national security letter
description: US government administrative subpoena
24 results
Pax Technica: How the Internet of Things May Set Us Free or Lock Us Up
by Philip N. Howard · 27 Apr 2015 · 322pp · 84,752 words
, http://www.cnet.com/news/how-the-u-s-forces-net-firms-to-cooperate-on-surveillance/. 22. Kim Zetter, “Google Takes on Rare Fight Against National Security Letters,” Wired, April 4, 2013, accessed September 30, 2014, http://www.wired.com/2013/04/google-fights-nsl/. 23. “Lavabit,” accessed June 16, 2014, http://lavabit
Click Here to Kill Everybody: Security and Survival in a Hyper-Connected World
by Bruce Schneier · 3 Sep 2018 · 448pp · 117,325 words
surveillance through a variety of mechanisms. Governments regularly demand access to that data in ways that don’t require a warrant, such as subpoenas and national security letters. I worry that some of the catastrophic risks I wrote about in Chapter 5 will lead policy makers to go beyond backdoors and weakened cryptography
Culture & Empire: Digital Revolution
by Pieter Hintjens · 11 Mar 2013 · 349pp · 114,038 words
thriving corporations denying their level of cooperation with the NSA, you need to question their freedom to tell the truth. When a firm receives a National Security Letter, it is obliged by law to deny that fact. The tragic irony is that it's the nicer business executives, the 96% or so who
Digital Disconnect: How Capitalism Is Turning the Internet Against Democracy
by Robert W. McChesney · 5 Mar 2013 · 476pp · 125,219 words
continues to exist.238 Since September 11, 2001, when it comes to spying on Americans, the Federal Bureau of Investigation has increasingly turned to the National Security Letter (NSL), an administrative demand letter or subpoena requiring neither probable cause nor judicial oversight. As David Rosen puts it: In effect, an NSL overrides 4th
…
Science Foundation, 101 National Science Foundation Network (NSFNet), 102, 104 national security, 51–52, 53, 100, 159–71, 196 National Security Agency, 161, 163, 164 National Security Letter (NSL), 166, 167 Naughton, John, 12, 72, 108, 135, 136, 161, 190 NBC Universal, 124, 137 NCTA v. Brand X, 111 “negative externalities,” 50–51
Future Crimes: Everything Is Connected, Everyone Is Vulnerable and What We Can Do About It
by Marc Goodman · 24 Feb 2015 · 677pp · 206,548 words
daily life of petitioners and beneficiaries suspected of fraud.” Federal agents can readily access your social data through a variety of means, by serving subpoenas, national security letters, and other administrative orders on your service providers, who under the third-party doctrine exception to the Fourth Amendment needn’t even notify you of
Dark Territory: The Secret History of Cyber War
by Fred Kaplan · 1 Mar 2016 · 383pp · 105,021 words
group’s staff had requested detailed briefings on the bureau’s relationship with the NSA and on its own version of metadata collection, known as National Security Letters, which, under Section 505 of the Patriot Act, allowed access to Americans’ phone records and other transactions that were deemed “relevant” to investigations into terrorism
…
allotted. Ten minutes into this dog-and-pony show, Clarke asked about the briefings that they’d requested. Specifically, he wanted to know how many National Security Letters the FBI issued each year and how the bureau measured their effectiveness. One of the officials responded that only the regional bureaus had those numbers
…
’s centerpiece: if the president rejected it, he felt, the whole exercise will have been pointless. Another proposal was to bar the FBI from issuing National Security Letters without a FISA Court order and, in any case, letting recipients disclose that they’d received such a letter after 180 days, unless a judge
…
“potential for abuse.” And so, he accepted many of its other recommendations. He rejected the proposal to require FISA Court orders for the FBI’s National Security Letters, but he did limit how long the letters could remain secret. (He eventually settled on a limit of 180 days, with a court order required
…
FANEX, 18, 66 Faurer, Lincoln, 26, 28 Federal Bureau of Investigation (FBI), 63, 74, 77–78, 98, 269, 288n National Infrastructure Protection Center of, 166 National Security Letters of, 254–55, 256, 260 Review Group briefings by, 254–55 Review Group recommendations for, 256 Federal Intrusion Detection Network (FIDNET), 100–102 Federal Trade
…
and, 156, 185 Tailored Access Operations of, see TAO National Security Council (NSC), 40, 97, 140, 150, 187, 188, 227 National Security Directive 42, 66 National Security Letters, 254–55, 260 Review Group recommendations for, 256 National Strategy to Secure Cyberspace, The, 141–42, 174, 199 Naval Postgraduate School, 148 Navy, U.S
Tools and Weapons: The Promise and the Peril of the Digital Age
by Brad Smith and Carol Ann Browne · 9 Sep 2019 · 482pp · 121,173 words
to the cloud. And we’d go to court to make it stick. We faced our first test when the FBI served us with a national security letter seeking data that belonged to an enterprise customer. The letter barred us from telling the customer that the FBI wanted its data. We studied the
Consent of the Networked: The Worldwide Struggle for Internet Freedom
by Rebecca MacKinnon · 31 Jan 2012 · 390pp · 96,624 words
its wiretapping of phone lines, as of mid-2011 it was not required to do so with Internet communications. Furthermore, until 2009, companies complying with National Security Letters (NSL)—a kind of administrative demand letter requiring no probable cause or judicial oversight—were barred by a provision of the Patriot Act from informing
…
intelligence investigations was found to be “ineffectual.” Furthermore, the EFF found that in nearly half of cases in which the FBI abused the use of National Security Letters requesting information, phone companies, Internet service providers, financial institutions, and credit agencies “contributed in some way to the FBI’s unauthorized receipt of personal information
…
Mozilla MSN Spaces Mubarak, Hosni Mubarak, Suzanne Mueller, Milton Mullenweg, Matt Munk Center, University of Toronto NARAL Pro-Choice America Narus Nashi National Religious Broadcasters National Security Letters (NSL), unconstitutionality of Navalny, Alexey Nawaat The Net Delusion (Morozov) Net neutrality abuse of arguments against Federal Communications Commission rules on laws promoting mobile access
…
in disclosure laws, necessity for Electronics Communications Privacy Act of 1986 (ECPA) Foreign Intelligence Surveillance Act (FISA) Amendments Act (2008) government requests for subscriber information National Security Letters (NSL), unconstitutionality of Patriot Act (2001) public accountability whistle-blowers wiretapping of Internet communications Universal Declaration of Human Rights US National Security Agency (NSA) US
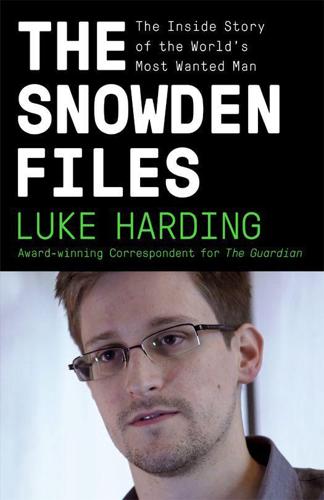
The Snowden Files: The Inside Story of the World's Most Wanted Man
by Luke Harding · 7 Feb 2014 · 266pp · 80,018 words
law professor. Barack Obama, in a 2007 stump speech for his nascent presidential campaign, had pledged, ‘No more illegal wiretapping of American citizens. No more National Security Letters to spy on American citizens who are not suspected of a crime. No more tracking citizens who do no more than protest a misguided war
Come and Take It: The Gun Printer's Guide to Thinking Free
by Cody Wilson · 10 Oct 2016 · 246pp · 70,404 words
-printing closet to fool the corporate repairman. “Are you not worried now?” John asked. “I mean, this is the part where they send us the national security letter. Or where you get disappeared.” “This ex–Special Forces guy started emailing me a couple months ago,” I said. “We talk now, and the other
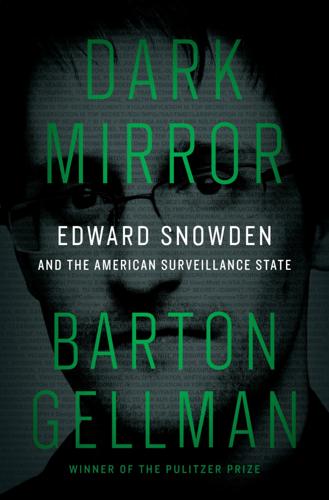
Dark Mirror: Edward Snowden and the Surveillance State
by Barton Gellman · 20 May 2020 · 562pp · 153,825 words
Nothing to Hide: The False Tradeoff Between Privacy and Security
by Daniel J. Solove · 28 Jun 2011 · 257pp · 72,251 words
Great American Hypocrites: Toppling the Big Myths of Republican Politics
by Glenn Greenwald · 14 Apr 2008 · 286pp · 79,601 words
Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World
by Bruce Schneier · 2 Mar 2015 · 598pp · 134,339 words
The Future of the Internet: And How to Stop It
by Jonathan Zittrain · 27 May 2009 · 629pp · 142,393 words
The Dangerous Case of Donald Trump: 27 Psychiatrists and Mental Health Experts Assess a President
by Bandy X. Lee · 2 Oct 2017 · 369pp · 105,819 words
Terms of Service: Social Media and the Price of Constant Connection
by Jacob Silverman · 17 Mar 2015 · 527pp · 147,690 words
Careless People: A Cautionary Tale of Power, Greed, and Lost Idealism
by Sarah Wynn-Williams · 11 Mar 2025 · 370pp · 115,318 words
Three Felonies a Day: How the Feds Target the Innocent
by Harvey Silverglate · 6 Jun 2011 · 389pp · 136,320 words
The Rights of the People
by David K. Shipler · 18 Apr 2011 · 495pp · 154,046 words
Habeas Data: Privacy vs. The Rise of Surveillance Tech
by Cyrus Farivar · 7 May 2018 · 397pp · 110,222 words
Paper Knowledge: Toward a Media History of Documents
by Lisa Gitelman · 26 Mar 2014
Free Speech: Ten Principles for a Connected World
by Timothy Garton Ash · 23 May 2016 · 743pp · 201,651 words
Doing Time Like a Spy
by John Kiriakou · 11 May 2017 · 299pp · 96,608 words