021 · 340pp · 90,674 words
Your Face Belongs to Us: A Secretive Startup's Quest to End Privacy as We Know It
by Kashmir Hill · 19 Sep 2023 · 487pp · 124,008 words
Blank Space: A Cultural History of the Twenty-First Century
by W. David Marx · 18 Nov 2025 · 642pp · 142,332 words
Dark Matters: On the Surveillance of Blackness
by Simone Browne · 1 Oct 2015 · 326pp · 84,180 words
The Death of Money: The Coming Collapse of the International Monetary System
by James Rickards · 7 Apr 2014 · 466pp · 127,728 words
The Great Delusion: Liberal Dreams and International Realities
by John J. Mearsheimer · 24 Sep 2018 · 443pp · 125,510 words
Basic Income: A Radical Proposal for a Free Society and a Sane Economy
by Philippe van Parijs and Yannick Vanderborght · 20 Mar 2017
Kill Chain: The Rise of the High-Tech Assassins
by Andrew Cockburn · 10 Mar 2015 · 389pp · 108,344 words
A Generation of Sociopaths: How the Baby Boomers Betrayed America
by Bruce Cannon Gibney · 7 Mar 2017 · 526pp · 160,601 words
Tracers in the Dark: The Global Hunt for the Crime Lords of Cryptocurrency
by Andy Greenberg · 15 Nov 2022 · 494pp · 121,217 words
Battle for the Bird: Jack Dorsey, Elon Musk, and the $44 Billion Fight for Twitter's Soul
by Kurt Wagner · 20 Feb 2024 · 332pp · 127,754 words

The Digital Party: Political Organisation and Online Democracy
by Paolo Gerbaudo · 19 Jul 2018 · 302pp · 84,881 words
Information Doesn't Want to Be Free: Laws for the Internet Age
by Cory Doctorow, Amanda Palmer and Neil Gaiman · 18 Nov 2014 · 170pp · 51,205 words
The Pentagon's Brain: An Uncensored History of DARPA, America's Top-Secret Military Research Agency
by Annie Jacobsen · 14 Sep 2015 · 558pp · 164,627 words
The Inevitable: Understanding the 12 Technological Forces That Will Shape Our Future
by Kevin Kelly · 6 Jun 2016 · 371pp · 108,317 words
The End of Policing
by Alex S. Vitale · 9 Oct 2017 · 318pp · 82,452 words
The WikiLeaks Files: The World According to US Empire
by Wikileaks · 24 Aug 2015 · 708pp · 176,708 words
Smart Cities, Digital Nations
by Caspar Herzberg · 13 Apr 2017
The Coming Wave: Technology, Power, and the Twenty-First Century's Greatest Dilemma
by Mustafa Suleyman · 4 Sep 2023 · 444pp · 117,770 words
Age of Discovery: Navigating the Risks and Rewards of Our New Renaissance
by Ian Goldin and Chris Kutarna · 23 May 2016 · 437pp · 113,173 words
Super Thinking: The Big Book of Mental Models
by Gabriel Weinberg and Lauren McCann · 17 Jun 2019
How Everything Became War and the Military Became Everything: Tales From the Pentagon
by Rosa Brooks · 8 Aug 2016 · 548pp · 147,919 words
The Internet of Us: Knowing More and Understanding Less in the Age of Big Data
by Michael P. Lynch · 21 Mar 2016 · 230pp · 61,702 words
Fire and Fury: Inside the Trump White House
by Michael Wolff · 5 Jan 2018 · 394pp · 112,770 words
America's Bitter Pill: Money, Politics, Backroom Deals, and the Fight to Fix Our Broken Healthcare System
by Steven Brill · 5 Jan 2015 · 554pp · 167,247 words
Everything for Everyone: The Radical Tradition That Is Shaping the Next Economy
by Nathan Schneider · 10 Sep 2018 · 326pp · 91,559 words
The Fourth Revolution: The Global Race to Reinvent the State
by John Micklethwait and Adrian Wooldridge · 14 May 2014 · 372pp · 92,477 words
Custodians of the Internet: Platforms, Content Moderation, and the Hidden Decisions That Shape Social Media
by Tarleton Gillespie · 25 Jun 2018 · 390pp · 109,519 words
Hiding in Plain Sight: The Invention of Donald Trump and the Erosion of America
by Sarah Kendzior · 6 Apr 2020
Dangerous Ideas: A Brief History of Censorship in the West, From the Ancients to Fake News
by Eric Berkowitz · 3 May 2021 · 412pp · 115,048 words
The Age of Surveillance Capitalism
by Shoshana Zuboff · 15 Jan 2019 · 918pp · 257,605 words
The Evolution of Everything: How New Ideas Emerge
by Matt Ridley · 395pp · 116,675 words
Rule Britannia: Brexit and the End of Empire
by Danny Dorling and Sally Tomlinson · 15 Jan 2019 · 502pp · 128,126 words
Collaborative Society
by Dariusz Jemielniak and Aleksandra Przegalinska · 18 Feb 2020 · 187pp · 50,083 words
The New Class War: Saving Democracy From the Metropolitan Elite
by Michael Lind · 20 Feb 2020
How Elites Ate the Social Justice Movement
by Fredrik Deboer · 4 Sep 2023 · 211pp · 78,547 words
Digital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires Trying to Reinvent Money
by Nathaniel Popper · 18 May 2015 · 387pp · 112,868 words
An Ugly Truth: Inside Facebook's Battle for Domination
by Sheera Frenkel and Cecilia Kang · 12 Jul 2021 · 372pp · 100,947 words
The Age of Cryptocurrency: How Bitcoin and Digital Money Are Challenging the Global Economic Order
by Paul Vigna and Michael J. Casey · 27 Jan 2015 · 457pp · 128,838 words
The Ethical Algorithm: The Science of Socially Aware Algorithm Design
by Michael Kearns and Aaron Roth · 3 Oct 2019
The Art of Gathering: How We Meet and Why It Matters
by Priya Parker · 14 May 2018 · 301pp · 90,362 words
Mastering Ethereum: Building Smart Contracts and DApps
by Andreas M. Antonopoulos and Gavin Wood Ph. D. · 23 Dec 2018 · 960pp · 125,049 words
Mindf*ck: Cambridge Analytica and the Plot to Break America
by Christopher Wylie · 8 Oct 2019
Deep Time Reckoning: How Future Thinking Can Help Earth Now
by Vincent Ialenti · 22 Sep 2020 · 224pp · 69,593 words
The City
by Tony Norfield · 352pp · 98,561 words
Exponential Organizations: Why New Organizations Are Ten Times Better, Faster, and Cheaper Than Yours (And What to Do About It)
by Salim Ismail and Yuri van Geest · 17 Oct 2014 · 292pp · 85,151 words
The Industries of the Future
by Alec Ross · 2 Feb 2016 · 364pp · 99,897 words
The Fourth Industrial Revolution
by Klaus Schwab · 11 Jan 2016 · 179pp · 43,441 words
Silk Road
by Eileen Ormsby · 1 Nov 2014 · 269pp · 79,285 words
Trumpocalypse: Restoring American Democracy
by David Frum · 25 May 2020 · 319pp · 75,257 words
Careless People: A Cautionary Tale of Power, Greed, and Lost Idealism
by Sarah Wynn-Williams · 11 Mar 2025 · 370pp · 115,318 words
Four Futures: Life After Capitalism
by Peter Frase · 10 Mar 2015 · 121pp · 36,908 words
Crashed: How a Decade of Financial Crises Changed the World
by Adam Tooze · 31 Jul 2018 · 1,066pp · 273,703 words
The Extreme Centre: A Warning
by Tariq Ali · 22 Jan 2015 · 160pp · 46,449 words
Chinese Spies: From Chairman Mao to Xi Jinping
by Roger Faligot · 30 Jun 2019 · 615pp · 187,426 words
A World in Disarray: American Foreign Policy and the Crisis of the Old Order
by Richard Haass · 10 Jan 2017 · 286pp · 82,970 words
Facebook: The Inside Story
by Steven Levy · 25 Feb 2020 · 706pp · 202,591 words
Machines of Loving Grace: The Quest for Common Ground Between Humans and Robots
by John Markoff · 24 Aug 2015 · 413pp · 119,587 words
The Euro and the Battle of Ideas
by Markus K. Brunnermeier, Harold James and Jean-Pierre Landau · 3 Aug 2016 · 586pp · 160,321 words
The Curse of Cash
by Kenneth S Rogoff · 29 Aug 2016 · 361pp · 97,787 words
Grave New World: The End of Globalization, the Return of History
by Stephen D. King · 22 May 2017 · 354pp · 92,470 words
World Without Mind: The Existential Threat of Big Tech
by Franklin Foer · 31 Aug 2017 · 281pp · 71,242 words
Internet for the People: The Fight for Our Digital Future
by Ben Tarnoff · 13 Jun 2022 · 234pp · 67,589 words
Character Limit: How Elon Musk Destroyed Twitter
by Kate Conger and Ryan Mac · 17 Sep 2024
Paper: A World History
by Mark Kurlansky · 3 Apr 2016 · 485pp · 126,597 words
Nine Pints: A Journey Through the Money, Medicine, and Mysteries of Blood
by Rose George · 22 Oct 2018 · 453pp · 130,632 words
Falter: Has the Human Game Begun to Play Itself Out?
by Bill McKibben · 15 Apr 2019
Age of Anger: A History of the Present
by Pankaj Mishra · 26 Jan 2017 · 410pp · 106,931 words
People, Power, and Profits: Progressive Capitalism for an Age of Discontent
by Joseph E. Stiglitz · 22 Apr 2019 · 462pp · 129,022 words
The Cosmopolites: The Coming of the Global Citizen
by Atossa Araxia Abrahamian · 14 Jul 2015 · 138pp · 41,353 words
Connectography: Mapping the Future of Global Civilization
by Parag Khanna · 18 Apr 2016 · 497pp · 144,283 words
The Woman Who Smashed Codes: A True Story of Love, Spies, and the Unlikely Heroine Who Outwitted America's Enemies
by Jason Fagone · 25 Sep 2017 · 592pp · 152,445 words
If Mayors Ruled the World: Dysfunctional Nations, Rising Cities
by Benjamin R. Barber · 5 Nov 2013 · 501pp · 145,943 words
Vertical: The City From Satellites to Bunkers
by Stephen Graham · 8 Nov 2016 · 519pp · 136,708 words
The Enemy Within
by Seumas Milne · 1 Dec 1994 · 497pp · 161,742 words
The Alps: A Human History From Hannibal to Heidi and Beyond
by Stephen O'Shea · 21 Feb 2017 · 322pp · 92,769 words
Who Rules the World?
by Noam Chomsky
Behave: The Biology of Humans at Our Best and Worst
by Robert M. Sapolsky · 1 May 2017 · 1,261pp · 294,715 words
Open Standards and the Digital Age: History, Ideology, and Networks (Cambridge Studies in the Emergence of Global Enterprise)
by Andrew L. Russell · 27 Apr 2014 · 675pp · 141,667 words
Giving the Devil His Due: Reflections of a Scientific Humanist
by Michael Shermer · 8 Apr 2020 · 677pp · 121,255 words
The Myth of Capitalism: Monopolies and the Death of Competition
by Jonathan Tepper · 20 Nov 2018 · 417pp · 97,577 words
Future Politics: Living Together in a World Transformed by Tech
by Jamie Susskind · 3 Sep 2018 · 533pp
The Riders Come Out at Night: Brutality, Corruption, and Cover-Up in Oakland
by Ali Winston and Darwin Bondgraham · 10 Jan 2023 · 498pp · 184,761 words
Political Order and Political Decay: From the Industrial Revolution to the Globalization of Democracy
by Francis Fukuyama · 29 Sep 2014 · 828pp · 232,188 words
Chokepoints: American Power in the Age of Economic Warfare
by Edward Fishman · 25 Feb 2025 · 884pp · 221,861 words
Extremely Hardcore: Inside Elon Musk's Twitter
by Zoë Schiffer · 13 Feb 2024 · 343pp · 92,693 words
The Everything Blueprint: The Microchip Design That Changed the World
by James Ashton · 11 May 2023 · 401pp · 113,586 words
Generations: The Real Differences Between Gen Z, Millennials, Gen X, Boomers, and Silents—and What They Mean for America's Future
by Jean M. Twenge · 25 Apr 2023 · 541pp · 173,676 words
The Targeter: My Life in the CIA, Hunting Terrorists and Challenging the White House
by Nada Bakos · 3 Jun 2019
Bit Rot
by Douglas Coupland · 4 Oct 2016
Small Data: The Tiny Clues That Uncover Huge Trends
by Martin Lindstrom · 23 Feb 2016 · 295pp · 89,430 words
The Business Blockchain: Promise, Practice, and Application of the Next Internet Technology
by William Mougayar · 25 Apr 2016 · 161pp · 44,488 words
American Kingpin: The Epic Hunt for the Criminal Mastermind Behind the Silk Road
by Nick Bilton · 15 Mar 2017 · 349pp · 109,304 words
Copenhagenize: The Definitive Guide to Global Bicycle Urbanism
by Mikael Colville-Andersen · 28 Mar 2018 · 293pp · 90,714 words
Burning Down the Haus: Punk Rock, Revolution, and the Fall of the Berlin Wall
by Tim Mohr · 10 Sep 2018 · 370pp · 107,791 words
Building Microservices
by Sam Newman · 25 Dec 2014 · 540pp · 103,101 words
Building Secure and Reliable Systems: Best Practices for Designing, Implementing, and Maintaining Systems
by Heather Adkins, Betsy Beyer, Paul Blankinship, Ana Oprea, Piotr Lewandowski and Adam Stubblefield · 29 Mar 2020 · 1,380pp · 190,710 words
The Hostage's Daughter
by Sulome Anderson · 24 Aug 2016 · 269pp · 83,959 words
Don't Trust, Don't Fear, Don't Beg: The Extraordinary Story of the Arctic 30
by Ben Stewart · 4 May 2015 · 347pp · 94,701 words
After the Fall: Being American in the World We've Made
by Ben Rhodes · 1 Jun 2021 · 342pp · 114,118 words
The Cryptopians: Idealism, Greed, Lies, and the Making of the First Big Cryptocurrency Craze
by Laura Shin · 22 Feb 2022 · 506pp · 151,753 words
The Mysterious Mr. Nakamoto: A Fifteen-Year Quest to Unmask the Secret Genius Behind Crypto
by Benjamin Wallace · 18 Mar 2025 · 431pp · 116,274 words
Radicalized
by Cory Doctorow · 19 Mar 2019 · 444pp · 84,486 words
Targeted: The Cambridge Analytica Whistleblower's Inside Story of How Big Data, Trump, and Facebook Broke Democracy and How It Can Happen Again
by Brittany Kaiser · 21 Oct 2019 · 391pp · 123,597 words
The One Device: The Secret History of the iPhone
by Brian Merchant · 19 Jun 2017 · 416pp · 129,308 words
The Divide: American Injustice in the Age of the Wealth Gap
by Matt Taibbi · 8 Apr 2014 · 455pp · 138,716 words
To Be a Machine: Adventures Among Cyborgs, Utopians, Hackers, and the Futurists Solving the Modest Problem of Death
by Mark O'Connell · 28 Feb 2017 · 252pp · 79,452 words
Rebooting India: Realizing a Billion Aspirations
by Nandan Nilekani · 4 Feb 2016 · 332pp · 100,601 words
Age of Context: Mobile, Sensors, Data and the Future of Privacy
by Robert Scoble and Shel Israel · 4 Sep 2013 · 202pp · 59,883 words
This Is Not Normal: The Collapse of Liberal Britain
by William Davies · 28 Sep 2020 · 210pp · 65,833 words

The Disappearing Act
by Florence de Changy · 24 Dec 2020
Vassal State
by Angus Hanton · 25 Mar 2024 · 277pp · 81,718 words
Designing Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable Systems
by Martin Kleppmann · 16 Mar 2017 · 1,237pp · 227,370 words
McMindfulness: How Mindfulness Became the New Capitalist Spirituality
by Ronald Purser · 8 Jul 2019 · 242pp · 67,233 words
The Second Curve: Thoughts on Reinventing Society
by Charles Handy · 12 Mar 2015 · 164pp · 57,068 words
Designing Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable Systems
by Martin Kleppmann · 17 Apr 2017
Twitter and Tear Gas: The Power and Fragility of Networked Protest
by Zeynep Tufekci · 14 May 2017 · 444pp · 130,646 words
Doing Data Science: Straight Talk From the Frontline
by Cathy O'Neil and Rachel Schutt · 8 Oct 2013 · 523pp · 112,185 words
After Steve: How Apple Became a Trillion-Dollar Company and Lost Its Soul
by Tripp Mickle · 2 May 2022 · 535pp · 149,752 words
The Dark Cloud: How the Digital World Is Costing the Earth
by Guillaume Pitron · 14 Jun 2023 · 271pp · 79,355 words
Intertwingled: The Work and Influence of Ted Nelson (History of Computing)
by Douglas R. Dechow · 2 Jul 2015 · 223pp · 52,808 words
No Is Not Enough: Resisting Trump’s Shock Politics and Winning the World We Need
by Naomi Klein · 12 Jun 2017 · 357pp · 94,852 words
American Girls: Social Media and the Secret Lives of Teenagers
by Nancy Jo Sales · 23 Feb 2016 · 487pp · 147,238 words
You Are Here: From the Compass to GPS, the History and Future of How We Find Ourselves
by Hiawatha Bray · 31 Mar 2014 · 316pp · 90,165 words
The Establishment: And How They Get Away With It
by Owen Jones · 3 Sep 2014 · 388pp · 125,472 words

The End of Ownership: Personal Property in the Digital Economy
by Aaron Perzanowski and Jason Schultz · 4 Nov 2016 · 374pp · 97,288 words
Licence to be Bad
by Jonathan Aldred · 5 Jun 2019 · 453pp · 111,010 words
Gilded Rage: Elon Musk and the Radicalization of Silicon Valley
by Jacob Silverman · 9 Oct 2025 · 312pp · 103,645 words
Data-Ism: The Revolution Transforming Decision Making, Consumer Behavior, and Almost Everything Else
by Steve Lohr · 10 Mar 2015 · 239pp · 70,206 words
Whiplash: How to Survive Our Faster Future
by Joi Ito and Jeff Howe · 6 Dec 2016 · 254pp · 76,064 words
Don't Be Evil: How Big Tech Betrayed Its Founding Principles--And All of US
by Rana Foroohar · 5 Nov 2019 · 380pp · 109,724 words
The Hype Machine: How Social Media Disrupts Our Elections, Our Economy, and Our Health--And How We Must Adapt
by Sinan Aral · 14 Sep 2020 · 475pp · 134,707 words
Rogue States
by Noam Chomsky · 9 Jul 2015
Fantasyland: How America Went Haywire: A 500-Year History
by Kurt Andersen · 4 Sep 2017 · 522pp · 162,310 words
The Code: Silicon Valley and the Remaking of America
by Margaret O'Mara · 8 Jul 2019
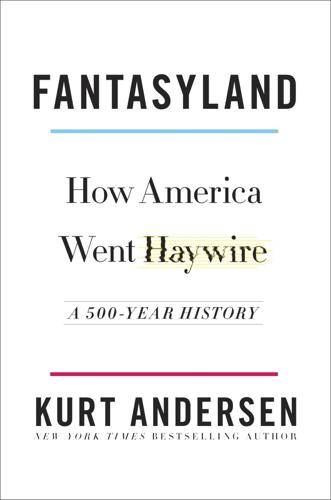
Fantasyland
by Kurt Andersen · 5 Sep 2017