Laura Poitras
description: an American documentary film director, known for her work on surveillance, privacy, and national security issues
43 results
The Snowden Files: The Inside Story of the World's Most Wanted Man
by Luke Harding · 7 Feb 2014 · 266pp · 80,018 words
edifice in the heart of the tourist district, and a short cab ride away from the Star Ferry to Hong Kong Island. Accompanying Greenwald was Laura Poitras, also an American citizen, documentary film-maker and notable thorn in the side of the US military. She had been a matchmaker, the first to
…
the remorseless stream of Twitter. At the end of January 2013, Snowden tried a different way to get to him. He sent an email to Laura Poitras. He was hoping to open an anonymous channel to the documentary film-maker, who was Greenwald’s friend and a close collaborator. Poitras was another
…
, Miranda had set off from their home in Rio de Janeiro to Berlin, flying via Heathrow. He spent several days with Greenwald’s fellow journalist Laura Poitras in the German capital. They discussed film projects. He did some sightseeing. He spent a couple of nights in a hotel. He was now flying
…
, Paul Johnson, Jeff Larson, David Leigh, Paul Lewis, Ewen MacAskill, Justin McCurry, Stuart Millar, Sara Montgomery, Richard Norton-Taylor, Philip Oltermann, Anna Pallai, Gill Phillips, Laura Poitras, Mark Rice-Oxley, Alan Rusbridger, Phoebe Taplin and Jon Watts
Breaking News: The Remaking of Journalism and Why It Matters Now
by Alan Rusbridger · 14 Oct 2018 · 579pp · 160,351 words
. Greenwald, as already discussed, lived in Rio with his partner, David Miranda, and 13 rescue dogs. I had never met him. Snowden had also contacted Laura Poitras,7 a gifted filmmaker with, it seemed, a marked antipathy to mainstream media. I had never met her either. Finally, Snowden was also in touch
…
could take two or three years and cost millions. We (and the government) would watch impotently as the NYT, Washington Post, ProPublica, Der Spiegel and Laura Poitras had a field day with the material we no longer had. We were certainly not handing anything over to the government. We owed it to
…
hours at Heathrow airport under Schedule 7 of the UK Terrorism Act 2000. He had (unknown to us) been acting as a go-between for Laura Poitras and Greenwald. Section 7 is intended for the purpose of determining whether the detained person is engaged in instigating acts of terrorism. The former lord
…
, George Brock, Charlie Beckett, Ian Hargreaves, Mark Thompson, Lloyd Embley, Maya Wolfe-Robinson, Jamie Wilson, Richard Sambrook, Jim Brady, Paul Foot, Stephen Engelberg, Paul Steiger, Laura Poitras, Jean Seaton, Hugh Muir, Mathew Ingram, Damian Tambini, Sarah Ellison, Eleanor Randolph, Martin Moore, Jane Martinson, Andrew Marr, Charles Moore, Steve Bell, Alexander Chancellor, Jacob
…
the CPJ and in 2017 led a delegation to protest at the extra-judicial killings of Ukrainian journalists. 59. Alan Rusbridger, Janine Gibson, Stuart Millar, Laura Poitras, Ewen MacAskill, Spencer Ackerman. The other main journalists, lawyers, technical advisers involved and so on, apart from Glenn Greenwald and
…
Laura Poitras – included Jeff Larson, Stephen Engelberg, Paul Steiger, James Ball, Nick Hopkins, David Leigh, Nick Davies, David Blishen, Henry Porter, Wolfgang Blau, Lenore Taylor, Gabriel Dance,
Dark Mirror: Edward Snowden and the Surveillance State
by Barton Gellman · 20 May 2020 · 562pp · 153,825 words
was fraught. He knew that I would not join his crusade, and he never relied on me to take his side as he did with Laura Poitras and Glenn Greenwald. We struggled over boundaries—mine as a journalist who wanted to know more, his as an advocate who saw his cause at
…
to lock them down tighter. That thought had reassured me once. It was the second half of May 2013. Nearly four months had passed since Laura Poitras, an independent filmmaker, reached out to me for advice about a confidential source. Verax, as I came to know him later, had brought her an
…
tracking device. It works well as a remote-controlled microphone, too, for someone who knows how to switch it on. * * * — The first time I met Laura Poitras, three days before Christmas 2010, she turned up unannounced at my office, just off Washington Square. Karen Greenberg, a mutual friend who ran a lively
…
showed participants how to work and communicate safely in an untrusted environment. One of the habits he taught them became a signature moment in the Laura Poitras film Citizen Four. Cover your keyboard with a blanket, he said, when typing your password. “He came across as brilliant,” Massarini said, with a gift
…
to novitiates at the cryptoparty in Honolulu. More to the point, he was staking his freedom on Tor as he contacted journalists. His conversations with Laura Poitras had begun three weeks before, and Poitras had already come to see me in New York. If Tor could be compromised, so might we all
…
Snowden’s interactions with me—when, how and why—are all false,” he wrote in the first of a series of angry posts on Twitter. “Laura Poitras and I have been working with him since February, long before anyone spoke to Bart Gellman.” He elaborated in his book No Place to Hide
…
the months to come. Three days after the PRISM story went live, Snowden announced his identity to the world in a twelve-minute video that Laura Poitras shot for the Guardian. Danielle Massarini was killing time in a Newark Liberty International Airport bar on her way to Germany. “I’m scrolling through
…
director in the course of a half-century career. In 2014, Clapper had come as close as anyone in government to accusing me, along with Laura Poitras and Glenn Greenwald, of taking part in a criminal conspiracy with Snowden. Four years later, in the summer of 2018, he agreed to meet face
…
. In meetings that fall, Alexander asked more than once about staging raids to seize control of unpublished Snowden documents in the hands of Glenn Greenwald, Laura Poitras, and me. He saw no reason for the government to sit back and watch as its precious secrets were spilled. It was only common sense
…
for weeks across multiple departments, including the Department of Justice. And “accomplice” has a meaning in criminal law. “I had in mind Glenn Greenwald or Laura Poitras,” Clapper told me years later, unrepentant, as the remains of his egg white omelet were cleared from the table. “They conspired with him, they helped
…
intelligence. Three of the best examples were obvious nonstarters: mentioning them would blow ongoing, productive collection against a significant U.S. adversary. Glenn Greenwald and Laura Poitras, who knew about all three of these stories, had decided independently not to publish them either. (I know that only because they did not do
…
technical officer in Geneva. Team Homeland did not seem convinced. Snowden doubled down, telling his audience about an early conversation between the two of us. Laura Poitras and I had received the first of his leaks but had not yet begun to publish. Snowden had warned me to hurry. “When I was
…
why. I have written about the text file called “README_FIRST,” which Snowden composed to accompany the NSA archive when he first conveyed it to Laura Poitras and me on May 21, 2013. In it he introduced himself by name and delivered an antisurveillance manifesto. The story I never wrote was the
…
to a vital public debate about the boundaries of secret intelligence in a free society. For introducing us, and for our early collaboration, I thank Laura Poitras. For helping us navigate a complex relationship, I owe Ben Wizner, Snowden’s lawyer at the ACLU, the world’s tallest beer. Hundreds of people
…
, New Zealand, and Australia. The paper has been reproduced online at https://perma.cc/CL7E-6VY9. It was first described publicly in James Risen and Laura Poitras, “N.S.A. Report Outlined Goals for More Power,” New York Times, November 22, 2013, https://nyti.ms/31ToL5T. “I’m not sure I’ll
…
the first contact with Poitras, the would-be confidential source wrote to him on January 11, 2013, saying, “I need to get information securely to Laura Poitras and her alone, but I can’t find an email/gpg key for her. Can you help?” Lee sent the source her key and verified
…
/. Other news sites have published portions of additional slides. They are aggregated at https://nsa.gov1.info/dni/prism.html. See also Barton Gellman and Laura Poitras, “U.S., British Intelligence Mining Data from Nine U.S. Internet Companies in Broad Secret Program,” Washington Post, June 7, 2013, http://wapo.st/1LcAw6p
…
the 2007 Academy Award nomination, see https://to.pbs.org/1QJZkGk. failed attempt to install democracy: “Interview: Laura Poitras, Director of ‘My Country, My Country,’” Indiewire, July 31, 2006, www.indiewire.com/article/indiewire_interview_laura_poitras_director_of_my_country_my_country. her latest, The Oath: See Zeitgeist Films, press kit, 2010, https
…
and Devastating Consequences,” American Civil Liberties Union, March 2014, www.aclu.org/us-government-watchlisting-unfair-process-and-devastating-consequences. “confiscated my laptop”: Affidavit of Laura Poitras, paragraph 35, August 24, 2016, in Poitras v. Department of Homeland Security, Civil Action No. 15-cv-01091-KBJ. U.S. government’s pretense: In
…
2011, at http://itlaw.wikia.com/wiki/NSANet, according to this date-based Google search: https://goo.gl/j0Jc8y. short film on another NSA critic: Laura Poitras, “The Program,” New York Times, August 23, 2012, http://nyti.ms/1TBmnJp, was a profile of the whistleblower William Binney for the newspaper’s “Op
…
like a Bond villain’s lair”: Snowden, encrypted live chat with author, February 14, 2014. other noms de code: At various stages of interaction with Laura Poitras, Glenn Greenwald, and me, Snowden used alter egos including Cincinnatus, anon108, and Citizen Four. “I was starting to operationalize”: Snowden, interview with author, July 1
…
involved a pair of case officers: Snowden, Permanent Record, 158–59. He first told a version of this story in Glenn Greenwald, Ewen MacAskill, and Laura Poitras, “Edward Snowden: The Whistleblower Behind the NSA Surveillance Revelations,” Guardian, June 11, 2013, www.theguardian.com/world/2013/jun/09/edward-snowden-nsa-whistleblower-surveillance
…
(UTT)/Gamut,” March 30, 2010, classified S//SI//REL, on file with author. CAPTAINCRUNCH: Confidential source, interview with author, 2015. In his first filmed interview: Laura Poitras and Glenn Greenwald, “NSA Whistleblower Edward Snowden: ‘I Don’t Want to Live in a Society That Does These Sort of Things,’” Guardian, June 9
…
to foreign diplomats, not to an audience of news consumers at large. “I just read his email”: Transcript of anonymous, encrypted chat between author and Laura Poitras, May 25, 2013. I am aware that this exchange with Poitras may be quoted selectively by critics who have long accused Snowden of betraying his
…
the Guardian.” As I explain in the previous note, my account was accurate but unavoidably incomplete. Gellman, “Code Name ‘Verax,’” Washington Post, June 9, 2013. “Laura Poitras and I”: Tweet by Glenn Greenwald (@ggreenwald), June 10, 2013, https://twitter.com/ggreenwald/status/344040301972815872, archived at https://archive.is/VMnMk. See also Mackenzie
…
/1pBnqfl, archived at https://archive.is/fFeol. unaware that Verax was the Cincinnatus: Greenwald, No Place to Hide, 82. “clueless on the security-technical side”: Laura Poitras, “Berlin Journal,” in Astro Noise: A Survival Guide for Living Under Total Surveillance (New York: Whitney Museum of American Art, 2016), 95. Verax connected with
…
I Teach You,” Intercept, October 28, 2014, http://interc.pt/1DXiB2S; Greenwald, No Place to Hide, especially 7–26; the “Berlin Journal” extracts reproduced in Laura Poitras, ed., Astro Noise: A Survival Guide for Living Under Total Surveillance (New York: Whitney Museum of American Art, 2016); screen shots from the documentary film
…
how. January 6, 2013—As anon108, Snowden sends Greenwald an instructional video on encryption. Greenwald does not reply. January 11, 2013—anon108 shifts focus to Laura Poitras, asking technology activist Micah Lee of the Electronic Frontier Foundation to supply a trustworthy encryption key for her. January 28, 2013—As “Citizen Four,” Snowden
…
: The Men Who Leaked the Secrets,” Rolling Stone, December 4, 2013, http://rol.st/1bIGujx, and Auletta, “Freedom of Information.” See also Peter Maass, “How Laura Poitras Helped Snowden Spill His Secrets,” New York Times Magazine, August 13, 2013, http://nyti.ms/2eAYykb. Now and then, when critics accused him of treason
…
other people say than what I do. I reconstructed my own comments shortly after we hung up. We moved the PRISM story: Barton Gellman and Laura Poitras, “U.S., British Intelligence Mining Data from Nine U.S. Internet Companies in Broad Secret Program,” Washington Post, June 6, 2013, http://wapo.st/1LcAw6p
…
Gellman and Sam Adler-Bell, “The Disparate Impact of Surveillance,” Century Foundation, December 21, 2017, at http://perma.cc/WV8A-ZMV3. learned from Der Spiegel: Laura Poitras, Marcel Rosenbach, Fidelius Schmid, and Holger Stark, “NSA Spied on European Union Offices,” Der Spiegel, June 29, 2013, at https://archive.is/5So5r. Standard Form
…
Ashkan Soltani’s older sister, July 2018. The family prefers that I not name the siblings and parents. my first NSA story: Barton Gellman and Laura Poitras, “U.S., British Intelligence Mining Data from Nine U.S. Internet Companies in Broad Secret Program,” Washington Post, June 6, 2013, http://wapo.st/1LcAw6p
…
,” Intercept, June 30, 2016, republished on January 31, 2017, at https://perma.cc/HRW5-ETNP. his coming-out video: The Guardian posted the videotaped interview: Laura Poitras and Glenn Greenwald, “NSA Whistleblower Edward Snowden: ‘I Don’t Want to Live in a Society That Does These Sort of Things,’” Guardian, on June
…
, 2016. Advocates for radical transparency: Julian Assange of WikiLeaks and John Young of the leak website Cryptome often criticized me, along with Glenn Greenwald and Laura Poitras, for holding back any documents at all. See, for example, “Snowden Long Drip Pie Charts,” March 14, 2014, at https://perma.cc/FZ9M-ZXPF. trafficking
Snowden's Box: Trust in the Age of Surveillance
by Jessica Bruder and Dale Maharidge · 29 Mar 2020 · 159pp · 42,401 words
is unlikely to be confiscated. Literally bury a backup copy in the woods, that sort of thing. — Edward L. Snowden, in an encrypted email to Laura Poitras, February 4, 2013 I’ve seen the nations rise and fall. I’ve heard their stories, heard them all. But love’s the only engine
…
added. In the years that followed, Snowden’s story would be told and retold, a ballad for our times. The saga unfolded in films, including Laura Poitras’s Oscar-winning documentary Citizenfour and Oliver Stone’s biopic Snowden, and in such books as No Place to Hide by Glenn Greenwald, Luke Harding
…
. Through the haze, I noticed a striking woman with dark hair occasionally glancing my way. “Who’s that?” I asked Julian. He introduced me to Laura Poitras. I was aware of her 2006 documentary, My Country, My Country, about an Iraqi physician running for office in his nation’s first democratic election
…
, without a shred of suspicion of wrongdoing, learn the most private and intimate details about them and their work … The ongoing, and escalating, treatment of Laura Poitras is a testament to how severe that abuse is. At her request, Greenwald didn’t write that Laura had been filming with Julian Assange and
…
had harvested nearly 3 billion pieces of intelligence from US computer networks. And so on. On June 9, the Guardian ran a short film by Laura Poitras. It showed Snowden answering questions posed by Greenwald. One of the most striking aspects of the video was how placid it felt. The opening shot
…
email read: From: anon108@XXXXX To: Micah Lee Date: Fri, 11 Jan 2013 Micah, I’m a friend. I need to get information securely to Laura Poitras and her alone, but I can’t find an email/gpg key for her. Can you help? Micah didn’t know it at the time
…
to try Micah instead. When Micah got the source’s request, he sent Laura an encrypted version of the following message: From: Micah Lee To: Laura Poitras Date: Sat, 12 Jan 2013 Hey Laura, This person just sent me this GPG encrypted email. Do you want to respond? If you want to
…
, and you need any help with using crypto, I’m happy to help. Laura wrote back: From: Laura Poitras To: Micah Lee Date: Sat, 12 Jan 2013 Hey Micah, Thanks for asking. Sure, you can tell this person I can be reached with GPG
…
sent Micah this encrypted email from her new account: From: XXX@riseup.net To: Micah Lee Date: Mon, 28 Jan 2013 Hey Micah, This is Laura Poitras. Someone is trying to verify my fingerprint to this email. The person has proposed you tweet the fingerprint. Would you be able to tweet this
…
demonstration or action by the police, you may end up possessing information that powerful interests would like to suppress. Something similar, after all, happened to Laura Poitras. She began her adult life as a chef. After she started making films with strong political themes, she became a target for government harassment. In
…
single step.” 6. The Tree The odds are against us, but odds never matter when you win. — Edward L. Snowden, in an encrypted email to Laura Poitras, May 23, 2013 Dale For years, Jess and I discussed that brittle summer of 2013. We hoped to someday share this story, plugging a gap
…
. Robot watch party someday. Kirsten Johnson let us see the world through her lens — with warmth, humor, and openness. This book would not exist without Laura Poitras, aka “the Chef,” who got us into this mess and had the forbearance to see us through to the other side. We’re grateful for
…
,” an article we coauthored for the May 2017 Harper’s Magazine. We conducted interviews from 2016 to 2019 with Barton Gellman, Micah Lee, Kirsten Johnson, Laura Poitras, Trevor Timm, Ben Wizner, and confidential sources. Foreword p. 2 The cover of the Guardian bore a giant yellow headline: Julian Borger and Glenn Greenwald
…
eyeglasses: James Bamford, “The Most Wanted Man In The World,” Wired, September 2014. p. 2 an existential threat to democracy: Glenn Greenwald, Ewen MacAskill, and Laura Poitras, “Edward Snowden: The Whistleblower behind the NSA Surveillance Revelations,” Guardian, June 9, 2013. p. 3 General Social Survey: Chris Cillizza, “Watch Americans’ Trust in Each
…
FBI to Listen In,” Seattle Times, December 13, 2006. p. 15 “no credible evidence”: Jamie Williams and Karen Gullo, “Government Documents Show FBI Cleared Filmmaker Laura Poitras after Six-Year Fishing Expedition,” Electronic Frontier Foundation, December 6, 2017, Eff.org. p. 16 she offered to write with crayons: Peter Maass, “How
…
Laura Poitras Helped Snowden Spill His Secrets,” New York Times Magazine, August 18, 2013. Substantiated in interviews with Laura Poitras. p. 17 Salon ran an article: Glenn Greenwald, “US Filmmaker Repeatedly Detained at Border,” Salon, April, 8
…
, 2012. p. 18 Laura was editing The Program: Laura Poitras, “The Program,” New York Times Op-Docs, video, Nytimes.com; Paul Harris, “US Data Whistleblower: ‘It’s a Violation of Everybody’s Constitutional Rights,’” Guardian,
…
. The Brittle Summer p. 31 Your worst enemy: George Orwell, 1984 (London: Secker and Warburg, 1949), 81. p. 31 excerpts from Laura’s Berlin journal: Laura Poitras, Astro Noise: A Survival Guide for Living under Total Surveillance (Whitney Museum of American Art, 2016), 87, 89, 91, 95. p. 33 NSA considered Tails
…
customs for ten days: Greenwald, No Place to Hide, 14. p. 39 My personal desire is that you paint the target directly on my back: Laura Poitras, director, Citizenfour (RADiUS TWC/Participant Media, 2017), 19:30–20:00. p. 40 Approaching the New York Times, however, was out of the question: David
…
‘Really Painful,’” National Public Radio, June 5, 2014, Npr.org. p. 40 New York Times “far too accommodating of power”: Edward Snowden, encrypted email to Laura Poitras in early May 2013. p. 40 the Times spiked a story: Margaret Sullivan, “Lessons in a Surveillance Drama Redux,” New York Times, November 9, 2013
…
: Glenn Greenwald and Ewen MacAskill, “NSA Prism Program Taps in to User Data of Apple, Google and Others,” Guardian, June 7, 2013; Barton Gelman and Laura Poitras, “US, British Intelligence Mining Data from Nine US Internet Companies in Broad Secret Program,” Washington Post, June 7, 2013. p. 48 Snowden answering questions: On
…
June 9, the Guardian ran a short film by Laura Poitras. It showed Snowden answering questions posed by Greenwald. “NSA Whistleblower Edward Snowden: ‘I don’t want to live in a society that does these sort
…
: Ewen MacAskill, “Edward Snowden: How the Spy Story of the Age Leaked Out,” Guardian, June 12, 2013. p. 49 “I will never commit suicide” (Binney): Laura Poitras, Astro Noise: A Survival Guide for Living under Total Surveillance (New York: Whitney Museum of American Art, 2016), 100. pp. 49–50 The Program (Binney
…
with Poitras: Neta Alexander, “Filming Death and Living to Tell the Tale: Interview with Documentarian Kirsten Johnson,” Haaretz, November 19, 2016. p. 64 The Oath. Laura Poitras, director, The Oath (Zeitgeist Films, 2010). p. 65 Micah Lee and his wife in Berkeley: Micah Lee, “Ed Snowden Taught Me to Smuggle Secrets Past
…
: staff directory, https://web.archive.org/eb/20121218123732/ https://pressfreedomfoundation.org/about/staff. p. 69 inscrutable string of nonsense: From an undated encrypted exchange between Laura Poitras and Dale Maharidge, circa summer or fall 2013. p. 70 sequence of events Micah would later recount: Lee, “Ed Snowden Taught Me to Smuggle Secrets
…
: Greenwald, No Place to Hide, 10. p. 72 Snowden had seen The Program and read what Greenwald had written about her in Salon: Maass, “How Laura Poitras Helped Snowden Spill His Secrets.” pp. 72–3 “The surveillance you’ve experienced means you’ve been selected”: Poitras, Citizenfour, 4:22–5:06. p
…
. 73 DARKDIAMOND for Laura and SILVERSHOT for Micah: Poitras, Astro Noise, 101. p. 73 COPPERCOMET for Greenwald: Edward Snowden to Laura Poitras in an encrypted email on April 21, 2013. pp. 73–4 Henk Penning on trust: “On the Apache.org Web of Trust,” WebCite, webcitation.org
…
,” Bloomberg News, November 21, 2018. p. 113 Goal: paralyzing “untrustworthy” people: ibid. 6. The Tree p. 124 Jeremy Scahill told the audience: Emily Buder, “Why Laura Poitras Is the ‘Most Badass Female Filmmaker’ and More from ‘CITIZENFOUR’ NYFF Premiere,” IndieWire, October 11, 2014, indiewire.com. p. 124 Lonnie Snowden: Debbi Wilgoren, “Snowden
…
Michael Bloom’s letter to staff: Maxwell Tani, “The Intercept Shuts Down Access to Snowden Trove, Daily Beast, March 14, 2019, thedailybeast.com. p. 128 Laura Poitras’s letter to the board of directors: Barrett Brown, “Why the Intercept Really Closed the Snowden Archive,” Medium, March 27, 2019, medium.com. p. 128
…
Laura Poitras barred from attending meeting: Maxwell Tani, “The Intercept Bars Co-Founder from Meeting after Snowden Archive Shutdown,” Daily Beast, March 14, 2019, thedailybeast.com. p.
The Hacker and the State: Cyber Attacks and the New Normal of Geopolitics
by Ben Buchanan · 25 Feb 2020 · 443pp · 116,832 words
which GCHQ has access, see “Cables: Where We Are,” UK Government Communications Headquarters, ca. 2012. This document was shared publicly in Frederick Obermaier, Henrik Moltke, Laura Poitras, and Jan Strozyk, “Snowden-Leaks: How Vodafone-Subsidiary Cable & Wireless Aided GCHQ’s Spying Efforts,” Süddeutsche Zeitung International, November 25, 2014. 16. Julia Angwin, Jeff
…
Larson, Charlie Savage, James Risen, Henrik Moltke, and Laura Poitras, “NSA Spying Relies on AT&T’s ‘Extreme Willingness to Help,’ ” ProPublica, August 15, 2015. 17. Michelle Nichols, “United Nations Says It Will Contact United
…
PRISM Program.” Among the reported stories making the deck public, see Greenwald and MacAskill, “NSA Prism Program Taps in to User Data”; Barton Gellman and Laura Poitras, “U.S., British Intelligence Mining Data from Nine U.S. Internet Companies in Broad Secret Program,” Washington Post, June 7, 2013; Jacques Follorou and Glenn
…
Source Access: Foreign Partner Access: Project Description,” National Security Agency, February 2012. The document is available online via Anton Geist, Sebastian Gjerding, Henrik Moltke, and Laura Poitras, “NSA ‘Third Party’ Partners Tap the Internet Backbone in Global Surveillance Program,” Dagbladet Information, June 19, 2014. 40. “DIR Opening Remarks Guidance for DP1,” National
…
; Gallagher, “How Secret Partners Expand NSA’s Surveillance Dragnet.” 47. “Special Source Access: Foreign Partner Access: Project Description,” 1. 48. Ryan Devereaux, Glenn Greenwald, and Laura Poitras, “Data Pirates of the Caribbean: The NSA Is Recording Every Cell Phone Call in the Bahamas,” The Intercept, May 19, 2014. 49. Devereaux et al
…
activity occurred, though the claim of embassy-based espionage is not confirmed beyond this article. Jacob Appelbaum, Nikolaus Blome, Hubert Gude, Ralf Neukirch, Rene Pfister, Laura Poitras, and Marcel Rosenbach, “The NSA’s Secret Spy Hub in Berlin,” Der Spiegel, October 27, 2013. 54. For one example of an early station, see
…
with Glenn Greenwald and Murtaza Hussain, “The NSA’s New Partner in Spying: Saudi Arabia’s Brutal State Police,” The Intercept, July 25, 2014. 56. Laura Poitras, Marcel Rosenbach, Fidelius Schmid, Holger Stark, and Johnathan Stock, “How the NSA Targets Germany and Europe,” Der Spiegel, July 1, 2013; Matthew M. Aid, “The
…
Davies, and James Ball, “Mastering the Internet: How GCHQ Set Out to Spy on the World Wide Web,” Guardian, June 21, 2013. 57. Jacob Appelbaum, Laura Poitras, Marcel Rosenbach, Christian Stöcker, Jörg Schindler, and Holger Stark, “Inside TAO: Documents Reveal Top NSA Hacking Unit,” Der Spiegel, December 20, 2013; “New Nuclear Sub
…
Apps Doubleheader: BADASS Angry Birds,” Government Communications Headquarters internal presentation deck, n.d., published online alongside Jacob Appelbaum, Aaron Gibson, Claudio Guarnieri, Andy Müller-Maguhn, Laura Poitras, Marcel Rosenbach, Leif Ryge, Hilmar Schmundt, and Michael Sontheimer, “The Digital Arms Race: NSA Preps America for Future Battle,” Der Spiegel, January 17, 2015. 64
…
alongside Marquis-Boire et al., “XKEYSCORE.” 70. “Contact Mapping: Tip-Off to Diplomatic Travel Plans,” Government Communications Headquarters internal presentation, January 2010, published online alongside Laura Poitras, Marcel Rosenbach, and Holger Stark, “ ‘Royal Concierge’: GCHQ Monitors Diplomats’ Hotel Bookings,” Der Spiegel, November 17, 2013. 71. Spiegel Staff, “Quantum Spying: GCHQ Used Fake
…
alongside Marquis-Boire et al., “XKEYSCORE”; “What Is HACIENDA?” Government Communications Headquarters internal presentation, published online alongside Jacob Appelbaum, Monika Ermert, Julian Kirsch, Henrik Moltke, Laura Poitras, and Christian Grothoff, “The HACIENDA Program for Internet Colonization,” Heise / c’t Magazin, August 15, 2014; “Pull-Through Steering Group Meeting #16,” 2. 73. Marquis
…
, and Scott Shane, “N.S.A. Able to Foil Basic Safeguards of Privacy on Web,” New York Times, September 5, 2013. 14. James Risen and Laura Poitras, “N.S.A. Report Outlined Goals for More Power,” New York Times, November 22, 2013. Within this article can be found National Security Agency, “SIGINT
…
underlying public key cryptography,” presumably including Diffie-Hellman. “Exceptionally Controlled Information (ECI) as of 12 September 2003,” National Security Agency, published alongside Peter Maass and Laura Poitras, “Core Secrets: NSA Saboteurs in China and Germany,” The Intercept, October 10, 2014, 5. 25. Andrea Peterson, “Why Everyone Is Left Less Secure When the
…
16, 2010, published alongside Ball, Borger, and Greenwald, “Revealed”; “National Initiative Protection Program—Sentry Eagle,” National Security Agency internal document, published alongside Peter Maass and Laura Poitras, “Core Secrets: NSA Saboteurs in China and Germany,” The Intercept, October 10, 2014, 9; Nicole Perlroth, Jeff Larson, and Scott Shane, “N.S.A. Able
…
for use in future operations. “What Is HACIENDA?” UK Government Communications Headquarters internal presentation, published online alongside Jacob Appelbaum, Monika Ermert, Julian Kirsch, Henrik Moltke, Laura Poitras, and Christian Grothoff, “The HACIENDA Program for Internet Colonization,” Heise / c’t Magazin, August 15, 2014. 9. Passive collection can be useful for this task
…
’,” Newsweek, November 5, 2008. 5. Mark Halperin and John Heilemann, “The Hunt for Pufferfish: A Double Down Excerpt,” Time, November 2, 2013. 6. Jens Gluesing, Laura Poitras, Marcel Rosenbach, and Holger Stark, “Fresh Leak on US Spying: NSA Accessed Mexican President’s Email,” Der Spiegel, October 20, 2013. For a broader look
…
and Anne Gearan, “Obama Didn’t Know about Surveillance of U.S.-Allied World Leaders until Summer, Officials Say,” Washington Post, October 28, 2013. 7. Laura Poitras, Marcel Rosenbach, and Holger Stark, “ ‘A’ for Angela: GCHQ and NSA Targeted Private German Companies and Merkel,” Der Spiegel, March 29, 2014. 8. FireEye Threat
Surveillance Valley: The Rise of the Military-Digital Complex
by Yasha Levine · 6 Feb 2018 · 474pp · 130,575 words
several thousand packs a massive auditorium to watch Tor developers and celebrity supporters talk about their fights against Internet surveillance. Last year, the stage featured Laura Poitras, the Academy Award–winning director of the Edward Snowden documentary, Citizen Four. In her speech, she held up Tor as a powerful antidote to America
…
as Tor’s pitchman more effective. In Berlin, Appelbaum caught another lucky break for the Tor Project. In 2013, his good friend and sometimes-lover Laura Poitras, an American documentary filmmaker who also lived in the German capital in self-imposed exile, was contacted by a mysterious source who told her he
…
. So was Cory Doctorow, a best-selling young adult science fiction author whose books about a totalitarian government’s surveillance were read and admired by Laura Poitras, Jacob Appelbaum, Roger Dingledine, and Edward Snowden.122 Doctorow was a huge personality in the crypto movement who could fill giant conference halls at privacy
…
Tor in the age of mobile phones. While Tor anonymized browsing, Signal encrypted voice calls and text, making it impossible for governments to monitor communication. Laura Poitras gave it two secure thumbs up as a powerful people’s encryption tool and told everyone to use it every day. People at the ACLU
…
Fadell, “Nest CEO Tony Fadell on the Future of the Internet,” Wall Street Journal, April 26, 2015. Chapter 6 1. Glenn Greenwald, Ewen MacAskill, and Laura Poitras, “Edward Snowden: The Whistleblower behind the NSA Surveillance Revelations,” Guardian, June 11, 2013. 2. Ewen MacAskill, “Edward Snowden, NSA Files Source: ‘If They Want to
…
. Sandra Jontz, “Data Analytics Programs Help Predict Global Unrest,” Signal, December 1, 2015, https://www.afcea.org/content/?q=node/15501/. 20. James Risen and Laura Poitras, “N.S.A. Gathers Data on Social Connections of U.S. Citizens,” New York Times, September 28, 2013. Actually, the NSA mostly sticks to planning
…
attachments—from one data center to another.” 27. “NSA Slides Explain the PRISM Data-Collection Program,” Washington Post, June 6, 2013. 28. Barton Gellman and Laura Poitras, “U.S., British Intelligence Mining Data from Nine U.S. Internet Companies in Broad Secret Program,” Washington Post, June 7, 2013. 29. Barton Gellman and
…
Dispatch, May 13, 2014, http://www.tomdispatch.com/post/175843/tomgram %3A_glenn_greenwald,_how_i_met_edward_snowden/. 44. Glenn Greenwald, Ewen MacAskill, and Laura Poitras, “Edward Snowden: The Whistleblower behind the NSA Surveillance Revelations,” Guardian, June 11, 2013. 45. Luke Harding, “How Edward Snowden Went from Loyal NSA Contractor to
…
. Fight for the Future, the hip, young Silicon Valley activist group, declared Tor to be “NSA-proof” and recommended that people use it every day. Laura Poitras, director of Citizen Four, the Academy Award–winning documentary on Edward Snowden, endorsed Tor as well. “When I was communicating with Snowden for several months
…
of Edward Snowden projected behind her on stage (Katina, “This Is What a Tor Supporter Looks Like: Laura Poitras,” Tor Project [blog], November 23, 2015, https://blog.torproject.org/blog/what-tor-supporter-looks-laura-poitras). 68. Every year Google funds university students to work at Tor during the summer with a stipend of
…
, December 19, 2015, 1:03 p.m., https://web.archive.org/web/20170808234142/https://twitter.com/puellavulnerata/status/678168846897934340. 3. Roger Dingledine, Jacob Appelbaum, and Laura Poitras, “State of the Onion,” 31c3, December 30, 2014, https://media.ccc.de/v/31c3_-_6251_-_en_-_saal_1_-_201412301400_-_state_of_the_onion_-_jacob_-_arma
…
/privacy-groups-announce-developer-challenge-mobile-apps). Teach-in at Whitney Museum featuring “Jacob Appelbaum, computer security researcher, privacy advocate, hacker, and human rights activist” (“Laura Poitras: Surveillance Teach-In,” Whitney Museum, April 20, 2012, http://web.archive.org/web/20170521210801/http://whitney.org/Events/LauraPoitrasObservationAndTrust). 87. “The FP Top 100 Global
…
2012 (Washington, DC: Open Technology Fund and Radio Free Asia, February 2013), https://www.opentech.fund /files/reports/otf_myanmar_access_openness_public.pdf. 107. Laura Poitras, Risk, documentary film, May 2016. 108. “The NSA and Its Willing Helpers,” Spiegel Online, July 8, 2013, http://www.spiegel.de/international/world/interview-with
The People's Platform: Taking Back Power and Culture in the Digital Age
by Astra Taylor · 4 Mar 2014 · 283pp · 85,824 words
cannot protect us from, and can even perpetuate, the perils of a peasant’s kingdom. 2 FOR LOVE OR MONEY Not that many years ago, Laura Poitras was living in Yemen, alone, waiting. She had rented a house close to the home of Abu Jandal, Osama bin Laden’s former bodyguard and
…
creative acts that require leaving one’s computer have hardly collapsed. Where will this new paradigm leave projects like The Oath? Following Shirky’s logic, Laura Poitras is one of those professionals who should be overthrown by noble amateurs, her labor-intensive filmmaking process a throwback to another era, before creativity was
…
from an interview with the author except for this one, which is from Justin Cox, “Documenting a Bin Laden Ex-Confidante: Q&A with Filmmaker Laura Poitras,” TheHill.com, July 13, 2010, http://thehill.com/capital-living/cover-stories/108553-documenting-a-bin-laden-ex-confidante-qaa-with-filmmaker
…
-laura-poitras#ixzz2YfhpMdXu. 2. The other person Snowden contacted was the journalist Glenn Greenwald of the Guardian, with whom Poitras collaborated. 3. That start-up is Narrative
Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World
by Bruce Schneier · 2 Mar 2015 · 598pp · 134,339 words
files show,” Guardian, http://www.theguardian.com/world/2013/sep/30/nsa-americans-metadata-year-documents. Another NSA database, MYSTIC: Ryan Devereaux, Glenn Greenwald, and Laura Poitras (19 May 2014), “Data pirates of the Caribbean: The NSA is recording every cell phone call in the Bahamas,” Intercept, https://firstlook.org/theintercept/article
…
.,” New Yorker, http://www.newyorker.com/news/amy-davidson/the-dominos-hypothetical-judge-leon-vs-the-n-s-a. NSA documents note: Barton Gellman and Laura Poitras (10 Jul 2013), “NSA slides explain the PRISM data-collection program,” Washington Post, http://www.washingtonpost.com/wp-srv/special/politics/prism-collection-documents. total
…
.com/sites/tonybradley/2014/01/17/nsa-reform-what-president-obama-said-and-what-he-didnt. This is what both the NSA: James Risen and Laura Poitras (20 Sep 2013), “NSA gathers data on social connections of U.S. citizens,” New York Times, http://www.nytimes.com/2013/09/29/us/nsa
…
/nsa-infiltrates-links-to-yahoo-google-data-centers-worldwide-snowden-documents-say/2013/10/30/e51d661e-4166-11e3-8b74-d89d714ca4dd_story.html. Barton Gellman and Laura Poitras (7 Jun 2013), “U.S., British intelligence mining data from nine U.S. Internet companies in broad secret program,” Washington Post, http://www.washingtonpost.com
…
.com/commentisfree/2014/jul/11/the-ultimate-goal-ofthe-nsa-is-total-population-control. we know it is doing so: Ryan Devereaux, Glenn Greenwald, and Laura Poitras (19 May 2014), “Data pirates of the Caribbean: The NSA is recording every cell phone call in the Bahamas,” Intercept, https://firstlook.org/theintercept/article
…
‘partner and target’ for the NSA,” Der Spiegel, http://www.spiegel.de/international/documents-show-nsa-and-gchq-spied-on-partner-turkey-a-989011.html. Laura Poitras et al. (31 Aug 2014), “How the NSA helped Turkey kill Kurdish rebels,” Intercept, https://firstlook.org/theintercept/2014/08/31/nsaturkeyspiegel. NSA spies on
…
,” Pro Publica, http://www.propublica.org/article/claim-on-attacks-thwarted-by-nsa-spreads-despite-lack-of-evidence. The NSA gives Israel’s: Glenn Greenwald, Laura Poitras, and Ewen MacAskill (11 Sep 2013), “NSA shares raw intelligence including Americans’ data with Israel,” Guardian, http://www.theguardian.com/world/2013/sep/11/nsa
…
call monitoring, surveillance gear,” Krebs on Security, http://krebsonsecurity.com/2014/05/backdoor-in-call-monitoring-surveillance-gear. they have employees secretly: Peter Maass and Laura Poitras (10 Oct 2014), “Core secrets: NSA saboteurs in China and Germany,” Intercept, https://firstlook.org/theintercept/2014/10/10/core-secrets. Eric Schmidt tried to
…
between the US law firm Mayer Brown and its client the government of Indonesia. The ASD passed those communications to the NSA. James Risen and Laura Poitras (15 Feb 2014), “Spying by NSA ally entangled US law firm,” New York Times, http://www.nytimes.com/2014/02/16/us/eavesdropping-ensnared-american
…
document,” Guardian, http://www.theguardian.com/world/2013/aug/14/nsa-intelligence-committee-under-pressure-document. Secret courts keep their own secrets: Charlie Savage and Laura Poitras (11 Mar 2014), “How a court secretly evolved, extending U.S. spies’ reach,” New York Times, http://www.nytimes.com/2014/03/12/us/how
…
Senate panel,” New York Times, http://www.nytimes.com/2014/08/01/world/senate-intelligence-commitee-cia-interrogation-report.html. the NSA had been spying: Laura Poitras, Marcel Rosenbach, and Holger Stark (26 Aug 2013), “Codename ‘Apalachee’: How America spies on Europe and the UN,” Der Spiegel, http://www.spiegel.de/international
…
America Foundation, http://www.newamerica.net/publications/policy/surveillance_costs_the_nsas_impact_on_the_economy_internet_freedom_cybersecurity. the PRISM program: Barton Gellman and Laura Poitras (7 Jun 2013), “U.S., British intelligence mining data from nine U.S. Internet companies in broad secret program,” Washington Post, http://www.washingtonpost.com
…
: Lawrence Lessig interviews Edward Snowden at Harvard Law,” LeakSourceInfo/YouTube, http://www.youtube.com/watch? v=DksIFG3Skb4. Bermuda phone system: Ryan Devereaux, Glenn Greenwald, and Laura Poitras (19 May 2014), “Data pirates of the Caribbean: The NSA is recording every cell phone call in the Bahamas,” Intercept, https://firstlook.org/theintercept/article
…
Greenwald (2014), No Place to Hide: Edward Snowden, the NSA and the US Surveillance State, Macmillan, http://glenngreenwald.net. the NSA spied on the UN: Laura Poitras, Marcel Rosenbach, and Holger Stark (26 Aug 2013), “Codename ‘Apalachee’: How America spies on Europe and the UN,” Der Spiegel, http://www.spiegel.de/international
No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State
by Glenn Greenwald · 12 May 2014 · 253pp · 75,772 words
liberties abuses done in the name of the War on Terror. On landing at JFK Airport, I saw that I had an email message from Laura Poitras, the documentary filmmaker, which read: “Any chance you’ll be in the US this coming week? I’d love to touch base about something, though
…
best to do in person.” I take seriously any message from Laura Poitras. One of the most focused, fearless, and independent individuals I’ve ever known, she has made film after film in the riskiest of circumstances, with
…
for the rest of my life. The impact this story had would have been impossible without my incomparably brave and brilliant journalistic partner and friend, Laura Poitras. Despite years of harassment at the hands of the US government for the films she made, she never once hesitated in pursuing this story aggressively
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
by Kevin Mitnick, Mikko Hypponen and Robert Vamosi · 14 Feb 2017 · 305pp · 93,091 words
. So he had to perform a complicated maneuver to establish a truly secure, anonymous, and fully encrypted means of communication with privacy advocate and filmmaker Laura Poitras, who had recently finished a documentary about the lives of whistle-blowers. Snowden wanted to establish an encrypted exchange with Poitras, except only a few
…
a purchase online. According to Micah Lee of the EFF, at one point Snowden was in his Hong Kong hotel room discussing government secrets with Laura Poitras and Glenn Greenwald, a reporter from the Guardian, and at the same time he was on hold with the customer support department at DreamHost, an
…
all the way off. At the beginning of the book I talked about the many precautions that Edward Snowden took to keep his communication with Laura Poitras private. Once Snowden’s secret cache of data was ready to be released to the public, however, he and Poitras needed a place to store
…
two anonymously created e-mail addresses and Bitcoin wallets. So how do you create anonymous e-mail addresses like those created by Edward Snowden and Laura Poitras? In my research, I found I was able to create an e-mail account on protonmail.com and one on tutanota.com using Tor, both
…
your anonymous laptop and creating another set of anonymous e-mail accounts with Bitcoin wallets and purchasing another anonymous hotspot. Remember that Edward Snowden and Laura Poitras, both of whom already had anonymous e-mail accounts, set up additional anonymous e-mail accounts so they could communicate specifically with each other. This
Bottoms Up and the Devil Laughs
by Kerry Howley · 21 Mar 2023

Fancy Bear Goes Phishing: The Dark History of the Information Age, in Five Extraordinary Hacks
by Scott J. Shapiro · 523pp · 154,042 words
Dark Territory: The Secret History of Cyber War
by Fred Kaplan · 1 Mar 2016 · 383pp · 105,021 words
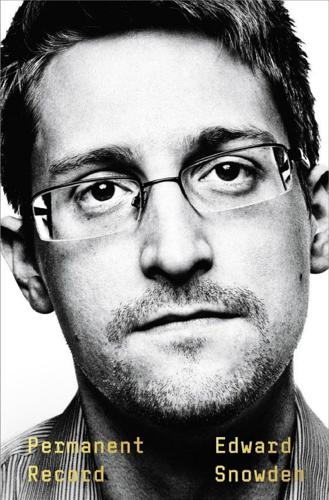
Permanent Record
by Edward Snowden · 16 Sep 2019 · 324pp · 106,699 words
Cult of the Dead Cow: How the Original Hacking Supergroup Might Just Save the World
by Joseph Menn · 3 Jun 2019 · 302pp · 85,877 words
Hacker, Hoaxer, Whistleblower, Spy: The Story of Anonymous
by Gabriella Coleman · 4 Nov 2014 · 457pp · 126,996 words
This Is How They Tell Me the World Ends: The Cyberweapons Arms Race
by Nicole Perlroth · 9 Feb 2021 · 651pp · 186,130 words
Free Speech: Ten Principles for a Connected World
by Timothy Garton Ash · 23 May 2016 · 743pp · 201,651 words
We Are Data: Algorithms and the Making of Our Digital Selves
by John Cheney-Lippold · 1 May 2017 · 420pp · 100,811 words
Future Crimes: Everything Is Connected, Everyone Is Vulnerable and What We Can Do About It
by Marc Goodman · 24 Feb 2015 · 677pp · 206,548 words
There's a War Going on but No One Can See It
by Huib Modderkolk · 1 Sep 2021 · 295pp · 84,843 words
My Glorious Defeats: Hacktivist, Narcissist, Anonymous: A Memoir
by Barrett Brown · 8 Jul 2024 · 332pp · 110,397 words
Raising Lazarus: Hope, Justice, and the Future of America’s Overdose Crisis
by Beth Macy · 15 Aug 2022 · 389pp · 111,372 words
The End of Policing
by Alex S. Vitale · 9 Oct 2017 · 318pp · 82,452 words
New Dark Age: Technology and the End of the Future
by James Bridle · 18 Jun 2018 · 301pp · 85,263 words
Dawn of the Code War: America's Battle Against Russia, China, and the Rising Global Cyber Threat
by John P. Carlin and Garrett M. Graff · 15 Oct 2018 · 568pp · 164,014 words
The System: Who Owns the Internet, and How It Owns Us
by James Ball · 19 Aug 2020 · 268pp · 76,702 words
The Perfect Weapon: War, Sabotage, and Fear in the Cyber Age
by David E. Sanger · 18 Jun 2018 · 394pp · 117,982 words
Merchants of Truth: The Business of News and the Fight for Facts
by Jill Abramson · 5 Feb 2019 · 788pp · 223,004 words
Pandora's Box: How Guts, Guile, and Greed Upended TV
by Peter Biskind · 6 Nov 2023 · 543pp · 143,084 words
The Stack: On Software and Sovereignty
by Benjamin H. Bratton · 19 Feb 2016 · 903pp · 235,753 words
The Code: Silicon Valley and the Remaking of America
by Margaret O'Mara · 8 Jul 2019
Accessory to War: The Unspoken Alliance Between Astrophysics and the Military
by Neil Degrasse Tyson and Avis Lang · 10 Sep 2018 · 745pp · 207,187 words
The Laundromat : Inside the Panama Papers, Illicit Money Networks, and the Global Elite
by Jake Bernstein · 14 Oct 2019 · 470pp · 125,992 words
Habeas Data: Privacy vs. The Rise of Surveillance Tech
by Cyrus Farivar · 7 May 2018 · 397pp · 110,222 words
Tools and Weapons: The Promise and the Peril of the Digital Age
by Brad Smith and Carol Ann Browne · 9 Sep 2019 · 482pp · 121,173 words
The Seventh Sense: Power, Fortune, and Survival in the Age of Networks
by Joshua Cooper Ramo · 16 May 2016 · 326pp · 103,170 words
Terms of Service: Social Media and the Price of Constant Connection
by Jacob Silverman · 17 Mar 2015 · 527pp · 147,690 words
Dragnet Nation: A Quest for Privacy, Security, and Freedom in a World of Relentless Surveillance
by Julia Angwin · 25 Feb 2014 · 422pp · 104,457 words
The Panama Papers: Breaking the Story of How the Rich and Powerful Hide Their Money
by Frederik Obermaier · 17 Jun 2016 · 372pp · 109,536 words
Orwell Versus the Terrorists: A Digital Short
by Jamie Bartlett · 12 Feb 2015 · 50pp · 15,603 words
Empire of Pain: The Secret History of the Sackler Dynasty
by Patrick Radden Keefe · 12 Apr 2021 · 712pp · 212,334 words
Culture & Empire: Digital Revolution
by Pieter Hintjens · 11 Mar 2013 · 349pp · 114,038 words