Applied Cryptography: Protocols, Algorithms, and Source Code in C
by Bruce Schneier · 10 Nov 1993
UNIX program, called Crypt Breakers Workbench (CBW), can be used to break files encrypted with crypt(1). Other Schemes Another generator is based on the knapsack problem (see Section 19.2) [1363]. CRYPTO-LEGGO is insecure [301]. Joan Daemen has developed SubStream, Jam, and StepRightUp [402]; they are all too new to
…
the computation with the previous block; the first exponent is given by an IV. Ivan Damgård designed a one-way hash function based on the knapsack problem (see Section 19.2) [414]; it can be broken in about 232 operations [290, 1232, 787]. Steve Wolfram’s cellular automata [1608] have been proposed
…
]. It could only be used for encryption, although Adi Shamir later adapted the system for digital signatures [1413]. Knapsack algorithms get their security from the knapsack problem, an NP-complete problem. Although this algorithm was later found to be insecure, it is worth examining because it demonstrates how an NP-complete problem
…
can be used for public-key cryptography. The knapsack problem is a simple one. Given a pile of items, each with different weights, is it possible to put some of those items into a knapsack
…
of items in the pile. The idea behind the Merkle-Hellman knapsack algorithm is to encode a message as a solution to a series of knapsack problems. A block of plaintext equal in length to the number of items in the pile would select the items in the knapsack (plaintext bits corresponding
…
the b values), and the ciphertext would be the resulting sum. Figure 19.1 shows a plaintext encrypted with a sample knapsack problem. The trick is that there are actually two different knapsack problems, one solvable in linear time and the other believed not to be. The easy knapsack can be modified to create
…
. People who don’t know the private key are forced to try to solve the hard knapsack problem. Superincreasing Knapsacks What is the easy knapsack problem? If the list of weights is a superincreasing sequence, then the resulting knapsack problem is easy to solve. A superincreasing sequence is a sequence in which every term is greater
…
. The private key is a sequence of weights for a superincreasing knapsack problem. The public key is a sequence of weights for a normal knapsack problem with the same solution. Merkle and Hellman developed a technique for converting a superincreasing knapsack problem into a normal knapsack problem. They did this using modular arithmetic. Creating the Public Key from
…
a y2 (mod N). According to Diffie [492,494], the Discrete Logarithm Problem was suggested by J. Gill, the Factoring Problem by Knuth, and the knapsack problem by Diffie himself. This narrowness in the mathematical foundations of public-key cryptography is worrisome. A breakthrough in either the problem of factoring or of
…
–Knowledge Computations,” Advances in Cryptology—CRYPTO ’87 Proceedings, Springer–Verlag, 1988, pp. 40–51. 754. I. Ingemarsson, “A New Algorithm for the Solution of the Knapsack Problem,” Lecture Notes in Computer Science 149; Cryptography: Proceedings of the Workshop on Cryptography, Springer–Verlag, 1983, pp. 309–315. 755. I. Ingemarsson, “Delay Estimation for
…
, 462–466 decryption, 465 encryption, 464 implementations, 465 patents, 466 public key created from private key, 464 security, 465 superincreasing, 463–464 variants, 465–466 Knapsack problem, 501 Known-plaintext attack, 6–7, 151, 359 Knudsen, Lars, 8, 293, 314, 316, 348–349 Knuth, 393, 501 Koblitz, Neal, 480 Konheim, Alan, 266
Crypto: How the Code Rebels Beat the Government Saving Privacy in the Digital Age
by Steven Levy · 15 Jan 2002 · 468pp · 137,055 words
figure out a way to tame this difficult problem for the proper keyholder. He did this by first using a much easier variation of the knapsack problem called a superincreasing knapsack. In these problems, the list of weights is ordered in such a way that discovering the solution is a breeze. Merkle
…
embarrassingly simple.” To be sporting about it, he made the task immeasurably easier, asking potential crackers to solve the problem with the difficulty of the knapsack problem set at a level so low that Merkle knew that there was at least a remote chance that someone might collect the reward. After that
Algorithms Unlocked
by Thomas H. Cormen · 15 Jan 2013
that all the other integers in S 0 came from R. Hence, there is a subset of R that sums to t. Knapsack In the knapsack problem, we are given a set of n items, each with a weight and a value, and we ask whether there exists a subset of items
…
which items to take backpacking or what loot a burglar should choose to pilfer. The partition problem is really just a special case of the knapsack problem, in which the value of each item equals its weight and both W and V equal half the total weight. If we could solve the
…
knapsack problem in polynomial time, then we could solve the partition problem in polynomial time. Therefore, the knapsack problem is at least as hard as the partition problem, and we don’t even need to go
…
through the full reduction process to show that the knapsack problem is NP-complete. General strategies As you have probably realized by now, there is no one-size-fits-all way to reduce one problem to
…
problems are just special cases of other NPcomplete problems, much as the partition problem is a special case of Chapter 10: Hard? Problems 207 the knapsack problem. If you know that problem X is NP-complete and that it’s a special case of problem Y, then problem Y must be NPcomplete
…
as well. That is because, as we saw for the knapsack problem, a polynomial-time solution for problem Y would automatically give a polynomial-time solution for problem X. More intuitively, problem Y, being more general than
…
, 158 Kevin Bacon number, 90–91 key in cryptography, 139 public, 144 in searching, 26 secret, 144 in sorting, 26 KMP string-matching algorithm, 136 knapsack problem, 205 Knuth-Morris-Pratt string-matching algorithm, 136 last in, first out, 77 LCS, see longest common subsequence leaf, 98 leaving edge, 75 lexicographic ordering
Life's Edge: The Search for What It Means to Be Alive
by Carl Zimmer · 9 Mar 2021 · 392pp · 109,945 words
problem in a few days. It’s kept them busy for centuries. Another puzzle that has kept generations of mathematicians busy is known as the Knapsack Problem. Imagine you’re preparing for a hike, and you have to decide what to put in your knapsack. You can choose from a lot of
…
. Now you must find the combination of items with the greatest value that is under a certain weight. Many businesses face practical versions of the Knapsack Problem. Airline companies want to figure out how to pack their planes so they can deliver the most valuable cargo using the least amount of fuel
…
. Financial firms look for the best way to spread their funds across investments with different potential returns. There’s no simple equation to solve the Knapsack Problem, though. Researchers have filled books with strategies to get us close to the best solution. Slime molds may not be able to write books, but
…
they can solve the Knapsack Problem. Audrey Dussutour, a scientist at Paul Sabatier University in Toulouse, France, and her colleagues brought their skill to light by translating the problem into the
…
Joyce, Gerald, 199, 209 Jupiter, 260 Kasianowicz, John, 230 Kaufmann, Stuart, 283, 284–85, 286, 291 kelp, 5–6 kidneys, 52–53, 60, 70, 74 Knapsack Problem, 85–86 Koch, Christof, 33–34 Kolbe, Hermann, 150 Kompanichenko, Vladimir, 236 Lamarckian evolution, 270 Lavoisier, Antoine, 149 Lederberg, Joshua, 25, 34, 251, 254 Leduc
The Logician and the Engineer: How George Boole and Claude Shannon Created the Information Age
by Paul J. Nahin · 27 Oct 2012 · 229pp · 67,599 words
) that could also benefit from the massive parallelism of a quantum computer are the so-called knapsack problems. They are old problems, dating back at least to 1897, but they have modern applications, including cryptography. One knapsack problem asks the following question: given a stretchable knapsack that can hold a maximum weight of W
…
J-K flip-flop Jobs, Steve Karnaugh, Maurice; map of Kelland, Philip Kelly, Jr., John Kelvin, Lord. See Thomson, William Kirchhoff, Gustav; circuit laws of knapsack problems Landauer, Rolf Laplace, Pierre-Simon latch Leibniz, Gottfried Levor, Norma logical operations: and; exclusive-or; inclusive-or; NOT. See also switch logic gates: irreversible; reversible
Algorithms to Live By: The Computer Science of Human Decisions
by Brian Christian and Tom Griffiths · 4 Apr 2016 · 523pp · 143,139 words
accepting the consequences). A rock band deciding which songs to cram into a limited set, for instance, is up against what computer scientists call the “knapsack problem”—a puzzle that asks one to decide which of a set of items of different bulk and importance to pack into a confined volume. In
…
its strict formulation the knapsack problem is famously intractable, but that needn’t discourage our relaxed rock stars. As demonstrated in several celebrated examples, sometimes it’s better to simply play
…
|∑ Cj?” “Nothing” [Lawler et al., “A Gift for Alexander!”; see also Lawler, “Old Stories”].) the problem becomes intractable: In fact, it’s equivalent to the “knapsack problem,” computer science’s most famously intractable problem about how to fill space. The connection between this scheduling problem and the
…
knapsack problem appears in Lawler, Scheduling a Single Machine to Minimize the Number of Late Jobs. a certain time to start some of your tasks: What we
…
, Johannes Kerr, Clark Keynes, John Maynard al-Khwārizmī King County Library System (KCLS) king of the hill Kipling, Rudyard Kirkpatrick, Scott Kleinrock, Leonard Kline, Charley knapsack problem Knuth, Donald Koomen, Pete Ladder tournaments Lagrange, Joseph-Louis Lagrangian Relaxation Lai, Tze Leung lancet liver fluke Lange, Rebecca language Lao Tzu Laplace, Pierre-Simon
Accelerando
by Stross, Charles · 22 Jan 2005 · 489pp · 148,885 words
showers, he sits on the toilet seat lid and rants about Turing-completeness as an attribute of company law, about cellular automata and the blind knapsack problem, about his work on solving the Communist Central Planning problem using a network of interlocking unmanned companies. About the impending market adjustment in integrity, the
Competing on Analytics: The New Science of Winning
by Thomas H. Davenport and Jeanne G. Harris · 6 Mar 2007 · 233pp · 67,596 words
goods supply chain, for example, it used an “integral min-cost flow problem with side constraints”; to round off fractional shipments, it used a “multiple knapsack problem using the greedy algorithm.” Logistics Management Sometimes a service company uses analytics with such skill and execution that entire lines of business can be created
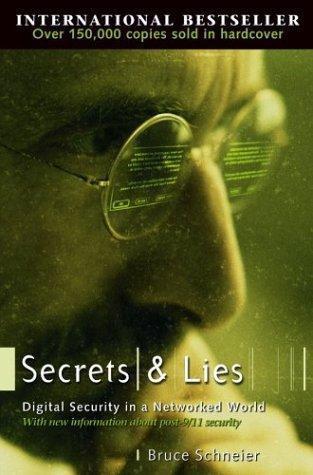
Secrets and Lies: Digital Security in a Networked World
by Bruce Schneier · 1 Jan 2000 · 470pp · 144,455 words
elide the details. Today, there are a good half-dozen algorithms, with names like RSA, ElGamal, and elliptic curves. (Algorithms based on something called the knapsack problem were another early contender, but over the course of about 20 years they were broken every which way.) The mathematicals are different for each algorithm