Free as in Freedom
by Sam Williams · 16 Nov 2015
input from the general hacker community on how to improve the license's language. One hacker to take up the offer was future software activist John Gilmore, then working as a consultant to Sun Microsystems. As part of his consulting work, Gilmore had ported Emacs over to SunOS, the company's in
…
" or something. Soon, we hope, Emacs will not be the biggest part of the GNU system, and the license applies to all of it.See John Gilmore, quoted from email to author. Gilmore wasn't the only person suggesting a more general approach. By the end of 1986, Stallman himself was at
…
in disguise."7. See Michael Tiemann, "Future of Cygnus Solutions: An Entrepreneur's Account," Open Sources (O'Reilly & Associates, Inc., 1999): 139. Teaming up with John Gilmore, another GNU Project fan, Tiemann launched a software consulting service dedicated to customizing GNU programs. Dubbed Cygnus Support, the company signed its first development contract
…
same approach as Debian-i.e., building an operating system completely out of free software parts. Cygnus Solutions, the company founded by Michael Tiemann and John Gilmore in 1990, was already demonstrating the ability to sell free software based on quality and customizability. What if Red Hat took the same approach with
…
'd been inflexible and unwilling to engage in dialogue. I wanted to make sure the GNU tradition was represented at the meeting, so I invited John Gilmore and Michael Tiemann, whom I knew personally, and whom I knew were passionate about the value of the GPL but seemed more willing to engage
…
Moglen. "They're going to be viewed as the main line of the story." The "couple other people" Moglen nominates for future textbook chapters include John Gilmore, Stallman's GPL advisor and future founder of the Electronic Frontier Foundation, and Theodor Holm Nelson, a.k.a. Ted Nelson, author of the 1982
This Machine Kills Secrets: Julian Assange, the Cypherpunks, and Their Fight to Empower Whistleblowers
by Andy Greenberg · 12 Sep 2012 · 461pp · 125,845 words
tools like anonymous remailers and Tor. ERIC HUGHES Mathematician, cryptographer, and cofounder of the cypherpunks who ran one of the Internet’s first anonymous remailers. JOHN GILMORE Former Sun Microsystems programmer who would cofound the cypherpunks as well as the Electronic Frontier Foundation. JOHN YOUNG Architect, activist, and cypherpunk who founded Cryptome
…
that cryptography would help to keep the government’s tendrils safely hogtied. The pair had met at a party thrown by their libertarian hacker friend John Gilmore, a ponytailed and balding software developer whose sad eyes hid a fiercely independent streak. As the fifth employee of Sun Microsystems, Gilmore had struck it
…
? As May had years earlier realized, cyber-utopias would have to be created on the Internet, not in someone’s living room. They later asked John Gilmore if he would host an e-mail list on the server of his personal site, Toad.com, and he eagerly agreed. But it was Jude
…
, its physical meetings would expand too. Within a year the group had moved out of Hughes’s house and into a spare conference room at John Gilmore’s software company, Cygnus, in Mountain View, in a building that bordered an herb farm and was permeated with the scent of fresh basil. The
…
himself, didn’t attend. “I don’t give free lessons, especially not to clueless software people,” he says.) Shortly after the group’s first meeting, John Gilmore and another cypherpunk named Hugh Daniel had bet Hughes that he couldn’t write an anonymous remailer system for stripping the identifying traces off e
…
settles into the matter at hand, the idea that was, to many, the most influential and controversial thought he produced in his role as what John Gilmore calls “the Thomas Jefferson of the cypherpunks.” That idea was BlackNet. BlackNet was a thought experiment, the fruit of Chaum’s anonymity ideas applied to
…
teach people how to make candles,” he says. “I had the ideas. But the idea of trying to be Julian Assange gives me the creeps.” John Gilmore and I are looking out onto the shiny wet streets of San Francisco’s Mission District as the entire Cypherpunk Mailing List archive, all 345
…
his eyes with hoods that wrinkle as he cracks open the cypherpunks’ dusty archives. The first messages are introductions from Tim May, Eric Hughes, and John Gilmore, along with Eric Hughes’s declaration of the first cypherpunk remailer, built on Gilmore’s dare. And then comes another message containing only an article
…
been living in the doldrums, and suddenly we were on the cutting edge,” he says. In June 1994, he discovered the cypherpunks when Tim May, John Gilmore, Eric Hughes, and Phil Zimmermann were featured in a New York Times magazine story that quoted chunks of both May’s “Crypto-Anarchist Manifesto” and
…
, one just as dangerous to the status quo as Gutenberg’s invention had been. For the next twenty-five years, he and fellow cyberlibertarians like John Gilmore and Lotus founder Mitch Kapor would spend much of their lives and enormous sums of money fighting the governments and corporations that would seek to
…
that’s not optimal,” he says weakly. “That’s all that I can give.” And then comes the final person in the line of interrogators: John Gilmore, the venerable bearded and ponytailed cofounder of the cypherpunks and the Electronic Frontier Foundation. His mere appearance at a conference east of the Mississippi River
…
GlobaLeaks’ source code. Or watching the archived video of Daniel Domscheit-Berg’s talk at the Chaos Communication Camp and learning from his mistakes, as John Gilmore suggested future leaking advocates ought to. We don’t yet know the names of the architects who will build the next upgrade to the secret
Rise of the Machines: A Cybernetic History
by Thomas Rid · 27 Jun 2016 · 509pp · 132,327 words
open; no finger files wanted. Everybody could subscribe by simply e-mailing cypherpunks-request@toad.com. The list was hosted on a machine owned by John Gilmore, an early San Francisco–based crypto activist with a long mane, a flimsy beard, and a keen interest in recreational drugs. Gilmore was one of
…
famous cover story for Wired, in the magazine’s second issue, which came out in May 1993. On the cover were Eric Hughes, Tim May, John Gilmore, holding up an American flag, their faces hidden behind white plastic masks, Gilmore even sporting an EFF T-shirt complete with the internet address of
…
the list for the first years.35 The emerging movement had no budget, no voting, no leaders. Yet the community remained active for many years. John Gilmore did the math: from December 1, 1996, to March 1, 1999, the list processed 24,575 messages. That’s approximately thirty messages each day for
…
From the start, cypherpunk was about getting stuff done, not just debate and organization for debate and organization’s sake. In the summer of 1992, John Gilmore, one of the three original crypto rebels on the Wired cover, had made a bold move against the NSA that catapulted the movement into the
…
the early 1990s. He covered and shaped the early tech counterculture and cofounded the Electronic Frontier Foundation. In a military library in Virginia, EFF cofounder John Gilmore discovered a coveted classified document that the NSA had refused to release to him, and he confronted the government. Here he celebrates his victory in
…
the most radical. He wrote the “Crypto Anarchist Manifesto,” came up with BlackNet in August 1993, and coined phrases like “crypto = guns.” Tim May (left), John Gilmore (right), and Eric Hughes, who appeared wearing these masks on the cover of Wired magazine’s second issue, in May 1993, their PGP fingerprints written
…
book in San Francisco and the Bay Area, interviewing pioneers of 1980s electronic counterculture, as well as 1990s crypto activists. I am particularly grateful to John Gilmore, Kevin Kelly, Ryan Lackey, and notably Tim May for being so helpful and generous with their time. Barbara Hayward, Alice Mary Hilton’s daughter, gave
…
/1996. My research was possible largely thanks to his archive at cypherpunks.venona.com. Ryan Lackey, e-mail to the author, February 16, 2015. 36.John Gilmore, “Summary of Cypherpunks Discussion Volume and Participants,” e-mail to Gene Grantham, April 13, 1999. 37.May, “True Nyms and Crypto Anarchy,” 83. 38.Ibid
…
too remarkable. James Bamford had prominently reported on the wider Friedman papers in an influential book on the NSA: The Puzzle Palace, published in 1982. John Gilmore, interview by the author, April 7, 2014. 47.Gilmore, interview, April 7, 2014. 48.Ibid. 49.John Markoff, “In Retreat, U.S. Spy Agency Shrugs
…
Goffman. R.U. a Cyberpunk? Mondo 2000, 1993, Nr 10, p. 30. Courtesy Ken Goffman. Photo of John Perry Barlow. Mondo 2000. Courtesy Ken Goffman. John Gilmore. Photo: Kevin Kelly. Timothy C. May. Photo: Kevin Kelly. May, Gilmore, and Hughes. Photo: Larry Dyer, WIRED Magazine. Ryan Lackey. Photo: Kim Gilmour. HavenCo platform
The Dark Net
by Jamie Bartlett · 20 Aug 2014 · 267pp · 82,580 words
.* – under which users could start their own relevant subgroups. To name the group, you took the main hierarchy name, and then added further categories.fn2* John Gilmore, who would go on to co-found the cypherpunk movement with Tim May and Eric Hughes in 1992, wanted to start a group about drugs
…
to political revolutions. He is a cypherpunk. The Mailing List One day in late 1992, retired businessman Tim May, mathematician Eric Hughes and computer scientist John Gilmore – the creator of alt.* – invited twenty of their favourite programmers and cryptographers to Hughes’ house in Oakland, California. After taking a degree in physics at
…
the crypto world. Hundreds of people used it to propose and learn ciphers, evade detection, discuss radical politics. It was finally discontinued in 2001 when John Gilmore booted it from his host, toad.com, for reasons not entirely clear – Gilmore claimed it had ‘degenerated’. But it had a remarkable track record: anonymous
Crypto: How the Code Rebels Beat the Government Saving Privacy in the Digital Age
by Steven Levy · 15 Jan 2002 · 468pp · 137,055 words
Privacy Information Center gave me access to the astounding documents coughed up by the government under their skillful use of the Freedom of Information Act. John Gilmore and his lawyer Lee Tien also provided me with armloads of declassified materials. Roger Schlafly sent me a huge pack of documents related to RSA
…
was upset that the agency had spiked it—so upset that he or she slipped it to an independent watchdog, a computer-hacker millionaire named John Gilmore. Gilmore had a weapon that wasn’t available a decade earlier, when the prepublication process was initiated: the Internet. One of the most popular Usenet
…
the next few weeks, they enlisted the aid of some influential figures in the antigovernment crypto community. One forceful ally was thirty-seven-year-old John Gilmore, a gentle computer hacker with long thinning hair and a wispy beard (when he stood beside Eric Hughes, the two of them looked like a
…
elaborate agenda including discussion of “societal implications of cryptography,” “voting networks,” and “anonymous information markets.” There were reports on digital money in virtual realities and John Gilmore’s assessment of the NSA. And there was time set aside, of course, for the “reading of manifestos.” Tim May had one prepared especially for
…
. Only dedicated individuals, willing to suffer the consequences of government sanction, could assure that the tools got circulated into the Internet’s bloodstream. After that, John Gilmore said, “It would take a pretty strong police state to suppress this technology.” One unexpected highlight was an observation made by Hughes’s companion, a
…
in a month. In the meantime, Eric Hughes set up what would be a much more robust and fertile cypherpunk gathering place: the Internet. Using John Gilmore’s server (its Internet domain name was toad.com) as a cyberspace hub, Hughes set up what was known as a list-serv, an ongoing
…
as they applied to Snuffle. He appealed the first CJ. When months passed without a response, he decided that he needed help. His benefactor was John Gilmore, no stranger to court battles against the government. The senior cypherpunk already had accumulated a file cabinet’s worth of documents with Freedom of Information
…
to get plaintext when it needed to. One caper funded by the Electronic Frontier Foundation had been particularly telling: a team of engineers led by John Gilmore and Paul Kocher had built a DES-cracking machine for $210,000. (DES, of course, was still deemed a munition too hazardous to send abroad
…
. The Clipper Chip The bulk of this chapter was derived from personal interviews and a wealth of declassified documents supplied to me by EPIC or John Gilmore. My contemporary account of the Clipper battle was “The Cypherpunks vs. Uncle Sam,” Sunday New York Times Magazine, June 12, 1994. Another helpful article was
The Transparent Society: Will Technology Force Us to Choose Between Privacy and Freedom?
by David Brin · 1 Jan 1998 · 205pp · 18,208 words
extolling a coming “golden age of privacy,” when no one need ever again fear snooping by bureaucrats, federal agents, or in-laws. The prominent iconoclast John Gilmore, who favors “law ʻnʼ chaos over law ʻnʼ order,” recently proclaimed that computers are literally extensions of our minds, and that their contents should therefore
…
even your name—without your explicit permission. Supporting a quite different approach are some of the most vivid and original thinkers of the information age. John Gilmore, Esther Dyson, John Perry Barlow, and others on the (roughly) libertarian wing were in the vanguard fighting against both the Clipper proposal and the Communications
…
face of physical destruction seem also to protect its happy chaos against attempts to impose rigorous discipline, a point illustrated in a popular aphorism by John Gilmore: “The Net perceives censorship as damage, and routes around it.” I plan to reconnect with this thought in later chapters, for it bears directly on
…
. In contrast, whatever comes along that increases the effectiveness of 3 and 4 may raise your discomfort level, if not ire. Illustrating this, EFF cofounder John Gilmore has been outspoken about restricting governmentʼs ability to conceal (through tools like FOIA), while also curbing its ability to see (by promoting encryption and
…
officials (already answerable to aggressive media and regular elections), need to be watched lest they lie, cheat, or cover up crimes and mistakes. EFF cofounder John Gilmore expressed this implicit assumption in discussing the Clipper controversy: “The ultimate goal of key escrow is to place the rights of the state over the
…
freedom over order. By proclaiming our fidelity to personal sovereignty, even if some will abuse that sovereignty to become obnoxious or dangerous to their neighbors. John Gilmore put the idea dramatically when he said, “We favor lawʻnʼ chaos ... weʼd rather have more drug dealers and fewer bureaucrats.” But the same
…
listen in on you or me, but why would he care? (Also, since he is so closely watched, heʼd fear getting caught.) EFF cofounder John Gilmore has pointed out that there is a big difference between individual and mass surveillance. Acknowledging that specific encryption regimes might be broken by top government
…
back into the crowd. First, who wants to fade into a crowd? Not outspoken citizens in a civilization of aficionados and individualists— and certainly not John Gilmore! Anyway, technology keeps enlarging the power of big shots to stare at the teeming masses. We cannot count on sheltering our privacy in a throng
…
this is true, it runs diametrically counter to everything we are taught to believe about officious and obtrusive bureaucrats. 37 ... the chief “designer” ... According to John Gilmore, “Paul Baran vastly underestimated the difficulty of routing the messages. Breakthroughs are needed (at each stage) to get a system that is robust and scales
…
fact, mutual criticism in society has the potential of being far more effective in correcting errors than the immune system of a living organism. As John Gilmore points out, “The immune system canʼt improve on the bodyʼs pre-existing design. But criticism can.” (Personal communication to the author.) 135 ... archetype
…
HOFFMAN I want to thank those who lent a kind (and critical) eye to early drafts of this book. These good folks include Stefan Jones, John Gilmore, Steve Jackson, Carl Malamud, Roger Clarke, Oliver Morton, John Perry Barlow, Bruce Murray, Bruce Sterling, Chris Peterson, Robin Hanson, Xavier Fan, Martha Minow, Ann Florini
Drugs 2.0: The Web Revolution That's Changing How the World Gets High
by Mike Power · 1 May 2013 · 378pp · 94,468 words
online – or anywhere, since they were populated by the most extraordinarily helpful, altruistic and technologically adept users in the world. Computer scientist Brian Reid, and John Gilmore (an early internet pioneer, civil libertarian, entrepreneur and techno-renaissance man whose work around cryptography, censorship and drug law reform make him an unsung early
…
and cyberutopians. The Well, or Whole Earth ‘Lectronic Link, was a virtual community that hosted conversations between some of the web’s earliest champions including John Gilmore. It was also an important meeting point for fans of the Grateful Dead, confirming for ever the association between high-tech geekery and psychedelics that
…
time we were still independent contractors with the EFF [the online freedom of speech group, the Electronic Freedom Foundation, set up by .alt newsgroup creator John Gilmore] and the American Department of Defence at the same time, which made for some strange meetings!’ says Lewman. Tor is not just used by those
This Is Your Country on Drugs: The Secret History of Getting High in America
by Ryan Grim · 7 Jul 2009 · 334pp · 93,162 words
lights. Make a mistake, and you would be engulfed in flames. The first entry on the FAQ sign read, “Is this safe? A: Probably not.” John Gilmore was the fifth employee at Sun Microsystems and registered the domain name Toad.com in 1987. A Burner and well-known psychonaut, he’s certainly
…
Gasser, Peter Gates, Bill Gates, Brad Gates, Daryl Gatien, Peter Gavin, Mary gender issues amphetamines and LSD and opium and Germany Gibbons, Stephen B. Gilmore, John Gilmore’s Law Gingrich, Newt Ginsberg, Allen Goddard, James Goldstein, Paul Gonzales v. O Centro Espirita Beneficiente União do Vegetal Gonzales v. Raich Gonzalez, Henry Gore
Cult of the Dead Cow: How the Original Hacking Supergroup Might Just Save the World
by Joseph Menn · 3 Jun 2019 · 302pp · 85,877 words
belief that they were not the main enemy. Then he convinced Boston software entrepreneur Mitch Kapor, inventor of the modern electronic spreadsheet, and libertarian engineer John Gilmore to join him in founding the Electronic Frontier Foundation. (Gilmore would soon host the Cypherpunks mailing list, which would be home to the most public
…
, who reprinted his Information America piece and introduced him to her boyfriend, Eric Hughes, who was about to start the Cypherpunks mailing list, hosted by John Gilmore. Misha spread the word among hackers. The dot-com boom that began with Netscape’s initial public offering in 1995 lured more waves of cDc
…
official at the Department of Justice who wanted back doors and weak encryption. It was there he met Cypherpunks mailing list sponsor and EFF cofounder John Gilmore and Phil Zimmerman, the inventor of Pretty Good Privacy (PGP) email encryption, who had also battled the federal government. “I ended up being friends with
…
-sized San Francisco hacker space Jake had cofounded, said he could not come back. Jake’s early defenders included some Tor node operators, EFF cofounder John Gilmore, and Daniel J. Bernstein, an antigovernment cryptographer who had helped loosen export rules with Cohn’s legal help years before. Most cautioned against rushing to
Rebel Code: Linux and the Open Source Revolution
by Glyn Moody · 14 Jul 2002 · 483pp · 145,225 words
business. And I talked with many people about this idea, and the only ones that took me seriously were the other two cofounders,” John Gilmore and David Henkel-Wallace. “John Gilmore’s e-mail handle is ‘gnu,’” Tiemann explains, “and some claim that he had nicknamed the GNU project.” Moreover, “John was employee number
…
we did before 1992.” While they were casting around for a product, one of them came up with what, in retrospect, was an interesting idea. “John Gilmore proposed that we write a free kernel for the 386,” Tiemann recalls. This was in 1990, fully one year before Linus would sit down and
…
partners at that time that we attempt to acquire Red Hat, and they would have none of it. In 1990-91, I said no to John Gilmore, and in 1995 he said no to me. So there was a long window of opportunity that we simply ignored.” The problem was hardly lack
The Hacker Crackdown
by Bruce Sterling · 15 Mar 1992 · 345pp · 105,722 words
Masters of Deception: The Gang That Ruled Cyberspace
by Michelle Slatalla and Joshua Quittner · 15 Jan 1995
The Mysterious Mr. Nakamoto: A Fifteen-Year Quest to Unmask the Secret Genius Behind Crypto
by Benjamin Wallace · 18 Mar 2025 · 431pp · 116,274 words
The Future of Ideas: The Fate of the Commons in a Connected World
by Lawrence Lessig · 14 Jul 2001 · 494pp · 142,285 words
Dawn of the New Everything: Encounters With Reality and Virtual Reality
by Jaron Lanier · 21 Nov 2017 · 480pp · 123,979 words

Howard Rheingold
by The Virtual Community Homesteading on the Electronic Frontier-Perseus Books (1993) · 26 Apr 2012
The System: Who Owns the Internet, and How It Owns Us
by James Ball · 19 Aug 2020 · 268pp · 76,702 words
Whole Earth: The Many Lives of Stewart Brand
by John Markoff · 22 Mar 2022 · 573pp · 142,376 words
Barefoot Into Cyberspace: Adventures in Search of Techno-Utopia
by Becky Hogge, Damien Morris and Christopher Scally · 26 Jul 2011 · 171pp · 54,334 words
Content: Selected Essays on Technology, Creativity, Copyright, and the Future of the Future
by Cory Doctorow · 15 Sep 2008 · 189pp · 57,632 words
They Don't Represent Us: Reclaiming Our Democracy
by Lawrence Lessig · 5 Nov 2019 · 404pp · 115,108 words
The Government of No One: The Theory and Practice of Anarchism
by Ruth Kinna · 31 Jul 2019 · 405pp · 103,723 words
The Code: Silicon Valley and the Remaking of America
by Margaret O'Mara · 8 Jul 2019

Engineering Security
by Peter Gutmann
Kings of Crypto: One Startup's Quest to Take Cryptocurrency Out of Silicon Valley and Onto Wall Street
by Jeff John Roberts · 15 Dec 2020 · 226pp · 65,516 words
The People vs Tech: How the Internet Is Killing Democracy (And How We Save It)
by Jamie Bartlett · 4 Apr 2018 · 170pp · 49,193 words
The Great Firewall of China
by James Griffiths; · 15 Jan 2018 · 453pp · 114,250 words
The Age of Spiritual Machines: When Computers Exceed Human Intelligence
by Ray Kurzweil · 31 Dec 1998 · 696pp · 143,736 words
This Is for Everyone: The Captivating Memoir From the Inventor of the World Wide Web
by Tim Berners-Lee · 8 Sep 2025 · 347pp · 100,038 words

Likewar: The Weaponization of Social Media
by Peter Warren Singer and Emerson T. Brooking · 15 Mar 2018
From Counterculture to Cyberculture: Stewart Brand, the Whole Earth Network, and the Rise of Digital Utopianism
by Fred Turner · 31 Aug 2006 · 339pp · 57,031 words
Dawn of the Code War: America's Battle Against Russia, China, and the Rising Global Cyber Threat
by John P. Carlin and Garrett M. Graff · 15 Oct 2018 · 568pp · 164,014 words
Little Brother
by Cory Doctorow · 29 Apr 2008 · 398pp · 120,801 words
Fire in the Valley: The Birth and Death of the Personal Computer
by Michael Swaine and Paul Freiberger · 19 Oct 2014 · 459pp · 140,010 words
Silicon City: San Francisco in the Long Shadow of the Valley
by Cary McClelland · 8 Oct 2018 · 225pp · 70,241 words
Secrets and Lies: Digital Security in a Networked World
by Bruce Schneier · 1 Jan 2000 · 470pp · 144,455 words
The Naked Eye: How the Revolution of Laser Surgery Has Unshackled the Human Eye
by Gerard Sutton and Michael Lawless · 15 Nov 2013 · 175pp · 54,497 words
Black Code: Inside the Battle for Cyberspace
by Ronald J. Deibert · 13 May 2013 · 317pp · 98,745 words
Singularity Rising: Surviving and Thriving in a Smarter, Richer, and More Dangerous World
by James D. Miller · 14 Jun 2012 · 377pp · 97,144 words
The Panic Virus: The True Story Behind the Vaccine-Autism Controversy
by Seth Mnookin · 3 Jan 2012 · 566pp · 153,259 words
Bitcoin: The Future of Money?
by Dominic Frisby · 1 Nov 2014 · 233pp · 66,446 words
Dragnet Nation: A Quest for Privacy, Security, and Freedom in a World of Relentless Surveillance
by Julia Angwin · 25 Feb 2014 · 422pp · 104,457 words
Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World
by Bruce Schneier · 2 Mar 2015 · 598pp · 134,339 words
Free Ride
by Robert Levine · 25 Oct 2011 · 465pp · 109,653 words
Twitter and Tear Gas: The Power and Fragility of Networked Protest
by Zeynep Tufekci · 14 May 2017 · 444pp · 130,646 words
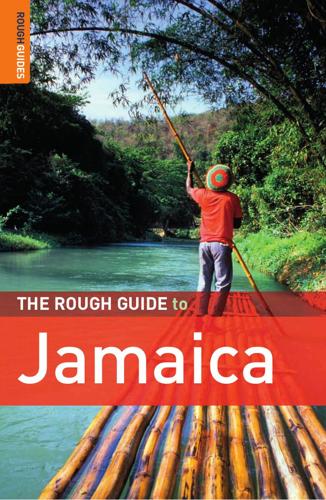
The Rough Guide to Jamaica
by Thomas, Polly,Henzell, Laura.,Coates, Rob.,Vaitilingam, Adam.
Click Here to Kill Everybody: Security and Survival in a Hyper-Connected World
by Bruce Schneier · 3 Sep 2018 · 448pp · 117,325 words
Surveillance Valley: The Rise of the Military-Digital Complex
by Yasha Levine · 6 Feb 2018 · 474pp · 130,575 words