
Fancy Bear Goes Phishing: The Dark History of the Information Age, in Five Extraordinary Hacks
by Scott J. Shapiro · 523pp · 154,042 words
, a software glitch displayed every user’s password, instead of the log-in “Message of the Day.” Users were forced to change their passwords. From Multics to UNIX Though limited in functionality, CTSS demonstrated that time-sharing was not only technologically possible, but also wildly popular. Programmers liked the immediate feedback
…
, decided to develop a complete multiuser operating system as a replacement for batch processing. They called it Multics, for Multiplexed Information and Computing Service. The Multics team designed its time-sharing with security in mind. Multics pioneered many security controls still in use today—one of which was storing passwords in garbled form
…
so that users couldn’t repeat Allan Scherr’s simple trick. After six years of development, Multics was released in 1969. The military saw potential in
…
Multics. Instead of buying separate computers to handle unclassified, classified, secret, and top-secret information, the Pentagon could buy one and
…
information for which they had clearance. The military estimated that it would save $100 million by switching to time-sharing. Before the air force purchased Multics, they tested it. The test was a disaster. It took thirty minutes to figure out how to hack into
…
Multics, and another two hours to write a program to do it. “A malicious user can penetrate the system at will with relatively minimal effort,” the
…
evaluation concluded. The research community did not love Multics either. Less concerned with its bad security, computer scientists were unhappy with its design. Multics was complicated and bloated—a typical result of decision by committee. In 1969, part of the
…
Multics group broke away and started over. This new team, led by Dennis Ritchie and Ken Thompson, operated out of an attic
…
” built by the Digital Equipment Corporation (DEC) that cost ten times less than an IBM mainframe. The Bell Labs team had learned the lesson of Multics’ failure: Keep it simple, stupid. Their philosophy was to build a new multiuser system based on the concept of modularity: every program should do one
…
of the operating system supported only one user—Ken Thompson—Peter Neumann, a security researcher at Stanford Research International, joked that it was an “emasculated Multics,” or “UNICS.” The spelling was eventually changed to UNIX. UNIX was a massive success when the first version was completed in 1971. The versatile operating
…
half of his lecture, Thompson described a devious hack first used by air force testers when they penetrated the Multics system in 1974. They showed how to insert an undetectable “backdoor” in Multics. A backdoor is a hidden entrance into a computer system that bypasses security, the digital equivalent of a bookcase
…
by the worm. Military computers were protected from infection because the military had its own internet, known as Milnet. As it had learned in the Multics fiasco, its security needs were too high to integrate with the public internet. It could not secure its end points well enough. As an organization
…
. A. Karger and R. R. Schell, “Thirty Years Late: Lessons from the Multics Security Evaluation,” Eighteenth Annual Computer Security Applications Conference, 2002, https://www.acsac.org/2002/papers/classic-multics.pdf. the evaluation concluded: Paul Karger and Roger Schell, “Multics Security Evaluation: Vulnerability Analysis,” June 1974, https://www.acsac.org/2002/papers/classic
…
-multics-orig.pdf. IBM mainframe: See, e.g., Digital Equipment Corporation, Ninteen Fifty-Seven to
…
Schell provided the first public description of the problem that compilers can insert malicious code into themselves. Karger and Schell noted in their examination of Multics vulnerabilities that a “penetrator could insert a trap door into the … compiler … [and] since the PL/I compiler is itself written in PL/I, the
…
trap door can maintain itself, even when the compiler is recompiled.” Karger, “Multics Security Evaluation,” 52. do the same to UNIX: David Wheeler proposed a countermeasure against the Thompson attack using two different compilers, in David Wheeler, Fully
…
legislation on; Kill Chain model and; in late 1980s; limits of; metacode limits and; Microsoft efforts in; military; moral duality and; Morris Worm lessons of; Multics and; NSA history and approach to; pre-internet; professionals and job market; Reagan executive order on; scientific internet beginnings and; SEC regulation on; social inequality
…
at; legal action against; Minecraft success for; Sinofsky work for; Slivka role at; Winner Take All market and Microsoft Windows Microsoft Word military: cybersecurity; internet; Multics application for; WarGames movie and; see also GRU Milnet Minecraft: about; DDoS attacks and; Jha obsession with Mirai botnet and gang; code dump; DDoS attacks
…
Odyssey; WarGames impact and Mr. Robot (television show) MtE, see Mutation Engine Mudge (hacker) mudges Mueller, Robert Mulaney, John Multiplexed Information and Computing Service (Multics) multiuser systems: CTSS; Multics Munson (judge) Murphy viruses Mutation Engine (MtE) Nakashima, Ellen NASA National Security Agency (NSA): cyberespionage tactics of; cybersecurity history; cybersecurity testing by; Five
…
All market for OVH (French cloud provider) Page, Carter passwords; Clinton 2016 campaign warnings about; CTSS vulnerability with; IoT security and; Morris Worm uncovering of; Multics approach to; phishing on resetting; side-channel attacks and; UNIX approach to; weak Patrick, Neal Patriot Act payment systems personal computer evolution Peterson, Elliott phishing
The Dream Machine: J.C.R. Licklider and the Revolution That Made Computing Personal
by M. Mitchell Waldrop · 14 Apr 2001
follow it up with a system that would be done right, that would be built around the notion of time-sharing from the ground up. Multics, as this hypothetical system came to be known-short for MULTiplexed Information 244 THE DREAM MACHINE and Computing Service-would have the ability to run
…
always be ready to take charge if another went down. Like a power utility, the information utility would be available to users day and night. Multics would also have a bulletproo£ hierarchical file system so that nothing would ever inadvertently disappear. And it would have built-in security: firewalls, passwords, private
…
directories-the works. Planning for Multics had begun right after the 1963 summer study, with a for- mer Burroughs engineer named Ted Glaser as chief designer. "He was blind, but an
…
amazing systems architect," says Corbato. "We worked together hand and glove." However, the actual programming of Multics wouldn't get under way until 1965. In the interim, the group was absorbed by a much more urgent task: finding a computer for
…
Multics to run on. The 7094 was out of the question; it had never been anything more than a stopgap machine to begin with. As Corbato
…
, the design is an extremely difficult one to learn because of the Byzantine-like detail, exceptions, and ad hoc solutions that exist throughout."34 Building Multics was going to be hard enough in any case; building it for System/360 would be a nightmare. That wasn't the worst of it
…
no way to upgrade without replacing the whole computer. Second, because the job of coordinat- ing all those processors would have to be handled by Multics itself, which would reside in the computer's memory banks, Corbato and his colleagues were looking for a "memory-centered" architecture. Trying to make the
…
, at least from IBM's standpoint. "QIickly after our decision to go with GE," says Fano, "Bell Labs decided to join us [in devel- oping Multics]. So it became a three-way partnership. And when that happened, IBM hit the ceiling. Then the next thing that happened was that Lincoln Lab
…
out a request for proposals on a new computing system with the spec that it had to be time-shared-in exactly the same way Multics was. So IBM decided they had to have that contract. They couldn't afford to lose again." Orders came down from the top: create a
…
. Downstairs in the AI Lab, for example, Marvin Minsky and his crew were as sus- picious and as xenophobic as ever. And Fernando Corbato's Multics crowd, who hadn't gotten their ambitious new operating system up and running until the previous fall-more than three years late-were still preoccupied
…
University's Terry Winograd, who was an AI student during this period. In the ninth-floor machine room of 545 Technology Square, he recalls, the Multics computers were on one side and the AI computers on the other, with a door in the middle-"and you were either a winner or
…
began to add up into bigger things, such as the AI Lab's conviction that Lick was cutting back on their funding in favor of Multics. And relations steadily went from bad to worse, until a final blowup came later in 1970. The last straw was so utterly triv- ial that
…
to Minsky, but it was deeply embarrassing nonetheless. And in the meantime, iron- ically, Lick hadn't been doing any better with the Multics crowd. In truth, Multics had been Lick's chief concern from the day he became di- rector. Originally planned for completion in 1966, the second-generation time- sharing
…
to the Vietnam involvement. There always seemed to be light at the end of the tunnel, yet somehow the end never came. Fundamentally, says Corbato, Multics was just too complicated. In their na.ivete, he says, he and his colleagues had drawn up specifications that called for everything an information utility
…
had to go on was IBM's written definition of the language, it seemed like the state of the art in power and flexibility. The Multics team accordingly made plans to buy a PL/1 com- piler being written by a commercial software company that had had some previ- ous success
…
360/67 for Carnegie Tech, swore he'd never use an IBM product agaIn. Shared na.ivete or no, however, Lick had begun to see Multics as a horren- dous opportunity cost for Project MAC, a diversion of talent and effort that had left the actual users in limbo. He also
…
knew that ARPA's patience wasn't going to last forever, given the new emphasis on "relevance." Indeed, he could foresee Multics' dragging down the whole ARPA dream with it. "The present time is . . . a critical one in the history of digital computing," he had declared in
…
few weeks before he took over at MAC. "Many are waiting to see how the sec- ond generation of general-purpose multiaccess systems [that is, Multics and TSS] turns out. [If they] turn out to be too complex to implement, or to operate efficiently, there may be a general retrenchment to
…
learning, experimenting, modeling, solving problems, making decisions, and other intellectual activities." Given that latter scenario, the new director of Project MAC had to wonder if Multics was still worth it. After all, it wasn't the only game in town anymore. The time-sharing system developed at Project Genie might have
…
was likewise workable, if not great. And if those systems were available now, one had to wonder, was there any real point in waiting for Multics? Was this just another case of "perfect" being the f " d ""\ enemy 0 goo !' Lick thought it was high time for Project MAC to get
…
where his maladroitness came into play. His way of dealing with the problem was to have ARPA call for a full-scale, outside review of Multics to de- termine if the time had come to terminate it. Opinions differ as to whether Lick was genuinely trying to kill
…
Multics or just attempting to save it with a swift kick in the backside to focus people's minds. But either way, he definitely got their
…
attention. The committee gathered at Tech Square starting December 18 and ultimately ended up granting Multics a stay of execution. "I felt that there were some excellent ideas in Multics, trapped in this overgrown, baroque monster," says committee member Ed Fredkin, who had 314 THE DREAM MACHINE joined
…
the AI Lab the summer before. "I thought that those ideas would be dis- credited if Multics was killed, and that would cause general harm to the progress of computer science." Even that favorable decision, however, came at a tremen- dous cost
…
for him as a person. But nonethe- less, a coolness had set in, an estrangement that would last for years. It didn't help that Multics itself in the end proved to be something of a disap- pointment. Although Corbato and his team did get a usable version up and run
…
owned marketing rights to a product they'd barely even heard of Only after considerable prodding from Larry Roberts at ARPA did Honeywell finally offer Multics for sale. And while some customers did indeed buy it-an eventual total of seventy-seven copies were sold worldwide, which was fairly respectable for
…
time-sharing system created for that machine by BBN. And then, of course, came the microcomputer revolution of the 1980s, which made Multics look like a complete dinosaur. If Multics became a dinosaur, however, it was a remarkably influential one. Witness the fact that the Association for Computing Machinery would award Corbato
…
its 1991 Turing Award, computerdom's most prestigious honor. For all its complexity and delay, Multics gave living proof that a grown-up operating system was possible-that sophisticated memory management, a hierarchical file system, careful attention to security, and all
…
the rest could be integrated into a single, coherent whole. In that sense, Multics was a prototype for virtually all the operating systems to follow. And along the way, not incidentally, the project became a model of planning and
…
documentation. At the 1965 Fall Joint Com- puter Conference in Las Vegas, Corbato and his team spelled out their prelimi- nary designs for Multics in unprecedented detail, giving six separate papers that would occupy some sixty pages of the proceedings volume. Once the project was history, moreover, they would
…
be equally open about the painful lessons they'd learned. In that sense, Multics was a significant contribution to the emerging discipline of software engineering. "I think we probably got people to think at a more sophisticated level about
…
Bricklin and Bob Frankston, who would go on to galvanize the emerging microcomputer industry with a little program called VisiCalc, the first electronic spreadsheet. So Multics definitely had an impact. And that's not even counting its biggest, if least direct, legacy, which came in the form of a backhanded compliment
…
. In January 1969, just a few weeks after the harrowing ARPA review at Tech Square, Bell Labs announced that it was dropping out of the Multics partner- ship, effective immediately. The timing mayor may not have been coincidental, but no one was surprised. Bell Labs' managers had grown increasingly impatient with
…
Multics-they needed a computer system now, not in some far-distant fu- ture-and work on it there was already close to a standstill. The
…
. But then a funny thing happened: two of Bell's former Multicians, Ken Thompson and Dennis Ritchie, began suffering from withdrawal pangs. As baroque as Multics was, it was responsive, interactive, alive. And once they no longer had it, Thompson and Ritchie found themselves craving that interactiv- ity. So, good hackers
…
they had to make do with a discarded, obsolete PDP-7 computer that Thompson had scrounged from somewhere. But they persevered, taking some ideas from Multics, others from Project Genie-Thompson had graduated from Berkeley in 1965-and adding a good many of their own. Their prime criterion was that the
…
result had to be lean, clean, and simple, with none of Multics's gargoyles and gingerbread. By mid- 1970, they had a preliminary version up and running. Somewhere along the way, moreover, their homebrew operating system had
…
acquired a name. According to one version of the story, the name signified "one of whatever Multics was many 0(" According to another, it stood for "Multics without balls." But either way it came out the same: Unix. So there it was: having inherited an admittedly difficult
…
had managed to offend almost everybody by the middle of 1969. The crew at the AI Lab thought he was selling them out to Multics, and the Multics group thought he was selling them out to ARPA. But that, alas, was not the end of Lick's troubles. In the fall of
…
the help they could get. As Lick himself pointed out in his 1969 article about software for the antiballistic-missile system, the agonies that afflicted Multics, OS/360, and IBM's 360-compatible Time- ::- Project MAC itself became a target only once, and then very briefly, as the MIT protests reached
…
of getting MIT connected. Never mind that it gave the rest of Project MAC one more thing to be irritated about. The AI Lab, the Multics team, and all the oth- ers were welcome to drag their feet if they wanted. Lick was quietly determined to get his PDP-10 on
…
sites that ARPA was funding. We had Tenex systems at BBN running on PDP-10s, but there were also PDP-8s, PDP-11s, IBM 360s, Multics on Honeywell machines-you name it. So we had to implement the protocols on each of these different architec- tures." And once they'd done
…
networks was the same principle, just one level up. Perhaps the idea also resonated with the open-software architecture of operating systems such as CTSS, Multics, and Unix, which gave users a standard interface for writing their own programs. Or perhaps it even resonated with Alan Kay's notion of software
…
, says Dertouzos. If nothing else, there was the name change: Project MAC was now LCS, the Laboratory for Computer Science. (The argument was that with Multics as finished as it would ever be, and with the Tech Square crowd's moving on to a variety of new activities, neither "Multi-Access
…
modify as you wished. Dennis Ritchie and Ken Thompson had created Unix for their own use back in 1969, after Bell Labs' withdrawal from the Multics partnership, and the project had retained that loose, hands-on feeling ever since. Then, too, Ritchie and Thompson had created Unix with hacking in mind
…
, deriving its basic structure from Fernando Corbato's CTSS via Multics-namely, a tool kit of utilities and software routines that the user could call upon to per- form specific tasks, all built on top of
…
differ- ence was that the Unix kernel was a marvel of efficiency, simplicity, and con- ciseness. This was partly a reaction against the complexities of Multics (the 426 THE DREAM MACHINE designers kept the features that seemed truly useful, such as the file structure, and left out the more baroque elaborations
The Mythical Man-Month
by Brooks, Jr. Frederick P. · 1 Jan 1975 · 259pp · 67,456 words
systems shows that the brute-force approach is costly, slow, inefficient, and produces systems that are not conceptually integrated. OS/360, Exec 8, Scope 6600, Multics, TSS, SAGE, etc.—the list goes on and on. The conclusion is simple: if a 200-man project has 25 managers who are the most
…
, however, a mean productivity of 1200 lines of debugged PL/I statements per man-year on the MULTICS system (between 1 and 2 million words).10 This number is very exciting. Like the other projects, MULTICS includes control programs and language translators. Like the others, it is producing a system programming product
…
I translate these to PL/I for matching to the system environment. Interactive programming. One of the justifications for MIT's Multics project was its usefulness for building programming systems. Multics (and following it, IBM's TSS) differs in concept from other interactive computing systems in exactly those respects necessary for systems
…
facilities for cooperative work among terminal users. I am convinced that interactive systems will never displace batch systems for many applications. But I think the Multics team has made its most convincing case in the system-programming application. There is not yet much evidence available on the true fruitfulness of such
…
were improved and implemented in 1963 in an experimental system for the 7090 by Corbato and colleagues at MIT.7 This development led to the MULTICS, TSS, and other time-sharing systems of today. The chief user-perceived differences between on-machine debugging as first practiced and the interactive debugging of
…
's: 0.6-0.8 KLOC/man-year on operating systems and 2-3 KLOC/man-year on compilers. 8.9 Corbatd's MIT Project MULTICS data show productivity of 1.2 KLOC/man-year on a mix of operating systems and compilers, but these are PL/I lines of code
…
, 1968), pp. 28-31. Chapter 11 Speech at Oglethorpe University, May 22, 1932. An illuminating account of Multics experience on two successive systems is in F. J. Corbatd, J. H. Saltzer, and C. T. Clingen, "Multics—the first seven years," AFIPS Proc S/CC, 40 (1972), pp. 571-583. Cosgrove, J., "Needed
…
for system programming," IBM Research Report RC 3489, Yorktown Heights, N.Y., August 5, 1971. Corbatd, F. J., J. H. Saltzer, and C. T. Clingen, "Multics—the first seven years," AFIPS Proc SJCC, 40 (1972), pp. 571-582. "Only a half-dozen areas which were written in PL/1 have been
The Art of UNIX Programming
by Eric S. Raymond · 22 Sep 2003 · 612pp · 187,431 words
), either the first or second timesharing system ever deployed (depending on some definitional questions we are going to determinedly ignore). Its father was the pioneering Multics project, an attempt to create a feature-packed ‘information utility’ that would gracefully support interactive timesharing of mainframe computers by large communities of users
…
. Multics, alas, did collapse of its own weight. But Unix was born from that collapse. Genesis: 1969–1971 Unix was born in 1969 out of the
…
mind of a computer scientist at Bell Laboratories, Ken Thompson. Thompson had been a researcher on the Multics project, an experience which spoiled him for the primitive batch computing that was the rule almost everywhere else. But the concept of timesharing was still
…
-33 was the natural parent of the Unix tradition of terse commands and sparse responses. When Bell Labs withdrew from the Multics research consortium, Ken Thompson was left with some Multics-inspired ideas about how to build a file system. He was also left without a machine on which to play a
…
-inventor of Unix and the inventor of the C language. Dennis Ritchie, Doug McIlroy, and a few colleagues had become used to interactive computing under Multics and did not want to lose that capability. Thompson's PDP-7 operating system offered them a lifeline. Ritchie observes: “What we wanted to preserve
…
not attach itself until 1970. The original spelling was “UNICS” (UNiplexed Information and Computing Service), which Ritchie later described as “a somewhat treacherous pun on Multics”, which stood for MULTiplexed Information and Computing Service. Even at its earliest stages, PDP-7 Unix bore a strong resemblance to today's Unixes and
…
systems. This pattern was set early, within Bell Labs itself. The Unix tradition of lightweight development and informal methods also began at its beginning. Where Multics had been a large project with thousands of pages of technical specifications written before the hardware arrived, the first running Unix code was brainstormed by
…
that Thompson and colleagues were building was incubating an operating system. Operating systems were not in the Bell Labs plan — AT&T had joined the Multics consortium precisely to avoid doing an operating system on its own. Nevertheless, the completed system was a rousing success. It established Unix as a permanent
…
culture was largely hosted on PDP-10 minicomputers. They used a variety of operating systems that have since passed into history: TOPS-10, TOPS-20, Multics, ITS, SAIL. They programmed in assembler and dialects of Lisp. PDP-10 hackers took over running the ARPANET itself because nobody else wanted the job
…
not have been trivial without the fundamental unifying notion of the process as an autonomous unit of computation, with process control being programmable. As in Multics, a shell was just another process; process control did not come from God inscribed in JCL. -- Doug McIlroy If an operating system makes spawning new
…
the CTSS system, developed at MIT around 1963 and running on the IBM 7094 mainframe. The group that developed CTSS then went on to write Multics, the immediate ancestor of Unix. IBM established a group in Cambridge to write a timesharing system for the IBM 360/40, a modified 360 with
…
a user interface that was very CTSS-like, complete with a shell named EXEC and a large supply of utilities analogous to those used on Multics and later on Unix. In another sense, VM/CMS and Unix are funhouse mirror images of one another. The unifying idea of the system, provided
…
for the future of Unix as a whole, a topic we'll return to in Chapter 20. * * * [24] See the OSData website. [25] Except for Multics which exerted most of its influence between the time its specifications were published in 1965 and when it actually shipped in 1969. [26] For details
…
comparison timesharing systems that either are now or have in the past been competitive with Unix. The field of plausible candidates is not wide. Most (Multics, ITS, DTSS, TOPS-10, TOPS-20, MTS, GCOS, MPE and perhaps a dozen others) are so long dead that they are fading from the collective
…
now-definitive version is Stallman's derived from Greenberg's. No complete account of the design history has been written in 2003, but Greenberg's Multics Emacs: The History, Design, and Implementation is illuminating and readily discoverable via keyword search on the Web. [120] http://www.cs.yorku.ca/~oz/wily
…
] is the best known, but one can find prefigurations in Brooks [Brooks] (1975) and as far back as Vyssotsky and Corbató's meditations on the Multics design (1965). I failed to get it over more than twenty years of observing software development, before being awakened by Linux in the mid-1990s
Hackers: Heroes of the Computer Revolution - 25th Anniversary Edition
by Steven Levy · 18 May 2010 · 598pp · 183,531 words
, which was operating since the mid-sixties, was the Compatible Time-sharing System (CTSS). The other, long in preparation and high in expense, was called Multics and was so offensive that its mere existence was an outrage. Unlike the quiltwork of constantly improving systems programs operating on the PDP-6, CTSS
…
got inside the system and changed the heading of that memo from MAC to HAC. But as bad as CTSS was, the hackers thought Multics was worse. Multics was the name of the hugely expensive time-sharing system for the masses being built and debugged on the ninth floor. Though it was
…
in a very personal light, especially a system created on the very floor of the building in which they hacked. So MULTICS was a big topic of hacker conversation. Originally, Multics was done in conjunction with General Electric; then Honeywell stepped in. There were all sorts of problems with it. As soon
…
sluggish. It was so slow that the hackers concluded the whole system must be brain-damaged, a term used so often to describe Multics that “brain-damaged” became a standard hackerese pejorative. But the worst thing about Multics was the heavy security and the system of charging the user for the time
…
. Multics took the attitude that the user paid down to the last nickel; it charged some for the memory you used, some more for the
…
disk space, more for the time. Meanwhile the Multics planners, in the hacker view, were making proclamations about how this was the only way that utilities could work. The system totally turned the Hacker
…
), it urged you to spend less time—and to use less of the computer’s facilities once you were on! The Multics philosophy was a disaster. The hackers plagued the Multics system with tricks and crashes. It was almost a duty to do it. As Minsky would later say, “There were people
…
was in constant demand; people were frustrated by long waits for access. But the hackers did not consider time sharing acceptable. They pointed at CTSS, Multics, even at Jack Dennis’ more amiable system on the PDP-1, as examples of the slower, less powerful access one would be stuck with when
…
. The more safeguards the system had against this, the bigger the challenge would be for some random hacker to bring the thing to its knees. Multics, for instance, required a truly nontrivial hack before it bombed. So there’d always be macho programmers proving themselves by crashing
…
Multics. ITS, in contrast, had a command whose specific function was crashing the system. All you had to do was type KILL SYSTEM, and the PDP-
…
BASIC Motorola microprocessors, Woz Mouse in the Maze game, Spacewar, The Wizard and the Princess Mouskattack game, The Third Generation Multi-format disk scheme, Applefest Multics, Winners and Losers, Winners and Losers Multiple Access Computing, Spacewar Mung (Mash Until No Good), The Tech Model Railroad Club Muppets, The, Frogger Music program
A People’s History of Computing in the United States
by Joy Lisi Rankin
a short-lived phenomenon of the 1960s, and they have focused on three t hings: the Massachusetts Institute of Technology (MIT), its Multics time-sharing project, and the financial market for time-sharing. They have overlooked that time-sharing systems were networks and that users appreciated the
…
believe. Neither time-sharing nor the vision for networked computing for the public good w ere short-lived, nor did they exclusively parallel the MIT-Multics-markets trajectory that others have highlighted. Chapter 5 exemplifies the unifying themes of the previous four chapters. It analyzes the drive for, and development of
…
businesses as v iable and attractive opportunities. ARPA invested millions of dollars in the new MIT time-sharing system, known as Multics (Multiplexed Information and Computing Service). The Multics team anticipated a system with one thousand terminals, of which three hundred could be used simultaneously. Fano and Corbató
…
to maintain its stronghold in the time-sharing realm. Ultimately the business market and the academic vision for computer utilities w ere prominently linked; through Multics, the fortunes of MIT, IBM, GE , and Bell Labs became entangled. During the 1950s and the first half of the 1960s, MIT and IBM enjoyed
…
appeared more responsive to academia’s time-sharing dreams. MIT opted to build Multics with GE computers. MIT’s choice of GE over IBM for its Multics machines stunned the business community, and MIT’s partnership with Bell Labs for Multics programming amplified the symbolic significance of the project. MIT, GE , and
…
and computing utilities; at the time and since, the ways in which journalists and historians alike focused on the struggles of MIT’s prominent Multics project masked the growth of the computing utilities business and GE’s success in that realm. Although MIT decision makers perceived GE as agile
…
simultaneous users at the outset. Thus, GE employees struggled to create the computing infrastructure to meet the Multics goal of hundreds of simultaneous users. In contrast, while MIT and GE grappled with Multics, Dartmouth students and GE employees successfully collaborated to expand the college’s time- sharing network. The Bell Labs
…
employees tasked with programming Multics w ere, like their GE colleagues on the MIT project, overwhelmed. Bell withdrew from
…
Multics in 1969, and a year later GE withdrew from the mainframe business. IBM had belatedly jumped
…
, “The MAC System: The Computer Utility Approach,” IEEE Spectrum 2, no. 1 (1965): 56–64; Fernando J. Corbató, Jerome H. Saltzer, and Chris T. Clingen, “Multics: The First Seven Years,” in Proceedings of the May 16–18, 1972, Spring Joint Computer Conference (New York: ACM, 1972), 571–583; J. A. N
…
’62 (Spring), 335–344. New York: ACM , 1962. doi:10.1145/1460833.1460871. Bibliography 301 Corbató, Fernando J., Jerome H. Saltzer, and Chris T. Clingen. “Multics: The First Seven Years.” In Proceedings of the May 16–18, 1972, Spring Joint Computer Conference, 571–583. New York: ACM , 1972. Cornew, Ronald W
…
, 194–195, 201–205, 207, 225, 233; ARPANET and, 9, 107, 109, 135–137, 194–195, 205–207, 224–225; Licklider’s role in, 114; Multics and, 116; myt hology of, 107 African American. See Race Albrecht, Bob, 95, 102, 229, 234–236; role in spreading BASIC, 7, 68
…
, 173; Index GE and, 24, 107, 119, 123–124; IBM, relationship with, 107, 110–111, 119, 123–124; mainframe computing and, 12, 14–15, 18; Multics and, 7–8, 116, 123–124; New England Computation Center at, 12, 16, 18, 91; SAGE project and, 110–111, 113–114, 123; time
…
, 84, 86 Mount Holyoke College (Massachusetts), 48, 56, 91, 93–94 Mouse: cartoon character, 222–223; technology, 189–190 Mueller, Van, 148 Multics. See Multiplexed Information and Computing Service Multiple-access computer (MAC) project, 114, 116, 119, 124 321 Multiplexed Information and Computing Serv ice
…
(Multics), 7, 8, 116, 123–124 Multiplexor, 161 My t hology, 2–4, 8, 10, 106–107, 190–192, 242 National Computer Development Agency (NCDA),
Computer: A History of the Information Machine
by Martin Campbell-Kelly and Nathan Ensmenger · 29 Jul 2013 · 528pp · 146,459 words
-sharing computer system that would be able to grow in a modular way and eventually support several hundred users. This system would be known as Multics (for Multiplexed Information and Computing Service). MIT had a long-standing relationship with IBM, and it had been assumed by the senior administrators in both
…
was an opportunity for GE to make a last effort to establish a profitable mainframe operation by attacking a market where IBM was particularly weak. Multics was to be the most ambitious time-sharing system yet; costing up to $7 million, it would support up to a thousand terminals, with three
…
the company was rich in computing talent but was not permitted, as a government-regulated monopoly, to operate as an independent computer-services company. The Multics contract enabled Bell Labs to find an outlet for its computing expertise and to continue building up its software-writing capabilities. Having been pushed aside
…
relatively simple Dartmouth-based system, and with thirty time-sharing centers in the United States and Europe running commercially, GE expected development of the new Multics system to be straightforward. The company and its partners, MIT and Bell Labs, were wholly unprepared for the magnitude of the software development problems. After
…
desire for communal computing that would surface again with the Internet in the 1990s. UNIX There was, however, one very beneficial spin-off of the Multics imbroglio: the Unix operating system, developed at Bell Labs during 1969–1974. The software disasters epitomized by OS/360 and
…
Multics occurred because they were too baroque. This led a number of systems designers to explore a small-is-beautiful approach to software that tried to
…
-haired, and portly—conformed to the stereotype of the 1960s computer guru. When Bell Labs pulled out of the Multics project in 1969, Thompson and Ritchie were left frustrated because working on Multics had provided them with a rather attractive programming environment: We didn’t want to lose the pleasant niche we
…
their own ideas and decided to explore the development of a small, elegant operating system that they later called Unix—“a somewhat treacherous pun on ‘Multics.’” Hardware was less forthcoming than freedom to pursue this research whim, however, and they “scrounged around, coming up with a discarded obsolete computer”—a PDP
…
Indicator (MTI) devices, 70–71 MS-DOS operating system, 199, 247, 256–258, 264, 265 MSN online service, 290–291 Multiple Information and Computing Service (Multics), 209–210, 214 Multiprogramming systems, 180–182 MySpace, 300–301, 302 Napster, 249 National BankAmericard Incorporated (NBI), 159, 160 National Cash Register Company (NCR). See
Founders at Work: Stories of Startups' Early Days
by Jessica Livingston · 14 Aug 2008 · 468pp · 233,091 words
really good way to learn an area in college is to work on a real project in one of the labs. I worked at the Multics project, which was a major project in the history of operating systems. Out of it came the Unix system and the 386-style chipset and
…
, when it was cheap. I mean really late. Basically, he slept during the day. Livingston: That was at MIT, right? Bricklin: We used MIT’s Multics system, the one we worked on. Livingston: Did they mind? Bricklin: No. We paid for it. Luckily it took a few months to be billed
…
a bank and from relatives, and we bought a Prime minicomputer, which had an operating system based on the ideas of Multics, done by people who used to work at Multics. We bought one of those of our own, and we sublet space through some other friends who had a business, and
…
NBI’s (Nothing But Initials) system, were document-oriented. This was before Wang did their first screen-based word processor. I came out of the Multics project, which used the Runoff system, which Jerry Saltzer had developed for the CTSS (the Compatible Time Sharing System), which was one of the first
…
Morris, Harry, 271, 272 Morris, Robert, 205, 447 motto, 161, 169 Movable Type, 405–412 Moveover, 118 Mozilla Foundation, 395 MSNTV, 188. See also WebTV Multics project, 73 462 Index Mundie, Craig, 428 Muxway, 224 Myers-Briggs corporate personality test, 387 N NASDAQ, 443–444 National Computer Conference, 78 NEA, 193
Coding Freedom: The Ethics and Aesthetics of Hacking
by E. Gabriella Coleman · 25 Nov 2012 · 398pp · 107,788 words
CRITIQUE OF INTELLECTUAL PROPERTY LAW EPILOGUE: HOW TO PROLIFERATE DISTINCTIONS, NOT DESTROY THEM NOTES REFERENCES INDEX ACKNOWLEDGMENTS This project marks the culmination of a multiyear, multicity endeavor that commenced in earnest during graduate school, found its first stable expression in a dissertation, and has, over a decade later, fully realized itself
…
of birth. Unix derives from another related OS, the much larger Multics, originally developed in AT&T’s Bell Labs. In 1969 Bell Labs canceled funding for Multics; its authors, Ken Thomson and Denis Ritchie, salvaged (and many would say improved) Multics by parsing it down to a much smaller system, which they
…
renamed Unix. Once Unix was “cut down,” its creators renamed Multics to “eunuchs” to capture the idea that some really significant “things” had been cut from its body, but what was created was something forever eternally
…
beautiful. Eventually, its creators kept the phonetic instantiation of eunuchs (Unix) to commemorate and signal its conditions of birth as an essentially castrated version of Multics. The cultural depth of Unix far exceeds naming conventions. Unix has been described as “our Gilgamesh epic” (Stephenson 1999), and its status is that of
…
, 69. See also Stallman, Richard Mitnick, Kevin, 16, 18 MITS. See Altair Moglen, Eben, 185 Motion Picture Association of America (MPAA), 71, 85, 171, 174 Multics, 36–37 Murdock, Ian, 43, 52, 129–30 Mutt, 102 Nelson, Ted, 218n8 neoliberalism, 4, 11, 66, 73, 89, 192–93, 196, 199 Netscape, 78
Coders at Work
by Peter Seibel · 22 Jun 2009 · 1,201pp · 233,519 words
not at the point where some of the more forward-looking timesharing systems were way, way back. Seibel: Which ones are you thinking of? Crockford: MULTICS was doing some really interesting stuff in cooperative processes, and having multiple address spaces which were able to communicate with each other but couldn't
…
start doing cooperative computing. And we're now trying to figure out how to get that into the browser. It's a long time between MULTICS and here. We're starting now to catch up to insights that were being acted on way back then. Seibel: I've noticed a similar
…
calls that were the equivalent of getc and putc. The other place where issues of interface started to show up were—again, based on the MULTICS mode—from the beginning we had a strong distinction between the kernel and what today we would call the shell. This was early enough in
…
times, included analog computing, systems programming, regular expressions, and computer chess. Hired as a researcher at Bell Labs to work on the MULTICS project, after Bell Labs pulled out of MULTICS, Thompson went on, with Dennis Ritchie, to invent Unix, an endeavor for which he fully expected to be fired. He also
…
kind of things did you do when you first arrived there? Thompson: Bell Labs was in the MULTICS project and I was hired in to work on MULTICS. And I did. I played with the machines, booted up MULTICS, and did my little piece of it. At some point, Bell Labs decided that
…
MULTICS wasn't for them, and they backed out of the project. But they had these MULTICS machines which were special-purpose machines that were just sitting around idle until someone could cart them away. So for approximately a
…
was some basic research we should be doing and some basic research we shouldn't be doing. And just coming out of the ashes of MULTICS, operating systems was one of those basic research things we shouldn't be doing. Because we tried it, it didn't work, it was a
…
a rivalry in their minds. Not in my mind at that point. We did Unix and they did MULTICS, which was this monster. This was just clearly the second-system syndrome. Seibel: Where MULTICS was the second system after the MIT's Compatible Time-Sharing System? Thompson: Yes. So overdesigned and overbuilt
…
still claim it's a monstrous success, but it just clearly wasn't. Seibel: My understanding was that a lot of the MIT hackers viewed MULTICS that same way. They preferred ITS and the Lisp-based systems that they built. It seems there was a real fork post
…
-MULTICS. Unix came out, as you well know, and at MIT these Lisp guys went off and did their things on PDP-10s and built Lisp-
…
's not faster. There was just no reason to ever build a Lisp machine. It was kind of stupid. Seibel: Are there any features of MULTICS that you did like but that never made it into Unix? Thompson: The things that I liked enough to actually take were the hierarchical file
…
, 344 Morgan, Bob, 525 Morningstar, Chip, 95, 106 Moses, Joel, 330 Mozilla, 25, 133, 138, 143, 150, 151, 154, 156, 157, 158 MS-DOS, 419 MULTICS, 127, 449, 458, 463 MySQL, 60 NASA, 287, 288, 308, 309, 311, 312, 313 NCSA/Mosaic, 14 N NELIAC, 452, 462 Netscape, 10, 12, 14
The Moral Animal: Evolutionary Psychology and Everyday Life
by Robert Wright · 1 Jan 1994 · 604pp · 161,455 words
Dealers of Lightning
by Michael A. Hiltzik · 27 Apr 2000 · 559pp · 157,112 words
Where Wizards Stay Up Late: The Origins of the Internet
by Katie Hafner and Matthew Lyon · 1 Jan 1996 · 352pp · 96,532 words
Secrets and Lies: Digital Security in a Networked World
by Bruce Schneier · 1 Jan 2000 · 470pp · 144,455 words
Bootstrapping: Douglas Engelbart, Coevolution, and the Origins of Personal Computing (Writing Science)
by Thierry Bardini · 1 Dec 2000
From Airline Reservations to Sonic the Hedgehog: A History of the Software Industry
by Martin Campbell-Kelly · 15 Jan 2003
Nonzero: The Logic of Human Destiny
by Robert Wright · 28 Dec 2010

Engineering Security
by Peter Gutmann
The Linux kernel primer: a top-down approach for x86 and PowerPC architectures
by Claudia Salzberg Rodriguez, Gordon Fischer and Steven Smolski · 15 Nov 2005 · 1,202pp · 144,667 words
The Art of Software Security Assessment: Identifying and Preventing Software Vulnerabilities
by Justin Schuh · 20 Nov 2006 · 2,054pp · 359,149 words
How We Got Here: A Slightly Irreverent History of Technology and Markets
by Andy Kessler · 13 Jun 2005 · 218pp · 63,471 words
Smart Mobs: The Next Social Revolution
by Howard Rheingold · 24 Dec 2011
The Soul of a New Machine
by Tracy Kidder · 1 Jan 1981 · 299pp · 99,080 words
Shady Characters: The Secret Life of Punctuation, Symbols, and Other Typographical Marks
by Keith Houston · 23 Sep 2013
Kill It With Fire: Manage Aging Computer Systems
by Marianne Bellotti · 17 Mar 2021 · 232pp · 71,237 words
CIOs at Work
by Ed Yourdon · 19 Jul 2011 · 525pp · 142,027 words
Rebel Code: Linux and the Open Source Revolution
by Glyn Moody · 14 Jul 2002 · 483pp · 145,225 words
Wonder Boy: Tony Hsieh, Zappos, and the Myth of Happiness in Silicon Valley
by Angel Au-Yeung and David Jeans · 25 Apr 2023 · 427pp · 134,098 words
Structure and interpretation of computer programs
by Harold Abelson, Gerald Jay Sussman and Julie Sussman · 25 Jul 1996 · 893pp · 199,542 words
Escape From Rome: The Failure of Empire and the Road to Prosperity
by Walter Scheidel · 14 Oct 2019 · 1,014pp · 237,531 words
Masterminds of Programming: Conversations With the Creators of Major Programming Languages
by Federico Biancuzzi and Shane Warden · 21 Mar 2009 · 496pp · 174,084 words
The Tangled Web: A Guide to Securing Modern Web Applications
by Michal Zalewski · 26 Nov 2011 · 570pp · 115,722 words
Growth Hacker Marketing: A Primer on the Future of PR, Marketing, and Advertising
by Ryan Holiday · 2 Sep 2013 · 52pp · 14,333 words
Methland: The Death and Life of an American Small Town
by Nick Reding · 1 Jul 2009 · 250pp · 83,367 words
Interlibrary Loan Practices Handbook
by Cherie L. Weible and Karen L. Janke · 15 Apr 2011 · 144pp · 55,142 words
Kings of Crypto: One Startup's Quest to Take Cryptocurrency Out of Silicon Valley and Onto Wall Street
by Jeff John Roberts · 15 Dec 2020 · 226pp · 65,516 words
Peggy Seeger
by Jean R. Freedman
Making It in America: The Almost Impossible Quest to Manufacture in the U.S.A. (And How It Got That Way)
by Rachel Slade · 9 Jan 2024 · 392pp · 106,044 words
Hormone Repair Manual
by Lara Briden · 14 Apr 2021
Lonely Planet Nicaragua (Travel Guide)
by Lonely Planet, Alex Egerton and Greg Benchwick · 30 Jun 2013
Free as in Freedom
by Sam Williams · 16 Nov 2015
Lonely Planet Morocco (Travel Guide)
by Lonely Planet, Paul Clammer and Paula Hardy · 1 Jul 2014 · 2,020pp · 267,411 words
Applied Cryptography: Protocols, Algorithms, and Source Code in C
by Bruce Schneier · 10 Nov 1993
Joel on Software
by Joel Spolsky · 1 Aug 2004 · 370pp · 105,085 words
Selfish, Shallow, and Self-Absorbed: Sixteen Writers on the Decision Not to Have Kids
by Meghan Daum · 29 Mar 2015 · 214pp · 71,585 words
Giving the Devil His Due: Reflections of a Scientific Humanist
by Michael Shermer · 8 Apr 2020 · 677pp · 121,255 words
Your Computer Is on Fire
by Thomas S. Mullaney, Benjamin Peters, Mar Hicks and Kavita Philip · 9 Mar 2021 · 661pp · 156,009 words
The Politics Industry: How Political Innovation Can Break Partisan Gridlock and Save Our Democracy
by Katherine M. Gehl and Michael E. Porter · 14 Sep 2020 · 627pp · 89,295 words
Empire of AI: Dreams and Nightmares in Sam Altman's OpenAI
by Karen Hao · 19 May 2025 · 660pp · 179,531 words
The Evolution of God
by Robert Wright · 8 Jun 2009
The Smartest Guys in the Room
by Bethany McLean · 25 Nov 2013 · 778pp · 233,096 words
Our Own Devices: How Technology Remakes Humanity
by Edward Tenner · 8 Jun 2004 · 423pp · 126,096 words
Hacking Exposed: Network Security Secrets and Solutions
by Stuart McClure, Joel Scambray and George Kurtz · 15 Feb 2001 · 260pp · 40,943 words
Build Awesome Command-Line Applications in Ruby: Control Your Computer, Simplify Your Life
by David B. Copeland · 6 Apr 2012 · 408pp · 63,990 words

Code: The Hidden Language of Computer Hardware and Software
by Charles Petzold · 28 Sep 1999 · 566pp · 122,184 words
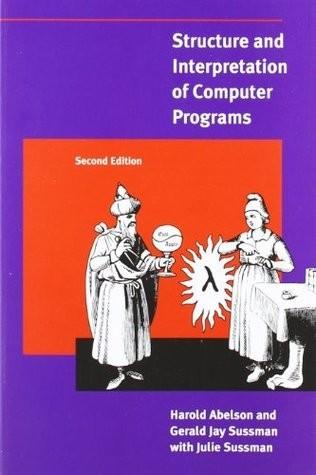
Structure and Interpretation of Computer Programs, Second Edition
by Harold Abelson, Gerald Jay Sussman and Julie Sussman · 1 Jan 1984 · 1,387pp · 202,295 words