web application
description: application that uses a web browser as a client
364 results
Learning Vue.js 2: Learn How to Build Amazing and Complex Reactive Web Applications Easily With Vue.js
by Olga Filipova · 13 Dec 2016 · 292pp · 66,588 words
a guru of frameworks and languages in the vast ocean of web technologies, this book might show you something new in the world of reactive web applications. If you are a Vue developer and have used Vue 1.0, this book might be a useful guide for you to migrate to Vue
…
we will do our best to address the problem. Chapter 1. Going Shopping with Vue.js "Vue.js is a JavaScript framework for building astonishing web applications. Vue.js is a JavaScript library for creating web interfaces. Vue.js is a tool that leverages the use of MVVM architecture." Simplified JavaScript Jargon
…
Vue.js is a progressive JavaScript framework: So what is Vue.js after all? Framework? Tool? Library? Should it be used for building full-stack web applications or just for adding some special functionality? Should I switch from my favorite framework to it? If yes, why? Can I use it alongside other
…
it—just do it! Note Vue.js was born as a tool for rapid prototyping. Now it can be used to build complex scalable reactive web applications. That was what Evan did. That is how he came to the idea of creating a library that would help in rapid prototyping by offering
…
so nonopinionated of the application structuring that it definitely can be considered as a framework capable of supporting the end-to-end building of complex web applications. The most important thing about Vue.js Vue.js allows you to simply bind your data models to the representation layer. It also allows you
…
change it, rebuild, test, deploy! Happy pull requests! Debugging your Vue application You can debug your Vue application the same way you debug any other web application. Use your developer tools (firebug), breakpoints, debugger statements, and so on. If you want to dive deep inside the Chrome debugging tools, check Chrome's
…
test all the aspects of the application—APIs, frontend, backend, databases, server load, assuring thus the quality of the system integration. In the case of web applications, these tests are performed via UI testing. Each test describes all the steps from opening the browser until closing it. All the steps needed to
…
definition means that after we perform all the necessary activities, our software will be accessible to the public. In our case, as we are deploying web applications, it means that there will be a public URL, and any person will be able to type this URL on their browser and access the
…
using Vue.js. Let's revisit them. Shopping list application The shopping list application that we have developed in this book's chapters is a web application that allows the following: Create different shopping lists Add new items to the shopping lists and check them once they are bought Rename shopping lists
…
would use every time you go shopping, isn't it? The Pomodoro application The Pomodoro application that we have developed in this book is a web application that implements a Pomodoro timer with white noise during the working Pomodoros and nice pictures of cats during the interval time. It allows the following
…
opportunities is endless. Use your creativity, use Vue's power to achieve your ideas. Extending our applications to other devices Both of our applications are web applications. While it might be okay for the Pomodoro application if we work the whole day on the computer and use the Web, it might be
…
browser in the supermarket, but it might be slow and not so nice to use. Use Weex ( https://github.com/alibaba/weex ) to bring our web applications to the mobile devices. Both the applications can also be extended to be used as a Google Chrome app, just as we learned in Chapter
The Tangled Web: A Guide to Securing Modern Web Applications
by Michal Zalewski · 26 Nov 2011 · 570pp · 115,722 words
few counterparts in dedicated, compartmentalized client architectures. Nonconvergence of Visions Fortunately, the browser security landscape is not entirely hopeless, and despite limited separation between web applications, several selective security mechanisms offer rudimentary protection against the most obvious attacks. But this brings us to another characteristic that makes the Web such an
…
the ban on goto statements), JavaScript exhibits a more fundamentalist stance. Execution Ordering Control In order to properly analyze the security properties of certain common web application design patterns, it is important to understand the JavaScript engine’s execution ordering and timing model. Thankfully, this model is remarkably sane. Virtually all
…
potentially hostile document has led to a fair number of security vulnerabilities in browser plug-ins, JavaScript-based extensions, and several classes of client-side web application security features. These vulnerabilities eventually resulted in the development of browser-level workarounds designed to partially protect this specific object against sabotage, but most
…
passive media formats (and unlike some types of plug-in-rendered content!), neither <bgsound> nor HTML5 multimedia are expected to have any unusual implications for web application security, as long as the possibility of content misidentification is mitigated appropriately.[37] * * * [37] But some far-fetched interactions between various technologies are a
…
xmlns namespace. Firefox uses XUL for much of its internal UI, but otherwise the language is seldom encountered on the Internet. From the standpoint of web application security, Internet-originating XUL documents can be considered roughly equivalent to HTML documents. Essentially, the language has JavaScript scripting capabilities and allows broad control
…
DOM of the embedding page. This last functionality is implemented by injecting eval(...)-like statements into the target JavaScript context. ActionScript offers fertile ground for web application vulnerabilities. For example, the getURL(...) and navigateToURL(...) functions, used to navigate the browser or open new windows, are sometimes invoked with attacker-controlled inputs.
…
most egregious mistakes were cautiously reverted in the past decade, two companies—Microsoft and Apple—largely resisted the effort. They decided that interoperability with broken web applications should trump the obvious security problems. To pacify any detractors, they implemented a couple of imperfect, secondary security mechanisms intended to mitigate the risk.
…
stretched thin between addressing comparatively more serious implementation-level flaws in the notoriously buggy browser codebases and rolling out new, shiny security features that appease web application developers, users, and the mainstream press alike. Denial-of-Service Attacks The possibility of an attacker crashing a browser or otherwise rendering it inoperable
…
Use Restrictions Window-related woes aside, all web-originating scripts can open certain browser- or OS-handled dialogs. The usefulness of these dialogs to modern web applications is minimal, but they still constitute another interesting part of the browser security landscape. Dialog-initiating APIs include window.alert(...), used to display simple
…
browsers and outright impossible to have in Internet Explorer. Other Developments The security features discussed previously in this chapter aim to shift the boundaries between web applications and change the way sites interact with each other. Another group of proposed mechanisms escapes this simple classification yet is important or mature enough
…
terms; nomenclature such as improper restriction of operations within the bounds of a memory buffer (Common Weakness Enumeration) or insecure direct object references (Open Web Application Security Project) finds no place in a reasonable conversation—and rightly so. Nevertheless, the industry has come up with a handful of reasonably precise phrases
…
Cache poisoning The possibility of long-term pollution of the browser cache (or any interim proxies) with a fabricated, malicious version of the targeted web application. Encrypted web applications may be targeted due to response-splitting vulnerabilities. For nonencrypted traffic, active network attackers may be able to modify the responses received by the requestor
…
byte order marks (BOM), Character Set Handling C cache manifests, URL- and Protocol-Level Proposals cache poisoning, Access to Internal Networks, Vulnerabilities Specific to Web Applications Cache-Control directive, Resolution of Duplicate or Conflicting Headers, Caching Behavior cache. See browser cache, Resolution of Duplicate or Conflicting Headers, Caching Behavior caching behavior
…
, Character Set Handling, Character Set Inheritance and Override, Character Set Inheritance and Override, Markup-Controlled Charset on Subresources, Problems to Keep in Mind in Web Application Design byte order marks and detection, Character Set Handling detection for non-HTTP files, Markup-Controlled Charset on Subresources for headers, Semicolon-Delimited Header Values
…
Text inheritance and override, Character Set Inheritance and Override markup-controlled, on subresources, Character Set Inheritance and Override sniffing, Problems to Keep in Mind in Web Application Design characters, Fragment ID, Putting It All Together Again, Putting It All Together Again, Reserved Characters and Percent Encoding, Reserved Characters and Percent Encoding,
…
transfers, Keepalive Sessions click() method, Pop-Up Filtering clickjacking, Unsolicited Framing, Beyond the Threat of a Single Click, Problems to Keep in Mind in Web Application Design client certificates, Protocol-Level Encryption and Client Certificates client-server architecture, The Breakdown of the Client-Server Divide client-side data, Origin Inheritance client
…
of, Primary CSP Directives violations, Policy Violations content sniffing, Content Recognition Mechanisms, Downloaded Files and Other Non-HTTP Content, Problems to Keep in Mind in Web Application Design Content-Disposition directive, Resolution of Duplicate or Conflicting Headers, Header Character Set and Encoding Schemes, Error-Handling Rules, Type-Specific Content Inclusion, Scalable
…
, The Unusual Danger of “localhost” and same-origin policy, Security Policy for Cookies deleting, HTTP Cookie Semantics forcing, Problems to Keep in Mind in Web Application Design limitations on third-party, Prohibited Ports security policy for, Security Policy for Cookies semantics, Caching Behavior user data in, Error-Handling Rules CORS. See
…
Domain Content Inclusion cross-site request forgery (XSRF, CSRF), Type-Specific Content Inclusion, postMessage(...), Access to Internal Networks, Access to Internal Networks, Vulnerabilities Specific to Web Applications exploitation of flaws, Access to Internal Networks login forms and, postMessage(...) cross-site script inclusion (XSSI), Impact on Potential Uses of the Language, Vulnerabilities Specific
…
to Web Applications cross-site scripting (XSS), Basic Concepts Behind HTML Documents, Access to Internal Networks, Form-Based Password Managers, In-Browser HTML Sanitizers, XSS Filtering, Vulnerabilities
…
Specific to Web Applications bugs, and password managers, Form-Based Password Managers exploitation of flaws, Access to Internal Networks filtering, In-Browser HTML Sanitizers, XSS Filtering crossdomain.xml file
…
Other Developments, XSS Filtering CSRF (cross-site request forgery), Type-Specific Content Inclusion, postMessage(...), Access to Internal Networks, Access to Internal Networks, Vulnerabilities Specific to Web Applications exploitation of flaws, Access to Internal Networks login forms and, postMessage(...) CSS. See Cascading Style Sheets (CSS), Problems with Domain Restrictions CUPS (Common UNIX Printing
…
delimiting characters, in URLs, Fragment ID denial-of-service (DoS) attacks, Dealing with Rogue Scripts, Strict Transport Security, Problems to Keep in Mind in Web Application Design DeviceOrientation API, Content-Level Features dialog use restrictions, Pop-Up Filtering digest credential-passing method, HTTP Authentication Digital Rights Management (DRM), Document Rendering Helpers
…
cross-domain communications, Frame Hijacking Risks frame-ancestors directive, Primary CSP Directives frame-src directive, Primary CSP Directives framebusting, Problems to Keep in Mind in Web Application Design frames, Frames, Life Outside Same-Origin Rules, Changing the Location of Existing Documents, Changing the Location of Existing Documents, Frame Descendant Policy and
…
of JavaScript HDP file format, Type-Specific Content Inclusion HEAD request (HTTP), HEAD header injection, Newline Handling Quirks, Current Status of CORS, Vulnerabilities Specific to Web Applications headers, Basic Syntax of HTTP Traffic, Proxy Requests, Resolution of Duplicate or Conflicting Headers, Semicolon-Delimited Header Values, Semicolon-Delimited Header Values, Content Security
…
Behavior, HTTP Cookie Semantics, Document Parsing Modes, Entity Encoding, Content Recognition Mechanisms, Connection Limits, URL- and Protocol-Level Proposals, Problems to Keep in Mind in Web Application Design authentication, HTTP Cookie Semantics basic syntax, Hypertext Transfer Protocol binary, URL- and Protocol-Level Proposals caching behavior, Chunked Data Transfers cookie semantics, Caching Behavior
…
downgrade, Problems to Keep in Mind in Web Application Design history, Hypertext Transfer Protocol HTML integration semantics, Entity Encoding newline handling, Newline Handling Quirks proxy requests, Proxy Requests request types, HTTP Request Types semantics
…
conditionals, in HTML, Interactions Between Multiple Tags IndexedDB design, Content-Level Features indicator of hierarchical URLs, Scheme Name information security, Security in the World of Web Applications inheritance, for vbscript: scheme, Inheritance for data: URLs inline-script setting, Content Security Policy innerHTML property, The Document Object Model innerStaticHTML API, In-Browser
…
Character Encoding Lessig, Lawrence, Prohibited Ports LF (newline), HTTP quirks in handling, Newline Handling Quirks LFI (local file inclusion), Problems to Keep in Mind in Web Application Design Lie, Wium, Håkon, Cascading Style Sheets LiveScript, Browser-Side Scripts livescript: scheme, Protocols Claimed by Third-Party Applications and Plug-ins loadPolicyFile() method,
…
Markup-Level Security Controls local file inclusion (LFI), Problems to Keep in Mind in Web Application Design local files, access issues, Hostnames with Extra Periods local intranet zone, for Internet Explorer, Form-Based Password Managers local machine zone, for Internet Explorer
…
Forms, and Navigation Mitchell, John C., Frame Descendant Policy and Cross-Domain Communications, XDomainRequest mixed content, A Note on Cross-Origin Subresources, Vulnerabilities Specific to Web Applications mmst: scheme, Common URL Schemes and Their Function mmsu: scheme, Common URL Schemes and Their Function Mocha language, Browser-Side Scripts mocha: scheme, Protocols Claimed
…
Isolation Logic cookie specification, Problems with Domain Restrictions Netscape Navigator, The First Browser Wars: 1995 to 1999 network fenceposts, Problems to Keep in Mind in Web Application Design networking, HTTP-less, URL- and Protocol-Level Proposals New York Times, Limitations on Third-Party Cookies newline, HTTP quirks in handling, Newline Handling
…
document, Privacy-Related Side Channels onmousemove events, Window-Positioning and Appearance Problems opacity property (CSS2), and JavaScript code, Unsolicited Framing open redirection, Vulnerabilities Specific to Web Applications opener.window.focus() function, Connection Limits OpenGL-based 3D graphics, Plug-in-Based Application Frameworks Opera, Tales of the Stone Age: 1945 to 1994,
…
permissions to examine payload, Content Recognition Mechanisms on HTTP, Resolution of Duplicate or Conflicting Headers RFI (remote file inclusion), Problems to Keep in Mind in Web Application Design rgb(...) pseudo functions (CSS), Basic CSS Syntax Riley, Chris John, Unrecognized Content Type Rios, Billy, Invoking a Plug-in risk management, Enter Risk
…
, Mark of the Web and Zone.Identifier, XSS Filtering, XSS Filtering, XSS Filtering, XSS Filtering, XSS Filtering, XSS Filtering, XSS Filtering, XSS Filtering building web applications on internal networks, Limitations on Third-Party Cookies Content Security Policy (CSP), XSS Filtering converting HTML to plaintext, A Note on Cross-Site Request Forgery
…
modes, XSS Filtering putting attacker-controlled values into CSS, Character Encoding relying on HTTP cookies for authentication, Other Uses of Origins requesting elevated permissions within web application, Mark of the Web and Zone.Identifier sandboxed frames, XSS Filtering security hygiene for all websites, Other SOP Loopholes and Their Uses security policy
…
Type-Specific Content Inclusion web 2.0, The Boring Period: 2000 to 2003 web applications, Vulnerabilities Specific to Web Applications, Vulnerabilities Specific to Web Applications, Problems to Keep in Mind in Web Application Design design issues, Vulnerabilities Specific to Web Applications vulnerabilities specific to, Vulnerabilities Specific to Web Applications Web Hypertext Application Technology Working Group (WHATWG), Web 2.0 and the Second
…
Cross-Domain Policy Files XSRF (cross-site request forgery), Type-Specific Content Inclusion, postMessage(...), Access to Internal Networks, Access to Internal Networks, Vulnerabilities Specific to Web Applications exploitation of flaws, Access to Internal Networks login forms and, postMessage(...) XSS (cross-site scripting), Basic Concepts Behind HTML Documents, Access to Internal Networks, Form
…
-Based Password Managers, In-Browser HTML Sanitizers, XSS Filtering, Vulnerabilities Specific to Web Applications bugs, and password managers, Form-Based Password Managers exploitation of flaws, Access to Internal Networks filtering, In-Browser HTML Sanitizers, XSS Filtering XUL (XML User
Developing Web Applications with Haskell and Yesod
by Michael Snoyman · 22 Apr 2012 · 485pp · 74,211 words
Developing Web Applications with Haskell and Yesod Michael Snoyman Editor Simon St. Laurent Copyright © 2012 Michael Snoyman O’Reilly books may be purchased for educational, business, or sales
…
-9938 or corporate@oreilly.com. Nutshell Handbook, the Nutshell Handbook logo, and the O’Reilly logo are registered trademarks of O’Reilly Media, Inc. Developing Web Applications with Haskell and Yesod, the rhinoceros beetle, the mountain apollo butterfly, and related trade dress are trademarks of O’Reilly Media, Inc. Many of the
…
’s fair to say that dynamic languages currently dominate the web development scene. Ruby, Python, and PHP are common choices for quickly creating a powerful web application. They give a much faster and more comfortable development setting than standard static languages in the C family, like Java. But some of us are
…
Yesod. The first group is long time Haskell users—already convinced of the advantages of Haskell—who are looking for a powerful framework for creating web applications. The second is web developers who are either dissatisfied with their existing tools, or are looking to expand their horizons into the functional world. This
…
’s documentation does require permission. We appreciate, but do not require, attribution. An attribution usually includes the title, author, publisher, and ISBN. For example: “Developing Web Applications with Haskell and Yesod by Michael Snoyman (O’Reilly). Copyright 2012 Michael Snoyman, 978-1-449-31697-6.” If you feel your use of code
…
solve some of the lingering difficulties of security threats, the stateless nature of HTTP, the multiple languages (HTML, CSS, JavaScript) necessary to create a powerful web application, and more. Yesod attempts to ease the web development process by playing to the strengths of the Haskell programming language. Haskell’s strong compile-time
…
a high-level definition and remain blissfully ignorant of the details. Concise We all know that there is a lot of boilerplate coding involved in web applications. Wherever possible, Yesod tries to use Haskell’s features to save your fingers the work: The forms library reduces the amount of code used for
…
flagship web server, Warp, is the fastest Haskell web server around. When these two pieces of technology are combined, it produces one of the fastest web application deployment solutions available. Modular Yesod has spawned the creation of dozens of packages, most of which are usable in a context outside of Yesod itself
…
). One of the features of Yesod is that you aren’t tied down to a single deployment strategy. Yesod is built on top of the Web Application Interface (WAI), allowing it to run on FastCGI, SCGI, Warp, or even as a desktop application using the Webkit library. We’ll discuss some of
…
file server in a number of production environments. Resources and Type-Safe URLs In our hello world, we defined just a single resource (HomeR). A web application is usually much more exciting with more than one page on it. Let’s take a look: {-# LANGUAGE TypeFamilies, QuasiQuotes, MultiParamTypeClasses, TemplateHaskell, OverloadedStrings #-} import Yesod
…
of syntactic sugar: the doctype statement. We have support for a number of different versions of a doctype, though we recommend $doctype 5 for modern web applications, which generates <!DOCTYPE html>. $doctype 5 <html> <head> <title>Hamlet is Awesome <body> <p>All done. Note There is an older and still supported syntax
…
to the POST parameters, you should use runRequest. If you need even more raw data, like request headers, you can use waiRequest to access the Web Application Interface (WAI) request value. See the WAI appendix for more details. Short Circuiting The following functions immediately end execution of a handler function and return
…
hinted at a number of more complex Yesod topics that we will be covering later. But you should be able to write some very sophisticated web applications with just the knowledge you have learned up until here. Chapter 8. Forms I’ve mentioned the boundary issue already: whenever data enters or leaves
…
one way we bypass the statelessness imposed by HTTP. We shouldn’t consider this an escape hatch to perform whatever actions we want: statelessness in web applications is a virtue, and we should respect it whenever possible. However, there are specific cases where it is vital to retain some state. The session
…
a sum type intended for representing arbitrary data: PersistValue: newtype Key entity = Key PersistValue But this has another problem. Let’s say we have a web application that takes an ID as a parameter from the user. It will need to receive that parameter as Text and then try to convert it
…
a simple combination to build your executable is: cabal clean && cabal configure && cabal build Warp As we have mentioned before, Yesod is built on the Web Application Interface (WAI), allowing it to run on any WAI backend. At the time of writing, the following backends are available: Warp FastCGI SCGI CGI Webkit
…
max; } } Server Process Many people are familiar with an Apache/mod_php or Lighttpd/FastCGI kind of setup, where the web server automatically spawns the web application. With nginx, either for reverse proxying or FastCGI, this is not the case: you are responsible for running your own process. I strongly recommend a
…
Representational State Transfer, also known as REST. This chapter describes the RESTful features in Yesod and how you can use them to create more robust web applications. Request Methods In many web frameworks, you write one handler function per resource. In Yesod, the default is to have a separate handler function for
…
> </tr> </table> or we could represent it as JSON: {"name":"Michael","age":25} or as XML: <person> <name>Michael</name> <age>25</age> </person> Oftentimes, web applications will use a different URL to get each of these representations; perhaps /person/michael.html, /person/michael.json, etc. Yesod follows the RESTful principle of
…
can of course extend this to work with XML, Atom feeds, or even binary representations of the data. A fun exercise could be writing a web application that serves data simply using the default Show instances of data types, and then writing a web client that parses the results using the default
…
start off by buffering our source. This buffered source is then used twice in our function, and then passed off to the application. Appendix C. Web Application Interface It is a problem almost every language used for web development has dealt with: the low-level interface between the web server and the
Flask Web Development: Developing Web Applications With Python
by Miguel Grinberg · 12 May 2014 · 420pp · 61,808 words
freedom is that Flask was designed from the start to be extended. It comes with a robust core that includes the basic functionality that all web applications need and expects the rest to be provided by some of the many third-party extensions in the ecosystem and, of course, by you. In
…
this book I present my workflow for developing web applications with Flask. I don’t claim to have the only true way to build applications with this framework. You should take my choices as recommendations
…
, you will spend a great deal of time in the command line. You should feel comfortable using the command line of your operating system. Modern web applications cannot avoid the use of HTML, CSS, and JavaScript. The example application that is developed throughout the book obviously makes use of these, but the
…
this book with the official Flask documentation. How This Book Is Organized This book is divided into three parts: Part I, explores the basics of web application development with the Flask framework and some of its extensions: Chapter 1 describes the installation and setup of the Flask framework. Chapter 2 dives straight
…
no native support in Flask for accessing databases, validating web forms, authenticating users, or other high-level tasks. These and many other key services most web applications need are available through extensions that integrate with the core packages. As a developer, you have the power to cherry-pick the extensions that work
…
: (venv) $ python >>> import flask >>> If no errors appear, you can congratulate yourself: you are ready for the next chapter, where you will write your first web application. Chapter 2. Basic Application Structure In this chapter, you will learn about the different parts of a Flask application. You will also write and run
…
your first Flask web application. Initialization All Flask applications must create an application instance. The web server passes all requests it receives from clients to this object for handling, using
…
will learn about production web servers in Chapter 17. A Complete Application In the previous sections, you learned about the different parts of a Flask web application, and now it is time to write one. The entire hello.py application script is nothing more than the three parts described earlier combined in
…
routes. The function will add any extra arguments to the query string. For example, url_for('index', page=2) would return /?page=2. Static Files Web applications are not made of Python code and templates alone. Most applications also use static files such as images, JavaScript source files, and CSS that are
…
checkout 3d to check out this version of the application. Localization of Dates and Times with Flask-Moment Handling of dates and times in a web application is not a trivial problem when users work in different parts of the world. The server needs uniform time units that are independent of the
…
cases is not the desired action. Many users do not understand the warning from the browser. For this reason, it is considered good practice for web applications to never leave a POST request as a last request sent by the browser. This practice can be achieved by responding to POST requests with
…
application data in an organized way. The application then issues queries to retrieve specific portions as they are needed. The most commonly used databases for web applications are those based on the relational model, also called SQL databases in reference to the Structured Query Language they use. But in recent years document
…
_email() function can be sent to a Celery task queue. This chapter completes the overview of the features that are a must-have for most web applications. The problem now is that the hello.py script is starting to get large and that makes it harder to work with. In the next
…
chapter, you will learn how to structure a larger application. Chapter 7. Large Application Structure Although having small web applications stored in a single script can be very convenient, this approach does not scale well. As the application grows in complexity, working with a single
…
db upgrade Believe it or not, you have reached the end of Part I. You now have learned the basic elements necessary to build a web application with Flask, but you probably feel unsure about how all these pieces fit together to form a real application. The goal of Part II is
…
Flask-Bootstrap: HTML templates Flask-WTF: Web forms Password Security The safety of user information stored in databases is often overlooked during the design of web applications. If an attacker is able to break into your server and access your user database, then you risk the security of your users, and the
…
the next chapter, the user subsystem of Flasky will be extended through the use of user roles. Chapter 9. User Roles Not all users of web applications are created equal. In most applications, a small percentage of users are trusted with extra powers to help keep the application running smoothly. Administrators are
…
checkout 11h to check out this version of the application. Figure 11-4. Edit and Permalink links in blog posts. Chapter 12. Followers Socially aware web applications allow users to connect with other users. Applications call these relationships followers, friends, contacts, connections, or buddies, but the feature is the same regardless of
…
as an API that clients other than web browsers can use. Chapter 14. Application Programming Interfaces In recent years, there has been a trend in web applications to move more and more of the business logic to the client side, producing an architecture that is known as Rich Internet Application (RIA). In
…
Object Access Protocol (SOAP) were popular choices a few years ago. More recently, the Representational State Transfer (REST) architecture has emerged as the favorite for web applications due to it being built on the familiar model of the World Wide Web. Flask is an ideal framework to build RESTful web services due
…
discover new web pages while browsing the Web by clicking on links that appear in pages that you know. Versioning In a traditional server-centric web application, the server has full control of the application. When an application is updated, installing the new version in the server is enough to update all
…
the app stores to coincide exactly with the deployment of the new server. For these reasons, web services need to be more tolerant than regular web applications and be able to work with old versions of its clients. A common way to address this problem is to version the URLs handled by
…
Now view functions in the web service can invoke these auxiliary functions to generate error responses. User Authentication with Flask-HTTPAuth Web services, like regular web applications, need to protect information and ensure that it is not given to unauthorized parties. For this reason, RIAs must ask their users for login credentials
…
url_for() calls so that fully qualified URLs are returned instead of the relative URLs that are typically used within the context of a traditional web application. This example also shows how it is possible to return “made-up” attributes in the representation of a resource. The comment_count field returns the
…
> GET A comment Note that the resources that were implemented enable a client to offer a subset of the functionality that is available through the web application. The list of supported resources could be expanded if necessary, such as to expose followers, to enable comment moderation, and to implement any other features
…
Large Resource Collections The GET requests that return a collection of resources can be extremely expensive and difficult to manage for very large collections. Like web applications, web services can choose to paginate collections. Example 14-21 shows a possible implementation of pagination for the list of blog posts. Example 14-21
…
which responses are generated and returned. After a view function executes, its response is passed to the test, which can check it for correctness. Testing Web Applications Example 15-2 shows a unit testing framework that uses the test client. Example 15-2. tests/test_client.py: Framework for tests using the
…
frustrate users, so it is important to detect and correct performance problems as soon as they appear. In this chapter, two important performance aspects of web applications are considered. Logging Slow Database Performance When application performance slowly degenerates with time, it is likely due to slow database queries, which get worse as
…
, Setting Up Logging T testing, Testing Web Services with HTTPie , Obtaining Code Coverage Reports unit tests, Unit Tests , Hashing Passwords with Werkzeug , Role Verification web applications, Testing Web Applications web services, Testing Web Services Twitter Bootstrap, Twitter Bootstrap Integration with Flask-Bootstrap U unittest, Unit Tests URL fragment, Comment Submission and Display user roles
The Web Application Hacker's Handbook: Finding and Exploiting Security Flaws
by Dafydd Stuttard and Marcus Pinto · 30 Sep 2007 · 1,302pp · 289,469 words
I've been getting into computers ever since. vii Contents at a Glance viii Contents Introduction xxiii Chapter 1 Web Application (In)security 1 The Evolution of Web Applications 2 Common Web Application Functions 4 Benefits of Web Applications 5 Web Application Security 6 "This Site Is Secure" 7 The Core Security Problem: Users Can Submit Arbitrary Input 9 Key
…
Configuration 851 13 Follow Up Any Information Leakage 852 Index 853 Introduction This book is a practical guide to discovering and exploiting security flaws in web applications. By "web applications" we mean those that are accessed using a web browser to communicate with a web server. We examine a wide variety of different technologies
…
Java applets, ActiveX controls, Silverlight, and Flash objects. xxvi Introduction Chapters 6, 7, and 8 cover some of the most important defense mechanisms implemented within web applications: those responsible for controlling user access. Chapter 6, "Attacking Authentication," examines the various functions by which applications gain assurance of their users' identity. This
…
"Automating Customized Attacks," does not introduce any new categories of vulnerabilities. Instead, it describes a crucial technique you need to master to attack web applications effectively. Because every web application is different, most attacks are customized in some way, tailored to the application's specific behavior and the ways you have discovered to manipulate
…
information, carry out financial fraud, and perform malicious actions against other users. 4 Chapter 1 Web Application (In)security Common Web Application Functions Web applications have been created to perform practically every useful function you could possibly implement online. Here are some web application functions that have risen to prominence in recent years: ■ Shopping (Amazon) ■ Social networking (
…
Application functions and data typically are shared between the various interfaces that the application exposes to different user platforms. In addition to the public Internet, web applications have been widely adopted inside organizations to support key business functions. Many of these provide access to highly sensitive data and functionality: ■ HR applications
…
, and tracking issues. These types of functionality often involve critical security and governance issues, and organizations often rely completely on the controls built into their web applications. ■ Business applications such as enterprise resource planning (ERP) software, which previously were accessed using a proprietary thick-client application, can now be accessed using
…
grasp of the essentials of securing networks and hardening hosts, widespread confusion and misconception still exist about many of the core concepts involved in web application security. A web application developer's work increasingly involves weaving together tens, or even hundreds, of third-party packages, all designed to abstract the developer away from
…
browser. This data sails past all the organization's network defenses, in the same way as does ordinary, benign traffic to the web application. The effect of widespread deployment of web applications is that the security perimeter of a typical organization has moved. Part of that perimeter is still embodied in firewalls and bastion
…
information sharing, and also the adoption of various technologies that broadly support this functionality, including asynchronous HTTP requests and cross-domain integration. Chapter 1 i Web Application (ln)security 15 ■ Cloud computing — This term refers to greater use of external service providers for various parts of the technology stack, including application
…
items were deleted, return to step 1. Can you bypass this validation mechanism to smuggle the following data past it? "><script>alert("foo")</script> Web Application Technologies Web applications employ a myriad of technologies to implement their functionality This chapter is a short primer on the key technologies that you are likely to encounter
…
approach. Here are some examples of components commonly used for key application functions: ■ Authentication — JAAS, ACEGI ■ Presentation layer — SiteMesh, Tapestry 54 Chapter 5 i Web Application Technologies ■ Database object relational mapping — Hibernate ■ Logging — Log4J If you can determine which open source packages are used in the application you are attacking, you
…
for common application functions, which are often incorporated into wider custom-built applications: ■ Bulletin boards — PHPBB, PHP-Nuke ■ Administrative front ends — PHPMyAdmin Chapter 3 i Web Application Technologies 55 ■ Web mail — SquirrelMail, IlohaMail ■ Photo galleries — Gallery ■ Shopping carts — osCommerce, ECW-Shop ■ Wikis — MediaWiki, WakkaWikki Because PHP is free and easy to
…
"> <Account> <FromAccount>18281008</FromAccount> <Amount>1430</Amount> <C1earedFunds >False</ClearedFunds > <ToAccount>08447656</ToAccount> </Account> </pre:Add> </soap:Body> </soap:Envelope> In the context of web applications accessed using a browser, you are most likely to encounter SOAP being used by the server-side application to communicate with various back-end systems
…
of output data, the output is padded with one or two = characters. For example, here is the Base64-encoded form of The Web Application Hacker's Handbook: VGhlIFdlYiBBcHBsaWNhdGlvbiBIYWNrZXIncyBIYW5kYm9vaw== Many web applications use Base64 encoding to transmit binary data within cookies and other parameters, and even to obfuscate (that is, to hide) sensitive data to
…
you attack them. For example, sample and diagnostic scripts may contain known vulnerabilities or functionality that may be leveraged for a malicious purpose. Furthermore, many web applications incorporate common third-party components for standard functionality, such as shopping carts, discussion forums, or content management system (CMS) functions. These are often installed
…
. home TransferFunds. selectAccounts BillPayment. addPayee TransferFunds. enterAmount TransferFunds. confirmTransfer BillPayment. selectPayee WahhBank. logout Figure 4-10: A mapping of the functional paths within a web application Representing an application's functionality in this way is often more useful even in cases where the usual picture based on application pages can be
…
cfide — Cold Fusion ■ silverstream — The SilverStream web server ■ WebObjects or {function} .woa — Apple WebObjects ■ rails — Ruby on Rails Session Tokens Many web servers and web application platforms generate session tokens by default with names that provide information about the technology in use. For example: ■ jsessionid — The Java Platform ■ aspsessionid — Microsoft IIS
…
server ■ asp . NET_sessionid — Microsoft ASP.NET ■ cfid/cftoken —ColdFusion ■ PHPSESSID — PHP Third-Party Code Components Many web applications incorporate third-party code components to implement common functionality such as shopping carts, login mechanisms, and message boards. These may be open source or may
…
force ■ Integrating with a smartcard reader Typically, these kinds of actions require the use of native code components, which integrate local application functionality with web application functionality Native client components are often delivered via ActiveX controls. These are custom browser extensions that run outside the browser sandbox. Native client components may
…
the other available technologies. Design Flaws in Authentication Mechanisms Authentication functionality is subject to more design weaknesses than any other security mechanism commonly employed in web applications. Even in the apparently simple, standard model where an application authenticates users based on their username and password, shortcomings in the design of this
…
change functionality is often vulnerable by design. Vulnerabilities that are deliberately avoided in the main login function often reappear in the password change function. Many web applications' password change functions are accessible without authentication and do the following: ■ Provide a verbose error message indicating whether the requested user-name is valid. ■
…
large number of sessions being created each second, a scripted attack may succeed in identifying large numbers of other users' tokens. When testing the web application of an online retailer, the authors encountered the following sequence of session tokens: 3124538-1172764258718 3124539-1172764259062 3124540-1172764259281 3124541-1172764259734 3124542-1172764260046 3124543-1172764260156
…
those requests using the standard methodology already described, using accounts with lower privileges. Securing Access Controls Access controls are one of the easiest areas of web application security to understand, although you must carefully apply a well-informed, thorough methodology when implementing them. First, you should avoid several obvious pitfalls. These
…
overflow vulnerabilities. Chapter 16 Attacking Native Compiled Applications 645 Summary Software vulnerabilities in native code represent a relatively niche area in relation to attacks on web applications. Most applications run in a managed execution environment in which the classic software flaws described in this chapter do not arise. However, occasionally these
…
chapter examines a range of different architectural configurations and describes how you can exploit defects within application architectures to advance your attack. Tiered Architectures Most web applications use a multitiered architecture, in which the application's user interface, business logic, and data storage are divided between multiple layers, which may use
…
, for any vulnerability you identify within the application, think imaginatively about how this can be exploited to achieve your objectives. Countless successful hacks against web applications begin from a vulnerability that is intrinsically limited in its impact. By exploiting trust relationships and undercutting controls implemented elsewhere within the application, it may
…
vulnerable or malicious component to compromise the wider application. Particular attention should be paid to shared logging and administrative functions. Summary Security controls implemented within web application architectures present a range of opportunities for application owners to enhance the overall security posture of their deployment. As a consequence, defects and oversights
…
the typical pitfalls awaiting any application implementing its own native extensions, modules, or APIs, or reaching outside the application container. This chapter also examines web application firewalls, describes their strengths and weaknesses, and details ways in which they can often be circumvented to deliver attacks. Vulnerable Server Configuration Even the simplest
…
nextlnt(); return 1 + (m « 32); } } Are the application's session tokens being generated in a predictable way? Explain your answer fully. A Web Application Hacker's Toolkit Some attacks on web applications can be performed using only a standard web browser; however, the majority of them require you to use some additional tools. Many
…
a number of highly functional tool suites, each containing several interconnected tools designed to facilitate the common tasks involved in attacking a web application. Several testing suites are commonly used by web application security testers: ■ Burp Suite ■ WebScarab ■ Paros ■ Zed Attack Proxy ■ Andiparos ■ Fiddler . CAT ■i Charles These toolkits differ widely in their
…
all relevant details about the target application and providing numerous useful functions. The typical suite contains the following core components: ■ An intercepting proxy ■ A web application spider ■ A customizable web application fuzzer ■ A vulnerability scanner ■ A manual request tool ■ Functions for analyzing session cookies and other tokens ■ Various shared functions and utilities Intercepting Proxies
…
6: The proxy history, allowing you to view, filter, search, and annotate requests and responses made via the proxy 760 Chapter 20 A Web Application Hacker's Toolkit Web Application Spiders Web application spiders work much like traditional web spiders. They request web pages, parse them for links to other pages, and then request those pages
…
barriers can be effectively addressed only by systems with full-blown artificial intelligence engines, going far beyond the capabilities of today's scanners. Every Web Application Is Different Web applications differ starkly from the domain of networks and infrastructures, in which a typical installation employs off-the-shelf products in more or less standard
…
the desired state to handle a particular attack request. Chapter 14 describes techniques for achieving this within custom automated attacks. They generally Chapter 20 A Web Application Hacker's Toolkit 781 require intelligent human involvement to understand the requirements, configure the testing tools appropriately, and monitor their performance. Current Products The
…
affect different applications in different ways, depending on the types of functionality and vulnerabilities they contain. Of the various kinds of vulnerabilities commonly found within web applications, automated scanners are inherently capable of discovering approximately half of these, where a standard signature exists. Within the subset of vulnerability types that scanners
…
response being received from the server ■ The TCP connection to the server closing abruptly without returning a response 858 Chapter 21 ■ A Web Application Hacker's Methodology ■ The entire web application no longer responding ■ Unexpected data being returned by the application, possibly indicating that a string in memory has lost its null terminator 8
…
sockets, 732 URL redirection, 731-732 server-side redirection, 392 SQL injection, 291 versatility, 358 Apple iDisk Server, path traversal vulnerabilities, 690 application. See web application application architecture. See tiered architectures application logic flaws access controls vulnerabilities, 411 attack surface, 405 audit trail, 429 authentication, 415-416 avoiding, 428-429 beating
…
114 naming schemes, 85-86 brute-force exercise, 88 identifying, 87 path traversal vulnerabilities, 371 server-side functionality identification, 106-110 technology identification, 101-106 web application pages versus functional paths, 93-96 application servers. See web servers application service providers (ASPs), 656-657. See also ASP NET; cloud computing attackers, 658
…
106-110 ASP.NET, 54,103 dissecting requests, 107-108 Java, 53-54 PHP, 54-55 Ruby on Rails, 55 SQL, 55-56 web application behavior extrapolation, 109-110 web application behavior isolation, 110 web services, 56-57 XML, 56 HTTP redirection, 390-392 exploiting, 391-392 technologies application mapping identifying, 101-106 banner
Building Web Applications With Flask
by Italo Maia · 25 Jun 2015 · 157pp · 35,874 words
Table of Contents Building Web Applications with Flask Credits About the Author About the Reviewers www.PacktPub.com Support files, eBooks, discount offers, and more Why subscribe? Free access for Packt
…
ex Placing your code in a server Setting up your database Setting up the web server StackOverflow Structuring your projects Summary Postscript Index Building Web Applications with Flask * * * Building Web Applications with Flask Copyright © 2015 Packt Publishing All rights reserved. No part of this book may be reproduced, stored in a retrieval system, or
…
and recipes for quick prototyping, he is active in the Brazilian Python communities, having open source tools and libraries available in GitHub and Bitbucket. Building Web Applications with Flask is a book written with the invaluable support of families—the Packt family, where I give special thanks to Shubhangi for her dedication
…
great guidelines such as the Zen of Python and PEP8, we have, at our disposal, a wide range of libraries and frameworks for creating great web applications, each with its own philosophy. Django, for example, is a bundle solution; it makes choices for you on how your project should look, what should
…
the chapters. Who this book is for This book targets Python developers, with some or no experience with web development, who wish to create minimalistic web applications. It is focused on those who want to become web developers as all the basics are covered to some extent, and also on those who
…
of Python, you're more than capable of understanding the examples and the chapters; at the end of the book, you will be creating amazing web applications that perform well and are easy to maintain. Conventions In this book, you will find a number of styles of text that distinguish between different
…
where is M? Flask does not provide you with an integrated model layer out-of-the-box as that is not actually needed for a web application. If you do need to work with a database, just pick your database solution from the many available and create your own model layer, which
…
model layer, although it does not restrict you in any way if you wish to create your own. If you need a simple, single-file web application that receives a form and gives back an answer, HTML or not, Flask will help you with that, easily. If you need a multilayer, high
…
Now, let's talk about awesomeness, your awesomeness after reading this book—you will be capable of handling HTTP and Ajax requests; creating fully featured web applications with database integration (SQL and NoSQL) and REST services; using Flask extensions (forms, caching, logging, debugging, auth, permissions, and so on); and modularizing and unit
…
templates. In order to create our "Hello World", we need to tell our Flask instance how to respond when a user tries to access our Web application (using a browser or whatever). For that purpose, Flask has routes. Routes are the way Flask reads a request header and decides which view should
…
to someone. We also did that. At last, we learned how to serve an HTML page and static files, which is pretty much what most Web applications do. You acquired all these skills in this chapter, and I hope the process has been quite easy but fulfilling! In the next chapter, we
…
, where True == 1. Then 5 < True is evaluated, which is certainly false. The for statement is pretty important. One can hardly think of a serious Web application that does not have to show a list of some kind at some point. The for statement can iterate over any iterable instance and has
…
block through the macro signature You can define a macro library inside a template and import only what is needed Commonly used macros in a Web application include a macro to render pagination, another to render fields, and another to render forms. You could have others, but these are pretty common use
…
chapter, we will be studying forms with Flask. Expect a lot of examples and complementary code, as forms are the doors you open from your Web application to the Web. Most problems arise from the Web, as well as most of your data. Chapter 4. Please Fill in This Form, Madam Have
…
data you wrote—comment, name, checkbox, or whatever—is encoded and sent through a protocol to the server, which then routes that information to the Web application. The Web application will validate the data origin, read the form, validate the data syntactically then semantically, and then decide what to do with it. Do you
…
input, textarea, or select element. When using input fields, always remember to name them with the attribute name as it facilitates handling them in the Web application. In the third line we have a special input field, which does not necessarily have any data to be sent, the Submit input button. By
…
form-like classes, implement fields and form validation, and include cross-source forgery protection (a nasty vulnerability that crackers may try to exploit in your Web applications). We certainly don't want that! First, to install WTForms library, use the following: pip install wtforms Now let's write some forms. A WTForms
…
to unprotect a form in the case of search fields that use the get method but are also validated with a Form. Challenges Create a Web application that receives a name and then answers: "Hello <NAME>". If the form is sent empty, an error message should be displayed. If the name given
…
is "Chuck Norris", the answer should be "Roundhouse KICK!". Create a Web application that shows an image and asks the user what he sees. The application should then validate if the answer is correct. If it is not
…
and validate our forms and how to protect our applications against CSRF attacks. In the next chapter, we'll look at how to store our Web application data in relational and non-relational databases using great, easy-to-use libraries and how to integrate them with Flask. A brief overview on databases
…
could later be lost or accessible to someone who could meddle with your "stash"? We are in the information era; information is power! In the web application world, we have two big players for data storage: relational databases and NoSQL databases. The first is the traditional way where your data is stored
…
The possibilities here are many. Why don't you try a few examples on your own now? Note The most common security problem related to web applications and databases is the SQL Injection Attack, where an attacker injects SQL instructions into your queries to the database, gaining privileges he/she should not
…
and SQLAlchemy, and how to use extensions to integrate Flask with each. Knowledge is stacking up fast! You're now capable of creating more complex web applications with database support, custom validation, CSRF protection, and user communication. In the next chapter, we'll learn about REST, its advantages, and how to create
…
, Web services and Web APIs following the REST architecture. Let's start at the beginning: what is a Web service? A Web service is a Web application that can be consulted by your application as if it was an API, improving the user experience. If your RESTful Web service does not need
…
next chapter, we'll be talking about the one way in which you can assure software quality: tests! We'll learn how to test our Web applications in the many ways that they may be tested and how to integrate these tests into our very coding routines. See you there! Chapter 7
…
cleaning the database are common ways to do that. The preceding case is common when writing scripts or desktop applications. A web application has different needs regarding the tests. A web application code usually runs in response to user interaction through a browser request and returns a response as the output. To test in
…
worry about the response HTTP code, which holds a lot of contextual meaning. To help you test your views and simulate user interaction with your web application, Flask gives you a test client tool through which you can send requests in any valid HTTP method to your application. For example, You may
…
're probably wasting time with premature optimization. And so, on to Flask. Blueprints 101 So far, our applications have all been flat: beautiful, single-file Web applications (templates and static resources not considered). In some cases, that's a nice approach; a reduced need for imports, easy to maintain with simple editors
…
counter goes up each time you reload? Well, that's the session working! Exercise How about putting our knowledge to work? Try making a shop web application, such as an online pet shop. It should have pet services, for example bathing and vet consultations, and also a small store with pet accessories
…
/), and RamNode (https://www.ramnode.com/) have whole businesses focused in providing cheap, reliable virtual machines to the public. Now, given that we have our web application ready (I mean, our Minimum Viable Product is ready), we must run the code somewhere accessible to our target audience. This usually means we need
…
to databases, one of the most basic things you should know during deployment is that it is a good practice to have your database and web application running on different (virtual) machines. You don't want them to compete for the same resources, believe me. That's why we hired two virtual
…
database mydb. We do that so that we're able to create tables, alter tables, and so on. You usually don't want your production web application database user (whoa!) to have all these privileges because, in the event of a security breach, the invader would be able to do anything to
…
your database. As one usually (coff coff never!) does not alter the database structure on user interaction, using a less privileged user with the web application is not a problem. Tip PgAdmin is an amazing, user-friendly, Postgres management application. Just use it with SSH tunneling (http://www.pgadmin.org/docs
…
recipe to quickly start a new Flask project, taking advantage of their suggested way of organizing the code. If you plan to create a large web application with Flask, you're strongly advised to take a look at at least one of these projects because they've probably already faced a few
…
-skeleton) Summary I must confess, I wrote this book for myself. It is so hard to find all the knowledge one needs to build a web application in just one place, that I had to place my notes somewhere, condensed. I hope that, if you reached this paragraph, you also feel like
Learning Node.js: A Hands-On Guide to Building Web Applications in JavaScript
by Marc Wandschneider · 18 Jun 2013
. To return to the previous page viewed, click the Back button on your device or app. Learning Node.js A Hands-On Guide to Building Web Applications in JavaScript Marc Wandschneider Upper Saddle River, NJ • Boston • Indianapolis • San Francisco New York • Toronto • Montreal • London • Munich • Paris • Madrid Cape Town • Sydney • Tokyo • Singapore
…
Modifying Your URL Scheme The JavaScript Loader/Bootstrapper Templating with Mustache Your Home Page Mustache Template Putting It All Together Summary Part III: Writing Web Applications 7 Building Web Applications with Express Installing Express Hello World in Express Routing and Layers in Express Routing Basics Updating Your Photo Album App for Routing REST API
…
Forms teams. As Contract Software Developer/Architect at SourceLabs, he built the SWiK open source Wiki platform. He authored PHP and MySQL LiveLessons and Core Web Application Development with PHP and MySQL. Introduction Welcome to Learning Node.js. Node.js is an exciting new platform for writing network and
…
web applications that has created a lot of buzz over the past couple of years and rapidly gathered a sizeable following in the developer community. In this
…
as well. Why Node.js? Node.js has arisen for a couple of primary reasons, which I explain next. The Web In the past, writing web applications was a pretty standard process. You have one or more servers on your machine that listens on a port (for example, 80 for HTTP), and
…
your scripts spend most of their time waiting for database servers to finish running a query—an extremely common scenario for a lot of modern web applications. Many solutions to this problem have been developed and are in common use. You can buy ever bigger and more powerful web servers with more
…
for the crown of browser king. As part of this, all these companies are investing heavily in the JavaScript portion of these systems as modern web applications continue to grow ever-more dynamic and script-based. In particular, Google Chrome’s V8 JavaScript runtime is particularly fast and also open-sourced for
…
use by anybody. With all these things in place, the opportunity arose for somebody to come along with a new approach to network (web) application development. Thus, the birth of Node.js. What Exactly Is Node.js? In 2009, a fellow named Ryan Dahl was working for a company called
…
Joyent, a cloud and virtualization services company in California. He was looking to develop push capabilities for web applications, similar to how Gmail does it, and found most of what he looked at not quite appropriate. He eventually settled on JavaScript because it lacked
…
that it is built entirely around an event-driven nonblocking model of programming. In short, you never (well, rarely) write code that blocks. If your web application—in order to process a request and generate a response—needs to run a database query, it runs the request and then tells Node.js
…
is centered around applications that are doing lots of different things with lots of different processes, servers, or services. Node.js truly shines when your web application is juggling connections to databases, caching servers, file systems, application servers, and more. The flip side of this, however, is that it’s actually not
…
writing your first Node.js programs with ease and a smile on your face! I also assume that you have a basic understanding of how web applications work: Browsers send HTTP requests to a remote server; the server processes that request and sends a response with a code indicating success or failure
…
3. Breaking Out the Big Guns—In this part, you look at some of the powerful tools and modules available to you for writing your web applications, such as help with web servers and communication with database servers. Part 4. Getting the Most Out of Node.js—Finally, I close out the
…
JavaScript Chances are, if you are reading this book, you have worked with JavaScript in the past. Perhaps you have worked on or written a web application that uses HTML, CSS, and JavaScript, and you have written some code to make the client more dynamic and interactive, either directly by manipulating the
…
: Infinity, citizenship: "man of the world" }; * * * About JSON One of the things used quite often in this book (and indeed in all the network and web applications) is JSON, or JavaScript Object Notation. This data exchange format gives you all the flexibility of a text-based data format, without the hassle that
…
be manipulated, extended, and passed around as data. Node.js takes advantage of this capability, and you will use it extensively in your network and web applications. Basics The simplest kind of function is exactly as you would expect: function hello(name) { console.log("hello " + name); } > hello("marc"); hello marc undefined > To
…
you work your way through this book, I hope you are able to see quite quickly that Node.js isn’t just for network or web applications. You can use it for everything from command-line utilities to prototyping to server management and more! Summary Switching from a model of programming, where
…
you have a better understanding of how the JavaScript language really works, it’s time to start unleashing the power of Node.js to write web applications. As I mentioned in the Introduction to this book, you will work on a small photo album website throughout this book. In this chapter, you
…
what changed. Receiving Form POST Data Although you won’t use this as much in your application, a lot of data sent to servers from web applications are sent via <form> elements, for example: Click here to view code image <form name='simple' method='post' action='http://localhost:8080'> Name: <input name
…
: null }) + "\n"); } ); var s = http.createServer(handle_incoming_request); s.listen(8080); } Starting in Chapter 6, however, when you learn how to use the express web application framework for Node, you’ll see that this functionality is typically all handled for you. Summary This chapter covered quite a lot of new material
…
. You wrote your first web application by writing a simple JSON server. I like this approach for a few key reasons: • It lets you focus on the server and the key
…
that all possible code paths (including errors) signal an event; otherwise, your Node program might hang. * * * Assembling Content on the Client: Templates In more traditional web application models, the client sends an HTTP request to the server, the server gathers all the data and generates the HTML response, and it sends that
…
stuff at you in the preceding sections, so stop now and make this all run. You should now have the following file layout for your web application: Click here to view code image + project_root/ server.js // GitHub source basic.html // Listing 6.1 + content/ home.js // Listing 6.2 album.js
…
in the browser Summary This chapter introduced two key Node.js features, streams and events, that you used to serve up static content from your web application. Equally importantly, this chapter introduced client-side template engines, and you used Mustache to put together a simple start to a front-end for your
…
with little code. You will do so using the Express Application Framework for Node. Part III: Writing Web Applications 7 Building Web Applications with Express 8 Databases I: NoSQL (MongoDB) 9 Databases II: SQL (MySQL) 7. Building Web Applications with Express Thus far, you have been learning the fundamentals and core concepts of Node.js; armed
…
to write a lot of code to do some reasonably basic things. It’s time to change gears a bit and start building more interesting web applications, using one of the biggest strengths of Node: the huge collection of libraries and modules available to you through npm. Now that you understand the
…
time to start finding ways to make your life significantly easier and your development much faster. In this chapter, you start working with express, a web application framework for Node. It takes care of many of the basic tasks you learned about in previous chapters, and even exposes some powerful new functionality
…
, the server.js file has left only the functions for serving static content, which you can view in the GitHub source for Chapter 7, “Building Web Applications with Express,” in the handlers_as_modules/ project folder. The application should have the same functionality as before, but is now much more modularized and
…
the little app into something more useful. 8. Databases I: NoSQL (MongoDB) Now that you have a solid foundation for your web application and are fully set up with the express web application framework and Mustache templating, you are ready to spend a couple of chapters adding a back end to it. In these
…
of the photo album application that uses MongoDB as its data store for albums and photos, but also a couple more interesting pages in your web application for creating albums and uploading photos to the server. The only problem is that anybody can view and use these pages and APIs to manipulate
…
source variants, MySQL and PostgreSQL. The good news is that the asynchronous nature of Node.js meshes perfectly well with using these databases in your web applications, and there is good npm module support for most of them. In this chapter, I cover using MySQL with Node, using the mysql module from
…
be limited to making connections to the MySQL server and executing these queries and statements. This gives you more than enough to run your straightforward web applications and extract much of the power of the database server. Connecting To connect to the remote server, you create a connection via the mysql module
…
/users.json', user_hdlr.register); app.post('/service/login', user_hdlr.login); The first is the CRUD method (see “API Design” in Chapter 7, “Building Web Applications with Express”) for creating users through the API. The second is the way you support logins and authentication for the web browser version of the
…
) { if (!err && resp) { next(); } else need_auth(req, res); } ); } else need_auth(req, res); } The code works as follows: 1. To maintain compatibility with the web application, you check to see whether the user has already logged in using sessions in the browser. If so, this user is clear to use any
…
use of a nice little program called nssm.exe (the Non-Sucking Service Manager) and an npm module called winser, you can install your Node web applications as services and manage them fully through the Windows Management Console. To set this up, you need to do two things: 1. Install a new
…
custom action in the package.json for the web application. 2. Download and install winser and have it do its work. For the first step, you just need to add the following to the package
…
servers? You can solve this problem by implementing a simple round-robin load balancer that is given a list of node servers running your particular web application. You then redirect incoming requests to your domain to these other servers, one at a time. You can, of course, experiment with more advanced strategies
…
use them effectively: The session data is currently stored per process using local MemoryStore objects (see “POST Data, Cookies, and Sessions” in Chapter 7, “Building Web Applications with Express”). This creates a rather serious problem, as shown in Figure 10.2. Figure 10.2. Multiple instances of the servers and session data
…
fetch the correct information, no matter where the request is processed. Virtual Hosting Running multiple websites on one server has been a major requirement of web application platforms for many years now, and fortunately Node.js offers a couple of very workable solutions here for you when you build your apps with
…
Server Support Although it’s cool that express has built-in support for virtual hosts, I worry a bit about the risks of having multiple web applications running within one process. If any one starts to misbehave or have problems, any number of your sites can start to have problems as well
…
almost fanatical about performance, and these components are sufficiently lightweight that they shouldn’t add much perceptible delay in the processing of requests for your web applications. Multiplatform Development One of the great strengths of Node.js is not only its strong support for UNIX and Mac-like computers, but also its
…
Node applications and run them in production environments, investing execution scripts, load balancing, and multiprocess applications. This chapter also showed you how to secure your web applications using HTTPS over SSL, and finally described multiplatform development, showing that it’s not nearly as scary as you might fear. You now have a
…
the readline object to exit the program. Working with Processes One other thing you can do from the command line (or even from within your web applications) in Node is to launch other programs. You have a couple of options for this using the child_process module, with varying degrees of complexity
…
, 183-187 paging functionality, adding, 80-82 structure of, 187 testing, 258-262 updating for routing, 141-144 Reverse Polish Notation calculator, testing, 255-258 web applications HTTP Basic Authentication, 157-158 node servers, launching, 220 PUT and DELETE, browser support for, 155-156 web browser applications, client-side templates, 121 arrays
…
-11 version of Node.js, displaying, 11 virtual hosting, 224-227 proxy server support, 227 testing, 225 VowsJS, 254 W watch command (Node debugger), 20 web applications DELETE, browser support for, 155-156 HTTP Basic Authentication, 157-158 node servers, launching, 220 PUT, browser support for, 155-156 virtual hosting, 224-227
The Everything Blueprint: The Microchip Design That Changed the World
by James Ashton · 11 May 2023 · 401pp · 113,586 words
Newton, the NC was ahead of its time. Whereas Arm had bigger opportunities to pursue, Acorn desperately needed a hit. The NC attempted to run web applications instead of installed software, but long before regular internet access was good enough to support the idea. His partners suspected Ellison lost interest early on
Money in the Metaverse: Digital Assets, Online Identities, Spatial Computing and Why Virtual Worlds Mean Real Business
by David G. W. Birch and Victoria Richardson · 28 Apr 2024 · 249pp · 74,201 words
user authentication across different applications and platforms. It simplifies the login process, enhances security and respects user privacy, making it a popular choice for modern web applications and services. OIDC also powers social logins (sign in with Facebook, Google, etc.), and we think its widespread adoption is interesting because it provides a
Rust Programming by Example
by Guillaume Gomez and Antoni Boucher · 11 Jan 2018 · 537pp · 82,938 words
know how concurrency works in Rust and use concurrency primitives such as threads and message passing Use syntax extensions and write your own Create a Web application with Rocket Use Diesel to build safe database abstractions Leave a review - let other readers know what you think Please share your thoughts on this
Exploring Everyday Things with R and Ruby
by Sau Sheong Chang · 27 Jun 2012
Programming in Scala
by Martin Odersky, Lex Spoon and Bill Venners · 15 Jan 2008 · 754pp · 48,930 words
The Decline and Fall of IBM: End of an American Icon?
by Robert X. Cringely · 1 Jun 2014 · 232pp · 71,024 words
Smart Money: How High-Stakes Financial Innovation Is Reshaping Our WorldÑFor the Better
by Andrew Palmer · 13 Apr 2015 · 280pp · 79,029 words
Data Mining in Time Series Databases
by Mark Last, Abraham Kandel and Horst Bunke · 24 Jun 2004 · 205pp · 20,452 words
Reactive Messaging Patterns With the Actor Model: Applications and Integration in Scala and Akka
by Vaughn Vernon · 16 Aug 2015
Vue.js
by Callum Macrae · 23 Feb 2018 · 296pp · 41,381 words
Functional Programming in Scala
by Paul Chiusano and Rúnar Bjarnason · 13 Sep 2014
Succeeding With AI: How to Make AI Work for Your Business
by Veljko Krunic · 29 Mar 2020
The Little Book on CoffeeScript
by Alex MacCaw · 1 Jan 2012 · 59pp · 12,801 words
Instant Ember.JS Application Development: How-To
by Marc Bodmer · 11 Feb 2013 · 48pp · 10,481 words
An Elegant Puzzle: Systems of Engineering Management
by Will Larson · 19 May 2019 · 227pp · 63,186 words
User Stories Applied: For Agile Software Development
by Mike Cohn · 1 Mar 2004 · 270pp · 75,626 words
Kill It With Fire: Manage Aging Computer Systems
by Marianne Bellotti · 17 Mar 2021 · 232pp · 71,237 words
Rapid GUI Programming With Python and Qt
by Mark Summerfield · 27 Oct 2007 · 643pp · 53,639 words
Learning Android
by Marko Gargenta · 11 Mar 2011 · 378pp · 67,804 words
Architecting For Scale
by Lee Atchison · 25 Jul 2016 · 255pp · 55,018 words

Programming Scala: tackle multicore complexity on the JVM
by Venkat Subramaniam · 1 May 2009 · 226pp · 17,533 words
MongoDB: The Definitive Guide
by Kristina Chodorow and Michael Dirolf · 23 Sep 2010 · 352pp · 64,282 words
Mastering Ember.js
by Mitchel Kelonye · 19 Oct 2014 · 266pp · 38,397 words
Essential SQLAlchemy
by Rick Copeland · 4 Jun 2008 · 357pp · 63,071 words
A Hacker's Mind: How the Powerful Bend Society's Rules, and How to Bend Them Back
by Bruce Schneier · 7 Feb 2023 · 306pp · 82,909 words
Gray Hat Python: Python Programming for Hackers and Reverse Engineers
by Justin Seitz · 15 Feb 2009 · 312pp · 52,762 words
Real World Haskell
by Bryan O'Sullivan, John Goerzen, Donald Stewart and Donald Bruce Stewart · 2 Dec 2008 · 1,065pp · 229,099 words
Team Topologies: Organizing Business and Technology Teams for Fast Flow
by Matthew Skelton and Manuel Pais · 16 Sep 2019
Simple Rules: How to Thrive in a Complex World
by Donald Sull and Kathleen M. Eisenhardt · 20 Apr 2015 · 294pp · 82,438 words
Version Control With Git: Powerful Tools and Techniques for Collaborative Software Development
by Jon Loeliger and Matthew McCullough · 14 Aug 2012
Shipping Greatness
by Chris Vander Mey · 23 Aug 2012 · 231pp · 71,248 words
Erlang Programming
by Francesco Cesarini · 496pp · 70,263 words
Working Effectively With Legacy Code
by Michael Feathers · 14 Jul 2004 · 508pp · 120,339 words
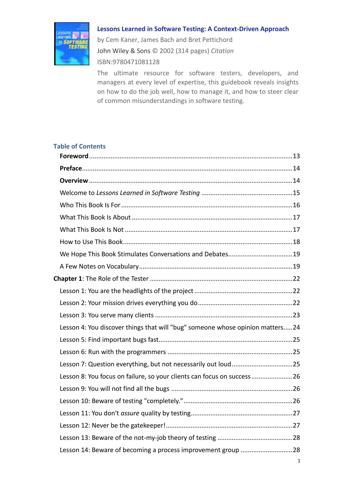
Lessons-Learned-in-Software-Testing-A-Context-Driven-Approach
by Anson-QA
The Silent Intelligence: The Internet of Things
by Daniel Kellmereit and Daniel Obodovski · 19 Sep 2013 · 138pp · 40,787 words
Site Reliability Engineering: How Google Runs Production Systems
by Betsy Beyer, Chris Jones, Jennifer Petoff and Niall Richard Murphy · 15 Apr 2016 · 719pp · 181,090 words
Programming Android
by Zigurd Mednieks, Laird Dornin, G. Blake Meike and Masumi Nakamura · 15 Jul 2011
Designing Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable Systems
by Martin Kleppmann · 17 Apr 2017
Programming Scala
by Unknown · 2 Jan 2010 · 448pp · 71,301 words
The Art of Scalability: Scalable Web Architecture, Processes, and Organizations for the Modern Enterprise
by Martin L. Abbott and Michael T. Fisher · 1 Dec 2009
Python Geospatial Development - Second Edition
by Erik Westra · 23 May 2013
The Facebook era: tapping online social networks to build better products, reach new audiences, and sell more stuff
by Clara Shih · 30 Apr 2009 · 255pp · 76,495 words
Vue.js 2 Cookbook
by Andrea Passaglia · 27 Apr 2017 · 550pp · 84,515 words
Programming Python
by Mark Lutz · 5 Jan 2011
Designing Interfaces
by Jenifer Tidwell · 15 Dec 2010
Masterminds of Programming: Conversations With the Creators of Major Programming Languages
by Federico Biancuzzi and Shane Warden · 21 Mar 2009 · 496pp · 174,084 words
Graph Databases
by Ian Robinson, Jim Webber and Emil Eifrem · 13 Jun 2013 · 201pp · 63,192 words
Code Complete (Developer Best Practices)
by Steve McConnell · 8 Jun 2004 · 1,758pp · 342,766 words
Personal Finance with Python
by Max Humber · 156pp · 15,746 words
Catalyst 5.8: The Perl MVC Framework
by Antano Solar John, Jonathan Rockway and Solar John Antano · 15 Nov 2010
Pro AngularJS
by Adam Freeman · 25 Mar 2014 · 671pp · 228,348 words
AngularJS Essentials
by Rodrigo Branas · 20 Aug 2014 · 180pp · 37,187 words
Introduction to Tornado
by Michael Dory, Adam Parrish and Brendan Berg · 29 Sep 2011 · 136pp · 20,501 words
Beginning Backbone.js
by James Sugrue · 15 Dec 2013 · 290pp · 119,172 words
Full Stack Web Development With Backbone.js
by Patrick Mulder · 18 Jun 2014 · 190pp · 52,865 words
Structuring Backbone Code With RequireJS and Marionette Modules
by David Sulc · 244pp · 20,327 words
Developing Backbone.js Applications
by Addy Osmani · 21 Jul 2012 · 420pp · 79,867 words
Human Compatible: Artificial Intelligence and the Problem of Control
by Stuart Russell · 7 Oct 2019 · 416pp · 112,268 words
API Marketplace Engineering: Design, Build, and Run a Platform for External Developers
by Rennay Dorasamy · 2 Dec 2021 · 328pp · 77,877 words
Model Thinker: What You Need to Know to Make Data Work for You
by Scott E. Page · 27 Nov 2018 · 543pp · 153,550 words
Practical Vim, Second Edition (for Stefano Alcazi)
by Drew Neil

Practical Vim
by Drew Neil
Mastering Blockchain, Second Edition
by Imran Bashir · 28 Mar 2018
Visual Thinking: The Hidden Gifts of People Who Think in Pictures, Patterns, and Abstractions
by Temple Grandin, Ph.d. · 11 Oct 2022
Mastering Ethereum: Building Smart Contracts and DApps
by Andreas M. Antonopoulos and Gavin Wood Ph. D. · 23 Dec 2018 · 960pp · 125,049 words
Text Analytics With Python: A Practical Real-World Approach to Gaining Actionable Insights From Your Data
by Dipanjan Sarkar · 1 Dec 2016
Monadic Design Patterns for the Web
by L.G. Meredith · 214pp · 14,382 words
Eloquent JavaScript: A Modern Introduction to Programming
by Marijn Haverbeke · 15 Nov 2018 · 560pp · 135,629 words
Seven Databases in Seven Weeks: A Guide to Modern Databases and the NoSQL Movement
by Eric Redmond, Jim Wilson and Jim R. Wilson · 7 May 2012 · 713pp · 93,944 words
Practical Ext JS Projects With Gears
by Frank Zammetti · 7 Jul 2009 · 602pp · 207,965 words
Learning Ext Js
by Shea Frederick · 19 Dec 2008 · 324pp · 87,064 words
Programming Computer Vision with Python
by Jan Erik Solem · 26 Jun 2012
Data Mining: Concepts, Models, Methods, and Algorithms
by Mehmed Kantardzić · 2 Jan 2003 · 721pp · 197,134 words
Python Web Development With Django
by Jeff Forcier
Mastering Blockchain: Unlocking the Power of Cryptocurrencies and Smart Contracts
by Lorne Lantz and Daniel Cawrey · 8 Dec 2020 · 434pp · 77,974 words
AngularJS
by Brad Green and Shyam Seshadri · 15 Mar 2013 · 196pp · 58,122 words
MongoDB and Python
by Niall O’Higgins · 66pp · 9,247 words
The Icon Handbook
by Jon Hicks · 23 Jun 2011
Dogfight: How Apple and Google Went to War and Started a Revolution
by Fred Vogelstein · 12 Nov 2013 · 275pp · 84,418 words
HBase: The Definitive Guide
by Lars George · 29 Aug 2011
SQL Hacks
by Andrew Cumming and Gordon Russell · 28 Nov 2006 · 696pp · 111,976 words

Haskell Programming: From First Principles
by Christopher Allen and Julie Moronuki · 1 Jan 2015 · 1,076pp · 67,364 words
Industry 4.0: The Industrial Internet of Things
by Alasdair Gilchrist · 27 Jun 2016

Tmux: Productive Mouse-Free Development
by Brian P. Hogan · 29 Feb 2012 · 122pp · 19,807 words
The Practice of Cloud System Administration: DevOps and SRE Practices for Web Services, Volume 2
by Thomas A. Limoncelli, Strata R. Chalup and Christina J. Hogan · 27 Aug 2014 · 757pp · 193,541 words
Learning Flask Framework
by Matt Copperwaite and Charles Leifer · 26 Nov 2015
Scala in Action
by Nilanjan Raychaudhuri · 27 Mar 2012
Realtime Web Apps: HTML5 WebSocket, Pusher, and the Web’s Next Big Thing
by Jason Lengstorf and Phil Leggetter · 20 Feb 2013
Solr in Action
by Trey Grainger and Timothy Potter · 14 Sep 2014 · 1,085pp · 219,144 words
The Stack: On Software and Sovereignty
by Benjamin H. Bratton · 19 Feb 2016 · 903pp · 235,753 words
The Art of Monitoring
by James Turnbull · 1 Dec 2014 · 514pp · 111,012 words
PostGIS in Action, 2nd Edition
by Regina O. Obe and Leo S. Hsu · 2 May 2015
Build Awesome Command-Line Applications in Ruby: Control Your Computer, Simplify Your Life
by David B. Copeland · 6 Apr 2012 · 408pp · 63,990 words
Apache Solr 3 Enterprise Search Server
by Unknown · 13 Jan 2012 · 470pp · 109,589 words
Startup Weekend: How to Take a Company From Concept to Creation in 54 Hours
by Marc Nager, Clint Nelsen and Franck Nouyrigat · 8 Nov 2011 · 179pp · 42,006 words
Mining the Social Web: Finding Needles in the Social Haystack
by Matthew A. Russell · 15 Jan 2011 · 541pp · 109,698 words
The Productive Programmer
by Neal Ford · 8 Dec 2008 · 224pp · 48,804 words
Beautiful security
by Andy Oram and John Viega · 15 Dec 2009 · 302pp · 82,233 words
Practical OCaml
by Joshua B. Smith · 30 Sep 2006
Beautiful Data: The Stories Behind Elegant Data Solutions
by Toby Segaran and Jeff Hammerbacher · 1 Jul 2009
The Architecture of Open Source Applications
by Amy Brown and Greg Wilson · 24 May 2011 · 834pp · 180,700 words
Big Data Analytics: Turning Big Data Into Big Money
by Frank J. Ohlhorst · 28 Nov 2012 · 133pp · 42,254 words
Essential Sqlalchemy
by Jason Myers and Rick Copeland · 27 Nov 2015 · 458pp · 46,761 words
Exploring Python
by Timothy Budd · 17 Feb 2009 · 263pp · 20,730 words
Python Data Analytics: With Pandas, NumPy, and Matplotlib
by Fabio Nelli · 27 Sep 2018 · 688pp · 107,867 words
Ruby by example: concepts and code
by Kevin C. Baird · 1 Jun 2007 · 309pp · 65,118 words
Bit Literacy: Productivity in the Age of Information and E-mail Overload
by Mark Hurst · 15 Jun 2007 · 153pp · 52,175 words
The Art of Community: Building the New Age of Participation
by Jono Bacon · 1 Aug 2009 · 394pp · 110,352 words
Python Network Programming Cookbook
by M. Omar Faruque Sarker · 15 Feb 2014 · 234pp · 57,267 words
Building Secure and Reliable Systems: Best Practices for Designing, Implementing, and Maintaining Systems
by Heather Adkins, Betsy Beyer, Paul Blankinship, Ana Oprea, Piotr Lewandowski and Adam Stubblefield · 29 Mar 2020 · 1,380pp · 190,710 words
Puppet 3 Cookbook
by John Arundel · 25 Aug 2013 · 274pp · 58,675 words

Engineering Security
by Peter Gutmann
Blockchain: Blueprint for a New Economy
by Melanie Swan · 22 Jan 2014 · 271pp · 52,814 words
Zero to Sold: How to Start, Run, and Sell a Bootstrapped Business
by Arvid Kahl · 24 Jun 2020 · 461pp · 106,027 words
UNIX® Network Programming, Volume 1: The Sockets Networking API, 3rd Edition
by W. Richard Stevens, Bill Fenner, Andrew M. Rudoff · 8 Jun 2013
The Art of UNIX Programming
by Eric S. Raymond · 22 Sep 2003 · 612pp · 187,431 words
Principles of Web API Design: Delivering Value with APIs and Microservices
by James Higginbotham · 20 Dec 2021 · 283pp · 78,705 words
Hands-On RESTful API Design Patterns and Best Practices
by Harihara Subramanian · 31 Jan 2019 · 422pp · 86,414 words
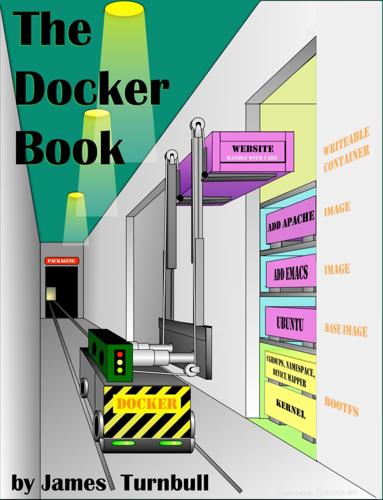
The Docker Book
by James Turnbull · 13 Jul 2014 · 265pp · 60,880 words
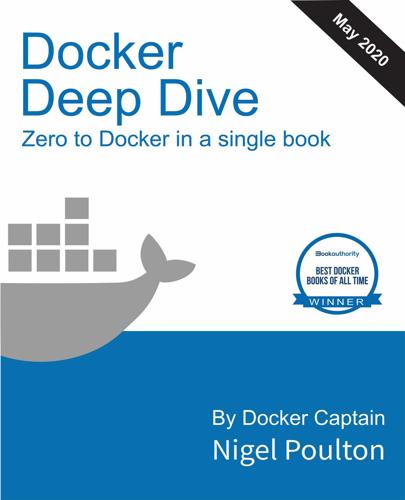
Docker Deep Dive
by Nigel Poulton · 10 May 2020
The Cultural Logic of Computation
by David Golumbia · 31 Mar 2009 · 268pp · 109,447 words
Clean Code: A Handbook of Agile Software Craftsmanship
by Robert C. Martin · 1 Jan 2007 · 462pp · 172,671 words
Android 3. 0 Application Development Cookbook
by Kyle Merrifield Mew · 3 Aug 2011 · 272pp · 52,204 words
Docker: Up & Running: Shipping Reliable Containers in Production
by Sean Kane and Karl Matthias · 14 May 2023 · 433pp · 130,334 words
The TypeScript Workshop: A Practical Guide to Confident, Effective TypeScript Programming
by Ben Grynhaus, Jordan Hudgens, Rayon Hunte, Matthew Thomas Morgan and Wekoslav Stefanovski · 28 Jul 2021 · 739pp · 174,990 words
Essential TypeScript 4: From Beginner to Pro
by Adam Freeman
Docker in Action
by Jeff Nickoloff and Stephen Kuenzli · 10 Dec 2019 · 629pp · 109,663 words
The Nature of Software Development: Keep It Simple, Make It Valuable, Build It Piece by Piece
by Ron Jeffries · 14 Aug 2015 · 444pp · 118,393 words
Docker: Up & Running: Shipping Reliable Containers in Production
by Sean P. Kane and Karl Matthias · 15 Mar 2018 · 350pp · 114,454 words
Programming TypeScript
by Boris Cherny · 16 Apr 2019 · 629pp · 83,362 words
Bad Data Handbook
by Q. Ethan McCallum · 14 Nov 2012 · 398pp · 86,855 words
Data Wrangling With Python: Tips and Tools to Make Your Life Easier
by Jacqueline Kazil · 4 Feb 2016
The Digital Divide: Arguments for and Against Facebook, Google, Texting, and the Age of Social Netwo Rking
by Mark Bauerlein · 7 Sep 2011 · 407pp · 103,501 words
The Future of the Internet: And How to Stop It
by Jonathan Zittrain · 27 May 2009 · 629pp · 142,393 words
Data and the City
by Rob Kitchin,Tracey P. Lauriault,Gavin McArdle · 2 Aug 2017
Tcl/Tk, Second Edition: A Developer's Guide
by Clif Flynt · 18 May 2003 · 792pp · 48,468 words
Designing Search: UX Strategies for Ecommerce Success
by Greg Nudelman and Pabini Gabriel-Petit · 8 May 2011
Designing Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable Systems
by Martin Kleppmann · 16 Mar 2017 · 1,237pp · 227,370 words
Slide:ology: the art and science of creating great presentations
by Nancy Duarte · 15 Nov 2008 · 297pp · 35,674 words
Dreaming in Code: Two Dozen Programmers, Three Years, 4,732 Bugs, and One Quest for Transcendent Software
by Scott Rosenberg · 2 Jan 2006 · 394pp · 118,929 words
Ansible Playbook Essentials
by Gourav Shah · 29 Jul 2015 · 178pp · 33,275 words
Super Founders: What Data Reveals About Billion-Dollar Startups
by Ali Tamaseb · 14 Sep 2021 · 251pp · 80,831 words
The End of Jobs: Money, Meaning and Freedom Without the 9-To-5
by Taylor Pearson · 27 Jun 2015 · 168pp · 50,647 words
Map Scripting 101: An Example-Driven Guide to Building Interactive Maps With Bing, Yahoo!, and Google Maps
by Adam Duvander · 14 Aug 2010 · 415pp · 95,261 words
Getting Started with RStudio
by John Verzani · 18 Sep 2011 · 99pp · 19,884 words
This Is How They Tell Me the World Ends: The Cyberweapons Arms Race
by Nicole Perlroth · 9 Feb 2021 · 651pp · 186,130 words
Jenkins Continuous Integration Cookbook
by Alan Berg · 15 Mar 2012 · 372pp · 67,140 words
The Data Journalism Handbook
by Jonathan Gray, Lucy Chambers and Liliana Bounegru · 9 May 2012
Effective Programming: More Than Writing Code
by Jeff Atwood · 3 Jul 2012 · 270pp · 64,235 words
Joel on Software
by Joel Spolsky · 1 Aug 2004 · 370pp · 105,085 words
Learning Ansible 2 - Second Edition
by Fabio Alessandro Locati · 21 Nov 2016
Programming in CoffeeScript
by Mark Bates · 2 Jun 2012 · 323pp · 65,306 words
The Business Blockchain: Promise, Practice, and Application of the Next Internet Technology
by William Mougayar · 25 Apr 2016 · 161pp · 44,488 words
Introducing Elixir
by Simon St.Laurent and J. David Eisenberg · 20 Dec 2016
Digital Accounting: The Effects of the Internet and Erp on Accounting
by Ashutosh Deshmukh · 13 Dec 2005
Gray Day: My Undercover Mission to Expose America's First Cyber Spy
by Eric O'Neill · 1 Mar 2019 · 299pp · 88,375 words
Quiet: The Power of Introverts in a World That Can't Stop Talking
by Susan Cain · 24 Jan 2012 · 377pp · 115,122 words
More Joel on Software
by Joel Spolsky · 25 Jun 2008 · 292pp · 81,699 words
Learn Python the Hard Way
by Zed Shaw · 1 Jan 2010 · 249pp · 45,639 words
The Future of the Brain: Essays by the World's Leading Neuroscientists
by Gary Marcus and Jeremy Freeman · 1 Nov 2014 · 336pp · 93,672 words
Nagios: System and Network Monitoring
by Wolfgang Barth · 25 May 2006
Designing Web Interfaces: Principles and Patterns for Rich Interactions
by Bill Scott and Theresa Neil · 15 Dec 2008 · 504pp · 67,845 words
Building Microservices
by Sam Newman · 25 Dec 2014 · 540pp · 103,101 words
Bank 3.0: Why Banking Is No Longer Somewhere You Go but Something You Do
by Brett King · 26 Dec 2012 · 382pp · 120,064 words
The Debian Administrator's Handbook, Debian Wheezy From Discovery to Mastery
by Raphaal Hertzog and Roland Mas · 24 Dec 2013 · 678pp · 159,840 words
Designing Social Interfaces
by Christian Crumlish and Erin Malone · 30 Sep 2009 · 518pp · 49,555 words
Facebook: The Inside Story
by Steven Levy · 25 Feb 2020 · 706pp · 202,591 words
Designing for the Social Web
by Joshua Porter · 18 May 2008 · 201pp · 21,180 words
jQuery UI 1.8: The User Interface Library for jQuery
by Dan Wellman · 14 Aug 2011
Where Does It Hurt?: An Entrepreneur's Guide to Fixing Health Care
by Jonathan Bush and Stephen Baker · 14 May 2014 · 238pp · 68,914 words
REST API Design Rulebook
by Mark Masse · 19 Oct 2011 · 153pp · 27,424 words
Python for Unix and Linux System Administration
by Noah Gift and Jeremy M. Jones · 29 Jun 2009 · 603pp · 141,814 words
Gamification by Design: Implementing Game Mechanics in Web and Mobile Apps
by Gabe Zichermann and Christopher Cunningham · 14 Aug 2011 · 145pp · 40,897 words
Programming HTML5 Applications
by Zachary Kessin · 9 May 2011 · 210pp · 42,271 words
Data Mining: Concepts and Techniques: Concepts and Techniques
by Jiawei Han, Micheline Kamber and Jian Pei · 21 Jun 2011
Django Book
by Matt Behrens · 24 Jan 2015
Reality Is Broken: Why Games Make Us Better and How They Can Change the World
by Jane McGonigal · 20 Jan 2011 · 470pp · 128,328 words
Beautiful Visualization
by Julie Steele · 20 Apr 2010
Java: The Good Parts
by Jim Waldo · 193pp · 31,998 words
Practical Vim: Edit Text at the Speed of Thought
by Drew Neil · 6 Oct 2012 · 722pp · 90,903 words

Fancy Bear Goes Phishing: The Dark History of the Information Age, in Five Extraordinary Hacks
by Scott J. Shapiro · 523pp · 154,042 words
Design for Hackers: Reverse Engineering Beauty
by David Kadavy · 5 Sep 2011 · 276pp · 78,094 words
Peer-to-Peer
by Andy Oram · 26 Feb 2001 · 673pp · 164,804 words
Solr 1.4 Enterprise Search Server
by David Smiley and Eric Pugh · 15 Nov 2009 · 648pp · 108,814 words
Coders at Work
by Peter Seibel · 22 Jun 2009 · 1,201pp · 233,519 words
JavaScript Cookbook
by Shelley Powers · 23 Jul 2010 · 1,038pp · 137,468 words
Team Geek
by Brian W. Fitzpatrick and Ben Collins-Sussman · 6 Jul 2012 · 209pp · 54,638 words
Makers at Work: Folks Reinventing the World One Object or Idea at a Time
by Steven Osborn · 17 Sep 2013 · 310pp · 34,482 words
Designing Great Web APIs: Creating Business Value Through Developer Experience
by James Higginbotham · 14 Apr 2015 · 39pp · 10,453 words
Backup & Recovery
by W. Curtis Preston · 9 Feb 2009 · 1,266pp · 278,632 words
Multitool Linux: Practical Uses for Open Source Software
by Michael Schwarz, Jeremy Anderson and Peter Curtis · 7 May 2002
Backbone.js Cookbook
by Vadim Mirgorod · 25 Aug 2013
PayPal APIs: Up and Running: A Developer's Guide
by Michael Balderas · 7 Mar 2011 · 124pp · 25,026 words
Hacking Exposed: Network Security Secrets and Solutions
by Stuart McClure, Joel Scambray and George Kurtz · 15 Feb 2001 · 260pp · 40,943 words
Python Cookbook
by David Beazley and Brian K. Jones · 9 May 2013 · 1,606pp · 168,061 words
Android Cookbook
by Ian F. Darwin · 9 Apr 2012 · 960pp · 140,978 words
CTOs at Work
by Scott Donaldson, Stanley Siegel and Gary Donaldson · 13 Jan 2012 · 458pp · 135,206 words
Getting Started With OAuth 2.0
by Ryan Boyd · 29 Feb 2012 · 91pp · 18,831 words

Learning SPARQL
by Bob Ducharme · 15 Jul 2011 · 315pp · 70,044 words
Professional Node.js: Building Javascript Based Scalable Software
by Pedro Teixeira · 30 Sep 2012 · 325pp · 85,599 words

Programming Clojure
by Stuart Halloway and Aaron Bedra · 17 Apr 2012 · 536pp · 73,482 words
Programming Collective Intelligence
by Toby Segaran · 17 Dec 2008 · 519pp · 102,669 words
Clojure Programming
by Chas Emerick, Brian Carper and Christophe Grand · 15 Aug 2011 · 999pp · 194,942 words
Testing Extreme Programming
by Lisa Crispin and Tip House · 15 Apr 2003 · 448pp · 84,462 words
Business Metadata: Capturing Enterprise Knowledge
by William H. Inmon, Bonnie K. O'Neil and Lowell Fryman · 15 Feb 2008 · 314pp · 94,600 words
Hadoop: The Definitive Guide
by Tom White · 29 May 2009 · 933pp · 205,691 words
Click Here to Kill Everybody: Security and Survival in a Hyper-Connected World
by Bruce Schneier · 3 Sep 2018 · 448pp · 117,325 words
Start Small, Stay Small: A Developer's Guide to Launching a Startup
by Rob Walling · 15 Jan 2010 · 183pp · 49,460 words
Test-Driven Development With Python
by Harry J. W. Percival · 10 Jun 2014 · 779pp · 116,439 words
Ubuntu 15.04 Server with systemd: Administration and Reference
by Richard Petersen · 15 May 2015
Exploring ES6 - Upgrade to the next version of JavaScript
by Axel Rauschmayer · 3 Oct 2015
WTF?: What's the Future and Why It's Up to Us
by Tim O'Reilly · 9 Oct 2017 · 561pp · 157,589 words
The Zero Marginal Cost Society: The Internet of Things, the Collaborative Commons, and the Eclipse of Capitalism
by Jeremy Rifkin · 31 Mar 2014 · 565pp · 151,129 words
The Business of Platforms: Strategy in the Age of Digital Competition, Innovation, and Power
by Michael A. Cusumano, Annabelle Gawer and David B. Yoffie · 6 May 2019 · 328pp · 84,682 words
Machine Learning Design Patterns: Solutions to Common Challenges in Data Preparation, Model Building, and MLOps
by Valliappa Lakshmanan, Sara Robinson and Michael Munn · 31 Oct 2020
The Art of Software Security Assessment: Identifying and Preventing Software Vulnerabilities
by Justin Schuh · 20 Nov 2006 · 2,054pp · 359,149 words
Founders at Work: Stories of Startups' Early Days
by Jessica Livingston · 14 Aug 2008 · 468pp · 233,091 words
HTML5 Cookbook
by Christopher Schmitt and Kyle Simpson · 13 Sep 2011 · 435pp · 62,013 words
Big Data Glossary
by Pete Warden · 20 Sep 2011 · 58pp · 12,386 words
Androids: The Team That Built the Android Operating System
by Chet Haase · 12 Aug 2021 · 580pp · 125,129 words
Hope Dies Last: Visionary People Across the World, Fighting to Find Us a Future
by Alan Weisman · 21 Apr 2025 · 599pp · 149,014 words
Mindf*ck: Cambridge Analytica and the Plot to Break America
by Christopher Wylie · 8 Oct 2019
Seeking SRE: Conversations About Running Production Systems at Scale
by David N. Blank-Edelman · 16 Sep 2018
Recoding America: Why Government Is Failing in the Digital Age and How We Can Do Better
by Jennifer Pahlka · 12 Jun 2023 · 288pp · 96,204 words
Presentation Zen
by Garr Reynolds · 15 Jan 2012
Advanced Software Testing—Vol. 3, 2nd Edition
by Jamie L. Mitchell and Rex Black · 15 Feb 2015
RDF Database Systems: Triples Storage and SPARQL Query Processing
by Olivier Cure and Guillaume Blin · 10 Dec 2014
AI in Museums: Reflections, Perspectives and Applications
by Sonja Thiel and Johannes C. Bernhardt · 31 Dec 2023 · 321pp · 113,564 words
Ajax: The Definitive Guide
by Anthony T. Holdener · 25 Jan 2008 · 982pp · 221,145 words
Coding Freedom: The Ethics and Aesthetics of Hacking
by E. Gabriella Coleman · 25 Nov 2012 · 398pp · 107,788 words
High Performance JavaScript
by Nicholas C. Zakas · 15 Mar 2010 · 375pp · 66,268 words
JavaScript: the good parts
by Douglas Crockford · 15 Nov 2008 · 273pp · 46,214 words
Puppet Essentials
by Felix Frank · 20 Nov 2014 · 234pp · 63,522 words
Tribe of Mentors: Short Life Advice From the Best in the World
by Timothy Ferriss · 14 Jun 2017 · 579pp · 183,063 words
PostgreSQL: Up and Running
by Regina Obe and Leo Hsu · 5 Jul 2012 · 205pp · 47,169 words
Beautiful Testing: Leading Professionals Reveal How They Improve Software (Theory in Practice)
by Adam Goucher and Tim Riley · 13 Oct 2009 · 351pp · 123,876 words
Working in Public: The Making and Maintenance of Open Source Software
by Nadia Eghbal · 3 Aug 2020 · 1,136pp · 73,489 words
Webbots, Spiders, and Screen Scrapers
by Michael Schrenk · 19 Aug 2009 · 371pp · 78,103 words
Technical Blogging: Turn Your Expertise Into a Remarkable Online Presence
by Antonio Cangiano · 15 Mar 2012 · 315pp · 85,791 words

Digital Bank: Strategies for Launching or Becoming a Digital Bank
by Chris Skinner · 27 Aug 2013 · 329pp · 95,309 words
HTML5 Canvas
by Steve Fulton and Jeff Fulton · 2 May 2013 · 1,881pp · 178,824 words

Vagrant: Up and Running
by Mitchell Hashimoto · 29 May 2013 · 192pp · 44,789 words
In the Plex: How Google Thinks, Works, and Shapes Our Lives
by Steven Levy · 12 Apr 2011 · 666pp · 181,495 words
ClojureScript: Up and Running
by Stuart Sierra and Luke Vanderhart · 24 Oct 2012 · 135pp · 31,098 words
Python Requests Essentials
by Rakesh Vidya Chandra and Bala Subrahmanyam Varanasi · 16 Jun 2015 · 134pp · 29,488 words
Nginx Essentials
by Valery Kholodkov · 21 Jul 2015 · 174pp · 34,672 words
Nagios: System and Network Monitoring, 2nd Edition
by Wolfgang Barth · 19 Aug 2009 · 996pp · 180,520 words
Nginx HTTP Server Second Edition
by Clement Nedelcu · 18 Jul 2013 · 319pp · 72,969 words
Website Optimization
by Andrew B. King · 15 Mar 2008 · 597pp · 119,204 words
Ansible: Up and Running: Automating Configuration Management and Deployment the Easy Way
by Lorin Hochstein · 8 Dec 2014 · 761pp · 80,914 words
Ansible for DevOps: Server and Configuration Management for Humans
by Jeff Geerling · 9 Oct 2015 · 313pp · 75,583 words
Learning SPARQL
by Bob Ducharme · 22 Jul 2011 · 511pp · 111,423 words
Programming Ruby 1.9: The Pragmatic Programmer's Guide
by Dave Thomas, Chad Fowler and Andy Hunt · 15 Dec 2000 · 936pp · 85,745 words
Lean Analytics: Use Data to Build a Better Startup Faster
by Alistair Croll and Benjamin Yoskovitz · 1 Mar 2013 · 567pp · 122,311 words
The Art of SEO
by Eric Enge, Stephan Spencer, Jessie Stricchiola and Rand Fishkin · 7 Mar 2012
Node.js in Action
by Mike Cantelon, Marc Harter, Tj Holowaychuk and Nathan Rajlich · 27 Jul 2013 · 628pp · 107,927 words
European Founders at Work
by Pedro Gairifo Santos · 7 Nov 2011 · 353pp · 104,146 words

Getting Real
by Jason Fried, David Heinemeier Hansson, Matthew Linderman and 37 Signals · 1 Jan 2006 · 132pp · 31,976 words
Mastering Structured Data on the Semantic Web: From HTML5 Microdata to Linked Open Data
by Leslie Sikos · 10 Jul 2015
Designing Web APIs: Building APIs That Developers Love
by Brenda Jin, Saurabh Sahni and Amir Shevat · 28 Aug 2018
Measure What Matters: How Google, Bono, and the Gates Foundation Rock the World With OKRs
by John Doerr · 23 Apr 2018 · 280pp · 71,268 words
Beautiful Architecture: Leading Thinkers Reveal the Hidden Beauty in Software Design
by Diomidis Spinellis and Georgios Gousios · 30 Dec 2008 · 680pp · 157,865 words
Collaborative Futures
by Mike Linksvayer, Michael Mandiberg and Mushon Zer-Aviv · 24 Aug 2010 · 188pp · 9,226 words
Mining of Massive Datasets
by Jure Leskovec, Anand Rajaraman and Jeffrey David Ullman · 13 Nov 2014
Future Crimes: Everything Is Connected, Everyone Is Vulnerable and What We Can Do About It
by Marc Goodman · 24 Feb 2015 · 677pp · 206,548 words
Service Design Patterns: Fundamental Design Solutions for SOAP/WSDL and RESTful Web Services
by Robert Daigneau · 14 Sep 2011
Pro Git
by Scott Chacon and Ben Straub · 12 Nov 2014 · 549pp · 134,988 words
PostgreSQL: Up and Running, 3rd Edition
by Unknown
Culture & Empire: Digital Revolution
by Pieter Hintjens · 11 Mar 2013 · 349pp · 114,038 words
Alpha Girls: The Women Upstarts Who Took on Silicon Valley's Male Culture and Made the Deals of a Lifetime
by Julian Guthrie · 15 Nov 2019
Architecting Modern Data Platforms: A Guide to Enterprise Hadoop at Scale
by Jan Kunigk, Ian Buss, Paul Wilkinson and Lars George · 8 Jan 2019 · 1,409pp · 205,237 words
Total Recall: How the E-Memory Revolution Will Change Everything
by Gordon Bell and Jim Gemmell · 15 Feb 2009 · 291pp · 77,596 words
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
by Kevin Mitnick, Mikko Hypponen and Robert Vamosi · 14 Feb 2017 · 305pp · 93,091 words
Internet for the People: The Fight for Our Digital Future
by Ben Tarnoff · 13 Jun 2022 · 234pp · 67,589 words
PostGIS in Action
by Regina O. Obe and Leo S. Hsu · 2 May 2015
Intrusion Detection With Snort, Apache, Mysql, Php, and Acid
by Rafeeq Ur Rehman · 7 May 2003 · 257pp · 64,973 words
Avogadro Corp
by William Hertling · 9 Apr 2014 · 247pp · 71,698 words
The Economics of Enough: How to Run the Economy as if the Future Matters
by Diane Coyle · 21 Feb 2011 · 523pp · 111,615 words
Ship It!: A Practical Guide to Successful Software Projects
by Jared R. Richardson and William A. Gwaltney · 15 Mar 2005 · 203pp · 14,242 words
Writing Effective Use Cases
by Alistair Cockburn · 30 Sep 2000
Python Web Penetration Testing Cookbook
by Cameron Buchanan, Terry Ip, Andrew Mabbitt, Benjamin May and Dave Mound · 28 Jun 2015 · 224pp · 45,431 words
Mobile First
by Luke Wroblewski · 4 Oct 2011 · 95pp · 23,041 words
JavaScript & jQuery: The Missing Manual
by David Sawyer McFarland · 28 Oct 2011 · 924pp · 196,343 words
The Invisible Web: Uncovering Information Sources Search Engines Can't See
by Gary Price, Chris Sherman and Danny Sullivan · 2 Jan 2003 · 481pp · 121,669 words
The Connected Company
by Dave Gray and Thomas Vander Wal · 2 Dec 2014 · 372pp · 89,876 words
JQuery Pocket Reference
by David Flanagan · 15 Dec 2010 · 211pp · 37,094 words
Web Scraping With Python: Collecting Data From the Modern Web
by Ryan Mitchell · 14 Jun 2015 · 255pp · 78,207 words
Adapt: Why Success Always Starts With Failure
by Tim Harford · 1 Jun 2011 · 459pp · 103,153 words
Cybersecurity: What Everyone Needs to Know
by P. W. Singer and Allan Friedman · 3 Jan 2014 · 587pp · 117,894 words
Speaking JavaScript: An In-Depth Guide for Programmers
by Axel Rauschmayer · 25 Feb 2014 · 692pp · 95,244 words
The Buddha and the Badass: The Secret Spiritual Art of Succeeding at Work
by Vishen Lakhiani · 14 Sep 2020
Bold: How to Go Big, Create Wealth and Impact the World
by Peter H. Diamandis and Steven Kotler · 3 Feb 2015 · 368pp · 96,825 words
50 Future Ideas You Really Need to Know
by Richard Watson · 5 Nov 2013 · 219pp · 63,495 words
Working Backwards: Insights, Stories, and Secrets From Inside Amazon
by Colin Bryar and Bill Carr · 9 Feb 2021 · 302pp · 100,493 words
Ask Your Developer: How to Harness the Power of Software Developers and Win in the 21st Century
by Jeff Lawson · 12 Jan 2021 · 282pp · 85,658 words
New Power: How Power Works in Our Hyperconnected World--And How to Make It Work for You
by Jeremy Heimans and Henry Timms · 2 Apr 2018 · 416pp · 100,130 words
A World Without Email: Reimagining Work in an Age of Communication Overload
by Cal Newport · 2 Mar 2021 · 350pp · 90,898 words
Start-Up Nation: The Story of Israel's Economic Miracle
by Dan Senor and Saul Singer · 3 Nov 2009 · 285pp · 81,743 words
The Rust Programming Language, 2nd Edition
by Steve Klabnik and Carol Nichols · 27 Feb 2023 · 648pp · 183,275 words
Deploying OpenStack
by Ken Pepple · 26 Jul 2011 · 90pp · 17,297 words
This Is for Everyone: The Captivating Memoir From the Inventor of the World Wide Web
by Tim Berners-Lee · 8 Sep 2025 · 347pp · 100,038 words
So Good They Can't Ignore You: Why Skills Trump Passion in the Quest for Work You Love
by Cal Newport · 17 Sep 2012 · 197pp · 60,477 words
The $100 Startup: Reinvent the Way You Make a Living, Do What You Love, and Create a New Future
by Chris Guillebeau · 7 May 2012 · 248pp · 72,174 words
The Art of Readable Code
by Dustin Boswell and Trevor Foucher · 14 Sep 2010
We Are the Nerds: The Birth and Tumultuous Life of Reddit, the Internet's Culture Laboratory
by Christine Lagorio-Chafkin · 1 Oct 2018
Pragmatic Guide to JavaScript
by Christophe Porteneuve · 15 Nov 2010 · 141pp · 9,896 words
Daemon
by Daniel Suarez · 1 Dec 2006 · 562pp · 146,544 words
NumPy Cookbook
by Ivan Idris · 30 Sep 2012 · 197pp · 35,256 words
Being Geek: The Software Developer's Career Handbook
by Michael Lopp · 20 Jul 2010 · 336pp · 88,320 words
Designing for Emotion
by Aarron Walter · 4 Oct 2011 · 89pp · 24,277 words
Ansible Configuration Management - Second Edition
by Daniel Hall · 29 Apr 2015 · 132pp · 28,815 words
HTML5 for Web Designers
by Jeremy Keith · 2 Jan 2010 · 73pp · 17,793 words
Producing Open Source Software: How to Run a Successful Free Software Project
by Karl Fogel · 13 Oct 2005
Tracers in the Dark: The Global Hunt for the Crime Lords of Cryptocurrency
by Andy Greenberg · 15 Nov 2022 · 494pp · 121,217 words
The Hacker's Diet
by John Walker
21 Recipes for Mining Twitter
by Matthew A. Russell · 15 Feb 2011 · 71pp · 14,237 words
The Book of CSS3
by Peter Gasston · 14 Apr 2011 · 502pp · 82,170 words
Mining Social Media: Finding Stories in Internet Data
by Lam Thuy Vo · 21 Nov 2019 · 237pp · 65,794 words
Data for the Public Good
by Alex Howard · 21 Feb 2012 · 25pp · 5,789 words
Kingpin: How One Hacker Took Over the Billion-Dollar Cybercrime Underground
by Kevin Poulsen · 22 Feb 2011 · 264pp · 79,589 words
The Googlization of Everything:
by Siva Vaidhyanathan · 1 Jan 2010 · 281pp · 95,852 words
The Boy Who Could Change the World: The Writings of Aaron Swartz
by Aaron Swartz and Lawrence Lessig · 5 Jan 2016 · 377pp · 110,427 words
Blitzscaling: The Lightning-Fast Path to Building Massively Valuable Companies
by Reid Hoffman and Chris Yeh · 14 Apr 2018 · 286pp · 87,401 words
The Knowledge Illusion
by Steven Sloman · 10 Feb 2017 · 313pp · 91,098 words
The Dark Cloud: How the Digital World Is Costing the Earth
by Guillaume Pitron · 14 Jun 2023 · 271pp · 79,355 words
Code Dependent: Living in the Shadow of AI
by Madhumita Murgia · 20 Mar 2024 · 336pp · 91,806 words
We Are Anonymous: Inside the Hacker World of LulzSec, Anonymous, and the Global Cyber Insurgency
by Parmy Olson · 5 Jun 2012 · 478pp · 149,810 words
Interactive Data Visualization for the Web
by Scott Murray · 15 Mar 2013 · 186pp · 50,651 words
Creating Development Environments With Vagrant - Second Edition
by Michael Peacock · 26 Feb 2015 · 161pp · 30,412 words
Gnuplot Cookbook
by Lee Phillips · 15 Feb 2012 · 199pp · 47,154 words
Traction: How Any Startup Can Achieve Explosive Customer Growth
by Gabriel Weinberg and Justin Mares · 5 Oct 2015 · 232pp · 63,846 words
Sleepyhead: Narcolepsy, Neuroscience and the Search for a Good Night
by Henry Nicholls · 1 Mar 2018 · 367pp · 102,188 words
JQuery UI
by Eric Sarrion · 15 Feb 2012 · 280pp · 40,881 words
We Are Data: Algorithms and the Making of Our Digital Selves
by John Cheney-Lippold · 1 May 2017 · 420pp · 100,811 words
Spam Nation: The Inside Story of Organized Cybercrime-From Global Epidemic to Your Front Door
by Brian Krebs · 18 Nov 2014 · 252pp · 75,349 words
Bezonomics: How Amazon Is Changing Our Lives and What the World's Best Companies Are Learning From It
by Brian Dumaine · 11 May 2020 · 411pp · 98,128 words
Your Money: The Missing Manual
by J.D. Roth · 18 Mar 2010 · 519pp · 118,095 words
Industrial Internet
by Jon Bruner · 27 Mar 2013 · 49pp · 12,968 words
Digital Dead End: Fighting for Social Justice in the Information Age
by Virginia Eubanks · 1 Feb 2011 · 289pp · 99,936 words
The Internet Trap: How the Digital Economy Builds Monopolies and Undermines Democracy
by Matthew Hindman · 24 Sep 2018
Silk Road
by Eileen Ormsby · 1 Nov 2014 · 269pp · 79,285 words
Brilliant, Crazy, Cocky: How the Top 1% of Entrepreneurs Profit From Global Chaos
by Sarah Lacy · 6 Jan 2011 · 269pp · 77,876 words

WikiLeaks and the Age of Transparency
by Micah L. Sifry · 19 Feb 2011 · 212pp · 49,544 words
Move Fast and Break Things: How Facebook, Google, and Amazon Cornered Culture and Undermined Democracy
by Jonathan Taplin · 17 Apr 2017 · 222pp · 70,132 words
Deep Work: Rules for Focused Success in a Distracted World
by Cal Newport · 5 Jan 2016
Bitcoin: The Future of Money?
by Dominic Frisby · 1 Nov 2014 · 233pp · 66,446 words
The Great Fragmentation: And Why the Future of All Business Is Small
by Steve Sammartino · 25 Jun 2014 · 247pp · 81,135 words
Sass for Web Designers
by Dan Cederholm · 14 May 2013 · 62pp · 15,274 words
Don't Make Me Think!: A Common Sense Approach to Web Usability
by Steve Krug · 2 Jan 2000 · 170pp · 42,196 words
Lab Rats: How Silicon Valley Made Work Miserable for the Rest of Us
by Dan Lyons · 22 Oct 2018 · 252pp · 78,780 words
The Snowden Files: The Inside Story of the World's Most Wanted Man
by Luke Harding · 7 Feb 2014 · 266pp · 80,018 words
Networks of Outrage and Hope: Social Movements in the Internet Age
by Manuel Castells · 19 Aug 2012 · 291pp · 90,200 words
Lurking: How a Person Became a User
by Joanne McNeil · 25 Feb 2020 · 239pp · 80,319 words
Company of One: Why Staying Small Is the Next Big Thing for Business
by Paul Jarvis · 1 Jan 2019 · 258pp · 74,942 words
Startupland: How Three Guys Risked Everything to Turn an Idea Into a Global Business
by Mikkel Svane and Carlye Adler · 13 Nov 2014 · 220pp
It Doesn't Have to Be Crazy at Work
by Jason Fried and David Heinemeier Hansson · 1 Oct 2018 · 117pp · 30,538 words
Grouped: How Small Groups of Friends Are the Key to Influence on the Social Web
by Paul Adams · 1 Nov 2011 · 123pp · 32,382 words