The Art of UNIX Programming
by Eric S. Raymond · 22 Sep 2003 · 612pp · 187,431 words
, and Open Source chapters released. Shipped to Mark Taub at AW. Revision 0.0 1999 esr Public HTML draft, first four chapters only. * * * Dedication To Ken Thompson and Dennis Ritchie, because you inspired me. Preface Preface Unix is not so much an operating system as an oral history. -- Neal Stephenson There is
…
, Steven M. Bellovin, Stuart Feldman, Jim Gettys, Steve Johnson, Brian Kernighan, David Korn, Mike Lesk, Doug McIlroy, Marshall Kirk McKusick, Keith Packard, Henry Spencer, and Ken Thompson) added a great deal of value to this book. Doug McIlroy, in particular, went far beyond the call of duty in the thoroughness of his
…
something comes along to replace Ethernet, it will be called “Ethernet”, so therefore Ethernet will never die.[4] Unix has already undergone several such transformations. -- Ken Thompson At least one of Unix's central technologies — the C language — has been widely naturalized elsewhere. Indeed it is now hard to imagine doing software
…
learns it. Thus the loyalty Unix commands. Much of Unix's stability and success has to be attributed to its inherent strengths, to design decisions Ken Thompson, Dennis Ritchie, Brian Kernighan, Doug McIlroy, Rob Pike and other early Unix developers made back at the beginning; decisions that have been proven sound over
…
MVS TSO facility by Stephen C. Johnson, perhaps better known as the author of yacc. Basics of the Unix Philosophy The ‘Unix philosophy’ originated with Ken Thompson's early meditations on how to design a small but capable operating system with a clean service interface. It grew as the Unix culture learned
…
of Unix [Salus]): Rob Pike, who became one of the great masters of C, offers a slightly different angle in Notes on C Programming [Pike]: Ken Thompson, the man who designed and implemented the first Unix, reinforced Pike's rule 4 with a gnomic maxim worthy of a Zen patriarch: More of
…
and excessively complex code. In the Unix world there is a long-established and very explicit tradition (exemplified by Rob Pike's comments above and Ken Thompson's maxim about brute force) that says: Prototype, then polish. Get it working before you optimize it. Or: Make it work first, then make it
…
. The most powerful optimization tool in existence may be the delete key. One of my most productive days was throwing away 1000 lines of code. -- Ken Thompson (We'll go into a bit more depth about related ideas in Chapter 12.) Rule of Diversity: Distrust all claims for “one true way”. Even
…
Unix was born from that collapse. Genesis: 1969–1971 Unix was born in 1969 out of the mind of a computer scientist at Bell Laboratories, Ken Thompson. Thompson had been a researcher on the Multics project, an experience which spoiled him for the primitive batch computing that was the rule almost everywhere
…
ASR-33 was the natural parent of the Unix tradition of terse commands and sparse responses. When Bell Labs withdrew from the Multics research consortium, Ken Thompson was left with some Multics-inspired ideas about how to build a file system. He was also left without a machine on which to play
…
with thousands of pages of technical specifications written before the hardware arrived, the first running Unix code was brainstormed by three people and implemented by Ken Thompson in two days — on an obsolete machine that had been designed to be a graphics terminal for a ‘real’ computer. Unix's first real job
…
turned into a product; indeed, under the terms of the consent decree, Bell Labs was required to license its nontelephone technology to anyone who asked. Ken Thompson quietly began answering requests by shipping out tapes and disk packs — each, according to legend, with a note signed “love, ken”. This was years before
…
as the single most important academic hot-spot in Unix development. Unix research had begun there in 1974, and was given a substantial impetus when Ken Thompson taught at the University during a 1975-76 sabbatical. The first BSD release had been in 1977 from a lab run by a then-unknown
…
product. AT&T promptly rushed to commercialize Unix System V—a move that nearly killed Unix. So true. But their marketing did spread Unix internationally. -- Ken Thompson Most Unix boosters thought that the divestiture was great news. We thought we saw in the post-divestiture AT&T, Sun Microsystems, and Sun's
…
's another side to that story; to tell it, we'll need to return to 1961 and the origins of the Internet hacker culture. * * * [13] Ken Thompson reminded me that today's cellphones have more RAM than the PDP-7 had RAM and disk storage combined; a large disk, in those days
…
–2001, and proved to be a turning point in both the history of the hacker culture and of Unix. * * * [18] SPACEWAR was not related to Ken Thompson's Space Travel game, other than by the fact that both appealed to science-fiction fans. [19] Current and historical webserver share figures are available
…
a consequence rather than a goal. I abhor a system designed for the “user”, if that word is a coded pejorative meaning “stupid and unsophisticated”. -- Ken Thompson To design the perfect anti-Unix, write an operating system that thinks it knows what you're doing better than you do. And then adds
…
-end hardware. Indeed, a substantial fraction of the Linux user community is understood to be wringing usefulness out of hardware as technically obsolete today as Ken Thompson's PDP-7 was in 1969. As a consequence, Linux applications are under pressure to stay lean and mean that their counterparts under proprietary Unix
…
refinements in tools (like C structures) and good practice in using them (like Rob Pike's rules for programming) before we could tame that complexity. -- Ken Thompson Early Unix hackers struggled with this in many ways. In the languages of 1970 function calls were expensive, either because call semantics were complicated (PL
…
to break up a subprogram when there are too many local variables. Another clue is [too many] levels of indentation. I rarely look at length. -- Ken Thompson Does your code have internal APIs — that is, collections of function calls and data structures that you can describe to others as units, each sealing
…
monitor the results of many intermediate steps in parsing and code generation. This is exactly the structure of cc, the first (PDP-11) C compiler. -- Ken Thompson There are many benefits of this organization. One that is particularly important for GCC is regression testing.[60] Because most of the various intermediate formats
…
chapter that are worth emulating. One very important practice is an application of the Rule of Clarity: choosing simple algorithms. In Chapter 1 we quoted Ken Thompson: “When in doubt, use brute force”. Thompson understood the full cost of complicated algorithms — not just that they're more bug-prone when initially implemented
…
process (so that, for example, cut and paste among buffers can carry along internal emacs state information like font highlighting). Pipes, Redirection, and Filters After Ken Thompson and Dennis Ritchie, the single most important formative figure of early Unix was probably Doug McIlroy. His invention of the pipe construct reverberated through the
…
. dc is the oldest language on Unix; it was written on the PDP-7 and ported to the PDP-11 before Unix [itself] was ported. -- Ken Thompson The domain of these two languages is unlimited-precision arithmetic. Other programs can use them to do such calculations without having to worry about the
…
emphasizes doing simple implementations that work, and that ship quickly, even if the methods are brute-force and some edge cases have to be punted. Ken Thompson's code and his maxims about programming have often seemed to lean in this direction. The tension between these approaches arises precisely because one can
…
-seriously maintain that all editors with more features than ed has are simply bloated — and a few still who seriously believe this. Appropriately, ed was Ken Thompson's deliberate simplification of the earlier qed[RitchieQED] editor — which was very similar (and the first editor to use regular expressions in the characteristic Unix
…
not widely known outside the Labs, it's favored by many of the original Unix developers who went on to work on Plan 9, including Ken Thompson himself. Sam is a fairly straightforward descendant of ed, remaining much closer to its parent than vi. Sam incorporates only two new concepts: a curses
…
, that something is not hard to identify; it's the desire for convenience. While ed may be theoretically adequate, very few people (other than perhaps Ken Thompson himself) would forgo screen-oriented editing to make a statement about software bloat. More generally, programs that mediate between the user and the rest of
…
. You may recall that we quoted Donald Knuth observing “Premature optimization is the root of all evil” in Chapter 1, and that Rob Pike and Ken Thompson had a few pungent observations on the topic as well. These were the voices of experience. Do good design. Think about what's right first
…
of C. Early History of C C began life in 1971 as a systems-programming language for the PDP-11 port of Unix, based on Ken Thompson's earlier B interpreter which had in turn been modeled on BCPL, the Basic Common Programming Language designed at Cambridge University in 1966-67.[142
…
be readily found with a Web search for the phrase ‘Plan 9 from Bell Labs’. [155] The tale of how UTF-8 was born involves Ken Thompson, Rob Pike, a new Jersey diner, and a frenzied overnight hack. Problems in the Design of Unix Plan 9 cleans up Unix, but only really
…
remote interface (a la Plan 9) and then have it implemented across the Internet as the standard rather than HTML. That would be ultimate cool. -- Ken Thompson * * * [156] Look for F_NOTIFY under fcntl(2). [157] This paragraph is based on a 1984 analysis by Henry Spencer. He went on to note
…
. Ritchie. An Incomplete History of the QED Text Editor. 2003. Available on the Web. [Ritchie-Thompson] The Unix Time-Sharing System. Dennis M. Ritchie and Ken Thompson. Available on the Web. [Saltzer] ACM Transactions on Computer Systems. Association for Computing Machinery. James. H. Saltzer, David P. Reed, and David D. Clark. “End
…
was a coauthor of C News, and has for many years been a voice of reason on Usenet and one of its most respected regulars. Ken Thompson invented Unix. Unix Koans Appendix D. Rootless Root The Unix Koans of Master Foo Editor's Introduction The discovery of the collection of koans known
The Dream Machine: J.C.R. Licklider and the Revolution That Made Computing Personal
by M. Mitchell Waldrop · 14 Apr 2001
conventional GE 635 computer that would operate in a conventional batch-processing mode. But then a funny thing happened: two of Bell's former Multicians, Ken Thompson and Dennis Ritchie, began suffering from withdrawal pangs. As baroque as Multics was, it was responsive, interactive, alive. And once they no longer had it
…
data tapes (nominal charge: $150 for materials), and you got the complete source code, which was yours to modify as you wished. Dennis Ritchie and Ken Thompson had created Unix for their own use back in 1969, after Bell Labs' withdrawal from the Multics partnership, and the project had retained that loose
…
. Ross, OH 65, OH 178;Jack P. Ruina, OH 163;Jules I. Schwartz, OH 161; Ivan Sutherland, OH 171; Robert A. Tay- lor, OH 154; Ken Thompson, OH 239;Joseph F. Traub, OH 70, OH 89, OH 94; Keith W. Uncapher, OH 174; Frank M. Verzuh, OH 63; David A. Walden, OH
Coders at Work
by Peter Seibel · 22 Jun 2009 · 1,201pp · 233,519 words
Armstrong Chapter 7: Simon Peyton Jones Chapter 8: Peter Norvig Chapter 9: Guy Steele Chapter 10: Dan Ingalls Chapter 11: L Peter Deutsch Chapter 12: Ken Thompson Chapter 13: Fran Allen Chapter 14: Bernie Cosell Chapter 15: Donald Knuth Appendix A: Bibliography Index About the Author Peter Seibel is either a writer
…
at Work. I sat down with fifteen highly accomplished programmers with a wide range of experiences in the field—heads down systems hackers such as Ken Thompson, inventor of Unix, and Bernie Cosell, one of the original implementers of the ARPANET; programmers who combine strong academic credentials with hacker cred such as
…
interest in computer science in recent decades at the feet of C and Bernie Cosell called it the “biggest security problem to befall modern computers”, Ken Thompson argued that security problems are caused by programmers, not their programming languages and Donald Knuth described C's use of pointers as one of the
…
? That's fairly strict. Seibel: You told me once that when Guido van Rossum came here he had to get checked out on Python and Ken Thompson had to get checked out on C, to make sure they could meet very explicit coding standards. Do you have design standards that are equally
…
at UC Berkeley, he got involved with Project Genie, one of the first minicomputer-based timesharing systems, writing most of the operating system's kernel. (Ken Thompson, inventor of Unix and the subject of Chapter 12, would also work on the project while a grad student at Berkeley, influencing his later work
…
, I saw a world that was completely dominated by an unethical monopolist, and I didn't see much of a place for me in it. Ken Thompson Ken Thompson is the original bearded Unix hacker. He has spent a career working on whatever he finds interesting, which has, at various times, included analog computing
…
was a brilliant scheme. It's teaching them a lesson that is hard to get except in the real world. Seibel: When I talked to Ken Thompson I asked him about whether there were inherent problems in C that lead to security problems and he basically said that's not the problem
Crash of the Titans: Greed, Hubris, the Fall of Merrill Lynch, and the Near-Collapse of Bank of America
by Greg Farrell · 2 Nov 2010 · 526pp · 158,913 words
-management systems, which had failed miserably in overseeing Semerci, also reported to Fakahany. O’Neal asked Fleming if he still had a good relationship with Ken Thompson, chief executive of Wachovia Bank in Charlotte. “Yes,” said Fleming. For more than a decade, like its crosstown competitor, BofA, Wachovia had been a serial
…
control. Wachovia, O’Neal figured, would be different. There would be a “softer landing” for Merrill Lynch. The price would not be as high, but Ken Thompson might allow Merrill to retain some autonomy. A deal with Wachovia would resemble a merger more than an acquisition. With a special board meeting a
Deep Thinking: Where Machine Intelligence Ends and Human Creativity Begins
by Garry Kasparov · 1 May 2017 · 331pp · 104,366 words
most amateurs. The next leap came out of the famous Bell Laboratories in New Jersey, which churned out patents and Nobel Prize winners for decades. Ken Thompson built a special-purpose chess machine with hundreds of chips. His machine, Belle, was able to search about 180,000 positions per second while the
…
the twelfth annual North American Computer Chess Championship, held in Los Angeles in 1982, the world’s best chess machines battled each other for supremacy. Ken Thompson’s special-purpose hardware machine Belle continued to show its superiority over the rest, and to show the potential for a hardware architecture and customized
…
seminal scientific experiments in biology, especially genetics. By the end of the 1980s, the computer chess community had largely resigned this great experiment. In 1990, Ken Thompson of Belle was openly recommending the game Go as a more promising target for real advances in machine cognition. In the same year, the compendium
…
correct in the playing hall, and was always seated in the front row. Frederic Friedel was there to serve as my unofficial computer chess advisor. Ken Thompson, the creator of Belle and who was still very involved in computer chess, agreed to be a sort of neutral overseer of the computer. Compared
…
the Deep Blue team wanted to improve, or because Garry Kasparov wanted another paycheck. It would because IBM wanted to win. CHAPTER 8 DEEPER BLUE KEN THOMPSON designed the revolutionary chess machine Belle, whose chips Deep Blue’s were based on, while working at Bell Laboratories in New Jersey, the famous “Idea
…
he thought his eclectic hobbies like playing Brazilian music and lock-picking actually helped him be better at physics instead of distracting him from it. Ken Thompson enjoys piloting himself around in a small plane. And even if it’s too late for you to win that Nobel, it’s never too
…
the printouts, hoping that at least there would be a permanent record for public examination. After some negotiations, Tan said he would give them to Ken Thompson, who was on the Appeals Board and was operating as a neutral tech supervisor, as he had in Philadelphia. That also did not happen despite
…
my suspicions. They continued to stonewall us on releasing the printouts from game two, which, if they had showed nothing amiss in the eyes of Ken Thompson, could have relieved some of my stress about what was going on behind the scenes. My agent Owen Williams told the organizers before game four
…
help it achieve the miraculous draw. There were rumors that the machine could access endgame tablebases during its analysis, and, if so, I would have Ken Thompson to blame for it. In 1977, Thompson showed up at the World Computer Chess Championship with a new creation, a database that played the king
…
. Frederic Friedel sparked my interest in chess machines, although he loves them so much I’ve never been completely sure whose side he’s on. Ken Thompson lent his invaluable expertise and goodwill to my sport and to my matches against machines. David Levy and Monty Newborn saw computer chess as a
The End of Wall Street
by Roger Lowenstein · 15 Jan 2010 · 460pp · 122,556 words
THAIN, former Goldman executive who replaced O’Neal as CEO of Merrill Lynch; after early stock sale resisted advice to raise more equity G. KENNEDY (KEN) THOMPSON, CEO of Wachovia, acquired high-flying Golden West, even as he predicted it could get him fired PAOLO TONUCCI, Lehman treasurer, prepared a list of
…
’s growth rate had been in double digits, it was clearly destined to slow down. Nonetheless, its CEO, a native North Carolinian named G. Kennedy “Ken” Thompson, was publicly committed to maintaining its growth. Acquisitions were the only route. In the spring of 2006, Lehman Brothers suggested that Wachovia might want to
…
entitlement and invincibility. Ultimately, the bankers fooled themselves. If their personal fortunes were guaranteed, how could the fate of their institutions be otherwise? In 2006, Ken Thompson earned $18 million for his handiwork in acquiring Golden West; Daniel Mudd netted $15 million from Fannie Mae; Angelo Mozilo, $43 million at Countrywide; John
…
a new high—utterly unforeseen in the rating agency models—of 18 percent. 5 Institutions touched by subprime could not escape collateral damage. At Wachovia, Ken Thompson, the chief executive, had predicted two years earlier that his acquisition of Golden West could get him fired. In June, it did. As subprime plummeted
Your Computer Is on Fire
by Thomas S. Mullaney, Benjamin Peters, Mar Hicks and Kavita Philip · 9 Mar 2021 · 661pp · 156,009 words
/10/09/upshot/as-sexual-harassment-scandals-spook-men-it-can-backfire-for-women.html. 13 Source Code Isn’t Ben Allen American computer programmer Ken Thompson is best known for his role in the creation of the Unix operating system and of C, the programming language in which Unix is written
…
quine programs is still a semi-popular recreational programming exercise.13 How, though, does the quine game relate to Thompson’s hack? In this speech Ken Thompson is accepting the highest award that the Association for Computing Machinery gives, an award often called the Nobel Prize for computer scientists. Why does he
…
lore dating from 1975 that was eventually repackaged and published as the New Hacker’s Dictionary, claims the following in its entry for “back door”: Ken Thompson has since confirmed that this hack was implemented and that the Trojan Horse code did appear in the login binary of a Unix Support group
…
chastisement from the instructors. Who gets to creatively play with computer technology depends less on creativity and more on identity categories. In the early 1970s, Ken Thompson, esteemed Bell Labs employee, was empowered to play with his company’s machines in order first to implement an esoteric but extraordinarily effective Trojan horse
…
language used to develop that system, and many of the software tools used on that system, Ken Thompson was in a position of tremendous power. If, to use Lawrence Lessig’s famous analogy, “code is law,” Ken Thompson had the power to write and alter the digital constitution by personal fiat.33 Thompson’s
…
sixth and C itself as the eighth most widely used language. Github, “Octoverse Report,” accessed August 13, 2020, https://octoverse.github.com/projects#languages. 2. Ken Thompson, “Reflections on Trusting Trust,” Communications of the ACM 27, no. 8 (1984): 761–763. 3. In his recent book Bits to Bitcoin, Mark Stuart Day
…
Hacker’s Dictionary (Cambridge, MA: MIT Press, 1996), 51. 30. Posted by Jay Ashworth to alt.folklore.computers (April 39, 1995). From private correspondence with Ken Thompson. 31. Sreela Sarkar, “Skills Will Not Set You Free,” this volume. 32. Sarkar, “Skills Will Not Set You Free.” 33. For one of Lessig’s

Fancy Bear Goes Phishing: The Dark History of the Information Age, in Five Extraordinary Hacks
by Scott J. Shapiro · 523pp · 154,042 words
result of decision by committee. In 1969, part of the Multics group broke away and started over. This new team, led by Dennis Ritchie and Ken Thompson, operated out of an attic at Bell Labs using a spare PDP-7, a “minicomputer” built by the Digital Equipment Corporation (DEC) that cost ten
…
“scripts” that can perform more complex tasks. The name UNIX began as a pun: because early versions of the operating system supported only one user—Ken Thompson—Peter Neumann, a security researcher at Stanford Research International, joked that it was an “emasculated Multics,” or “UNICS.” The spelling was eventually changed to UNIX
…
crime: the Counterfeit Access Device and Computer Fraud and Abuse Act of 1984, enacted in October 1984. Politicians were not the only ones concerned. When Ken Thompson won the Turing Lifetime Achievement Award in 1984, the highest honor in the computer-science community, for developing UNIX, he devoted his lecture to cybersecurity
…
twenty-six years at Bell Labs. During that time, he had created many of the core utilities of UNIX. Indeed, he was close friends with Ken Thompson, who a few years earlier had publicly denounced whiz-kid hackers as drunk drivers. Given his position, Bob understood that his son was in legal
…
-force attack that does not require much coding talent either. In fact, Morris’s father wrote about this type of attack in an article with Ken Thompson published in 1979. The fourth vector—the attack on Finger—was inspired, however. Even Eugene Spafford was impressed. In a comment buried deep in the
…
Program: An Analysis,” Purdue Technical Report CSD-TR-823, November 29, 1988, 2, https://spaf.cerias.purdue.edu/tech-reps/823.pdf. Ken Thompson published in 1979: Robert Morris Sr. and Ken Thompson, “Password Security: A Case History,” Communications of the ACM, 22, 11 (January 1979), 595. “What this routine does”: Source code for
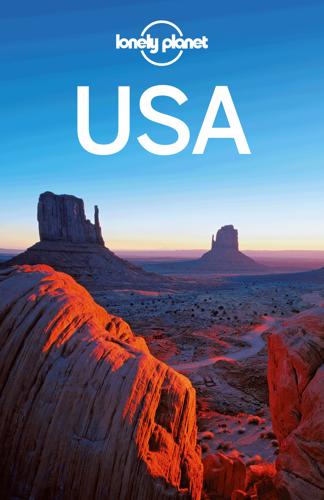
USA Travel Guide
by Lonely, Planet
’s best and most popular strands; Siesta Village is also a lively, family-friendly beach town. Mote Aquarium ( 941-388-4441; www.mote.org; 1600 Ken Thompson Pkwy; adult/child $17/12; 10am-5pm) is a leading shark research center providing intimate encounters with sharks, manatees, sea turtles, rays and more, plus

Engineering Security
by Peter Gutmann
different colours in different situations [562], let alone knowing what it was that the different colours signified (the depicted dialog is another gem from the “Ken Thompson’s car” school of user interface design that’s discussed below). Another study, carried out by Microsoft themselves, found that only 13% of users could
…
]. Bonus points if you can explain the significance of those distinctions. (The dialog in Figure 63 is reminiscent of a fable about the car that Ken Thompson, one of the creators of Unix, helped design. Whenever there’s a problem a giant ‘?’ lights up on the dashboard. When asked about this Ken
…
better” [274]111. Case Study: Windows UAC Previous sections have described the usability problems of Windows Vista’s UAC prompts, which comes straight from the “Ken Thompson’s car” school of user interface design (it should be mentioned here that the open-source world is no better when it comes to communicating
…
that any resulting decision made by the user, whether a rank beginner or hardcore geek, as reduced to a coin toss. Figure 131, from the “Ken Thompson’s car” school of user interface design, is an example of such a coin-toss interface. The easiest way to determine how to speak the
…
(July 1978), p.54. [258] “Multics Security”, Tom Van Vleck, http://www.multicians.org/security.html. [259] “Password Security: A Case History”, Robert Morris and Ken Thompson, Communications of the ACM, Vol.22, No.11 (November 1979), p.594. [260] “A Study of Password Security”, Michael Luby and Charles Rackoff, Journal of
The Next Great Migration: The Beauty and Terror of Life on the Move
by Sonia Shah
Artificial Intelligence: A Modern Approach
by Stuart Russell and Peter Norvig · 14 Jul 2019 · 2,466pp · 668,761 words
Paper Knowledge: Toward a Media History of Documents
by Lisa Gitelman · 26 Mar 2014
The Firm
by Duff McDonald · 1 Jun 2014 · 654pp · 120,154 words
I Can't Breathe
by Matt Taibbi · 23 Oct 2017 · 392pp · 112,954 words
Into the Wild
by Jon Krakauer · 2 Jan 1996 · 216pp · 70,341 words
Rebel Code: Linux and the Open Source Revolution
by Glyn Moody · 14 Jul 2002 · 483pp · 145,225 words
Dawn of the Code War: America's Battle Against Russia, China, and the Rising Global Cyber Threat
by John P. Carlin and Garrett M. Graff · 15 Oct 2018 · 568pp · 164,014 words
Protocol: how control exists after decentralization
by Alexander R. Galloway · 1 Apr 2004 · 287pp · 86,919 words
This Is How They Tell Me the World Ends: The Cyberweapons Arms Race
by Nicole Perlroth · 9 Feb 2021 · 651pp · 186,130 words
In the Plex: How Google Thinks, Works, and Shapes Our Lives
by Steven Levy · 12 Apr 2011 · 666pp · 181,495 words
Computer: A History of the Information Machine
by Martin Campbell-Kelly and Nathan Ensmenger · 29 Jul 2013 · 528pp · 146,459 words
Coders: The Making of a New Tribe and the Remaking of the World
by Clive Thompson · 26 Mar 2019 · 499pp · 144,278 words
All the Devils Are Here
by Bethany McLean · 19 Oct 2010 · 543pp · 157,991 words
Too big to fail: the inside story of how Wall Street and Washington fought to save the financial system from crisis--and themselves
by Andrew Ross Sorkin · 15 Oct 2009 · 351pp · 102,379 words
Eastern USA
by Lonely Planet
Average Is Over: Powering America Beyond the Age of the Great Stagnation
by Tyler Cowen · 11 Sep 2013 · 291pp · 81,703 words
Smart Mobs: The Next Social Revolution
by Howard Rheingold · 24 Dec 2011
Dark Mirror: Edward Snowden and the Surveillance State
by Barton Gellman · 20 May 2020 · 562pp · 153,825 words
Kill It With Fire: Manage Aging Computer Systems
by Marianne Bellotti · 17 Mar 2021 · 232pp · 71,237 words
The Most Human Human: What Talking With Computers Teaches Us About What It Means to Be Alive
by Brian Christian · 1 Mar 2011 · 370pp · 94,968 words
The Wikipedia Revolution: How a Bunch of Nobodies Created the World's Greatest Encyclopedia
by Andrew Lih · 5 Jul 2010 · 398pp · 86,023 words
The Architecture of Open Source Applications
by Amy Brown and Greg Wilson · 24 May 2011 · 834pp · 180,700 words
WTF?: What's the Future and Why It's Up to Us
by Tim O'Reilly · 9 Oct 2017 · 561pp · 157,589 words
Wilding: The Return of Nature to a British Farm
by Isabella Tree · 2 May 2018 · 473pp · 124,861 words
The Art of Software Security Assessment: Identifying and Preventing Software Vulnerabilities
by Justin Schuh · 20 Nov 2006 · 2,054pp · 359,149 words
Bread, Wine, Chocolate: The Slow Loss of Foods We Love
by Simran Sethi · 10 Nov 2015 · 396pp · 112,832 words
Designing Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable Systems
by Martin Kleppmann · 17 Apr 2017
Not the End of the World
by Hannah Ritchie · 9 Jan 2024 · 335pp · 101,992 words
JavaScript: the good parts
by Douglas Crockford · 15 Nov 2008 · 273pp · 46,214 words
The Linux kernel primer: a top-down approach for x86 and PowerPC architectures
by Claudia Salzberg Rodriguez, Gordon Fischer and Steven Smolski · 15 Nov 2005 · 1,202pp · 144,667 words
Turing's Vision: The Birth of Computer Science
by Chris Bernhardt · 12 May 2016 · 210pp · 62,771 words
The Future of Ideas: The Fate of the Commons in a Connected World
by Lawrence Lessig · 14 Jul 2001 · 494pp · 142,285 words
How Cycling Can Save the World
by Peter Walker · 3 Apr 2017 · 231pp · 69,673 words
The Mysterious Mr. Nakamoto: A Fifteen-Year Quest to Unmask the Secret Genius Behind Crypto
by Benjamin Wallace · 18 Mar 2025 · 431pp · 116,274 words
Deaths of Despair and the Future of Capitalism
by Anne Case and Angus Deaton · 17 Mar 2020 · 421pp · 110,272 words
Designing Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable Systems
by Martin Kleppmann · 16 Mar 2017 · 1,237pp · 227,370 words
Team Geek
by Brian W. Fitzpatrick and Ben Collins-Sussman · 6 Jul 2012 · 209pp · 54,638 words
Halting State
by Charles Stross · 9 Jul 2011 · 350pp · 107,834 words
Commodore: A Company on the Edge
by Brian Bagnall · 13 Sep 2005 · 781pp · 226,928 words
The Practice of Cloud System Administration: DevOps and SRE Practices for Web Services, Volume 2
by Thomas A. Limoncelli, Strata R. Chalup and Christina J. Hogan · 27 Aug 2014 · 757pp · 193,541 words
The Mythical Man-Month
by Brooks, Jr. Frederick P. · 1 Jan 1975 · 259pp · 67,456 words
Nexus
by Ramez Naam · 16 Dec 2012 · 502pp · 124,794 words
Masterminds of Programming: Conversations With the Creators of Major Programming Languages
by Federico Biancuzzi and Shane Warden · 21 Mar 2009 · 496pp · 174,084 words
New York 2140
by Kim Stanley Robinson · 14 Mar 2017 · 693pp · 204,042 words
Hacking Capitalism
by Söderberg, Johan; Söderberg, Johan;
My Life as a Quant: Reflections on Physics and Finance
by Emanuel Derman · 1 Jan 2004 · 313pp · 101,403 words
The Idea Factory: Bell Labs and the Great Age of American Innovation
by Jon Gertner · 15 Mar 2012 · 550pp · 154,725 words
Free as in Freedom
by Sam Williams · 16 Nov 2015
Brexit and Ireland: The Dangers, the Opportunities, and the Inside Story of the Irish Response
by Tony Connelly · 4 Oct 2017 · 356pp · 112,271 words
Androids: The Team That Built the Android Operating System
by Chet Haase · 12 Aug 2021 · 580pp · 125,129 words
Personal Kanban: Mapping Work, Navigating Life
by Jim Benson and Tonianne Demaria Barry · 2 Feb 2011 · 147pp · 37,622 words
Roads and Bridges
by Nadia Eghbal · 139pp · 35,022 words
Hacking Exposed: Network Security Secrets and Solutions
by Stuart McClure, Joel Scambray and George Kurtz · 15 Feb 2001 · 260pp · 40,943 words
Red Moon
by Kim Stanley Robinson · 22 Oct 2018 · 492pp · 141,544 words

Code: The Hidden Language of Computer Hardware and Software
by Charles Petzold · 28 Sep 1999 · 566pp · 122,184 words
The C Programming Language
by Brian W. Kernighan and Dennis M. Ritchie · 15 Feb 1988 · 238pp · 93,680 words
The Switch: How Solar, Storage and New Tech Means Cheap Power for All
by Chris Goodall · 6 Jul 2016 · 271pp · 79,367 words
Fire in the Valley: The Birth and Death of the Personal Computer
by Michael Swaine and Paul Freiberger · 19 Oct 2014 · 459pp · 140,010 words
How We Got Here: A Slightly Irreverent History of Technology and Markets
by Andy Kessler · 13 Jun 2005 · 218pp · 63,471 words
Practical C Programming, 3rd Edition
by Steve Oualline · 15 Nov 2011 · 544pp · 96,029 words