Firefox
description: a free and open-source web browser developed by Mozilla
303 results
The Book of CSS3
by Peter Gasston · 14 Apr 2011 · 502pp · 82,170 words
the browsers have decided to implement it to see how it works. In this case, you would use the following code: E { -moz-monkeys: value ; /* Firefox */ -ms-monkeys: value ; /* Internet Explorer */ -o-monkeys: value ; /* Opera */ -webkit-monkeys: value; /* WebKit */ } The amount of repetition may seem somewhat unnecessary, but the repetition
…
Quite often people will suggest that when using prefixed, experimental CSS properties, you also add the unprefixed property at the end: E { -moz-monkeys: value; /* Firefox */ -ms-monkeys: value; /* Internet Explorer */ -o-monkeys: value; /* Opera */ -webkit-monkeys: value; /* WebKit */ monkeys: value; } The theory is that this future-proofs the code;
…
-class selectors, but with IE9 promising to rectify this, I think the new selectors will shortly prove worthwhile. DOM and Attribute Selectors: Browser Support WebKit Firefox Opera IE Structural pseudo-classes Yes Yes Yes No (expected in IE9) :target Yes Yes Yes No (expected in IE9) :empty Yes Yes Yes
…
you’d use this combination: E { text-wrap: suppress; word-wrap: break-word; } As of this writing, text-wrap remains unimplemented. Setting Text Rendering Options Firefox and WebKit browsers support a property called text-rendering, which allows developers to control the optimization of speed or legibility. This new feature means the
…
incorrectly, however, and instead creates five columns of 100px each, leaving empty white space, as shown in Figure 7-8. The first example shows Firefox’s correct interpretation of the spec; the second example shows WebKit’s incorrect interpretation. As these properties use proprietary prefixes, however, there is an opportunity
…
for this inconsistency to be corrected before the final implementation of the nonprefixed properties. Figure 7-8. How Firefox (top) and WebKit (bottom) interpret combined column properties If you want to use these two properties together, a shorthand property is available: E { columns:
…
to introduce ways you can improve the overall visual presentation of your websites, starting with new background and border effects. Multiple Columns: Browser Support WebKit Firefox Opera IE column-count Yes (with prefix) Yes (with prefix) No No column-width Yes (with prefix) Yes (with prefix) No No column-gap
…
border image is by Flickr user SkeletalMess (http://www.flickr.com/photos/skeletalmess/4396262635/) and is published under a Creative Commons Attribution license. Multicolored Borders Firefox has a series of proprietary properties that let you define multiple colors on a border. The syntax is very similar (one letter different!) to
…
, white, black); } div { background-image: -moz-linear-gradient(-90deg, white, black); } Linear Gradients in WebKit WebKit’s implementation is pretty similar to that of Firefox’s, although angle values are not permitted, and the syntax is somewhat more precise and verbose: E { background-image: -webkit-gradient(type, start-point, end
…
any gradual change between the two colors, creating the hard diagonal lines you see here. Repeating Radial Gradients Accompanying the -moz-radial-gradient function in Firefox is -moz-repeating-radial-gradient, which repeats the values supplied until its specified limit is reached. It works in the same way as -moz-
…
page elements, I’m going to move on to cover a whole new field of expertise: transforming and animating page elements. Gradients: Browser Support WebKit Firefox Opera IE Gradients Yes (with prefix; incorrect syntax) Yes (with prefix) No No Repeating Gradients No Yes (with prefix) No No Chapter 12. 2D
…
, each with its proprietary prefix, which means that to use this property currently, you have to specify it four times: E { -moz-transform: function(value); /* Firefox */ -ms-transform: function(value); /* Internet Explorer */ -o-transform: function(value); /* Opera */ -webkit-transform: function(value); /* WebKit */ } Ordinarily, I would recommend adding the nonprefixed property
…
of the browser-specific ones, so future browser version releases that implement the nonprefixed property are accounted for, like so: E { -moz-transform: function(value); /* Firefox */ -ms-transform: function(value); /* Internet Explorer */ -o-transform: function(value); /* Opera */ -webkit-transform: function(value); /* WebKit */ transform: function(value); /* Future-proofing */ } Some browsers, however,
…
one—I’m going to show how you can introduce subtle (or not so subtle) animation effects, without using JavaScript. 2D Transformations: Browser Support WebKit Firefox Opera IE 2D Transformations Yes (with prefix) Yes (with prefix) Yes (with prefix) No (expected in IE9, with prefix) box-reflect Yes (with prefix)
…
those browsers I had available to me when I began writing this book were: WebKit Safari 4.04 and Chrome 6.0 Firefox Firefox 3.6 and Beta releases of Firefox 4.0 Opera Opera 10.5 Internet Explorer Internet Explorer 8 During the period I was writing this book, Safari 5, Opera
…
Yes Yes Yes No (expected in IE9) currentColor Value Yes Yes Yes No (expected in IE9) appearance Yes Yes No No Gradients (Chapter 11) WebKit Firefox Opera IE Gradients Yes (with prefix; incorrect syntax; correct syntax in future versions) Yes (with prefix) No No Repeating Gradients No Yes (with prefix)
…
No No 2D Transformations (Chapter 12) WebKit Firefox Opera IE 2D Transformations Yes (with prefix) Yes (with prefix) Yes (with prefix) No (expected in IE9 with prefix) box-reflect Yes (with prefix)
…
CSS reference, which lists all of the supported properties, including those with a -webkit- prefix: http://developer.apple.com/safari/library/documentation/AppleApplications/Reference/SafariCSSRef/ Firefox Firefox bucks the open source documentation trend I just mentioned with their fantastic CSS reference on their excellent Mozilla Developer Network. This site explains all of
…
Multiple Columns, Combining column-count and column-width, Multiple Background Images, Background Clip and Origin, Image Masks, border-radius Shorthand, Gradients, Linear Gradients in Firefox, Radial Gradients in Firefox, Using Radial Gradients, 2D Transformations, Transforming Elements with Matrices, Transforming Elements with Matrices, Transitions and Animations, Triggers, Key Frames, 3D Transformations, Flexible Box
…
Layout, The box Value in Firefox, Cross-Browser Flex Box with JavaScript, CSS Modules and 3D transformations, 3D Transformations and animations, Triggers, Key Frames and background-clip property, Background Clip and
…
chaining queries, Pixel Ratio for Media Query, Syntax Android devices, device-width for, Device Width and Height angle argument, for linear gradient, Linear Gradients in Firefox Animations Module, Transitions and Animations, Triggers, More Complex Animations, Key Frames, Animation Properties, Name, Name, Name, Delay, Delay, Shorthand, Shorthand, The Complete Animations Example,
…
Shadows ` (backtick character), for constants, Constants and Variables backtick character (`), for constants, Constants and Variables balance keyword, for column-fill property, Different Distribution Methods in Firefox and WebKit bandwidth allowances, background image and, Using Media Queries in the Real World baseline keyword, for box-align property, Alignment Basic User Interface Module
…
Alignment, Same-Axis Alignment box-direction property, Changing Orientation, Cross-Browser Flex Box with JavaScript box-flex property, Making the Boxes Flexible, Zero Values and Firefox Layouts, Cross-Browser Flex Box with JavaScript box-flex-group property, Grouping Flexible Boxes box-lines property, Same-Axis Alignment box-ordinal-group property, Reversing
…
Using Linear Gradients, Using Linear Gradients adding to linear gradient, Using Linear Gradients in gradient, Gradients color-stop() function, Using Linear Gradients, Radial Gradients in Firefox, Multiple color-stop Values for radial gradients, Multiple color-stop Values for WebKit, Using Linear Gradients column-count property, Multiple Columns, Different Distribution Methods in
…
-rule-width property, Column Gaps and Rules column-span element, Containing Elements within Columns column-width property, Prescriptive Columns: column-count, Different Distribution Methods in Firefox and WebKit columns, Multiple Columns, Multiple Columns, Prescriptive Columns: column-count, A Note on Readability, A Note on Readability, Combining column-count and column
…
Columns gaps and rules, Combining column-count and column-width layout methods, Multiple Columns, Prescriptive Columns: column-count, A Note on Readability distribution differences in Firefox and WebKit, A Note on Readability dynamic columns, Prescriptive Columns: column-count lines between, Column Gaps and Rules readability, A Note on Readability setting
…
attribute, of textarea element, not disabled pseudo-class selector, not disabling kerning, OpenType Features discretionary ligatures, OpenType Features display property, The box Value in Firefox, Cross-Browser Flex Box with JavaScript, Using position and display to Create Rows, Using position and display to Create Rows, Setting Height and Width on
…
within Columns total width calculation, Module Status and the Recommendation Process transformed, position in document flow, rotate ellipse keyword, for radial gradient, Radial Gradients in Firefox ellipsis keyword, for text-overflow property, Restricting Overflow Embeddable Open Type (EOT) font format, A “Bulletproof” @font-face Syntax empty pseudo-class, empty, Summary
…
A Note on Readability, Multiple Background Images, border-radius Shorthand, 2D Transformations, 2D Transformations, Flexible Box Layout, Triggering the Flexible Box Layout, Zero Values and Firefox Layouts, Grouping Flexible Boxes, Same-Axis Alignment, Calculation Functions, Grouping Selectors, CSS Modules 2D Transformations Module, 2D Transformations algorithms for column calculations, A Note on
…
Grouping Selector, Grouping Selectors support. See browser support, Applying Dimensional Effects: text-shadow web resources, CSS Modules zero values and layouts, Zero Values and Firefox Layouts first-of-type pseudo-class, first-of-type, last-child, and last-of-type fit-content keyword, for column widths, Setting Height and Width
…
Flex Box with JavaScript Flexible Box Layout Module, Flexible Box Layout, Flexible Box Layout, Making the Boxes Flexible, Making the Boxes Flexible, Zero Values and Firefox Layouts, Grouping Flexible Boxes, Grouping Flexible Boxes, Changing Orientation, Reversing the Order, Alignment, Alignment, Same-Axis Alignment, Same-Axis Alignment, Stop the Presses: New
…
Alignment new syntax, Stop the Presses: New Syntax same-axis alignment, Alignment unequal ratios, Making the Boxes Flexible zero values and layouts, Zero Values and Firefox Layouts flipping elements, scale float property, Extended Floats font faces, The @font-face Rule, The @font-face Rule, True vs. Artificial Font Faces defining
…
States cross-browser styling of, UI Element States states, UI Element States fraction unit, Implicit and Explicit Grids from() function, Linear Gradients in Firefox, Radial Gradients in Firefox from-stop, in gradient, Gradients G Gecko, Mozilla-Specific Media Features General Sibling Combinator, The General Sibling Combinator Gentium Basic font, True vs
…
an Axis, Rotation Around an Axis element along axis, Rotation Around an Axis elements from default position, translate properties between states, Transitions and Animations Mozilla Firefox. See Firefox, Let’s Get Started: Introducing the Syntax, CSS Modules Mozilla, and Web Open Font Format (WOFF), Using Local Fonts Multi-column Layout Module, Multiple
…
repeat property, background-repeat repeat-y keyword, for background-repeat property, background-repeat repeating gradients, Multiple Gradients, Summary, Gradients: Browser Support browser support, Summary in Firefox, Multiple Gradients resize property, Restricting Overflow, Summary browser support, Summary reusable code, Extending Variables Using Mixins reverse keyword, for box-direction property, Changing Orientation reverse
…
Borders for text, Text Effects and Typographic Styles, Understanding Axes and Coordinates, Multiple Shadows multiple, Multiple Shadows shape argument, for radial gradient, Radial Gradients in Firefox Simple Attribute Selector, Attribute Selectors sine function, Transforming Elements with Matrices single keyword, for box-lines property, Same-Axis Alignment size of elements, Restricting Overflow
…
three-dimensional. See 3D elements; 3D transformations, background-repeat tiling images, background-repeat time requirement for transition, Property to() function, Linear Gradients in Firefox, Radial Gradients in Firefox to-stop, in gradient, Gradients top keyword, Giving Your Borders Rounded Corners, Giving Your Borders Rounded Corners, Perspective for border-radius property, Giving
…
Queries, UI Element States, The @font-face Rule, Licensing Fonts for Web Use, font-size-adjust, font-stretch, OpenType Features, background-repeat, Linear Gradients in Firefox, Summary, Transforming Elements with Matrices, Transforming Elements with Matrices, Property, The Cubic Bézier Curve, 3D Transformations, 3D Transformations, 3D Elements in CSS, Rotation Around
…
an Axis, Scaling, Zero Values and Firefox Layouts, Cross-Browser Flex Box with JavaScript, Cross-Browser Flex Box with JavaScript, Cross-Browser Flex Box with JavaScript, Template Layout, Default Content: The @ Sign
…
font-stretch Media Queries gallery, The Advantages of Media Queries on 3D matrix, Scaling on 3D transforms, 3D Transformations on angle argument, Linear Gradients in Firefox on Cartesian coordinate system, 3D Transformations on cubic Bézier curves, The Cubic Bézier Curve on direction vector calculation, Rotation Around an Axis on flexible box
…
Features on Grid Positioning Module, Cycle on image sprites, background-repeat on matrices, Transforming Elements with Matrices on Quirks Mode box model, Zero Values and Firefox Layouts on Template Layout Module, Template Layout, Default Content: The @ Sign on transitions, Property trigonometric functions, Transforming Elements with Matrices web fonts, CSS3 Gradient
JavaScript Cookbook
by Shelley Powers · 23 Jul 2010 · 1,038pp · 137,468 words
the String replace method to trim the unwanted whitespace from around a string. Now, trimming a string is as simple as calling the trim method. Firefox already supported a trim method, but its use was nonstandard before ECMAScript 5. Most, if not all, browsers will eventually support trim. Among the target
…
. In addition, there is no left or right trim in ECMAScript 5, though there are nonstandard versions of these methods in some browsers, such as Firefox. So if you want left- or right-only trim, you’ll want to create your own functions: function leftTrim(str) { return str.replace(/^\s+/,""); }function
…
is a new method, toISOString: var dt = "October 15, 2009 15:10:10"; alert(dt.toISOString()); Currently only a few browsers support this new functionality (Firefox 3.5 and the WebKit nightly). Until there is broader support, you’ll still need the functionality outlined in the solution to output the correctly
…
value with the replacement string, **. Don’t return a value from the function passed to the forEach method, as the value will be discarded. Chrome, Firefox, Opera, and Safari support forEach, but IE8 does not. 82 | Chapter 5: Working with Arrays and Loops See Also The concept of callback functions is
…
authors wouldn’t need these events, anyway. There are also events associated with the increasingly popular mobile and other hand- held computing environments. For instance, Firefox has a nonstandard set of events having to do with touch swiping, which Mozilla calls the mouse gesture events. It’s interesting, but use with
…
ASCII numeric code). Cross- browser functionality is used to access this value: IE and Opera do not support char Code, but do support keyCode; Safari, Firefox, and Chrome support charCode. Not listed in the possible keyboard events is the textInput event, which is part of the new DOM Level 3 event
…
specification, drag-and-drop has been implemented natively, though Opera doesn’t currently support drag-and-drop and it can be a bit tricky in Firefox, Chrome, Safari, and IE8. The example does not work with IE7, either. Currently, implementations of HTML5 drag-and-drop are not robust or consistent. Use
…
element (accessible via target, which has the element context). You can specify the element directly, but this is a more complex operation. For instance, in Firefox, I could try the following, which is derived from the Mozilla documentation: evt.dataTransfer.setData("application/x-moz-node",target); and then try to process
…
); } else if (eventObj.attachEvent) { event = "on" + event; eventObj.attachEvent(event, eventHandler); } else { eventObj["on" + event] = eventHandler; } } You can access the element context with this for Firefox, Opera, Chrome, Safari, but not for IE8. For IE8, you’ll have to access the element using the event object: function handleClick(evt) { // cross browser
…
, the program control then skips to the first statement that follows the exception handling statements. 182 | Chapter 10: Debugging and Error Handling Figure 10-3. Firefox console error when accessing a nonexistent function You can also use an optional finally statement with code that you want to process regardless of the
…
comes with useful information. In the solution, the error message is accessed and printed out to an alert message box. Peering into the exception in Firefox, we find the following properties: fileName Name of file where exception occurred lineNumber Number of the line where exception occurred message The exception message name
…
The name of the exception (i.e., ReferenceError) stack A stack trace of the exception The fileName, lineNumber, and stack are nonstandard Firefox extensions and aren’t guaranteed to exist between browsers. The message and error name are standard, and should always be available if the application or
…
and give it a name of test, use the following: console.profile('test'); When you want to finish the profile, use: console.profileEnd(); 10.8 Firefox and the Console | 191 Figure 10-11. The Firebug Console, including command line Figure 10-12. Using the Firebug Console command line 192 | Chapter 10
…
JavaScript The JavaScript profile functionality provides information about where your application is spending its time. It is compatible with the console.profile methods described with Firefox, and provides a nice interface to view the results. Figure 10-29 demonstrates a profile of a small Canvas application. I’ll cover one last
…
how long it’s taking. The resources tracked are JavaScript files, stylesheets, images, and the document, as shown in Figure 10-30. See Also The Firefox JavaScript profile functionality is covered in Recipe 10.9. For a detailed overview of the developer tools available with Safari 4, see http://www.apple
…
="http://web.resource.org/cc/DerivativeWorks"/> </cc:License> </rdf:RDF> </metadata> </svg> </body> </html> The result of the application can vary between browsers. When using Firefox and ac- cessing title without using the namespace variation, the only title returned is the XHTML document title. However, when using the namespace variation (getElements
…
time this was written. It has broad implementation across browsers, though there are some differences in implementation support. Earlier versions of browsers, such as IE7, Firefox 2, and so on, do not support the Selectors API. You’ll have to use fallback methods to per- form the same queries. In addition
…
(1), where parentheses are used to wrap the number of the target element. Figure 11-3. Page displaying highlighted first paragraphs in every div element Firefox, Safari, Chrome, and Opera support :first-of-type. IE8 doesn’t, but it does support :first-child. However, as the example demonstrates, we can’t
…
the type: var lis = document.querySelectorAll('li:nth-child(odd)'); 230 | Chapter 11: Accessing Page Elements Not all browsers support this relatively new selector type. Firefox, Opera, Safari, and Chrome do, but IE8 doesn’t support the first two approaches given in the solution, and older versions of most other browsers
…
work with multiple classes: var elems = document.getElementsByClassName("firstclass secondclass"); 11.8 Creating an Array of All Elements of a Given Class | 231 Chrome, Safari, Firefox, and Opera support getElementsByClassName, but IE8 doesn’t. The second approach using querySelectorAll is a good alternative option. It, too, can search for multiple class
…
= document.querySelectorAll('div:not(.test)'); 232 | Chapter 11: Accessing Page Elements This and the selector syntax examples given in the solution work with Opera, Chrome, Firefox, and Safari. Both of the selector syntax examples in the solution work with IE8, but the use of the negation operator, :not, does not. The
…
approach to accessing the window viewport informa- tion, which is why we have to use a series of case statements. Most major browsers, including Opera, Firefox, Chrome, and Safari, support window object properties called innerWidth and innerHeight, which return the window’s view- port area, minus any scrollbar dimensions. However, Internet
…
in implementations) that contains information about the bounding rectangle for the element. Most implementations support four properties on the object: top, bottom, right, and left. Firefox also includes width and height, though both can be derived from the other values. When I mention the bounding rectangle for the element, the dimensions
…
</p> </div> </div> </div> </body> Figure 13-4 shows the application with two containers, different tabbed pages open in each. The application works with Chrome, Firefox, Opera, Safari, and IE8. It doesn’t work with IE7 because of the use of querySelectorAll. Figure 13-4. A tabbed page application with two
…
"); Discussion Elements have different CSS display settings, depending on the type of element, and to some extent, the user agent. For browsers like Opera or Firefox, a span has an inline display value, while a div element has a block display value. Regardless of element type, though, setting the display to
…
("fill","#ff0000"); } } } ]]> </script> <svg:rect id="square" width="400" height="400" fill="#ff0000" x="10" y="10" /> </svg:svg> </body> </html> Chrome, Safari, Opera, and Firefox all support SVG. IE8 doesn’t, but IE9 will. Rec- ipe 15.6 covers how you can enable SVG graphics in IE8. 15.5 Accessing
…
In addition to the different approaches to get the SVG document, you also have to handle browser differences in how the onload event handler works. Firefox and Opera fire the onload event handler for the window after all the document contents have loa- ded, including the SVG in the object element
…
used instead. Here’s the finished scripting block, which encompasses all of these changes and works in IE8 as well as Safari, Chrome, Opera, and Firefox: <script> // set element onclick event handler window.addEventListener('SVGLoad', function () { var circle = document.getElementById("redcircle"); // onclick event handler, change circle radius circle.addEventListener('click', function
…
video control, displaying the number of seconds of video The video control is providing two different video codecs: H.264 ( .mp4), and Ogg Theora ( .ogv). Firefox, Opera, and Chrome support Ogg Theora, but Safari/WebKit only supports the H.264 formatted video. However, by providing both types, the video works in
…
with the custom objects. However, using defineProperty on DOM elements causes an exception in WebKit. None of the new property methods work with Opera. The Firefox Minefield nightly and the Chrome beta were the only browsers that currently work with both types of objects, as shown in Figure 16-2, which
…
displays the Image object properties in Firefox. Figure 16-2. Displaying Image properties after adding a new property with defineProperty 16.6 Extending an Object by Defining a New Property | 373 After
…
to true, because the property descriptor for experience allows modification on descriptor values. Enu- merating over the experience property now yields the following string for Firefox: Techbook has prototype experience However, Chrome does not pick up the prototype property. The next two lines of code create a new instance of the
…
Neither the category property in TechBook nor the title property in Book are returned, as these are private data members. When using WebKit nightly or Firefox Minefield, the same result is returned when using the new Object.keys method: alert(Object.keys(newBook).join(" ")); The same result is also returned, again
…
with WebKit nightly or Firefox Minefield, when using the new Object.getOwnPropertyNames method: var props = Object.getOwnPropertyNames(newBook); alert(props.join(" ")); However, if I add a property descriptor for the
…
does not support defineProperty and the associated new ECMAScript 5 functionality. WebKit nightly and the Chrome beta support all of the new functionality, while the Firefox nightly (Minefield), supports Object.keys, but not getOwnPropertyNames. IE8’s coverage is limi- ted because it only supports the new methods on DOM elements, such
…
yet, but should, knock on wood, by the time you read this book. Look for a first implementation in a Safari nightly build or a Firefox Minefield build. 16.9 Preventing Object Additions and Changes to Property Descriptors | 379 The Object.seal method prevents extensions to an object, like Object.preventExten
…
or both windows can add an event listener for the new message event. To ensure the event handling works with IE as well as Opera, Firefox, Safari, and Chrome, using object detection: function manageEvent(eventObj, event, eventHandler) { if (eventObj.addEventListener) { eventObj.addEventListener(event, eventHandler,false); } else if (eventObj.attachEvent) { event = "on
…
the back button, the window.onpopstate event handlers fires. Perfect timing to get the state data, and repair the page. Works beautifully, too. In the Firefox Minefield edition, that is. 468 | Chapter 20: Persistence One other change that had to be made to the older example, is that functionOne had to
…
an impact on sessionStorage, which could also be an unwelcome surprise for your users. Use sessionStorage with caution. The sessionStorage object is currently supported in Firefox 3.5 and up, Safari 4.x and up, and IE 8. There are some implementation differences for sessionStorage, but the example shown in this
…
also support the length property, which provides a count of stored item pairs, and the clear method (no parameters), which clears out all Storage (but Firefox only supports clearing storage for localStorage). In addition, both are scoped to the HTML5 origin, which means that the data storage is shared across all
…
among browsers: you can 20.5 Creating a localStorage Client-Side Data Storage Item | 477 capture the event on the body or document elements for Firefox, on the body for IE, or on the document for Safari. Example 20-5 demonstrates a more comprehensive implementation than the use case covered in
…
type="text" id="field4" /> <br /> <br /> <input type="submit" value="Save" /> </body> The size alloted for localStorage varies by browser, and some browsers, such as Firefox, allow users to extend the Storage object limits. The localStorage object can be used for offline work. For the form example, you can store the
…
Add-0n, Plug-in, or Extension | 485 Figure 21-1. Loading a Chrome extension Mozilla extensions The Mozilla extensions for the organization’s applications, including Firefox and Thunderbird, are reasonably uncomplicated to create, but even then, the number of files you need in order to implement an add-on is a
…
mean, and what you need to bring your application together. There is also an Extension Wizard, which can simplify your work. The functionality for your Firefox add-on is going to be based, in part, on JavaScript, though the environment may not be one you recognize. For instance, your extension could
…
worry about XUL, XPCOM, or intimidating file structures. Mozilla recently released the first milestone release of the Jetpack SDK, providing a simpler environment for creating Firefox extensions. Read more about it and download the SDK at http://mozillalabs.com/jetpack/ 2010/03/09/announcing-the-jetpack-sdk/. 21.1 Creating a
…
. Reversed array from uploaded file displayed in page Running the application again, but this time in the newest WebKit nightly build, the results match the Firefox result. What happened with Safari 4 is that postMessage didn’t serialize the object correctly when it transmitted the object to the web worker routine
JavaScript & jQuery: The Missing Manual
by David Sawyer McFarland · 28 Oct 2011 · 924pp · 196,343 words
, Microsoft introduced jScript, their own version of JavaScript included with Internet Explorer. Fortunately the worst of those days is nearly gone and contemporary browsers like Firefox, Safari, Chrome, Opera, and Internet Explorer 9 have standardized much of the way they handle JavaScript, making it easier to write JavaScript programs that
…
Bold command). That’s why many experienced computer mavens prefer to trigger menu commands by pressing certain combinations on the keyboard. For example, in the Firefox web browser, you can press Ctrl-+ (Windows) or ⌘-+ (Mac) to make text on a web page get larger (and more readable). When you read
…
this section shows you how to turn on the JavaScript console in all major browsers, so you can track down problems in each. The Firefox JavaScript Console Firefox’s JavaScript console is a great place to begin tracking down errors in your code. Not only does the console provide fairly clear descriptions
…
error with an arrow—in this case, highlighting the opening quote mark. Warning Although the error console draws an arrow pointing to the location where Firefox encountered the error, that’s not always where you made the mistake. Sometimes you need to fix your code before or after that arrow.
…
Figure 1-4. Firefox’s JavaScript console identifies errors in your programs. The console keeps a list of errors for previous pages as well, so pretty soon the list
…
can get very long. Just click the Clear button to erase all the errors listed in the console. To show the JavaScript console, click the Firefox menu and choose Web Developer→Error Console (on Windows) or Tools→Error Console (on Macs). The console is a free-floating window that you
…
—aler(‘hello’);—you’ll get an error saying that the (misspelled) command isn’t defined: for example, “aler is not defined.” Syntax error. Occasionally, Firefox has no idea what you were trying to do and provides this generic error message. A syntax error represents some mistake in your code. It
…
a typo in your code. Compare the script above with what you typed and check Tracking Down Errors for tips on debugging a script using Firefox, Safari, Chrome, or IE 9. Return to your text editor and change the second line of the script to read: var lastName = 'Jar'; Save
…
or Opera. Also, different browsers treat white space (like tabs and spaces) in HTML differently—in some cases treating white space like additional text nodes (Firefox and Safari) and in other cases ignoring that white space (IE). And those are just a few of the differences between how the most common
…
interactive user interfaces and adding cool effects to your websites, instead of worrying about how to get your script to work identically in Internet Explorer, Firefox, Safari, and Opera. In addition, the traditional DOM methods for selecting page elements aren’t very intuitive for web designers, especially since you already
…
CSS, and other useful resources. The exact name of the tab and method for turning on the tools panel varies from browser to browser: In Firefox, install the Firebug plug-in (discussed on Debugging with Firebug). Open a page with the JavaScript code you wish to see and open Firebug (Tools
…
complete DOM (including any HTML generated by JavaScript). Alternatively, you can use the Web Developer toolbar (https://addons.mozilla.org/en-US/firefox/addon/web-developer/) in Firefox to view both the regular HTML source, and the generated HTML. In IE 9, press the F12 key to open the Developer Tools
…
more columns of content to fit the space. Note Internet Explorer, Opera, and Safari fire multiple resize events as you resize the window, whereas Firefox only fires the resize event a single time after you’ve let go of the resize handle. scroll. The scroll event is triggered whenever you
…
keydown event is like the keypress event—it’s fired when you press a key. Actually, it’s fired right before the keypress event. In Firefox and Opera, the keydown event only fires once. In Internet Explorer and Safari, the keydown event behaves just like the keypress event—it fires
…
visit http://api.jquery.com/unbind/. POWER USERS’ CLINIC: Stopping an Event in Its Tracks Both Internet Explorer and the W3C event model supported by Firefox, Safari, and Opera let an event pass beyond the element that first receives the event. For example, say you’ve assigned an event helper for
…
, like Chrome and Safari, won’t let you hide scrollbars. status controls the appearance of the status bar at the bottom of the window. Firefox and Internet Explorer normally don’t let you hide the status bar, so it’s always visible in those browsers. toolbar sets the visibility of
…
the jQuery Way There are enough differences between browsers that you have to write extra code for your Ajax programs to work in Internet Explorer, Firefox, Safari, and Opera. And although the basic XMLHttpRequest process isn’t too complicated, since you must take so many steps each time you make
…
run, the browser lets you know if you’ve made a syntax error, but, confusingly, they all describe the problem differently. In the Firefox error console (The Firefox JavaScript Console), you get an error message like “missing ) after argument list”; Internet Explorer 9’s console (Displaying the Internet Explorer 9 Console
…
’s error console (Opening the Chrome JavaScript Console) gives you the less-helpful message “SyntaxError: ParseError.” As mentioned on Accessing the Safari Error Console, Firefox tends to provide the most understandable error messages, so it’s a good browser to start with when trying to figure out why a script
…
isn’t working (see Figure 15-1). Figure 15-1. Firefox’s Error Console lists all JavaScript errors that the browser encounters. You can display the console by choosing Web Developer→Error Console (Ctrl+Shift+J
…
to include the second quote mark as well. For example, alert(‘hello); produces an error because the final single quote is missing: alert(‘hello’);. In Firefox, if you forget to include both quote marks, you’ll get an “unterminated string literal” error, while Internet Explorer reports an “unterminated string constant”;
…
. For example, document refers to the HTML document. For example, look at the following code: var document='Something strange is happening here.'; alert(document); Firefox, Safari, and Opera don’t generate an error, but instead pop up an alert with the text “[object HTMLDocument],” which refers not to the HTML
…
correct path to the JavaScript file. Tip If you’re using the jQuery library and you get the error “$ is not defined” in the Firefox error console, you probably haven’t correctly linked to the jquery.js file (see Adding jQuery to a Page for more). Incorrect Paths Within External
…
program, as suggested in the previous point. In addition, you should test the script in different browsers—preferably Internet Explorer 7, 8, and 9; Firefox 5 and 6; the latest versions of Chrome and Safari; and whatever other browsers you think your site’s visitors might be using. Debugging with
…
have. It’s free, easy to install and use, and can help you improve your HTML, CSS, and JavaScript. Firebug is an extension for Firefox that adds a bunch of helpful diagnostic tools to let you pick apart your HTML, CSS, and (most importantly for this book) JavaScript programs. Installing
…
very thing. Click the Restart button. Voila, Firebug is installed and ready to use, but first you need to open it. On Windows, choose Firefox→Web Developer→Firebug→Open Firebug or Press F12; on Macs, choose Tools→ Web Developer→Firebug→Enable Firebug. Now you can begin using Firebug to help
…
you debug your scripts. Viewing Errors with Firebug Firebug provides an easier and more useful way to view errors than Firefox’s built-in error console. With Firebug, when you load a web page with JavaScript errors, you’ll see a counter in the upper
…
3). Click the Firebug icon to open the Firebug console, which lists any JavaScript errors. The errors listed in the console are the same as Firefox’s error console (Figure 15-1), but Firebug only lists errors for the page you’re currently viewing (unlike the error console, which lists
…
of variables in the script to make sure the variable contains the information you’re expecting it to have. Save the file, reload it in Firefox, and type some text into the comments box. The console should now display the contents in the comments box each time you type a
…
of characters: %d',chars); 10 $('#count').text(chars + " characters"); 11 }); // end keyup 12 }); // end ready 13 </script> Save the file, and preview it in Firefox. Make sure Firebug is open, and the page and console should now look something like Figure 15-5. You’ll find a finished version of
…
time. In this way, you can see exactly what’s happening at any particular line. Here’s the basic process. Open a web page in Firefox. You need Firebug installed and enabled as described on Debugging with Firebug. Open Firebug. Click the Firebug icon (in the upper-right corner of
…
Developer→Firebug→Enable Firebug (Mac). Note If you don’t like the cramped appearance of the web page stacked directly on top of Firebug, choose Firefox→Web Developer→Firebug→“Open Firebug in New Window” (Windows) or Tools→ Web Developer→Firebug→“Open Firebug in New Window” (Mac). Click the Script tab
…
on that line. Only add breakpoints to lines containing actual JavaScript code. Reload the web page. Since you have to view your web page in Firefox in order to open Firebug and add breakpoints, the JavaScript you want to debug may have already run (before you added any breakpoints). In
…
editor and modify your script (you’ll run through an example of fixing a script in the tutorial on Debugging Tutorial). Test the page in Firefox, and, if necessary, repeat the above steps to keep debugging your script. Controlling your script with the debugger Once you’ve added breakpoints to
…
bracket ended a nested array (Tutorial: A Simple Quiz) that contained all of the questions and answers for the quiz. Save the file; return to Firefox, and reload the page. Another error! This time the error console says “$ is not defined” and points to line 10 containing jQuery’s $(document
…
).ready() function. When Firefox reports that something’s “not defined,” it means the code is referring to something that doesn’t exist, which could be the name of a
…
text editor, and then remove the last s from askQuestions() in line 70 (near the end of the script). Save the file, reload it in Firefox, and then click the Start Quiz button again. Now, a quiz question appears along with five multiple-choice options. Unfortunately, the last option has
…
for the number of items in the answers array, creating one radio button for each possible answer. Save the file, and preview it in Firefox. You can turn off the breakpoint by clicking its red dot in the firebug script window to see the finished page run without interruption. The
…
Basics, Conditional Statement Basics, Tips for Writing Conditional Statements equalTo validation rule, Advanced rules error() function, jQuery, Handling Errors errors, Your First JavaScript Program, The Firefox JavaScript Console, Adding validation rules, Adding error messages, Advanced rules, Advanced error messages, Styling Error Messages, Styling Error Messages, Formatting the Error Messages, Handling Errors
…
Messages, Formatting the Error Messages from web server, with Ajax, Handling Errors in Internet Explorer, blocked content, Your First JavaScript Program syntax errors, The Firefox JavaScript Console, Top JavaScript Programming Mistakes, Non-Closed Pairs, Disappearing Variables and Functions types of, Non-Closed Pairs viewing in Firebug, Viewing Errors with Firebug
…
, Selecting Form Elements find() function, jQuery, Tutorial: Using the get() Function, Optimizing Your Selectors, Traversing the DOM, Traversing the DOM Firebug plug-in, The Firefox JavaScript Console, Replacing and Removing Selections, Disappearing Variables and Functions, Installing and Turning On Firebug, Installing and Turning On Firebug, Using console.log() to Track
…
Debugging, Watching your script installing, Installing and Turning On Firebug Firefox, Tracking Down Errors, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console JavaScript console in, Tracking Down Errors, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console flags, boolean data type used for, Adding
…
messages, Using AnythingSlider, Adding Google Maps to Your Site, Adding Google Maps to Your Site, Adding Google Maps to Your Site, Other GoMap Options for Firefox, How HTML Tags Work HTML Validator, How HTML Tags Work for jQuery, About JavaScript Libraries, jQuery Validation Plug-in, Advanced Validation, Advanced error messages,
…
About JavaScript Libraries pull quotes, tutorial for, Automatic Pull Quotes, Automatic Pull Quotes, Overview, Programming, Programming punctuation errors, Your First JavaScript Program, The Firefox JavaScript Console, The Firefox JavaScript Console, Non-Closed Pairs, Non-Closed Pairs, Non-Closed Pairs, Non-Closed Pairs, Non-Closed Pairs push() method, arrays, Adding an item
…
, Creating Fast-Loading JavaScript, The Switch Statement, The Switch Statement, The Switch Statement, Creating Fast-Loading JavaScript syntax errors, Your First JavaScript Program, The Firefox JavaScript Console, Non-Closed Pairs, Non-Closed Pairs, Using Reserved Words, Single Equals in Conditional Statements, Single Equals in Conditional Statements, Incorrect Path to External
…
FancyBox, FancyBox options transitionOut option, FancyBox, FancyBox options trigger, for tooltip, Adding Tooltips, The HTML, Tooltips Tutorial troubleshooting, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console, Displaying the Internet Explorer 9 Console, Displaying the Internet Explorer 9 Console, Opening the Chrome JavaScript Console
…
Error Console conditional statements, Tips for Writing Conditional Statements, Tutorial: Using Conditional Statements, Tutorial: Using Conditional Statements Firefox JavaScript Console for, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console, The Firefox JavaScript Console Internet Explorer 9 Console for, Displaying the Internet Explorer 9 Console, Displaying the Internet Explorer
The Tangled Web: A Guide to Securing Modern Web Applications
by Michal Zalewski · 26 Nov 2011 · 570pp · 115,722 words
the problem, but the trend eventually created an atmosphere conducive to a small rebellion. In 2004, a new contender in the browser wars emerged: Mozilla Firefox (a community-supported descendant of Netscape Navigator) took the offensive, specifically targeting Internet Explorer’s poor security track record and standards compliance. Praised by both
…
IT journalists and security experts, Firefox quickly secured a 20 percent market share. While the newcomer soon proved to be nearly as plagued by security bugs as its counterpart from Redmond
…
By bundling, promoting, or demoting certain online services (even as simple as the default search engine), whoever controls the browser controls much of the Internet. Firefox aside, Microsoft had other reasons to feel uneasy. Its flagship product, the Windows operating system, was increasingly being used as an (expendable?) launch pad for
…
from the past, vendors also decided to experiment boldly with new ideas, sometimes unilaterally rolling out half-baked or somewhat insecure designs like globalStorage in Firefox or httponly cookies in Internet Explorer, just to try their luck. To further complicate the picture, frustrated by creative differences with W3C, a group
…
Vendor Browser Name Market Share Microsoft Internet Explorer 6 10% 52% Internet Explorer 7 7% Internet Explorer 8 31% Internet Explorer 9 4% Mozilla Firefox 3 12% 22% Firefox 4+ 10% Google Chrome 13% Apple Safari 7% Opera Software Opera 3% Source: Data drawn from public Net Applications reports.[93] Part I
…
other than general URL section delimiters, in this section with two exceptions: Safari, for unclear reasons, rejects a broader set of characters, including “<”, “>”, “{”, and “}”, while Firefox also rejects newlines.[10] Server Address For all fully qualified hierarchical URLs, the server address section must specify a case-insensitive DNS name (such as
…
inception, Internet Explorer accepted backslashes (\) in lieu of slashes in any location in the URL, presumably to assist inexperienced users.[11] All browsers other than Firefox eventually followed this trend and recognize URLs such as http:\\example.com\. STEP 3: Grab the authority section. Scan for the next “/”, “?”, or “#”, whichever
…
its impact ranged from the heavy-handed and oddly specific (e.g., disabling URL-based authentication in Internet Explorer or crippling it with warnings in Firefox) to the fairly sensible (e.g., hostname highlighting in the address bar of several browsers). Reserved Characters and Percent Encoding The URL-parsing algorithm
…
appear in URLs without escaping and will send these characters to the server as is. Internet Explorer further permits “<”, “>”, and “`” to go through; Internet Explorer, Firefox, and Chrome all accept “\”; Chrome and Internet Explorer will permit a double quote; and Opera and Internet Explorer both pass the nonprintable character 0x7F (DEL
…
types of social engineering attacks, and consequently, various countermeasures have been deployed through the years. As usual, some of these countermeasures are disruptive (for example, Firefox flat out rejects percent-encoded text in hostnames), and some are fairly good (such as the forced “canonicalization” of the address bar by decoding all
…
msbd:, and rtsp: protocols for streaming media players; and so on. Browsers are sometimes also included on the list. The previously mentioned firefoxurl: scheme launches Firefox from within another browser, while cf: gives access to Chrome from Internet Explorer. For the most part, when these schemes appear in URLs, they usually
…
values are supposed to use the quoted-string format outlined in HTTP specs (see Semicolon-Delimited Header Values in Semicolon-Delimited Header Values), but only Firefox and Opera recognize this syntax in practice. Reliance on quoted-string values is therefore unsafe, and so is allowing stray quote characters in attacker-
…
surface and graphic primitives for JavaScript applications to build their interfaces with. * * * [25] To process HTML documents, Internet Explorer uses the Trident engine (aka MSHTML); Firefox and some derived products use Gecko; Safari, Chrome, and several other browsers use WebKit; and Opera relies on Presto. With the exception of WebKit, a
…
speculatively extract <meta http-equiv> information before actually parsing the document, which may lead to embarrassing mistakes. For example, a security bug recently fixed in Firefox 4 caused the browser to interpret the following statement as a character set declaration: <meta http-equiv="Refresh" content="10;http://www.example.com/charset
…
begins. In Chrome, Safari, and Opera, it is possible to subsequently remove the eval(...) function altogether, using the delete operator. Confusingly, attempting the same in Firefox will restore the original built-in function, undoing the effect of the original override. Finally, in Internet Explorer, the deletion attempt will generate a belated
…
unnecessary but elegant plan to incorporate XML syntax directly into JavaScript as an alternative to JSON-style serializations. In any E4X-compatible engine, such as Firefox, the following two snippets of code would be roughly equivalent: // Normal object serialization var my_object = { "user": { "given_name": "John", "family_name": "Smith", "id":
…
user-specific text displayed in an unrelated document. The following example illustrates the risk: To their credit, after several years of living with the flaw, Firefox developers decided to disallow any E4X statements that span the entirety of any parsed script, partly closing this loophole. Nevertheless, the fluidity of the language
…
name property permits this). * * * [33] There are a recently added window.crypto.getRandomValues(...) API in Chrome and a currently nonoperational window.crypto.random(...) API in Firefox. Script Character Encoding JavaScript engines support several familiar, backslash-based string-encoding methods that can be employed to escape quote characters, HTML markup, and other
…
namespace associated with it, will have no visible effect. The second one will be understood as an XHTML tag that triggers underlining. Figure 7-1. Firefox displaying an XML document with no recognized namespaces The consequences of this fault-tolerant approach to the rendering of unknown XML documents and unrecognized namespaces
…
its .NET framework to the point of silently installing nonremovable Windows Presentation Foundation plug-ins—not only in Internet Explorer but also in the competing Firefox and Chrome. This move stirred some well-deserved controversy, especially once the first vulnerability reports started pouring in. (Mozilla even temporarily disabled the plug-
…
untrusted environments, and over the next 15 years, researchers discovered several hundred significant security vulnerabilities in web-accessible ActiveX controls. Heck, the simple observation that Firefox does not support this technology helped bolster its security image at the onset of the Second Browser Wars. Despite this fiasco, Microsoft stood by ActiveX
…
another. Similarly, the TRACE method is blocked everywhere, because of the unanticipated risk it posed to httponly cookies—but the CONNECT method is permitted in Firefox, despite carrying a vague risk of messing with HTTP proxies. Naturally, implementing these blacklists has proven to be an entertaining exercise on its own. Strictly
…
closely related mechanism, DOMService,[193] ignores this setting and gives applets largely unconstrained access to the embedding page. While DOMService is not supported in Firefox and Opera, it is available in other browsers, which makes any attempt to load third-party Java content equivalent to granting full access to the
…
other page. Another special case is the loading of a normal server-supplied document that subsequently redirects to about:blank using Location or Refresh. In Firefox and WebKit-based browsers, such redirection results in a unique, nonaccessible origin, similar to the scenario outlined in the previous paragraph. In Internet Explorer,
…
Location redirect Refresh redirect URL entry or gesture Internet Explorer Inherited from caller Unique origin (Denied) Frame: Inherited from parent Unique origin Window: Unique origin Firefox Inherited from caller Unique origin All WebKit Inherited from caller (Denied) Unique origin Opera Inherited from caller Inherited from redirecting party Inherited from parent * * * [
…
care. WebKit browsers In Chrome and Safari, all data: documents are given a unique, nonaccessible origin and do not inherit from the parent at all. Firefox In Firefox, the origin for data: documents is inherited from the navigating context, similar to about:blank. However, unlike with about:blank, manually entering data: URLs
…
same-origin page Location redirect Refresh redirect URL entry or gesture Internet Explorer 6/7 (Not supported) Internet Explorer 8/9 (Not supported for navigation) Firefox Inherited from caller Unique origin Inherited from previous page All WebKit Unique origin (Denied) Unique origin Unique origin Opera Shared origin (This is a bug
…
and then navigate that frame to javascript:do_evil_stuff() and call it a day. Consequently, such navigation is prohibited in all browsers except for Firefox. Firefox appears to permit it for some reason, but it changes the semantics in a sneaky way. When the origin of the caller and the navigation
…
page Location redirect Refresh redirect URL entry or gesture Internet Explorer Inherited from caller Inherited from navigated page (Denied) (Denied) (Denied) Inherited from navigated page Firefox Null context (Denied) All WebKit (Denied) Inherited from navigated page Opera (Denied) Inherited from navigated page On top of these fascinating semantics, there is a
…
from interfering with any other simultaneously opened browser sessions. Surprisingly, even this simple policy proved difficult to implement correctly. It was only in 2008 that Firefox eliminated this class of problems,[199] while Microsoft essentially ignored the problem until 2006. Still, these setbacks aside, we should be fine—right? Frame
…
in many versions of Internet Explorer, it was possible to manipulate the value of window.opener or window.name of an unrelated window. Meanwhile in Firefox, there are currently no constraints on setting location.hash across domains, even though all other partial location properties are restricted. The primary significance of these
…
Comparably disastrous consequences have been observed with a variety of privileged, internally handled URLs. The ability to navigate directly to locations such as about:config (Firefox) not only made it possible to exploit potential vulnerabilities in the privileged scripts (a transgression to which browser vendors are not immune) but also led
…
Esser, Abhishek Arya, and several other researchers demonstrated a number of plausible attacks that leveraged this feature to force UTF-7 parsing on unsuspecting targets, Firefox and WebKit developers decided to limit the behavior to same-origin frames. (Opera still permits cross-domain inheritance. Although it does not support UTF-7
…
signals. For example, was the mouse pointer in the current window 500 milliseconds ago? * * * [69] See, for example, Mozilla bug 561177, where one of the Firefox UI engineers proposed the removal of a security delay from the plug-in installation prompt. Chapter 15. Extrinsic Site Privileges To wrap up the discussion
…
plans, as of this writing only one browser includes the Origin header on non-CORS navigation: WebKit-based implementations send it when submitting HTML forms. Firefox seems to be considering a different approach, but nothing specific seems to have been implemented yet. * * * [77] Malicious URL blacklists, a feature supported by (
…
browser in response to a call to the registerProtocolHandler(...) API, with the protocol name set to “doing really awesome stuff” and application name set to “Firefox (mozilla.org)”. This particular example is harmless, but more sinister abuse is within reach. Address bar manipulation The newly introduced HTML5 history.pushState(...) API,[257
…
] supported by Firefox, WebKit, and Opera, permits the currently displayed document to change the contents of the address bar to any other same-origin URL, without actually triggering
…
is currently supported only in Chrome, and other than select Google services, it is not commonly encountered on the Web. It may be coming to Firefox soon, too, however. HTTP-less networking WebSocket[259] is a still-evolving API designed for negotiating largely unconstrained, bidirectional TCP streams for when the
…
storage mechanisms such as localStorage (Chapter 9), this allows certain self-sufficient JavaScript applications to be used in offline mode. Offline operation is supported in Firefox, the WebKit browser, and Opera. As with localStorage, the persistent nature of this mechanism could exacerbate the long-term consequences of visiting an untrusted network
…
Web 2.0 Security and Privacy, Oakland, CA (2008), http://seclab.stanford.edu/websec/origins/scheme/. [92] “Security Exploit Uses Internet Explorer to Attack Mozilla Firefox,” MozillaZine (July 11, 2007), http://www.mozillazine.org/talkback.html?article=22198. [93] Net Applications website, http://marketshare.hitslink.com/browser-market-share.aspx?qprid
…
error” message, retrieved file snippet in, Beyond the Threat of a Single Click A about:blank document, origin inheritance, Origin Inheritance, Origin Inheritance about:config (Firefox), navigation risks, Navigation to Sensitive Schemes absolute URLs, vs. relative, Scheme Name Accept request header, Basic Syntax of HTTP Traffic Accept-Language request header, Basic
…
filtering, Basic Concepts Behind HTML Documents, Connection Limits, Pop-Up Filtering pop-up, Pop-Up Filtering reserved characters, in HTML, Basic Concepts Behind HTML Documents Firefox (Mozilla), Web 2.0 and the Second Browser Wars: 2004 and Beyond, Cross-Browser Interactions: Synergy in Failure, Indicator of a Hierarchical URL, Reserved Characters
…
Disposition, Internet Explorer’s Zone Model mouse cursors, redefining, Basic CSS Syntax Moved Permanently status code (301), 300-399: Redirection and Other Status Messages Mozilla Firefox. See Firefox (Mozilla), Content Security Policy Mozilla specification, Content Security Policy msbd: scheme, Common URL Schemes and Their Function MsgBox (VBScript), Code Inclusion Modes and Nesting

Engineering Security
by Peter Gutmann
just how tolerant browsers have to be of such technology errors in order to function, enable script debugging (Internet Explorer), look at the error console (Firefox), or install Safari Enhancer and look at the error log (Safari). No matter which detection method you use, you can barely navigate to any Javascript
…
delivery network in Korea didn’t help [534]. Another certificate, this time a genuine EV one, was displayed as a non-EV certificate for which Firefox reported that “This website does not supply ownership information” (even though the information was present in the certificate), which was enough to confuse antiphishing people
…
over time, with no consistency across the indicators used by different browsers, or in some cases even within browsers [558]. For example Internet Explorer and Firefox both reserve the colour green for EV certificates, while Chrome uses it for both EV and non-EV certificates [559], and the Android browser using
…
between the near-invisible indicators and the change in the way that certificate errors are handled in newer browser versions. In Internet Explorer 8 and Firefox 3 any form of certificate error (including minor bookkeeping ones like forgetting to pay your annual CA tax) results in a huge scary warning that
…
of benefit to attackers to spoof non-SSL rather than spoofing SSL. The high level of effectiveness of this form of attack against the new Firefox 3 interface was shown in one proof-of-concept demonstration that garnered credentials for 117 email accounts, 7 PayPal logins, and 300 other miscellaneous secure
…
mechanism as one component of a security riskdiversification approach as described in “Security through Diversity” on page 315. The awkward certificate-warning process introduced in Firefox 3 and Internet Explorer 8 is a prime example of a phenomenon that social psychologists describe as task focus overriding goal focus, in which users
…
lose sight of the overall goal. This task-focus induced perceptual narrowing is aptly summed up by one user’s experience with the Firefox 3 certificate warning mechanism, “Firefox makes me jump through so many hoops that all my focus is on getting through the hoops, rather than evaluating security” [572]. This
…
result was echoed in a study into warning dialogs, in which the more obnoxious dialogs, like the certificate warnings introduced in Firefox 3/IE8, caused users to focus on working past the dialog rather than thinking about the underlying security issue. Because of this the dialogs performed
…
), p.62. 100 Problems [140] “JavaScript and HTML: Forgiveness by Default”, Jeff Atwood, 26 April 2007, http://www.codinghorror.com/blog/archives/000848.html. [141] “Firefox and the Worry-free Web”, Blake Ross, in “Security and Usability: Designing Secure Systems That People Can Use”, O’Reilly, 2005, p.577. [142] “Access
…
and CAs: Revocation isn’t enough and everyone knows it”, Jacob Appelbaum, 18 March 2011, https://bugzilla.mozilla.org/show_bug.cgi?id=643056. [283] “Firefox Blocking Fraudulent Certificates”, Mozilla Security Blog, 22 March 2011, https://blog.mozilla.com/security/2011/03/22/firefoxblocking-fraudulent-certificates/. [284] “Comodo Certificate Issue — Follow
…
Donald <jamesd@echeque.com>, posting to the hcisec@yahoogroups.com mailing list, message-ID 45DD1784.5010606@echeque.com, 22 February 2007. [544] “Spoofing SSL in Firefox 3”, Eddy Nigg, 20 May 2008, https://blog.startcom.org/?p=86. [545] “Вскрываем SSL. Перехват данных в защищенных соединениях”, Anton Zhukov, Xakep, No.125
…
to take some risks in order to get the job done [511]. Something similar happened during usability testing of a password-manager plugin for the Firefox browser designed to replace the existing primitive built-in password manager, users simply gave up trying to use the password manager rather than looking to
…
” [669]. Although developers are usually quite capable of shooting users in the foot without outside assistance, this degree of bureaucratic indecision can’t have helped. Firefox developers discovered via feedback from users that the users actually saw through this deception, recognising the warning dialogs as “intentionally obfuscated warnings that companies can
…
4th International Conference on Electronic Commerce Research -— Volume 2, November 2001, p.628. [470] “Re: [hcisec] Are there any recent studies on the effectiveness of Firefox’s URL-bar colouring?”, Serge Egelman, posting to the hcisec@yahoogroups.com mailing list, message-ID c46d4ffc0809161156i6af493d0kf281150d18594532@mail.gmail.com, 16 September 2008. [471] “Re
…
: [hcisec] Are there any recent studies on the effectiveness of Firefox’s URL-bar colouring?”, Rachna Dhamija, posting to the hcisec@yahoogroups.com mailing list, message-ID 823AB7C6-34E1-49E2A1E2-9983B010577B@deas.harvard.edu, 16 September
…
and Business of Giving Psychology Away”. Gerald Rosen, Russell Glasgow and Timothy Moore in “Science and Pseudocience in Clinical Psychology”, Guilford Press, 2003, p.399. “Firefox and the Worry-Free Web”, Blake Ross, in “Security and Usability: Designing Secure Systems That People Can Use”, O’Reilly, 2005, p.577. “Users and
…
as the ability to hijack session authenticators like cookies sent out over unprotected channels, as was so aptly demonstrated by the Firesheep add-on for Firefox in late 2010 [78] after years of unsuccessful attempts to get the problem fixed [79]. Another example of this type of problem occurred with
…
be treated with caution. An alternative view of this vulnerability was that it was actually MSIE, or the Windows shell/ShellExecute() function, or anything but Firefox, that was at fault for allowing itself to be used for threat tunnelling [168], although this argument was derailed somewhat when it was revealed that
…
combined, the result may exhibit new properties not present in the original, with the resulting combination no longer being secure. Examples of this were the Firefox URL and second-order SQL injection problems mentioned in “Threat Modelling with Data Flow Diagrams” on page 263. Another example occurs when you connect a
…
sent random Windows event messages [218]. A related study on the reliability of thirty different GUI applications on OS X, including Acrobat Reader, Apple Mail, Firefox, iChat, iTunes, MS Office, Opera, and Xcode found them to be even worse than the Windows ones [219]. Attack Surface Reduction 337 Normal user actions
…
can be done by a compromised plugin [302]. The seriousness of this problem was shown by one analysis of vulnerabilities in a random selection of Firefox plugins, which revealed numerous problems including bypassing of filtering by the popular NoScript plugin (so that NoScript wouldn’t protect against the remainder of the
…
, this coin-toss tweaking of the user interface actually represents a step backwards in security. The reason given for making the change was that the Firefox developers felt that making the exception non-permanent meant that users would see the add-anexception page more frequently, thus training them to ignore it
…
that the training effect was occurring anyway regardless of the change [348], and another study a few years later again confirmed this, not just for Firefox but for Internet Explorer as well [349], yielding a net loss in security. Attack Surface Reduction 353 A similar problem has been reported for cell
…
brands are secure, merely that these were all the routers that were available for the demonstration, and all of them proved vulnerable) [382]. Somewhat surprisingly, Firefox is the easiest browser to abuse for this type of attack and Internet Explorer the hardest [383]. A slightly different approach that uses DNS rebinding
…
it was available for use, people might actually rely on it (!!) [571]. Link fingerprints have however been supported by a range of download managers and Firefox add-ons for several years [572][573], and a standardised form of this mechanism provided as part of a download-management framework called Metalink provides
…
concept developed at Xerox PARC [678]. This bundles a site-specific profile and site information with an instance of XULRunner, a componentised interface to the Firefox browser core, inside a digitally signed package. Each of these packages is about 40kB in size and launches a locked-down, secure-by-default instance
…
Stiegler, Alan Karp, Ka-Ping Yee, Tyler Close and Mark Miller, Communications of the ACM, Vol.49, No.9 (September 2006), p.83. [346] “Abusing Firefox Extensions”, Roberto Liverani and Nick Freeman, presentation at Defcon 17, July 2009, https://www.defcon.org/images/defcon-17/dc-17-presentations/defcon-17-roberto
…
browser installs the malicious ActiveX control. This attack, known as Z-order spoofing [91], was first discovered in 2001 and then subsequently rediscovered by the Firefox browser developers [92][93][94] but also affected Internet Explorer [95] (a variation of this, clickjacking, is more generally used to redirect clicks from one
…
by the attacker, they can make the user see anything they want in there, with the problem affecting (in various forms) Internet Explorer, Google Chrome, Firefox, and Safari. Only Opera seems to get it right [159]. Figure 116: golaid gninraw resu no kcatta noitatneserP (Image courtesy FSecure) A particularly amusing example
…
[166] (witness the eight-year-long — and still ongoing — battle by a non-commercial CA to have its root certificates included in every version of Firefox since release 0.6 [167]). Worse, by changing the browser behaviour in an attempt to frighten users away from blindly accepting invalid certificates (be it
…
to note that they make an attacker’s job quite a bit harder). In fact of the applications that were evaluated, which included Adobe Reader, Firefox, Flash, iTunes, Java, OpenOffice, Quicktime and Winamp, just one single application, Google Chrome, enabled both DEP and ASLR [282][283] (although several vendors promised to
…
problem occurs. Suddenly their browser is complaining whenever they try to access SSL sites. Such problems are already being reported with OCSP-enabled browsers like Firefox [49][50], leading to what’s been described as “an impassable brick wall with geek speak written on it” [51]. An even more serious situation
…
by users to mean that the site was down, leading to OCSP-induced apparent outages of major services like FedEx [52]117. Mozilla later changed Firefox’ behaviour to ignore problems that occurred when communicating with OCSP responders, acknowledging the fact that “breaking web sites because of the unreliability of an OCSP
…
/green colour blindness Blue/yellow colour blindness Total colour blindness Normal vision Figure 137: Breakdown of colour blindness by type 120 Unfortunately newer versions of Firefox undid this change again, if you want to restore it then the magic incantation “#urlbar[level] .autocomplete-textbox-container > * { background-color: #FFFFB7 !important; }” in the
…
indicator like giving the password-entry box a red or blinking background to warn the user that something’s wrong. This is exactly what a Firefox plugin that performs this function, written by one of the Mozilla developers, does [75]. Figure 140: Unprotected login screen, with (in)security indicators The fact
…
7th Conference on Availability, Reliability and Security (ARES’12), August 2012, p.327. “Mark Unsecured Password Elements”, Johnathan Nightingale, https://addons.mozilla.org/en-US/firefox/addon/8128. “Why Phishing Works”, Rachna Dhamija, J.D.Tygar and Marti Hearst, Proceedings of the 24th Conference on Human Factors in Computing Systems (CHI
…
Sandler and Dan Wallach, Proceedings of Web 2.0 Security and Privacy (W2SP’08), May 2008, http://w2spconf.com/2008/papers/s1p2.pdf. “TargetAlert for Firefox”, Michael Bolin, http://www.bolinfest.com/targetalert/. “Bank’s own developers a much bigger problem than browsers”, ‘mhp’, 18 July 2004, http://news.netcraft.com
…
issue that helped kill multilevel secure (MLS) workstations in the 1980s. More recently, the same issue dissuaded users from employing a password manager plugin for Firefox since it made them feel that they’d lost control over their own passwords, a problem explored in more detail in “Password Manager Browser Plugins
…
stored in different profiles, but that’s mostly a bookkeeping function rather than any real attempt to distinguish between different classes of passwords). For example Firefox uses a single master password to protect all secrets in the system, whether it’s the password for the Knitting Pattern Weekly or the password
…
as plaintext). The level of interest in this style of password management is demonstrated by the existence of at least half a dozen independently-created Firefox browser plugins [411] and even completely browser-independent bookmarklets [412] that retroactively add this functionality, and can be demonstrated even more dramatically by typing “password
…
Symposium (Usenix Security’05), August 2005, p.17. References 655 [412] “SuperGenPass: A Free Bookmarklet Password Generator”, Chris Zarate, http://supergenpass.com/. [413] “How Many Firefox Users Customize Their Browser?”, Ken Kovash, 11 August 2009, http://blog.mozilla.com/metrics/2009/08/11/how-manyfirefox-users-customize-their-browser/. [414] “How
…
expired certificates as well [450], which none of the PKI software that the responder was being used with had noticed until it was accessed with Firefox, which performs more rigorous checking for OCSP, including imposing the not-unreasonable requirement that the certificate is actually valid. This lack of checking may be
…
whose certificate was displayed as being for DigiSign. X.509 709 Figure 193: A certificate both issued by, and owned by, nobody Newer versions of Firefox were updated to try and address the fixed-DN assumptions by pulling in substitute identifiers from other locations, with the result that they now display
…
public CA like Verisign, not because it’s found anything wrong with the certificate itself). Figure 195: Komplex Labs certificate as viewed by Windows and Firefox The certificate’s negative validity period is from midnight on January 1951 to one second before midnight on January 1951, with both applications considering it
…
in the mozilla.dev.security.policy newsgroup, message-ID cdOdnRQNY8a1uivWnZ2dnUVZ_h-dnZ2d@mozilla.org, 2 April 2010. [594] “RSA says it fathered orphan credential in Firefox, Mac OS”, Dan Goodin, 6 April 2010, http://www.theregister.co.uk/2010/04/06/mysterious_mozilla_apple_certificate/. [595] “Nautilus Secure Phone Home Page
…
. Is there a way I can turn some on” [76], possibly a first ever for a security application. Password Manager Browser Plugins Several browsers like Firefox have optional password manager plugins that implement some of the strengthened-password mechanisms described in more detail in “Passwords” on page 563. A study of
High Performance JavaScript
by Nicholas C. Zakas · 15 Mar 2010 · 375pp · 66,268 words
Other browsers soon followed suit with their own optimizing JavaScript engines. Safari 4 features the Squirrel Fish Extreme (also called Nitro) JIT JavaScript engine, and Firefox 3.5 includes the TraceMonkey engine, which optimizes frequently executed code paths. With these newer JavaScript engines, optimizations are being done at the compiler-level
…
DOM and therefore execution can be safely deferred until a later point in time. The defer attribute is supported only in Internet Explorer 4+ and Firefox 3.5+, making it less than ideal for a generic cross-browser solution. In other browsers, the defer attribute is simply ignored and so
…
’t executed until after the second but is executed before the onload event handler is called. If your target browsers include only Internet Explorer and Firefox 3.5, then deferring scripts in this manner can be helpful. If you have a larger cross-section of browsers to support, there are
…
contents have not yet been loaded.* When a file is downloaded using a dynamic script node, the retrieved code is typically executed immediately (except in Firefox and Opera, which will wait until any previous dynamic script nodes have executed). This works well when the script is self-executing but can be
…
when the code has been fully downloaded and is ready for use. This is accomplished using events that are fired by the dynamic <script> node. Firefox, Opera, Chrome, and Safari 3+ all fire a load event when the src of a <script> element has been retrieved. You can therefore be
…
notified when the script is ready by listening for this event: var script = document.createElement("script") script.type = "text/javascript"; //Firefox, Opera, Chrome, Safari 3+ script.onload = function(){ alert("Script loaded!"); }; script.src = "file1.js"; document.getElementsByTagName("head")[0].appendChild(script); Internet Explorer supports an
…
as necessary on a page, but make sure you consider the order in which files must be loaded. Of all the major browsers, only Firefox and Opera guarantee that the order of script execution will remain the same as you specify. Other browsers will download and execute the various code
…
with inline code. • There are several ways to download JavaScript in a nonblocking fashion: — Use the defer attribute of the <script> tag (Internet Explorer and Firefox 3.5+ only) — Dynamically create <script> elements to download and execute the code — Download the JavaScript code using an XHR object, and then inject the
…
relative speed of accessing 200,000 values from each of these four locations in various browsers. Older browsers using more traditional JavaScript engines, such as Firefox 3, Internet Explorer, and Safari 3.2, show a much larger amount of time taken to access values versus browsers that use optimizing JavaScript engines
…
the same across all browsers: literal value and local variable access tend to be faster than array item and object member access. The one exception, Firefox 3, 15 Figure 2-1. Time per 200,000 reads from various data locations optimized array item access to be much faster. Even so,
…
given object type, and so all instances also share the prototype object’s members. An object is tied to its prototype by an internal property. Firefox, Safari, and Chrome expose this property to developers as __proto__; other browsers do not allow script access to this property. Any time you create
…
Data access going deeper into the prototype chain Although newer browsers with optimizing JavaScript engines perform this task well, older browsers—especially Internet Explorer and Firefox 3.5—incur a performance penalty with each additional step into the prototype chain. Keep in mind that the process of looking up an instance
…
in 35 its latest version). Google Chrome also uses WebCore libraries from WebKit for rendering pages but implements its own JavaScript engine called V8. In Firefox, Spider-Monkey (the latest version is called TraceMonkey) is the JavaScript implementation, a separate part of the Gecko rendering engine. Inherently Slow What does
…
childNodes childElementCount childNodes.length firstElementChild firstChild lastElementChild lastChild nextElementSibling nextSibling previousElementSibling previousSibling All of the properties listed in Table 3-1 are supported as of Firefox 3.5, Safari 4, Chrome 2, and Opera 9.62. Of these properties, IE versions 6, 7, and 8 only support children. Looping over
…
of the results of getElementsbyTagName() DOM Access and Modification | 49 The Selectors API is supported natively in browsers as of these versions: Internet Explorer 8, Firefox 3.5, Safari 3.1, Chrome 1, and Opera 10. As the results in the figure show, it’s a good idea to check
…
array itself. The following is an example usage: items.forEach(function(value, index, array){ process(value); }); Loops | 67 The forEach() method is implemented natively in Firefox, Chrome, and Safari. Additionally, most JavaScript libraries have the logical equivalent: //YUI 3 Y.Array.each(items, function(value, index, array){ process(value); }); //jQuery
…
, the browser will error out with one of the following messages: • Internet Explorer: “Stack overflow at line x” 74 | Chapter 4: Algorithms and Flow Control • Firefox: “Too much recursion” • Safari: “Maximum call stack size exceeded” • Opera: “Abort (control stack overflow)” Chrome is the only browser that doesn’t display a
…
errors in some browsers, and can therefore be trapped using a try-catch statement. The exception type varies based on the browser being used. In Firefox, it’s an InternalError; in Safari and Chrome, it’s a RangeError; and Internet Explorer throws a generic Error type. (Opera doesn’t throw
…
right from JavaScript: try { recurse(); } catch (ex){ alert("Too much recursion!"); } If left unhandled, these errors bubble up as any other error would (in Firefox, it ends up in the Firebug and error consoles; in Safari/Chrome it shows up in the JavaScript console), except in Internet Explorer. IE will
…
to see this in action: function foldingDemo() { var str = "compile" + "time" + "folding"; str += "this" + "works" + "too"; str = str + "but" + "not" + "this"; } alert(foldingDemo.toString()); /* In Firefox, you'll see this: function foldingDemo() { var str = "compiletimefolding"; str += "thisworkstoo"; str = str + "but" + "not" + "this"; } */ When strings are folded together like this, there are
…
to fail, and with 20 As, that number explodes to more than a million. Thirty-five As should be enough to hang Chrome, IE, Firefox, and Opera for at least 10 minutes (if not permanently) while they process the more than 34 billion backtracking steps required to invalidate all permutations
…
regexes with groupings or optional tokens, and avoid top-level alternation such as /one|two/ since that forces the regex to consider multiple leading tokens. Firefox is sensitive to the use of any quantifier on leading tokens, and is better able to optimize, e.g., \s\s* than \s+ or
…
left to right, so the more frequently an option is expected to match, the sooner you want it to be considered. Note that Chrome and Firefox perform some of these optimizations automatically, and are therefore less affected by techniques for hand-tuning alternation. Use noncapturing groups Capturing groups spend time and
…
e.g., element zero in arrays returned by regex.exec() or $& in replacement strings. Replacing capturing groups with their noncapturing kin has minimal impact in Firefox, but can make a big difference in other browsers when dealing with long strings. Capture interesting text to reduce postprocessing As a caveat to the
…
JavaScript function. Subsequent implementations of this example assume that this conditional is in place, though it is not written out each time. You can give Firefox a performance boost of roughly 35% (less or more depending on the target string’s length and content)* by replacing /\s+$/ (the second regex)
…
with /\s\s*$/. Although these two regexes are functionally identical, Firefox provides additional optimization for regexes that start with a nonquantified token. In other browsers, the difference is less significant or is optimized differently altogether. However
…
to replace all matches rather than just the first (it will match twice when its target contains both leading and trailing whitespace). This * Tested in Firefox versions 2, 3, and 3.5. 100 | Chapter 5: Strings and Regular Expressions isn’t a terrible approach, but it’s slower than using
…
evaluating intermediate characters (although backtracking positions must still be recorded), and then backtracks as appropriate. Unfortunately, this method is String Trimming | 101 considerably slower in Firefox and Opera 9, so at least for now, using two substitutions still holds up better cross-browser. // trim 5 String.prototype.trim = function() { return
…
\S+)—helps a bit, slashing roughly 20%–45% off the time needed in Opera, IE, and Chrome, along with much slighter improvements in Safari and Firefox. Still, a noncapturing group can’t redeem this implementation. Note that the outer group cannot be converted to a noncapturing group since it is referenced
…
million statements; this limit is stored in a Windows registry setting called HKEY_CURRENT_USER\Software\Microsoft\InternetExplorer\Styles\MaxScriptStatements. The Browser UI Thread | 109 • Firefox has a default limit of 10 seconds; this limit is stored in the browser’s configuration settings (accessible by typing about:config in the address
…
contain at least one item when the timer function executes, so a post-test loop makes more sense than a pretest one. When run in Firefox 3, this function processes an array of 1,000 items, where process() is an empty function, in 38–43 milliseconds; the original processArray() function
…
web workers API has been split out into its own specification ( http://www.w3.org/TR/workers/); web workers have already been implemented natively in Firefox 3.5, Chrome 3, and Safari 4. Web workers represent a potentially huge performance improvement for web applications because each new worker spawns its
…
allows you to pass strings using postMessage(). The specification was updated after that point to allow serializable data to be passed through, which is how Firefox 3.5 implements workers. Loading External Files Loading extra JavaScript files into a worker is done via the importScripts() method, which accepts one or more
…
, so you must also write fallback code using the older style of DOM traversal. At this time, DOM Level 3 XPath has been implemented by Firefox, Safari, Chrome, and Opera. Internet Explorer 8 has a similar but slightly less advanced interface. Response sizes and parse times Let’s take a
…
JSON and allow you to pass in a function that can be used to filter or transform the results. Currently this method is implemented in Firefox 3.5, Internet Explorer 8, and Safari 4. Most JavaScript libraries contain JSON parsing code that will call the native version, if present, or
…
that JavaScript Minification | 169 provides a mapping between the obfuscated symbols and the original symbols. Nevertheless, this extension is not available on browsers other than Firefox, which may be a problem when debugging browser-specific code paths, and debugging still remains harder than with other, less aggressive minification tools. Buildtime Versus
…
which case the JavaScript code must itself handle the expiration. Finally, another technique is the use of the HTML 5 offline application cache, implemented in Firefox 3.5, Safari 4.0, and on the iPhone beginning with iPhone OS 2.1. This technology relies on a manifest file listing the
…
a debug build process. Always use uncompressed versions of your scripts for debugging and profiling. This will ensure that your functions are easily identifiable. Firebug Firefox is a popular browser with developers, partially due to the Firebug addon (available at http://www.getfirebug.com/), which was developed initially by Joe Hewitt
…
guaranteed to have its dependencies ready prior to execution. The gaps between scripts may indicate script blocking. Newer browsers such as Safari 4, IE 8, Firefox 3.5, and Chrome have addressed this by allowing parallel downloading of scripts but blocking execution, to ensure dependencies are ready. Although this allows the
…
insights into the overall loading and execution of the initial page view. This tool was originally developed internally at Yahoo! by Steve Souders as a Firefox addon (via GreaseMonkey). It has been made available to the public as a Firebug addon, and is maintained and updated regularly by Yahoo! developers.
…
dynaTrace Ajax Edition The developers of dynaTrace, a robust Java/.NET performance diagnostic tool, have released an “Ajax Edition” that measures Internet Explorer performance (a Firefox version is coming soon). This free tool provides an end-to-end performance analysis, from network and page rendering to runtime scripts and CPU usage
…
object anonymous functions members, 27 about, 182 bracket notation versus dot notation, 31 YUI Profiler, 181 browsers, 1 Apache Ant, 163, 173 (see also Chrome; Firefox; IE; Safari) Apache web server, ExpiresDefault directive, call stack limits, 74 172 DOM and JavaScript implementations, 35 APIs DOM scripting, 35 console API: Firebug, 184
…
–59 collection elements, 45 access document structure, 46–50 HTML collections, 42–46 browsers, 35 combining JavaScript files, 165 cloning nodes, 41 compile-time folding, Firefox, 84 event delegation, 57 compression, 170 HTML collections, 42–46 concat method, 86 innerHTML, 37–40 concatenating strings, 40, 81–87 repaints and reflows,
…
compression, 169, 170 combining JavaScript files, 165 loading external files, 122 H preprocessing JavaScript files, 166 handleClick() method, 108 Firebug, 183–186 hasOwnProperty() method, 28 Firefox headers compile-time folding, 84 Expires headers, 146 time limits, 110 HTTP headers, 146 flow control, 61–80 :hover, IE, 57 conditionals, 68–73 HTML
…
–79 local variables, 45 flows (see reflows) HTML, data format, 141 flushing render tree changes, 51 HTTP headers, Ajax, 146 folding, compile-time folding and Firefox, 84 for loops, 62 for-in loops, 62, 63 I forEach() method, 67 idempotent action, 127 Function() constructor, 151 identifier resolution, scope, 16–21
…
if-else Versus switch Optimizing if-else Lookup Tables Recursion Call Stack Limits Recursion Patterns Iteration Memoization Summary �� String Concatenation Plus (+) and Plus-Equals (+=) Operators Firefox and compile-time folding Array Joining String.prototype.concat Regular Expression Optimization How Regular Expressions Work Understanding Backtracking Alternation and backtracking Repetition and backtracking Runaway
Founders at Work: Stories of Startups' Early Days
by Jessica Livingston · 14 Aug 2008 · 468pp · 233,091 words
. . . . . . . . . . . . . . . . . . . . . . . . 345 CHAPTER 26 STEPHEN KAUFER TripAdvisor. . . . . . . . . . . . . . . . . . . . . . . . . . . . . 361 CHAPTER 27 JAMES HONG HOT or NOT . . . . . . . . . . . . . . . . . . . . . . . . . . . 377 CHAPTER 28 JAMES CURRIER Tickle . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 387 CHAPTER 29 BLAKE ROSS Firefox . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 395 Contents vii CHAPTER 30 MENA TROTT Six Apart . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 405 CHAPTER 31 BOB DAVIS Lycos . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 419 CHAPTER 32 RON GRUNER Alliant Computer Systems, Shareholder.com
…
stuff, but he had a good product sense and ended up doing a great deal of product work as well. The first version of the Firefox toolbar, he dealt with, for example. Livingston: What were some of the biggest technical problems that you encountered? Schachter: Scaling, inevitably. Scaling, dealing with bandwidth
…
and every product we have here because there was no overlap. C H A P T E 29 R Blake Ross Creator, Firefox Blake Ross and Dave Hyatt started Firefox as a side project while working at the Mozilla Foundation. They were working to revive the struggling Netscape browser, but became frustrated
…
, simple, and reliable. In 2002, they launched the initial version, called Phoenix, and in 2004 they released Firefox 1.0, which was an instant hit. Like a lot of things described in this book, Firefox was something new. It was an open source project run like a startup, both in the concern
…
for the end user and in the attention paid to marketing. The results were impressive: Firefox has cut into the formerly overwhelming market share of Internet Explorer, and dominates among technical users. In 2005, Ross took a leave from Stanford University
…
to start a startup with fellow Firefox developer Joe Hewitt. Livingston: Tell me about how Firefox got started. Ross: Firefox grew out of Mozilla, which itself has a very long history that I won’t go into now. I personally
…
. There were search buttons everywhere, advertisements everywhere. It was a mess. The culture didn’t focus on users. It was painful to be working there. Firefox was more a response to our experience at Netscape than to the dominant browser, Internet Explorer. Explorer had basically been abandoned at that point; in
…
2001, Microsoft disbanded the IE team. So we started Firefox as a way to work on the browser that we knew we could make if we weren’t being controlled by marketing, sales, and all
…
of the name. We just went through Fireanything names for a couple of months, and somebody came up with Firefox, which is actually the Chinese name for a red panda. Livingston: Were the Firefox developers all in different places? Ross: When we first started doing it, we were all at Netscape. Then
…
and I still collaborate through IM on Parakey, even though we’re about 20 minutes apart, because we’re so used to that environment from Firefox. It’s just so much faster to collaborate online than it is for him to drive down to me or me to drive up to
…
. Livingston: Did he leave Apple? Ross: No. He still works on Safari right now. He did Firefox and then went off to Apple. Livingston: So then it was just a few of you. Ross: The Firefox team is always changing. It’s not fair to say there are just a few of
…
’re based on Mozilla, which obviously has dozens of developers, and there are a lot of developers working on Gecko, the core layout engine. The Firefox team itself—the people worrying about everything wrapped around the engine and working on the separate fork of the code base—was always about four
…
. Now there are a lot more, obviously, because it’s the main source tree. All those people that were working on Mozilla now work on Firefox. Livingston: What was the first turning point when you knew you were really onto something? Ross: I think it was when we put out our
…
of Netscape—they made technology and Netscape distributed it. When Netscape said goodbye, Mozilla didn’t really have any kind of major distributor anymore. As Firefox matured, Mozilla decided that they could try to distribute it directly to the user without having to go through a middleman like Netscape. At that
…
organization had to cater to more users or potentially collapse. Livingston: As you were working on this, did you worry about competitive threats? Ross: No, Firefox was very different from traditional startups. Companies usu- ally worry about competition for financial reasons, but when we did
…
Firefox, money was just always sort of there. There were donations, seed money from AOL; we eventually got this Google deal, but it wasn’t a
…
’t crunch numbers or conduct market analysis; we relaxed and followed our gut. There’s a lot more pressure now with Parakey. People expect another Firefox or something like that. Livingston: People must have high expectations for you, which is not a bad thing, I suppose. Ross: Not a bad thing
…
and the competition, and that doesn’t seem like the right motivation to make a good product. Livingston: Looking back, what did people misunderstand about Firefox? Ross: Many die-hard open source fans misunderstood our goal. Usually, in an open source project, if you’re not a developer, it’s kind
…
of the world at large. I don’t think Mozilla did that, and the project stagnated at a few million users. Livingston: Do you think Firefox has reached the mainstream because it is better? Ross: There are a million different reasons. Many people think it’s easier. Others were just sort
…
plenty of legwork to reach the mainstream. It’s all word-of-mouth marketing. We have a site called Spread Firefox that Asa Dotzler and I started in 2004 when we launched Firefox. It’s basically a way to leverage the talents of people who are not coders. We said, “Instead of
…
every organization you’re a part of. How do we match you up with other people in your region and give you tools to spread Firefox?” That was a huge success. We’ve had over 250,000 people sign up. We also did an ad in the New York Times. Ten
…
thousand people donated between $10 and $30 each to buy two full-page facing ads in the New York Times when Firefox launched. Of course, that’s a couple hundred thousand dollars, but we didn’t have a marketing budget. That was all communityfunded, which is pretty
…
unusual for any software project, let alone an open source project. Livingston: So Firefox spread because the browser is better and through word of mouth? Ross: Yes. We don’t have people shaping a message or working the press
…
. It’s all been grassroots, word of mouth, done through Spread Firefox. It’s been interesting because we’ve seen about a dozen companies adopt the same model since then. There’s GoTrillian.com, SpreadOpenOffice.org—there
…
, and of course that’s just not true. It’s just really freeing not to be . . . We weren’t trying to strike it rich with Firefox. It’s open source and it’s free. We weren’t trying to take over the world; we had kind of modest goals, and it
…
capitalists or marketing or sales. Just product and users, all day every day. Blake Ross 401 Livingston: You were pretty young when you worked on Firefox. Was there anything you found you were better at than you thought? Ross: I thought marketing was something that required a degree and formal experience
…
with professional marketers who try to “craft” the “message” and all that junk. Livingston: What surprised you most? Ross: How easy it was to get Firefox to take off, at least in light of the death knell people had been sounding for years. We’d been hearing forever that nobody downloads
…
ignored all that and did it anyway, and it worked. It’s a bit harder to take analysts and other “industry insiders” seriously now, because Firefox proved them wrong. There are a lot of people in the industry who aren’t actually the ones writing the code or contributing to the
…
. One analyst has already announced he’s “skeptical” about Parakey and he barely even knows what it is, let alone tried it out. Smells like Firefox all over again. Those kinds of comments are so motivating. I love the challenge. We talked to plenty of people at the very beginning of
…
Firefox. It was obvious that people were not happy with their browser, and it was very clear that, if we could do something better, we might
…
weird is that I didn’t really talk to anyone I knew personally throughout the course of Firefox development. My parents and my friends—most of them didn’t really know I was working on Firefox until it came out and there was the Business 2.0 article. That’s when everyone
…
was like, “Wait, you work on Firefox?” They knew I “did something” with computers, but . . . Livingston: Your parents didn’t know? Ross: Kind of. I think they knew I worked on Mozilla.
…
They knew I worked at Netscape, so they knew I worked in browsers, but they didn’t really know my involvement in Firefox until they read about it in a magazine. Which is kind of how I prefer it, because it’s much easier to spend a couple
…
at Netscape, Joe and I were always shooting the breeze about how terrible software was and what we would change if we could. After some Firefox press hit, we started getting emails from investors saying, “We want to meet.” And we’d think, “Meet about what? It’s an open source
…
well go for it.” Livingston: Do you have a name? Ross: We’re calling it Parakey for now, but who knows if it will stick. Firefox was our fourth name. Livingston: Can you tell me about any of the challenges you’ve faced? Ross: One thing is just time. Whenever I
…
. We’re starting to push people away to give us space to work, but in some respects it would be so much easier if the Firefox thing hadn’t happened. We should be setting our own timeline, but people are already waiting for what we’re going to do next, so
…
also found “programmer” to work well in many situations. But we’ll have our day. Livingston: Are there any lessons that you learned in the Firefox days that you are applying to this new startup? Ross: One is to make sure you are always in communication with the people who are
…
refining what you are doing. I also learned how you build up the right kind of buzz about your product in an honest way. With Firefox, we catered to the bloggers first, even though they weren’t our primary target audience. Once you get the prominent bloggers to pick up the
…
, then they start to cover the story, and they actually make it kind of a self-fulfilling prophecy. They write that “everyone is talking about Firefox” when, of course, mainstream users haven’t even heard of it yet. But they are going to, now that the New York Times wrote about
…
Feynman, Carl, 275–276 Feynman, Richard, 266 Filo, David, 127 financial institutions, 11–12 financing, 4, 299–302. See also angel investors Firefox, 395–404 Firefox 1.0, 395 Firefox toolbar, 226 FirePower Systems, 17–18 flagging, 251–252 flash card program, 52 Fletcher, Mark, 233–246 Flickr, 257–264 floppy disk drive
…
, 444 Sony, 179, 182–184, 199, 201 Sousan, Andre, 43 space-based technology, 147–148 Spencer, Graham, 61, 62, 71 Spolsky, Joel, 345–360 Spread Firefox site, 400 Squared Circle group, 262 Stanford, 134 Star workstation, 289 start-up like projects, 168 startup culture, 16 startup financing, 450, 451, 453 state
Beautiful Testing: Leading Professionals Reveal How They Improve Software (Theory in Practice)
by Adam Goucher and Tim Riley · 13 Oct 2009 · 351pp · 123,876 words
the basis for your own. For example, Jesse Ruderman of Mozilla fame has written a JavaScript fuzzer (jsfunfuzz) that has found security vulnerabilities in both Firefox and Opera.† Inspired by the success of jsfunfuzz, I wrote my own custom fuzzer to test Gnumeric’s formula and function parser to make sure
…
plan and the design of test cases. Many of the test cases come from open source communities. For example, most of the test cases for Firefox are from the Mozilla community, which uses a test case management tool called Litmus. For most of the desktop applications, although 100% of the test
…
. For example, a team building a web portal and service may decide that valid test platforms are the last two versions of Internet Explorer and Firefox, and the latest versions of Chrome, Safari, and Opera. It’s likely that not every test will need to run on every platform. For some
…
already know that this part of the code is not testable using the existing test suite. CHANGE-CENTRIC TESTING 151 Example 2 Look at the Firefox browser instrumentation and test cases execution example from https://wiki .mozilla.org/QA:CodeCoverage. Once an instrumented module is tested using the planned test cases
…
out the latest version of the code and rip through the story tests in all supported browsers: the newest and previous versions of Internet Explorer, Firefox, and Safari. I also try odd combinations of characters, special characters, and, of course, straight text with no spaces. 222 CHAPTER SIXTEEN After story tests
…
-link') ? true : false } catch(e) { false }, 30000 ok 16 - click, st-edit-button-link § Firebug and the Web Developer plug-in are free for Mozilla Firefox. The IE developer toolbar is a good alternative for Internet Explorer. 226 CHAPTER SIXTEEN ok 17 - wait_for_condition, try { selenium.isVisible('st-save-button
…
in a way that is consistent with the vision of the Internet we wish to create.* The most notable example of our work is the Firefox browser, but there are many other products built from the same base; Thunderbird, Komodo, Miro, and Songbird are some of the more well-known examples
…
submit test markup or a link to a page that contains the navigation code. If the test markup and its previous renderings change between two Firefox milestone releases, we will send you a notice. We are also submitting our reference tests to various W3C groups that are working on interoperable test
…
/projects/fusil. It’s written in Python and comes with a set of so-called fuzzing projects that cover some popular applications such as ClamAV, Firefox, and MPlayer. It’s also relatively easy to create other fuzzers or adapt Fusil to your own needs. The framework provides many ways to detect
…
CLI Running: windmill 'browser' 'url' test=test_file.py (or a directory) Loading: windmill 'browser' 'url' loadtest=test_file.py (or a directory) Ex. windmill firefox http://www.google.com test=test_googlesearch.py EXAMPLE 21-4. Example of running and loading Python tests from the shell windmill shell 'browser' 'url
…
the directory files to run. EXAMPLE 21-5. Example of running JavaScript tests from the CLI windmill 'browser' 'url' jsdir=js_tests_dir ex. windmill firefox http://www.google.com jsdir=js_tests_dir 290 CHAPTER TWENTY-ONE EXAMPLE 21-6. Example of running JavaScript tests from the shell windmill shell
…
it (Example 21-7). EXAMPLE 21-7. Example shell session interacting with the browser zsh% windmill shell firefox http://www.google.com (Start the Windmill server in shell mode) Started ['/Applications/Firefox.app/Contents/MacOS/firefox-bin', '-profile', '/var/folders/YO/YOAvf2hSGt0+VnBIAKuImE+++TM/-Tmp-/tmpy0xq6y.mozrunner', 'http://www.google.com/windmill-serv
…
Model (DOM) and JavaScript. Firebug Lite Firebug Lite is integrated into the Windmill IDE. It provides much of the same functionality found in the Firebug Firefox plug-in and is available on all of the browsers, in both your testing window and the Windmill IDE. The main goal of Firebug is
…
it didn’t scale up from there, because the list had to be predefined. The purpose of this tool was to load the pages in Firefox and check for crashes and assertions. Memory leaks, assertions, and crashes were all recorded into a big logfile. Crashes were indicated via the exit status
…
that was output into the log for each crashing top site. The following is a logfile example: 2009-04-25-14-41-02+0200,firefox,1.9.1,debug,darwin,tomcat2.local, tests_mozilla.org_top-sites.log. With text editor tools or commands such as grep, we could search
…
generate and manage larger lists of URLs—several orders of magnitude larger! Another nagging issue was that we had problems with interaction between Firefox rendering web pages and Firefox extensions. How could we load extensions so that they were in the mix? The Tools Merge and Evolve So we were looking for
…
• Manage those large sets of URLs in the context of the test framework (Spider) • Launch a selected version of Firefox, open a page, collect memory leak and assertion information, and then quit Firefox (Sisyphus) • Load extensions (Sisyphus) • Continue across crashes (Sisyphus) • In addition to launching web pages, spider through their links for
…
tried to scale the tests, we simply wanted to find a better way of running the leak tests. We needed something that would start Firefox, load a website, and then quit Firefox. Running a debug build provided the functionally to collect memory leak and assertion information, and to continue testing even if
…
Firefox crashed. We wondered how to save a logfile. It turned out there was a preference to have leak data piped into a logfile. The next
…
challenge was to be able to run this with different versions of Firefox. We had a special TraceMonkey build (TraceMonkey adds native-code compilation to Mozilla’s JavaScript engine) along with trunk, 3.0, and 3.5 builds
…
about extension testing. We had had some problems with people thinking that Firefox was leaking badly, and frequently the problem turned out to be extensions leaking. Firefox wasn’t innocent of leaks, but we had come a long way in Firefox § See the “Free Download Top 1,000,000 Sites (Updated Daily)” link
…
/topsites. 298 CHAPTER TWENTY-TWO 3.0 and 3.5 in cleaning this up. Consequently, the most likely source of leaks had dramatically shifted from Firefox itself to extensions. At that point in time, Sisyphus just ran a list of URLs and could spider them to any depth desired. We added
…
/nsDebugImpl.cpp#254. The Nitty-Gritty OK, so enough about the history. How does it work? Sisyphus doesn’t install Firefox, but instead can launch any specific previously installed version of Firefox. This is good, in a way, as it allows you to easily substitute custom builds, such as special patched builds
…
, install it, and start throwing websites at it. Currently, the sequence is: pick an installed Firefox ‖ See “Testing Extensions and Firefox for Memory Leaks with a Debug Build” at https://wiki.mozilla.org/ MozillaQualityAssurance:Home_Page:Firefox_3.0_TestPlan:Leaks:LeakTesting-How-To and “Debugging memory leaks” at https://developer.mozilla.org
…
/En/Debugging_memory_leaks. TESTING ONE MILLION WEB PAGES 299 build, launch Firefox, install extensions, run the
…
tests, exit Firefox, and repeat, a million times if you like. The command line looks like this: ./tester.sh -t "$TEST_DIR/tests/mozilla.org
…
/top-sites/test.sh \ -s $TEST_DIR/tests/mozilla.org/top-sites/global1000.txt -D 0 -r" \ firefox 1.9.1-tracemonkey debug -t -s -D -r = which tests to run = file containing URLs to test with is how deep to spider (0
…
= just load the current URL) = which revision of Firefox to test The following are some key environment variables: • XPCOM_DEBUG_BREAK=stack (capture the stack with assertions) • XPCOM_MEM_LOG=1 (log leak data
…
page is functionally correct is a different issue and has entire books dedicated to its treatment. We are just looking for the basic ability of Firefox to deal with all the crazy JavaScript, HTML, and CSS out there and load these pages. Does JavaScript throw any exceptions? Is the page causing
…
our community. The TraceMonkey branch is an example of how we have addressed this, so the long-haul tests are saved for the maintenance branch (Firefox 3.0 as of this writing). We also have a 150,000-URL set that takes three to four weeks to run. We use the
…
Board. E MILY C HEN is a software engineer working on OpenSolaris desktop. Now she is responsible for the quality of Mozilla products such as Firefox and Thunderbird on OpenSolaris. She is passionate about open source. She is a core contributor of the OpenSolaris community, and she worked on the Google
…
on testing projects. These days, he leads the Mozilla Test Development team concentrating on QA for the Gecko platform, which is the substrate layer for Firefox and many other applications. He is also an aspiring fiction writer. When not testing or writing, he loves to rock climb and surf everywhere from
…
–163 eXtensible Messaging and Presence Protocol (see XMPP) Extreme Programming (see XP) F failure analysis, 114 false negatives, 281 false positives, 281 Firebug Lite, 291 Firefox, testing with Sisyphus, 297 Fit, 177 FitNesse, 201 FIXME developer notes, 240 foreign languages, 237 Fusil tool, 125, 277 fuzzing (fuzz testing), 57 ClamAV, 276
…
scripted testing, 162, 165 scripting, 239 security, 59, 236 Selenium, 177, 293, 306 Selenium IDE, 311 session initialization, 97 Sisyphus, 297 extension testing with, 298 Firefox, operation on, 299 Slideshow, 229 SocialCalc, 230 Socialtext, 215 business purpose, 216 software process, 218 software development, 171–176 aesthetics and, 176 agile teams, 172
Test-Driven Development With Python
by Harry J. W. Percival · 10 Jun 2014 · 779pp · 116,439 words
find yourself a little confused, I’ll recommend a couple of guides at that point. Required Software Installations Aside from Python, you’ll need: The Firefox web browser A quick Google search will get you an installer for whichever platform you’re on. Selenium can actually drive any of the major
…
browsers, but Firefox is the easiest to use as an example because it’s reliably cross-platform and, as a bonus, is less sold out to corporate interests
…
up with the latest features. If you ever find Selenium misbehaving for some reason, the answer is often that it’s a new version of Firefox and you need to upgrade to the latest Selenium … Unless you’re absolutely sure you know what you’re doing, don’t use a virtualenv
…
help: 4 | Chapter 1: Getting Django Set Up Using a Functional Test www.it-ebooks.info functional_tests.py. from selenium import webdriver browser = webdriver.Firefox() browser.get('http://localhost:8000') assert 'Django' in browser.title Adieu to Roman Numerals! So many introductions to TDD use Roman numerals as an example
…
tests. For now, it’s enough to assure ourselves that we understand what it’s doing: • Starting a Selenium webdriver to pop up a real Firefox browser window • Using it to open up a web page which we’re expecting to be served from the local PC • Checking (making a test
…
open localhost:8000, and then the Python error message should appear. And then, you will probably be irritated at the fact that it left a Firefox window lying around your desktop for you to tidy up. We’ll fix that later! Obey the Testing Goat! Do Nothing Until You Have a
…
functional_tests.py $ Not much action on the command line, but you should notice two things: firstly, there was no ugly AssertionError and secondly, the Firefox window that Selenium popped up had a different-looking page on it. Well, it may not look like much, but that was our first ever
…
next visit. Open up functional_tests.py and write a story a bit like this one: from selenium import webdriver functional_tests.py. browser = webdriver.Firefox() # Edith has heard about a cool new online to-do app. She goes # to check out its homepage browser.get('http://localhost:8000') # She notices
…
’t very helpful—it would be nice if the test told us what it actually found as the browser title. Also, it’s left a Firefox window hanging around the desktop, it would be nice if this would clear up for us automatically. One option would be to use the second
…
like: assert 'To-Do' in browser.title, "Browser title was " + browser.title And we could also use a try/finally to clean up the old Firefox window. But these sorts of problems are quite common in testing, and there are some ready-made solutions for us in the standard library’s
…
use that! In functional_tests.py: functional_tests.py. from selenium import webdriver import unittest class NewVisitorTest(unittest.TestCase): # def setUp(self): # self.browser = webdriver.Firefox() def tearDown(self): # self.browser.quit() def test_can_start_a_list_and_retrieve_it_later(self): # # Edith has heard about a cool new online
…
’re a bit like a try/except, in that tearDown will run even if there’s an error during the test itself.1 No more Firefox windows left lying around! We use self.assertIn instead of just assert to make our test assertions. unittest provides lots of helper functions like this
…
in 'Welcome to Django' --------------------------------------------------------------------Ran 1 test in 1.747s FAILED (failures=1) That’s a bit nicer isn’t it? It tidied up our Firefox window, it gives us a nicely formatted report of how many tests were run and how many failed, and the assertIn has given us a
…
! Implicit waits There’s one more thing to do at this stage: add an implicitly_wait in the setUp: [...] def setUp(self): self.browser = webdriver.Firefox() self.browser.implicitly_wait(3) functional_tests.py. def tearDown(self): [...] This is a standard trope in Selenium tests. Selenium is reasonably good at waiting
…
.py index d333591..b0f22dc 100644 --- a/functional_tests.py +++ b/functional_tests.py @@ -1,6 +1,45 @@ from selenium import webdriver +import unittest -browser = webdriver.Firefox() -browser.get('http://localhost:8000') +class NewVisitorTest(unittest.TestCase): -assert 'Django' in browser.title + def setUp(self): + self.browser = webdriver
…
.Firefox() + self.browser.implicitly_wait(3) + + def tearDown(self): + self.browser.quit() [...] Now let’s do a: $ git commit -a The -a means “automatically add any
…
selenium import webdriver from selenium.webdriver.common.keys import Keys import unittest functional_tests.py. class NewVisitorTest(unittest.TestCase): def setUp(self): self.browser = webdriver.Firefox() self.browser.implicitly_wait(3) def tearDown(self): self.browser.quit() def test_can_start_a_list_and_retrieve_it_later(self): # Edith has heard
…
a new browser session to make sure that no information ## of Edith's is coming through from cookies etc # self.browser.quit() self.browser = webdriver.Firefox() # Francis visits the home page. There is no sign of Edith's # list self.browser.get(self.live_server_url) page_text = self.browser.find
…
! It works! Mwahahahaha. That’s pretty much it! Along the way, I had to fight pretty hard, including debugging Ajax requests by hand in the Firefox console (see Figure 15-2), catching infinite pagerefresh loops, stumbling over several missing attributes on my custom user model (be‐ cause I didn’t read
…
bug, which thankfully turned out to be irrelevant. Exploratory Coding, aka “Spiking” www.it-ebooks.info | 249 Figure 15-2. Debugging Ajax requests in the Firefox network console If it’s not working when you try it manually, and you see “audience mismatch” errors in the console, make sure you’re
…
for something to happen. Listings for them follow. I found the ID of the Persona login box by opening the site manually, and using the Firefox debug toolbar (Ctrl+Shift+I). See Figure 15-3. Rather than using a “real” email address and having to click through their authentication screens, we
…
the initialize function is being called with: var initialize = function (navigator) { console.log(navigator); }; accounts/static/accounts.js (ch15l028). window.Superlists = { Accounts: { initialize: initialize } }; In Firefox and I believe Chrome also, you can use the shortcut Ctrl-Shift-I to bring up the JavaScript console, and see the [object Object] that
…
) That was a puzzler—that “missing argument 1 when calling function navigator.id.watch” took me a while to figure out. Turns out that, in Firefox, .watch is a function on every object. We’ll need to mock it out in the previous test too: accounts/static/tests/tests.html. test
…
def tearDownClass(cls): if not cls.against_staging: super().tearDownClass() def setUp(self): if self.against_staging: reset_database(self.server_host) # self.browser = webdriver.Firefox() self.browser.implicitly_wait(3) Instead of just storing cls.server_url, we also store the server_host and against_staging attributes if we detect
…
user@server:$ sudo apt-get install jenkins While we’re at we’ll install a few other dependencies: user@server:$ sudo apt-get install git firefox python3 python-virtualenv xvfb At the time of writing, the shiningpanda plugin was incompatible with Python 3.4. It works fine with Python 3.3
…
not the main app. Now what? File "/var/lib/jenkins/shiningpanda/jobs/ddc1aed1/virtualenvs/d41d8cd9/lib/python3. line 100, in _wait_until_connectable self._get_firefox_output()) selenium.common.exceptions.WebDriverException: Message: 'The browser appears to have exited before we could connect. The output was: b"\\n(process:19757): GLib-CRITICAL
…
== 0\' failed\\nError: no display specified\\n"' Setting Up a Virtual Display so the FTs Can Run Headless As you can see from the traceback, Firefox is unable to start because the server doesn’t have a display. There are two ways to deal with this problem. The first is to
…
actual browsers. The alternative is to set up a virtual display: we get the server to pretend it has a screen attached to it, so Firefox runs happily. There’s a few tools out there to do this; we’ll use one called “Xvfb” (X Virtual Framebuffer)3 because it’s
…
_WAIT = 5 SCREEN_DUMP_LOCATION = os.path.abspath( os.path.join(os.path.dirname(__file__), 'screendumps') ) class FunctionalTest(StaticLiveServerCase): [...] def setUp(self): self.browser = webdriver.Firefox() self.browser.implicitly_wait(DEFAULT_WAIT) Now we can rerun the test to confirm it still works locally: $ python3 manage.py test functional_tests.test
…
_browser = self.browser self.addCleanup(lambda: quit_if_possible(edith_browser)) # Her friend Oniciferous is also hanging out on the lists site oni_browser = webdriver.Firefox() self.addCleanup(lambda: quit_if_possible(oni_browser)) self.browser = oni_browser self.create_pre_authenticated_session('oniciferous@example.com') # Edith goes to the home
…
to use PythonAnywhere to follow along with this book? Here’s a few notes on how to get things working, specifically with regards to Selenium/Firefox tests, running the test server, and screenshots. If you haven’t already, you’ll need to sign up for a PythonAnywhere account. A free one
…
should be fine. Running Firefox Selenium Sessions with Xvfb The next thing is that PythonAnywhere is a console-only environment, so it doesn’t have a display in which to
…
pop up Firefox. But we can use a virtual display. In Chapter 1, when we write our first ever test, you’ll find things don’t work as
…
expected. The first test looks like this, and you can type it in using the PythonAnywhere editor just fine: from selenium import webdriver browser = webdriver.Firefox() browser.get('http://localhost:8000') assert 'Django' in browser.title But when you try and run it (in a Bash console), you’ll get an
…
(most recent call last): File "tests.py", line 3, in <module> browser = webdriver.Firefox() File "/usr/local/lib/python3.3/site-packages/selenium/webdriver/firefox/webdrive self.binary, timeout), File "/usr/local/lib/python3.3/site-packages/selenium/webdriver/firefox/extensio self.binary.launch_browser(self.profile) File "/usr/local/lib/python3.3
…
/site-packages/selenium/webdriver/firefox/firefox_ self._wait_until_connectable() File "/usr/local/lib/python3.3
…
/site-packages/selenium/webdriver/firefox/firefox_ 409 www.it-ebooks.info self._get_firefox_output()) selenium.common.exceptions.WebDriverException: Message: 'The browser appears to have exited before we
…
: Error: no display specified\n' The fix is to use Xvfb, which stands for X Virtual Framebuffer. It will start up a “virtual” display, which Firefox can use even though the server doesn’t have a real one. If, instead, you see "ImportError, no module named selenium“, do a pip3 install
The Web Application Hacker's Handbook: Finding and Exploiting Security Flaws
by Dafydd Stuttard and Marcus Pinto · 30 Sep 2007 · 1,302pp · 289,469 words
/1.1 Host: mdsec.net User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-GB; rv:1.9.2.10) Gecko/20100914 Firefox/3.6.10 Accept: text/html, application/xhtml+xml, application/xml; q=0.9, */ *; q=0.8 Accept-Language: en-gb,en;q=0.5
…
situation, an eavesdropper cannot intercept the user's credentials but may still capture the session token. The Firesheep tool, released as a plug-in for Firefox, makes this an easy process. ■ Some applications use HTTP for preauthenticated areas of the site, such as the site's front page, but switch to
…
Internet Explorer do not include a Referer header when following off-site links contained in a page that was accessed over HTTPS. In this situation, Firefox includes the Referer header provided that the off-site link is also being accessed over HTTPS, even if it belongs to a different domain. Hence
…
was written in March 2011, and the attacks described all work on at least one of the following: ■ Internet Explorer version 8.0.7600.16385 ■ Firefox version 3.6.15 Script Tags Beyond directly using a <script> tag, there are various ways in which you can use somewhat convoluted syntax to
…
. However, on later versions of IE, the following can be used to the same effect: <x style=behavior:url(#default#time2) onbegin=alert(1)> The Firefox browser used to allow CSS-based attacks via the mo z-binding property, but restrictions made to this feature mean that it is now less
…
■ Attacking Users: Cross-Site Scripting 461 According to specifications, <base> tags should appear within the <head> section of the HTML page. However, some browsers, including Firefox, accept <base> tags appearing anywhere in the page, considerably widening the scope of this attack. Space Following the Tag Name Several characters can replace the
…
, which uses ECMAScript for XML (E4X) syntax, does not contain a valid opening script tag but nevertheless executes the enclosed script on current versions of Firefox: <script<{alert(1)}/></script> 464 Chapter 12 i Attacking Users: Cross-Site Scripting HI J In several of the filter bypasses described, the attack results
…
in an unusual situation, it can be helpful to view the virtual HTML that the browser constructs out of the server's actual response. In Firefox, you can use the WebDeveloper tool, which contains a View Generated Source function that performs precisely this task. Character Sets In some situations, you can
…
)');</script> <script>eval(String.fromCharCode(97,108,101,114,116,40,49,41));</script> <script>eval(atob('amF2YXNjcmlwdDphbGVydCgxKQ'));</script> The final example, which works on Firefox, allows you to decode a Base64-encoded command before passing it to eval. Alternatives to eval If direct calls to the eval command are not
…
URL encoding of parameter names or values. Although some browsers do not honor this specification, it is properly honored by current versions of Internet Explorer, Firefox, and Opera. The behavior described means that you can send arbitrary data in the message body, provided that there is at least one equals sign
…
markup to define a new namespace that is mapped to XHTML, causing the browser to parse uses of that namespace as HTML. For example, when Firefox processes the following response, the injected script is executed: HTTP/1.1 200 Ok Content-Type: text/xml Chapter 12 ■ Attacking Users: Cross-Site Scripting
…
-Site Scripting 487 HTML can be embedded in various locations within a valid image file, including the comment section of the image. Several browsers, including Firefox and Safari, happily render an image file as HTML. The binary parts of the image are displayed as junk, and any embedded HTML is displayed
…
code. In this situation, it can be beneficial to use a JavaScript debugger to monitor the script's execution dynamically. The FireBug extension to the Firefox browser is a full-fledged debugger for client-side code and content. It enables you to set breakpoints and watches on interesting code and data
…
Chapter 3, JSON is a flexible notation for representing arrays of data and can be consumed directly by a JavaScript interpreter. In older versions of Firefox, it was possible to perform a cross-domain script include attack to capture this data by overriding the default Array constructor in JavaScript. For example
…
values, and invokes the attacker's custom setter function for each value in the array. Since this type of attack was discovered in 2006, the Firefox browser has been modified so that custom setters are not invoked during array initialization. This attack is not possible in current browsers. 522 Chapter 13
…
to ECMAScript languages (including JavaScript) that adds native support for the XML language. At the present time, it is implemented in current versions of the Firefox browser. Although it has since been fixed, a classic example of cross-domain data capture can be found in
…
Firefox's handling of E4X. As well as allowing direct usage of XML syntax within JavaScript, E4X allows nested calls to JavaScript from within XML: var
…
in a {. . .} block that contains sensitive data. For example: <html> <head> <script> function setNonceO { nonce = '222230313740821'; } </script> </head> <body> </body> </html> In earlier versions of Firefox, it was possible to perform a cross-domain script include of a full HTML response like this and have some of the embedded JavaScript execute
…
to be checked. 4. To verify that sensitive information is being cached, use a default installation of a standard browser, such as Internet Explorer or Firefox. In the browser's configuration, completely clean its cache and all cookies, and then access the application pages that contain sensitive data. Review the files
…
this exact path and have hidden folders showing, or browse to the folder just listed from the command line. ■ Firefox (on Windows)—c: XDocuments and Settings\username\ Local SettingsXApplication DataXMozillaXFirefox\ Prof ilesXprofile namexcache ■ Firefox (on Linux)—/ .mozilla/f irefox/ profile name/cache 552 Chapter 13 Attacking Users: Other Techniques Browsing History Most
…
-based input fields, which may store sensitive data such as credit card numbers, usernames, and passwords. Internet Explorer stores autocomplete data in the registry, and Firefox stores it on the file system. As already described, in addition to being accessible by local attackers, data in the autocomplete cache can be retrieved
…
in LSOs is shared between different browser types, provided that they have the Flash extension installed. HACK STEPS 1. Several plug-ins are available for Firefox, such as BetterPrivacy, which can be used to browse the LSO data created by individual applications. 2. You can review the contents of the raw
…
the like. Chapter 20 A Web Application Hacker's Toolkit 749 Figure 20-1: HttpWatch analyzes the HTTP requests issued by Internet Explorer Fi refox Firefox is currently the second most widely used web browser. By most estimates it makes up approximately 35% of the market. The majority of web applications
…
work correctly on Firefox; however, it has no native support for ActiveX controls. There are many subtle variations among different browsers' handling of HTML and JavaScript, particularly when they
…
defenses against bugs such as cross-site scripting mean that your attacks are not effective against every browser platform. Firefox's popularity is sufficient that Firefox-specific XSS exploits are perfectly valid, so you should test these against Firefox if you encounter difficulties getting them to work against IE. Also, features specific to
…
Firefox have historically allowed a range of attacks to work that are not possible against IE, as described in Chapter 13. 750 Chapter 20 A Web
…
Application Hacker's Toolkit A large number of browser extensions are available for Firefox that may be useful when attacking web applications, including the following: ■ Http Watch is also available for Firefox. ■ FoxyProxy enables flexible management of the browser's proxy configuration, allowing quick switching, setting of different
…
Application Hacker's Toolkit 755 for addresses beginning with" box, remove these expressions. Click OK in all the dialogs to confirm the new configuration. ■ In Firefox, select Tools ^ Options A Advanced 'r Network 'r Settings. Ensure that the Manual Proxy Configuration option is selected. In the HTTP Proxy field, enter 127
…
application while allowing the browser to use its normal means of communicating with the problematic application. Numerous extensions are available for both Internet Explorer and Firefox that implement broadly similar functionality. We will illustrate one example of each. We recommend that you experiment with various options to find the one that
…
target that would not be possible using only a standard browser. Tamper Data Tamper Data, shown in Figure 20-15, is an extension to the Firefox browser. Anytime you submit a form. Tamper Data displays a pop-up showing all the request details, including HTTP headers and parameters, which you can
…
view and modify. Figure 20-15: Tamper Data lets you modify HTTP request details within Firefox Tam perlE TamperlE, shown in Figure 20-16, implements essentially the same functionality within the Internet Explorer browser as Tamper Data does on
…
Firefox. Chapter 20 A Web Application Hacker's Toolkit 775 TamperlE — Edit Request Figure 20-16: TamperlE lets you modify HTTP request details within Internet Explorer
…
feature. 12.2.6 Check for technology-specific local storage. 12.2.6.1 Check for Flash local objects using the BetterPrivacy plug-in for Firefox. 12.2.6.2 Check any Silverlight isolated storage in this directory: C:\Users\{username}\AppData\LocalLow\Microsoft\ SilverlightX 12.2.6.3 Check any
…
-152 decompiling, 139-150 bytecode, 139-141 bytecode obfuscation, 144-146 Java applets example, 146-150 JavaScript manipulating original bytecode, 144 source code, 142-144 Firefox, 750 hacker's methodology, 802-804 ActiveX controls, 804 debugger, 803-804 decompiling, 802-803 native client components, 153 same-origin policy, 525-527 Flash
…
strength, 192 validation, 193-195 web server and default, 670-671 hacker's methodology, 846 cross-domain data capture, 515-516 CSS injection, 517-519 Firefox, 521 HTML injection, 516-517 JavaScript hijacking, 519-520 E4X, 523-524 function callbacks, 520 JSON, 521 preventing, 524 variable assignment, 522 proxy services, 529
…
-452 IE, 479-481 web browsers, 479-481 financial services application logic flaws, 412-416 ASPs, 658 fingerprinting databases, SQL injection, 303-304 Firebug, 785 Firefox, 459 browser extensions, 750 cross-domain data capture, 521 Firesheep tool, 234 hacker's toolkit, 749-750 Ref errer header, 239 Firesheep tool
…
, Firefox, 234 firewalls, 12 alerts, 33 WAFs, NULL bytes, 460 first-order XSS. See reflected XSS 500 Internal Server Error, 49 brute-force techniques, 85 Index ■
…
Wget, 788 Firebug, 785 Hydra, 785-786 integrated testing suites, 751-773 components, 752-769 types, 751 Nikto, 785 web browsers, 748-750 Chrome, 750 Firefox, 749-750 IE, 748-749 Wikto, 785 Hammad, Sherief, 322 Harper, Allen, 634 Harris, Shon, 634 HEAD functions, 43 HEAD method, 265 heap overflows, 635
…
■ S-S 871 redirection attacks. See open redirection vulnerabilities referer-based access controls, 266 Ref err er header, 41-42 client-side data transmission, 122 Firefox, 239 XSS exploiting via, 475-476 reflected XSS, 434-438 Apache, 442 cookies, 437-438 delivering, 448-449 DOM XSS converted from, 472-473 exploiting
…
-561 threats to, 3 rapidly evolving, 11 XPath subverting logic of, 345-346 web archives, public information, 89-90 web browsers. See also browser extensions; Firefox; Internet Explorer attackers, 559-568 browsing history, 552 bugs, 563 capabilities, 5-6 DNS rebinding, 563-564 exploitation frameworks, 564-566 BeEF, 565-566 XSS
…
Shell, 566 hacker's toolkit, 748-750 Chrome, 750 Firefox, 749-750 IE, 748-749 integrated testing suites, intercepting proxies configuring, 752-755 XSS filters, 479-481 web container, Java, 53 web functionality client-side
HTML5 Cookbook
by Christopher Schmitt and Kyle Simpson · 13 Sep 2011 · 435pp · 62,013 words
Programming HTML5 Applications
by Zachary Kessin · 9 May 2011 · 210pp · 42,271 words
Jenkins Continuous Integration Cookbook
by Alan Berg · 15 Mar 2012 · 372pp · 67,140 words
The Art of Community: Building the New Age of Participation
by Jono Bacon · 1 Aug 2009 · 394pp · 110,352 words
Practical Ext JS Projects With Gears
by Frank Zammetti · 7 Jul 2009 · 602pp · 207,965 words
The Art of SEO
by Eric Enge, Stephan Spencer, Jessie Stricchiola and Rand Fishkin · 7 Mar 2012
The Architecture of Open Source Applications
by Amy Brown and Greg Wilson · 24 May 2011 · 834pp · 180,700 words
HTML5 Canvas
by Steve Fulton and Jeff Fulton · 2 May 2013 · 1,881pp · 178,824 words
Beautiful Architecture: Leading Thinkers Reveal the Hidden Beauty in Software Design
by Diomidis Spinellis and Georgios Gousios · 30 Dec 2008 · 680pp · 157,865 words
Gray Hat Python: Python Programming for Hackers and Reverse Engineers
by Justin Seitz · 15 Feb 2009 · 312pp · 52,762 words
Designing Interfaces
by Jenifer Tidwell · 15 Dec 2010
The Business of Platforms: Strategy in the Age of Digital Competition, Innovation, and Power
by Michael A. Cusumano, Annabelle Gawer and David B. Yoffie · 6 May 2019 · 328pp · 84,682 words
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
by Kevin Mitnick, Mikko Hypponen and Robert Vamosi · 14 Feb 2017 · 305pp · 93,091 words
Website Optimization
by Andrew B. King · 15 Mar 2008 · 597pp · 119,204 words
Reinventing Discovery: The New Era of Networked Science
by Michael Nielsen · 2 Oct 2011 · 400pp · 94,847 words
Ajax: The Definitive Guide
by Anthony T. Holdener · 25 Jan 2008 · 982pp · 221,145 words
Speaking JavaScript: An In-Depth Guide for Programmers
by Axel Rauschmayer · 25 Feb 2014 · 692pp · 95,244 words
Nagios: System and Network Monitoring, 2nd Edition
by Wolfgang Barth · 19 Aug 2009 · 996pp · 180,520 words
Producing Open Source Software: How to Run a Successful Free Software Project
by Karl Fogel · 13 Oct 2005
Html5 Boilerplate Web Development
by Divya Manian · 17 Nov 2012 · 193pp · 36,189 words
Python Network Programming Cookbook
by M. Omar Faruque Sarker · 15 Feb 2014 · 234pp · 57,267 words

The End of Big: How the Internet Makes David the New Goliath
by Nicco Mele · 14 Apr 2013 · 270pp · 79,992 words
Eloquent JavaScript: A Modern Introduction to Programming
by Marijn Haverbeke · 15 Nov 2018 · 560pp · 135,629 words
Pragmatic Guide to JavaScript
by Christophe Porteneuve · 15 Nov 2010 · 141pp · 9,896 words
The Icon Handbook
by Jon Hicks · 23 Jun 2011
Python for Unix and Linux System Administration
by Noah Gift and Jeremy M. Jones · 29 Jun 2009 · 603pp · 141,814 words
Data Wrangling With Python: Tips and Tools to Make Your Life Easier
by Jacqueline Kazil · 4 Feb 2016
Design for Hackers: Reverse Engineering Beauty
by David Kadavy · 5 Sep 2011 · 276pp · 78,094 words
In the Plex: How Google Thinks, Works, and Shapes Our Lives
by Steven Levy · 12 Apr 2011 · 666pp · 181,495 words
Designing Web Interfaces: Principles and Patterns for Rich Interactions
by Bill Scott and Theresa Neil · 15 Dec 2008 · 504pp · 67,845 words
The Debian Administrator's Handbook, Debian Wheezy From Discovery to Mastery
by Raphaal Hertzog and Roland Mas · 24 Dec 2013 · 678pp · 159,840 words
jQuery UI 1.8: The User Interface Library for jQuery
by Dan Wellman · 14 Aug 2011
The Wikipedia Revolution: How a Bunch of Nobodies Created the World's Greatest Encyclopedia
by Andrew Lih · 5 Jul 2010 · 398pp · 86,023 words
The Productive Programmer
by Neal Ford · 8 Dec 2008 · 224pp · 48,804 words
JQuery UI
by Eric Sarrion · 15 Feb 2012 · 280pp · 40,881 words
Interactive Data Visualization for the Web
by Scott Murray · 15 Mar 2013 · 186pp · 50,651 words
Originals: How Non-Conformists Move the World
by Adam Grant · 2 Feb 2016 · 410pp · 101,260 words
Ubuntu 15.04 Server with systemd: Administration and Reference
by Richard Petersen · 15 May 2015
Dreaming in Code: Two Dozen Programmers, Three Years, 4,732 Bugs, and One Quest for Transcendent Software
by Scott Rosenberg · 2 Jan 2006 · 394pp · 118,929 words
Responsive Web Design
by Ethan Marcotte · 4 Jun 2011 · 114pp · 27,996 words
Mastering Structured Data on the Semantic Web: From HTML5 Microdata to Linked Open Data
by Leslie Sikos · 10 Jul 2015
Beautiful security
by Andy Oram and John Viega · 15 Dec 2009 · 302pp · 82,233 words
People Powered: How Communities Can Supercharge Your Business, Brand, and Teams
by Jono Bacon · 12 Nov 2019 · 302pp · 73,946 words
The New CSS Layout
by Rachel Andrew · 9 Oct 2017
Network Security Through Data Analysis: Building Situational Awareness
by Michael S Collins · 23 Feb 2014 · 446pp · 102,421 words
Learning Ext Js
by Shea Frederick · 19 Dec 2008 · 324pp · 87,064 words
Data Mining the Web: Uncovering Patterns in Web Content, Structure, and Usage
by Zdravko Markov and Daniel T. Larose · 5 Apr 2007
ClojureScript: Up and Running
by Stuart Sierra and Luke Vanderhart · 24 Oct 2012 · 135pp · 31,098 words
Apache Solr 3 Enterprise Search Server
by Unknown · 13 Jan 2012 · 470pp · 109,589 words
Sass and Compass for Designers
by Ben Frain · 24 Apr 2013
Canvas Pocket Reference: Scripted Graphics for HTML5
by David Flanagan · 15 Dec 2010 · 131pp · 22,892 words
Dragnet Nation: A Quest for Privacy, Security, and Freedom in a World of Relentless Surveillance
by Julia Angwin · 25 Feb 2014 · 422pp · 104,457 words
Solr 1.4 Enterprise Search Server
by David Smiley and Eric Pugh · 15 Nov 2009 · 648pp · 108,814 words
More Joel on Software
by Joel Spolsky · 25 Jun 2008 · 292pp · 81,699 words
Programming Python
by Mark Lutz · 5 Jan 2011
Groundswell: Winning in a World Transformed by Social Technologies
by Charlene Li and Josh Bernoff · 23 May 2011 · 344pp · 96,690 words
Web Scraping With Python: Collecting Data From the Modern Web
by Ryan Mitchell · 14 Jun 2015 · 255pp · 78,207 words
Always Day One: How the Tech Titans Plan to Stay on Top Forever
by Alex Kantrowitz · 6 Apr 2020 · 260pp · 67,823 words
Rebel Ideas: The Power of Diverse Thinking
by Matthew Syed · 9 Sep 2019 · 280pp · 76,638 words
This Is for Everyone: The Captivating Memoir From the Inventor of the World Wide Web
by Tim Berners-Lee · 8 Sep 2025 · 347pp · 100,038 words
Dark Mirror: Edward Snowden and the Surveillance State
by Barton Gellman · 20 May 2020 · 562pp · 153,825 words
The End of College: Creating the Future of Learning and the University of Everywhere
by Kevin Carey · 3 Mar 2015 · 319pp · 90,965 words
Coders at Work
by Peter Seibel · 22 Jun 2009 · 1,201pp · 233,519 words
The Mesh: Why the Future of Business Is Sharing
by Lisa Gansky · 14 Oct 2010 · 215pp · 55,212 words
Python Web Development With Django
by Jeff Forcier
Coders: The Making of a New Tribe and the Remaking of the World
by Clive Thompson · 26 Mar 2019 · 499pp · 144,278 words
Realtime Web Apps: HTML5 WebSocket, Pusher, and the Web’s Next Big Thing
by Jason Lengstorf and Phil Leggetter · 20 Feb 2013
The Complete Android Guide: 3Ones
by Kevin Purdy · 15 Apr 2011
Consent of the Networked: The Worldwide Struggle for Internet Freedom
by Rebecca MacKinnon · 31 Jan 2012 · 390pp · 96,624 words
Sass for Web Designers
by Dan Cederholm · 14 May 2013 · 62pp · 15,274 words
Traction: How Any Startup Can Achieve Explosive Customer Growth
by Gabriel Weinberg and Justin Mares · 5 Oct 2015 · 232pp · 63,846 words
Catalyst 5.8: The Perl MVC Framework
by Antano Solar John, Jonathan Rockway and Solar John Antano · 15 Nov 2010
Designing Social Interfaces
by Christian Crumlish and Erin Malone · 30 Sep 2009 · 518pp · 49,555 words
Exploring ES6 - Upgrade to the next version of JavaScript
by Axel Rauschmayer · 3 Oct 2015
Raw Data Is an Oxymoron
by Lisa Gitelman · 25 Jan 2013
The Future of the Internet: And How to Stop It
by Jonathan Zittrain · 27 May 2009 · 629pp · 142,393 words
The 4-Hour Workweek: Escape 9-5, Live Anywhere, and Join the New Rich
by Timothy Ferriss · 1 Jan 2007 · 426pp · 105,423 words
This Is How They Tell Me the World Ends: The Cyberweapons Arms Race
by Nicole Perlroth · 9 Feb 2021 · 651pp · 186,130 words
Getting Started with D3
by Mike Dewar · 26 Jun 2012 · 100pp · 15,500 words
Android Cookbook
by Ian F. Darwin · 9 Apr 2012 · 960pp · 140,978 words
Making Globalization Work
by Joseph E. Stiglitz · 16 Sep 2006
The Googlization of Everything:
by Siva Vaidhyanathan · 1 Jan 2010 · 281pp · 95,852 words
JQuery Pocket Reference
by David Flanagan · 15 Dec 2010 · 211pp · 37,094 words
Masterminds of Programming: Conversations With the Creators of Major Programming Languages
by Federico Biancuzzi and Shane Warden · 21 Mar 2009 · 496pp · 174,084 words
Nagios: System and Network Monitoring
by Wolfgang Barth · 25 May 2006
HTML5 for Web Designers
by Jeremy Keith · 2 Jan 2010 · 73pp · 17,793 words
Little Brother
by Cory Doctorow · 29 Apr 2008 · 398pp · 120,801 words
The Innovators: How a Group of Inventors, Hackers, Geniuses and Geeks Created the Digital Revolution
by Walter Isaacson · 6 Oct 2014 · 720pp · 197,129 words
Flask Web Development: Developing Web Applications With Python
by Miguel Grinberg · 12 May 2014 · 420pp · 61,808 words
Mastering Ethereum: Building Smart Contracts and DApps
by Andreas M. Antonopoulos and Gavin Wood Ph. D. · 23 Dec 2018 · 960pp · 125,049 words
There's a War Going on but No One Can See It
by Huib Modderkolk · 1 Sep 2021 · 295pp · 84,843 words
Cult of the Dead Cow: How the Original Hacking Supergroup Might Just Save the World
by Joseph Menn · 3 Jun 2019 · 302pp · 85,877 words
Sex Power Money
by Sara Pascoe · 26 Aug 2019 · 287pp · 92,194 words
We Are Anonymous: Inside the Hacker World of LulzSec, Anonymous, and the Global Cyber Insurgency
by Parmy Olson · 5 Jun 2012 · 478pp · 149,810 words
Free Ride
by Robert Levine · 25 Oct 2011 · 465pp · 109,653 words
AngularJS
by Brad Green and Shyam Seshadri · 15 Mar 2013 · 196pp · 58,122 words
Dogfight: How Apple and Google Went to War and Started a Revolution
by Fred Vogelstein · 12 Nov 2013 · 275pp · 84,418 words
Nginx HTTP Server Second Edition
by Clement Nedelcu · 18 Jul 2013 · 319pp · 72,969 words
SQL Hacks
by Andrew Cumming and Gordon Russell · 28 Nov 2006 · 696pp · 111,976 words
Terms of Service: Social Media and the Price of Constant Connection
by Jacob Silverman · 17 Mar 2015 · 527pp · 147,690 words
Learning Node.js: A Hands-On Guide to Building Web Applications in JavaScript
by Marc Wandschneider · 18 Jun 2013
Drive: The Surprising Truth About What Motivates Us
by Daniel H. Pink · 1 Jan 2008 · 204pp · 54,395 words
Blitzscaling: The Lightning-Fast Path to Building Massively Valuable Companies
by Reid Hoffman and Chris Yeh · 14 Apr 2018 · 286pp · 87,401 words
Beautiful Data: The Stories Behind Elegant Data Solutions
by Toby Segaran and Jeff Hammerbacher · 1 Jul 2009
Adapt: Why Success Always Starts With Failure
by Tim Harford · 1 Jun 2011 · 459pp · 103,153 words
Measure What Matters: How Google, Bono, and the Gates Foundation Rock the World With OKRs
by John Doerr · 23 Apr 2018 · 280pp · 71,268 words
How to Predict the Unpredictable
by William Poundstone · 267pp · 71,941 words
Beginning Backbone.js
by James Sugrue · 15 Dec 2013 · 290pp · 119,172 words
Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon
by Kim Zetter · 11 Nov 2014 · 492pp · 153,565 words
Future Crimes: Everything Is Connected, Everyone Is Vulnerable and What We Can Do About It
by Marc Goodman · 24 Feb 2015 · 677pp · 206,548 words
The Internet Trap: How the Digital Economy Builds Monopolies and Undermines Democracy
by Matthew Hindman · 24 Sep 2018
Culture & Empire: Digital Revolution
by Pieter Hintjens · 11 Mar 2013 · 349pp · 114,038 words
Wired for War: The Robotics Revolution and Conflict in the 21st Century
by P. W. Singer · 1 Jan 2010 · 797pp · 227,399 words
The Rust Programming Language, 2nd Edition
by Steve Klabnik and Carol Nichols · 27 Feb 2023 · 648pp · 183,275 words
Programming TypeScript
by Boris Cherny · 16 Apr 2019 · 629pp · 83,362 words
The Internet of Us: Knowing More and Understanding Less in the Age of Big Data
by Michael P. Lynch · 21 Mar 2016 · 230pp · 61,702 words
iPad: The Missing Manual, Fifth Edition
by J.D. Biersdorfer · 21 Nov 2012
Deep Nutrition: Why Your Genes Need Traditional Food
by Catherine Shanahan M. D. · 2 Jan 2017 · 659pp · 190,874 words
Makers
by Chris Anderson · 1 Oct 2012 · 238pp · 73,824 words
Exponential: How Accelerating Technology Is Leaving Us Behind and What to Do About It
by Azeem Azhar · 6 Sep 2021 · 447pp · 111,991 words
Real World Haskell
by Bryan O'Sullivan, John Goerzen, Donald Stewart and Donald Bruce Stewart · 2 Dec 2008 · 1,065pp · 229,099 words
Brilliant, Crazy, Cocky: How the Top 1% of Entrepreneurs Profit From Global Chaos
by Sarah Lacy · 6 Jan 2011 · 269pp · 77,876 words
Virtual Competition
by Ariel Ezrachi and Maurice E. Stucke · 30 Nov 2016
Because Internet: Understanding the New Rules of Language
by Gretchen McCulloch · 22 Jul 2019 · 413pp · 106,479 words
The Charisma Machine: The Life, Death, and Legacy of One Laptop Per Child
by Morgan G. Ames · 19 Nov 2019 · 426pp · 117,775 words
Discardia: More Life, Less Stuff
by Dinah Sanders · 7 Oct 2011 · 267pp · 78,857 words
Blockchain Revolution: How the Technology Behind Bitcoin Is Changing Money, Business, and the World
by Don Tapscott and Alex Tapscott · 9 May 2016 · 515pp · 126,820 words
Life After Google: The Fall of Big Data and the Rise of the Blockchain Economy
by George Gilder · 16 Jul 2018 · 332pp · 93,672 words
Snowden's Box: Trust in the Age of Surveillance
by Jessica Bruder and Dale Maharidge · 29 Mar 2020 · 159pp · 42,401 words
Pax Technica: How the Internet of Things May Set Us Free or Lock Us Up
by Philip N. Howard · 27 Apr 2015 · 322pp · 84,752 words
Map Scripting 101: An Example-Driven Guide to Building Interactive Maps With Bing, Yahoo!, and Google Maps
by Adam Duvander · 14 Aug 2010 · 415pp · 95,261 words
Python for Data Analysis
by Wes McKinney · 30 Dec 2011 · 752pp · 131,533 words
Webbots, Spiders, and Screen Scrapers
by Michael Schrenk · 19 Aug 2009 · 371pp · 78,103 words
The System: Who Owns the Internet, and How It Owns Us
by James Ball · 19 Aug 2020 · 268pp · 76,702 words
Effective Programming: More Than Writing Code
by Jeff Atwood · 3 Jul 2012 · 270pp · 64,235 words
Attack of the 50 Foot Blockchain: Bitcoin, Blockchain, Ethereum & Smart Contracts
by David Gerard · 23 Jul 2017 · 309pp · 54,839 words
Getting Things Done for Hackers
by Lars Wirzenius · 15 Jun 2012 · 32pp · 10,468 words
@War: The Rise of the Military-Internet Complex
by Shane Harris · 14 Sep 2014 · 340pp · 96,149 words
Rewired: The Post-Cyberpunk Anthology
by James Patrick Kelly and John Kessel · 30 Sep 2007 · 571pp · 162,958 words
Simple and Usable Web, Mobile, and Interaction Design
by Giles Colborne · 14 Sep 2010
Future Files: A Brief History of the Next 50 Years
by Richard Watson · 1 Jan 2008
The Rust Programming Language
by Steve Klabnik and Carol Nichols · 14 Jun 2018 · 821pp · 178,631 words
Programming Rust: Fast, Safe Systems Development
by Jim Blandy and Jason Orendorff · 21 Nov 2017 · 1,331pp · 183,137 words
What Would Google Do?
by Jeff Jarvis · 15 Feb 2009 · 299pp · 91,839 words
Learning Android
by Marko Gargenta · 11 Mar 2011 · 378pp · 67,804 words
Ansible for DevOps: Server and Configuration Management for Humans
by Jeff Geerling · 9 Oct 2015 · 313pp · 75,583 words
The Little Book on CoffeeScript
by Alex MacCaw · 1 Jan 2012 · 59pp · 12,801 words
You Are Here: From the Compass to GPS, the History and Future of How We Find Ourselves
by Hiawatha Bray · 31 Mar 2014 · 316pp · 90,165 words
Digital Photography: The Missing Manual
by Chris Grover and Barbara Brundage · 7 Jul 2006
Lean Analytics: Use Data to Build a Better Startup Faster
by Alistair Croll and Benjamin Yoskovitz · 1 Mar 2013 · 567pp · 122,311 words
Algorithms to Live By: The Computer Science of Human Decisions
by Brian Christian and Tom Griffiths · 4 Apr 2016 · 523pp · 143,139 words
Black Code: Inside the Battle for Cyberspace
by Ronald J. Deibert · 13 May 2013 · 317pp · 98,745 words
Hacking Politics: How Geeks, Progressives, the Tea Party, Gamers, Anarchists and Suits Teamed Up to Defeat SOPA and Save the Internet
by David Moon, Patrick Ruffini, David Segal, Aaron Swartz, Lawrence Lessig, Cory Doctorow, Zoe Lofgren, Jamie Laurie, Ron Paul, Mike Masnick, Kim Dotcom, Tiffiniy Cheng, Alexis Ohanian, Nicole Powers and Josh Levy · 30 Apr 2013 · 452pp · 134,502 words
Cancel Cable: How Internet Pirates Get Free Stuff
by Chris Fehily · 1 Feb 2011 · 106pp · 22,332 words
Geek Sublime: The Beauty of Code, the Code of Beauty
by Vikram Chandra · 7 Nov 2013 · 239pp · 64,812 words
Tools of Titans: The Tactics, Routines, and Habits of Billionaires, Icons, and World-Class Performers
by Timothy Ferriss · 6 Dec 2016 · 669pp · 210,153 words
Learning Vue.js 2: Learn How to Build Amazing and Complex Reactive Web Applications Easily With Vue.js
by Olga Filipova · 13 Dec 2016 · 292pp · 66,588 words
The Patterning Instinct: A Cultural History of Humanity's Search for Meaning
by Jeremy Lent · 22 May 2017 · 789pp · 207,744 words
Hello World: Being Human in the Age of Algorithms
by Hannah Fry · 17 Sep 2018 · 296pp · 78,631 words
Natural language processing with Python
by Steven Bird, Ewan Klein and Edward Loper · 15 Dec 2009 · 504pp · 89,238 words
Ruby by example: concepts and code
by Kevin C. Baird · 1 Jun 2007 · 309pp · 65,118 words
Fatal System Error: The Hunt for the New Crime Lords Who Are Bringing Down the Internet
by Joseph Menn · 26 Jan 2010 · 362pp · 86,195 words
Bit Literacy: Productivity in the Age of Information and E-mail Overload
by Mark Hurst · 15 Jun 2007 · 153pp · 52,175 words
Cold Hands
by John J. Niven · 14 May 2012 · 210pp · 63,879 words
AngularJS Essentials
by Rodrigo Branas · 20 Aug 2014 · 180pp · 37,187 words
Eat People: And Other Unapologetic Rules for Game-Changing Entrepreneurs
by Andy Kessler · 1 Feb 2011 · 272pp · 64,626 words
Digital Wars: Apple, Google, Microsoft and the Battle for the Internet
by Charles Arthur · 3 Mar 2012 · 390pp · 114,538 words
Bold: How to Go Big, Create Wealth and Impact the World
by Peter H. Diamandis and Steven Kotler · 3 Feb 2015 · 368pp · 96,825 words
The Choice Factory: 25 Behavioural Biases That Influence What We Buy
by Richard Shotton · 12 Feb 2018 · 184pp · 46,395 words
Throwing Rocks at the Google Bus: How Growth Became the Enemy of Prosperity
by Douglas Rushkoff · 1 Mar 2016 · 366pp · 94,209 words
Developing Backbone.js Applications
by Addy Osmani · 21 Jul 2012 · 420pp · 79,867 words
Laziness Does Not Exist
by Devon Price · 5 Jan 2021 · 362pp · 87,462 words
Greater: Britain After the Storm
by Penny Mordaunt and Chris Lewis · 19 May 2021 · 516pp · 116,875 words
Doing Data Science: Straight Talk From the Frontline
by Cathy O'Neil and Rachel Schutt · 8 Oct 2013 · 523pp · 112,185 words
Epic Win for Anonymous: How 4chan's Army Conquered the Web
by Cole Stryker · 14 Jun 2011 · 226pp · 71,540 words
Elsewhere, U.S.A: How We Got From the Company Man, Family Dinners, and the Affluent Society to the Home Office, BlackBerry Moms,and Economic Anxiety
by Dalton Conley · 27 Dec 2008 · 204pp · 67,922 words
The Optimist: Sam Altman, OpenAI, and the Race to Invent the Future
by Keach Hagey · 19 May 2025 · 439pp · 125,379 words
Markets, State, and People: Economics for Public Policy
by Diane Coyle · 14 Jan 2020 · 384pp · 108,414 words
Hacking Capitalism
by Söderberg, Johan; Söderberg, Johan;
Recoding America: Why Government Is Failing in the Digital Age and How We Can Do Better
by Jennifer Pahlka · 12 Jun 2023 · 288pp · 96,204 words
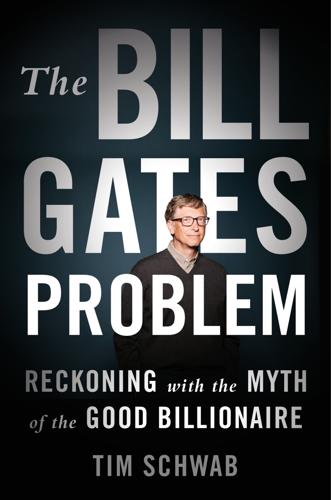
The Bill Gates Problem: Reckoning With the Myth of the Good Billionaire
by Tim Schwab · 13 Nov 2023 · 618pp · 179,407 words
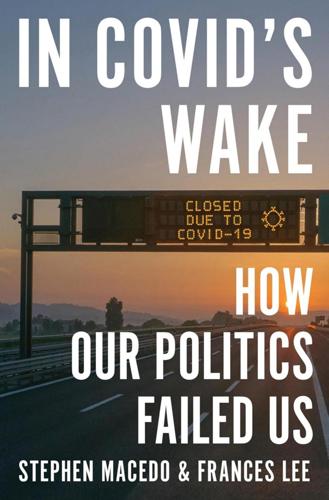
In Covid's Wake: How Our Politics Failed Us
by Stephen Macedo and Frances Lee · 10 Mar 2025 · 393pp · 146,371 words
Searches: Selfhood in the Digital Age
by Vauhini Vara · 8 Apr 2025 · 301pp · 105,209 words
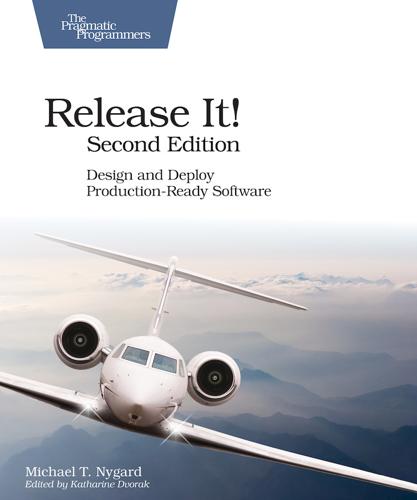
The Nature of Software Development: Keep It Simple, Make It Valuable, Build It Piece by Piece
by Ron Jeffries · 14 Aug 2015 · 444pp · 118,393 words
Stolen Focus: Why You Can't Pay Attention--And How to Think Deeply Again
by Johann Hari · 25 Jan 2022 · 390pp · 120,864 words
Bad Data Handbook
by Q. Ethan McCallum · 14 Nov 2012 · 398pp · 86,855 words
The Molecule of More: How a Single Chemical in Your Brain Drives Love, Sex, and Creativityand Will Det Ermine the Fate of the Human Race
by Daniel Z. Lieberman and Michael E. Long · 13 Aug 2018 · 287pp · 78,609 words
The Age of Entitlement: America Since the Sixties
by Christopher Caldwell · 21 Jan 2020 · 450pp · 113,173 words
Technically Wrong: Sexist Apps, Biased Algorithms, and Other Threats of Toxic Tech
by Sara Wachter-Boettcher · 9 Oct 2017 · 223pp · 60,909 words
Artificial Unintelligence: How Computers Misunderstand the World
by Meredith Broussard · 19 Apr 2018 · 245pp · 83,272 words
Beautiful Solutions: A Toolbox for Liberation
by Elandria Williams, Eli Feghali, Rachel Plattus and Nathan Schneider · 15 Dec 2024 · 346pp · 84,111 words
Microsoft Office Outlook 2010 QuickSteps
by Malestrom
The Future Was Now: Madmen, Mavericks, and the Epic Sci-Fi Summer Of 1982
by Chris Nashawaty · 251pp · 86,553 words
Busting Vegas: The MIT Whiz Kid Who Brought the Casinos to Their Knees
by Ben Mezrich · 26 Sep 2005 · 303pp · 81,981 words
Peers Inc: How People and Platforms Are Inventing the Collaborative Economy and Reinventing Capitalism
by Robin Chase · 14 May 2015 · 330pp · 91,805 words
The Pirate's Dilemma: How Youth Culture Is Reinventing Capitalism
by Matt Mason
The Computer Boys Take Over: Computers, Programmers, and the Politics of Technical Expertise
by Nathan L. Ensmenger · 31 Jul 2010 · 429pp · 114,726 words
Makers at Work: Folks Reinventing the World One Object or Idea at a Time
by Steven Osborn · 17 Sep 2013 · 310pp · 34,482 words
Ghost Fleet: A Novel of the Next World War
by P. W. Singer and August Cole · 28 Jun 2015 · 537pp · 149,628 words
The Best of 2600: A Hacker Odyssey
by Emmanuel Goldstein · 28 Jul 2008 · 889pp · 433,897 words
Dawn of the New Everything: Encounters With Reality and Virtual Reality
by Jaron Lanier · 21 Nov 2017 · 480pp · 123,979 words
Postcapitalism: A Guide to Our Future
by Paul Mason · 29 Jul 2015 · 378pp · 110,518 words
McMafia: A Journey Through the Global Criminal Underworld
by Misha Glenny · 7 Apr 2008 · 487pp · 147,891 words
Working in Public: The Making and Maintenance of Open Source Software
by Nadia Eghbal · 3 Aug 2020 · 1,136pp · 73,489 words
Mastering Blockchain: Unlocking the Power of Cryptocurrencies and Smart Contracts
by Lorne Lantz and Daniel Cawrey · 8 Dec 2020 · 434pp · 77,974 words
How to Fix the Future: Staying Human in the Digital Age
by Andrew Keen · 1 Mar 2018 · 308pp · 85,880 words
Travel While You Work: The Ultimate Guide to Running a Business From Anywhere
by Mish Slade · 13 Aug 2015 · 288pp · 66,996 words
Roads and Bridges
by Nadia Eghbal · 139pp · 35,022 words
The Year Without Pants: Wordpress.com and the Future of Work
by Scott Berkun · 9 Sep 2013 · 361pp · 76,849 words
How to DeFi
by Coingecko, Darren Lau, Sze Jin Teh, Kristian Kho, Erina Azmi, Tm Lee and Bobby Ong · 22 Mar 2020 · 135pp · 26,407 words
Backbone.js Cookbook
by Vadim Mirgorod · 25 Aug 2013
The Data Journalism Handbook
by Jonathan Gray, Lucy Chambers and Liliana Bounegru · 9 May 2012
Everything's Trash, but It's Okay
by Phoebe Robinson · 15 Oct 2018 · 257pp · 90,857 words
HBase: The Definitive Guide
by Lars George · 29 Aug 2011
Your Money: The Missing Manual
by J.D. Roth · 18 Mar 2010 · 519pp · 118,095 words
Mining Social Media: Finding Stories in Internet Data
by Lam Thuy Vo · 21 Nov 2019 · 237pp · 65,794 words
Building Web Applications With Flask
by Italo Maia · 25 Jun 2015 · 157pp · 35,874 words
The Relentless Revolution: A History of Capitalism
by Joyce Appleby · 22 Dec 2009 · 540pp · 168,921 words
The Seventh Sense: Power, Fortune, and Survival in the Age of Networks
by Joshua Cooper Ramo · 16 May 2016 · 326pp · 103,170 words
Forge Your Future with Open Source
by VM (Vicky) Brasseur · 266pp · 79,297 words
Python Cookbook
by David Beazley and Brian K. Jones · 9 May 2013 · 1,606pp · 168,061 words
Commodore: A Company on the Edge
by Brian Bagnall · 13 Sep 2005 · 781pp · 226,928 words
The Practice of Cloud System Administration: DevOps and SRE Practices for Web Services, Volume 2
by Thomas A. Limoncelli, Strata R. Chalup and Christina J. Hogan · 27 Aug 2014 · 757pp · 193,541 words
How to Buy Property at Auction: The Essential Guide to Winning Property and Buy-To-Let Bargains
by Samantha Collett · 20 Mar 2014 · 218pp · 60,935 words
Free Speech: Ten Principles for a Connected World
by Timothy Garton Ash · 23 May 2016 · 743pp · 201,651 words
Python Geospatial Development - Second Edition
by Erik Westra · 23 May 2013
PostGIS in Action, 2nd Edition
by Regina O. Obe and Leo S. Hsu · 2 May 2015
Fuller Memorandum
by Stross, Charles · 14 Jan 2010 · 366pp · 107,145 words
Interlibrary Loan Practices Handbook
by Cherie L. Weible and Karen L. Janke · 15 Apr 2011 · 144pp · 55,142 words
The Corruption of Capitalism: Why Rentiers Thrive and Work Does Not Pay
by Guy Standing · 13 Jul 2016 · 443pp · 98,113 words
Professional Node.js: Building Javascript Based Scalable Software
by Pedro Teixeira · 30 Sep 2012 · 325pp · 85,599 words
Node.js in Action
by Mike Cantelon, Marc Harter, Tj Holowaychuk and Nathan Rajlich · 27 Jul 2013 · 628pp · 107,927 words
Hopes and Prospects
by Noam Chomsky · 1 Jan 2009
Program Or Be Programmed: Ten Commands for a Digital Age
by Douglas Rushkoff · 1 Nov 2010 · 103pp · 32,131 words
The Story of Stuff: The Impact of Overconsumption on the Planet, Our Communities, and Our Health-And How We Can Make It Better
by Annie Leonard · 22 Feb 2011 · 538pp · 138,544 words
Programming Collective Intelligence
by Toby Segaran · 17 Dec 2008 · 519pp · 102,669 words
Clojure Programming
by Chas Emerick, Brian Carper and Christophe Grand · 15 Aug 2011 · 999pp · 194,942 words
The new village green: living light, living local, living large
by Stephen Morris · 1 Sep 2007 · 289pp · 112,697 words
Googled: The End of the World as We Know It
by Ken Auletta · 1 Jan 2009 · 532pp · 139,706 words
Click Here to Kill Everybody: Security and Survival in a Hyper-Connected World
by Bruce Schneier · 3 Sep 2018 · 448pp · 117,325 words
Mining the Social Web: Finding Needles in the Social Haystack
by Matthew A. Russell · 15 Jan 2011 · 541pp · 109,698 words
The Bitcoin Guidebook: How to Obtain, Invest, and Spend the World's First Decentralized Cryptocurrency
by Ian Demartino · 2 Feb 2016 · 296pp · 86,610 words
The Boy Who Could Change the World: The Writings of Aaron Swartz
by Aaron Swartz and Lawrence Lessig · 5 Jan 2016 · 377pp · 110,427 words
Taming the To-Do List: How to Choose Your Best Work Every Day
by Glynnis Whitwer · 10 Aug 2015 · 181pp · 53,257 words
Ctrl Alt Delete: Reboot Your Business. Reboot Your Life. Your Future Depends on It.
by Mitch Joel · 20 May 2013 · 260pp · 76,223 words
Cities Are Good for You: The Genius of the Metropolis
by Leo Hollis · 31 Mar 2013 · 385pp · 118,314 words
The Snowden Files: The Inside Story of the World's Most Wanted Man
by Luke Harding · 7 Feb 2014 · 266pp · 80,018 words
Python for Data Analysis: Data Wrangling with Pandas, NumPy, and IPython
by Wes McKinney · 25 Sep 2017 · 1,829pp · 135,521 words
Actionable Gamification: Beyond Points, Badges and Leaderboards
by Yu-Kai Chou · 13 Apr 2015 · 420pp · 130,503 words
Nomad Citizenship: Free-Market Communism and the Slow-Motion General Strike
by Eugene W. Holland · 1 Jan 2009 · 265pp · 15,515 words
Pragmatic Version Control Using Git
by Travis Swicegood · 1 Dec 2008 · 184pp · 12,922 words
To Save Everything, Click Here: The Folly of Technological Solutionism
by Evgeny Morozov · 15 Nov 2013 · 606pp · 157,120 words
Life Inc.: How the World Became a Corporation and How to Take It Back
by Douglas Rushkoff · 1 Jun 2009 · 422pp · 131,666 words
Robots Will Steal Your Job, But That's OK: How to Survive the Economic Collapse and Be Happy
by Pistono, Federico · 14 Oct 2012 · 245pp · 64,288 words
The Purpose Economy: How Your Desire for Impact, Personal Growth and Community Is Changing the World
by Aaron Hurst · 31 Aug 2013 · 209pp · 63,649 words
Introduction to Tornado
by Michael Dory, Adam Parrish and Brendan Berg · 29 Sep 2011 · 136pp · 20,501 words
Collaborative Futures
by Mike Linksvayer, Michael Mandiberg and Mushon Zer-Aviv · 24 Aug 2010 · 188pp · 9,226 words
Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World
by Bruce Schneier · 2 Mar 2015 · 598pp · 134,339 words
Delete: The Virtue of Forgetting in the Digital Age
by Viktor Mayer-Schönberger · 1 Jan 2009 · 263pp · 75,610 words
The Complete Guide to Property Investment: How to Survive & Thrive in the New World of Buy-To-Let
by Rob Dix · 18 Jan 2016 · 228pp · 68,315 words
Alchemy: The Dark Art and Curious Science of Creating Magic in Brands, Business, and Life
by Rory Sutherland · 6 May 2019 · 401pp · 93,256 words
Facebook: The Inside Story
by Steven Levy · 25 Feb 2020 · 706pp · 202,591 words
The Patient Will See You Now: The Future of Medicine Is in Your Hands
by Eric Topol · 6 Jan 2015 · 588pp · 131,025 words
Magic Internet Money: A Book About Bitcoin
by Jesse Berger · 14 Sep 2020 · 108pp · 27,451 words
The Wealth of Networks: How Social Production Transforms Markets and Freedom
by Yochai Benkler · 14 May 2006 · 678pp · 216,204 words
The Digital Doctor: Hope, Hype, and Harm at the Dawn of Medicine’s Computer Age
by Robert Wachter · 7 Apr 2015 · 309pp · 114,984 words
I Think You'll Find It's a Bit More Complicated Than That
by Ben Goldacre · 22 Oct 2014 · 467pp · 116,094 words
Drugs 2.0: The Web Revolution That's Changing How the World Gets High
by Mike Power · 1 May 2013 · 378pp · 94,468 words
WTF?: What's the Future and Why It's Up to Us
by Tim O'Reilly · 9 Oct 2017 · 561pp · 157,589 words
Blockchain: Blueprint for a New Economy
by Melanie Swan · 22 Jan 2014 · 271pp · 52,814 words
Silk Road
by Eileen Ormsby · 1 Nov 2014 · 269pp · 79,285 words

The End of Ownership: Personal Property in the Digital Economy
by Aaron Perzanowski and Jason Schultz · 4 Nov 2016 · 374pp · 97,288 words
Architecting Modern Data Platforms: A Guide to Enterprise Hadoop at Scale
by Jan Kunigk, Ian Buss, Paul Wilkinson and Lars George · 8 Jan 2019 · 1,409pp · 205,237 words
Mastering Ember.js
by Mitchel Kelonye · 19 Oct 2014 · 266pp · 38,397 words
The Age of Cryptocurrency: How Bitcoin and Digital Money Are Challenging the Global Economic Order
by Paul Vigna and Michael J. Casey · 27 Jan 2015 · 457pp · 128,838 words
Mine!: How the Hidden Rules of Ownership Control Our Lives
by Michael A. Heller and James Salzman · 2 Mar 2021 · 332pp · 100,245 words
Instant Ember.JS Application Development: How-To
by Marc Bodmer · 11 Feb 2013 · 48pp · 10,481 words
Lurking: How a Person Became a User
by Joanne McNeil · 25 Feb 2020 · 239pp · 80,319 words
People, Power, and Profits: Progressive Capitalism for an Age of Discontent
by Joseph E. Stiglitz · 22 Apr 2019 · 462pp · 129,022 words
The Art of Software Security Assessment: Identifying and Preventing Software Vulnerabilities
by Justin Schuh · 20 Nov 2006 · 2,054pp · 359,149 words
Chokepoint Capitalism
by Rebecca Giblin and Cory Doctorow · 26 Sep 2022 · 396pp · 113,613 words
Androids: The Team That Built the Android Operating System
by Chet Haase · 12 Aug 2021 · 580pp · 125,129 words
Mastering Blockchain, Second Edition
by Imran Bashir · 28 Mar 2018
Help for Women With ADHD: My Simple Strategies for Conquering Chaos
by Joan Wilder · 18 May 2016 · 37pp · 10,757 words
PostGIS in Action
by Regina O. Obe and Leo S. Hsu · 2 May 2015
Badvertising
by Andrew Simms · 314pp · 81,529 words
The Cryptopians: Idealism, Greed, Lies, and the Making of the First Big Cryptocurrency Craze
by Laura Shin · 22 Feb 2022 · 506pp · 151,753 words
More Everything Forever: AI Overlords, Space Empires, and Silicon Valley's Crusade to Control the Fate of Humanity
by Adam Becker · 14 Jun 2025 · 381pp · 119,533 words
The End of Absence: Reclaiming What We've Lost in a World of Constant Connection
by Michael Harris · 6 Aug 2014 · 259pp · 73,193 words
Django Book
by Matt Behrens · 24 Jan 2015
The TypeScript Workshop: A Practical Guide to Confident, Effective TypeScript Programming
by Ben Grynhaus, Jordan Hudgens, Rayon Hunte, Matthew Thomas Morgan and Wekoslav Stefanovski · 28 Jul 2021 · 739pp · 174,990 words
Algorithms of Oppression: How Search Engines Reinforce Racism
by Safiya Umoja Noble · 8 Jan 2018 · 290pp · 73,000 words
Enshittification: Why Everything Suddenly Got Worse and What to Do About It
by Cory Doctorow · 6 Oct 2025 · 313pp · 94,415 words